Denne artikel vil hjælpe dig til at fjerne .FileSlack Ransomware. Følg ransomware fjernelse vejledningen i slutningen af artiklen.
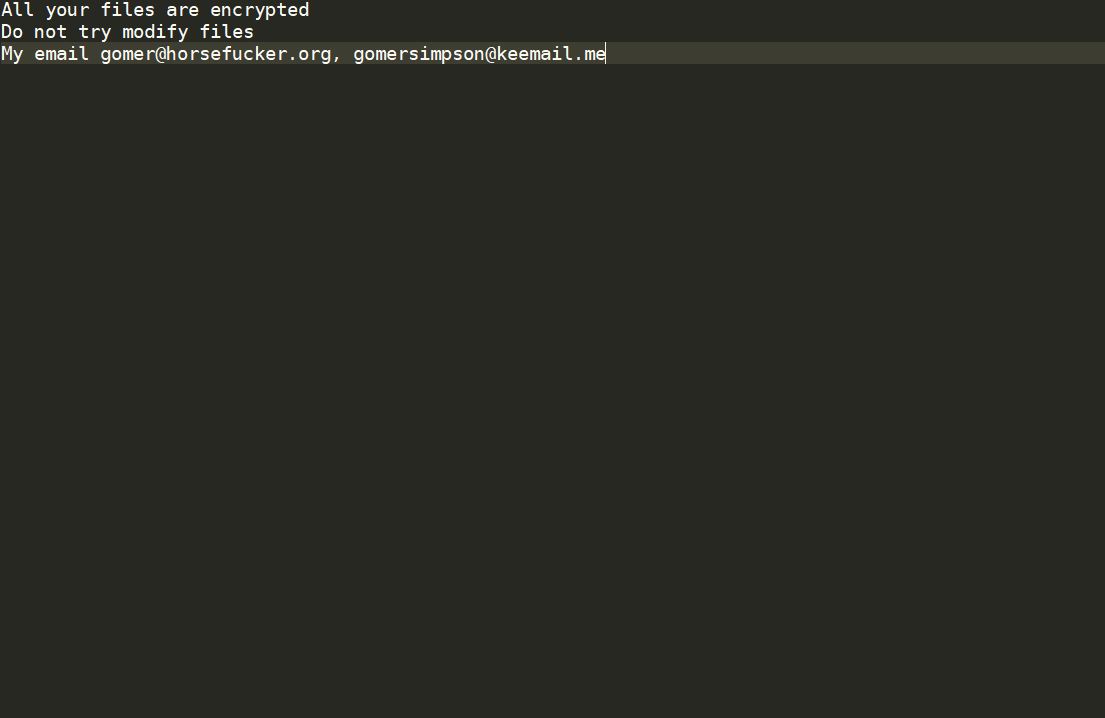
.FileSlack Ransomware er en, der krypterer dine data og kræver penge som en løsesum for at få det restaureret. Filer vil modtage .FileSlack udvidelse. Den .FileSlack Ransomware vil efterlade ransomware instruktioner som en desktop baggrundsbillede. Hold på at læse artiklen og se, hvordan du kan forsøge at potentielt genvinde nogle af dine låste filer og data.

Trussel Summary
| Navn | .FileSlack ransomware |
| Type | Ransomware, Cryptovirus |
| Kort beskrivelse | Den ransomware krypterer filer ved at placere .FileSlack udvidelse på de berørte filer på din computer og kræver en løsesum, der skal betales til angiveligt inddrive dem. |
| Symptomer | Den ransomware vil kryptere dine filer og efterlade en løsesum notat med betalingsinstrukser. |
| Distributionsmetode | Spam e-mails, Vedhæftede filer |
| Værktøj Detection |
Se, om dit system er blevet påvirket af malware
Hent
Værktøj til fjernelse af malware
|
Brugererfaring | Tilmeld dig vores forum at diskutere. FilSlack ransomware. |
| Data Recovery Tool | Windows Data Recovery af Stellar Phoenix Varsel! Dette produkt scanner dine drev sektorer til at gendanne mistede filer, og det kan ikke komme sig 100% af de krypterede filer, men kun få af dem, afhængigt af situationen og uanset om du har omformateret drevet. |

.FileSlack Ransomware - Distributionsteknikker
Denne særlige trussel blev fundet i en angrebskampagne med lavt antal, der viser, at det meget muligt er, at det i øjeblikket er en tidlig testudgivelse. Som sådan har vi ikke oplysninger om den foretrukne distributionsmetode for de endelige prøver, der skal frigives. Vi formoder, at de mest populære bliver brugt på samme tid for at øge antallet af ramte ofre.
En af de mest populære måder er at levere phishing e-mails der sendes på en bulk måde og forsøger at manipulere ofrene til at tro, at de har modtaget en legitim anmeldelse fra et velkendt firma eller en tjeneste. Kroppens indhold indeholder links til .FileSlack ransomware-filen, eller de kan vedhæftes direkte.
En lignende strategi er at implementere falske ondsindede websteder som udgør som legitime søgemaskiner, download-portaler og software destinationssider. De hostes på domæner, der på samme måde er opkaldt efter de rigtige domæner. Stålede eller hackerfremstillede sikkerhedscertifikater kan også bruges til at få siderne til at vises som sikre.
En mekanisme, der ofte bruges til at integrere virusinstallationsskripterne, er at placere dem i payload luftfartsselskaber, to af de mest populære typer er følgende:
- Dokumenter - Virusinstallationsskripterne kan placeres som makroer, der er vigtige funktioner, der kan gøres til en del af ethvert populært format: regneark, præsentationer, tekstdokumenter og databaser. Hver gang de åbnes af offerbrugerne, vises en meddelelse, der beder dem om at aktivere scripts. Den citerede årsag, der oftest vises, er at dette er et krav for korrekt visning af filen.
- Ondsindet program Installers - Den anden strategi er at oprette virusinficerede installationsfiler af populær software, der distribueres ved hjælp af de nævnte distributionsmetoder. Det kriminelle kollektiv vælger applikationer, der almindeligvis installeres af slutbrugerne: systemværktøjer, kreativitet suiter, produktivitet og kontor apps og etc. Hackerne tager den rigtige fil og ændrer den i overensstemmelse hermed. Derefter kan det sendes via e-mail-beskeder, linket i falske websteder eller uploadet til fildelingsnetværk.
Større kampagner kan planlægges ved programmering browser hijackers at levere dem som nyttelast. De er ondsindede plugins til webbrowsere, der har det primære mål at omdirigere ofrene til en forudindstillet destinationsside. Dette gøres ved at ændre deres standardindstillinger: startside, søgemaskine og nye faner side. Ransomware-infektionen udføres, så snart plugins er installeret. De findes ofte i det relevante webbrowser-plugin-lager, der indeholder falske brugeranmeldelser og beskrivelser, der lover adskillige ydeevne forbedringer og tilføjelser af funktioner.

.FileSlack Ransomware - Detaljeret analyse
Da der ikke findes nogen oplysninger om .FileSlack ransomware, antager vi, at kun basiskrypteringsmotoren er en del af den. Disse tidlige versioner af virussen kan kun præsentere en modulær ramme, som man kan arbejde på. Som sådan er det muligt, at standardadfærdsmønsteret som observeret af os.
De fleste vira starter infektionen med hentning af følsomme oplysninger fra inficerede maskiner. Dette gøres via en motor, der er programmeret til at lede efter bestemte strenge i henhold til den ønskede information. Hvis den interagerer med Windows Volume Manager-tjenesten, kan den også få adgang til og hente data fra netværksshares og flytbare lagerenheder.. I de fleste af de registrerede tilfælde vil denne motor have det primære mål at tildele et unikt ID til hver maskine. Dette gøres ved hjælp af en algoritme, der tager dens inputparametre fra listen over installerede hardwarekomponenter, brugerindstillinger og miljø værdier.
De indsamlede oplysninger kan bruges til at bypass sikkerhedssoftware findes på de inficerede maskiner. Motoren scanner hukommelsen og harddiskindholdet for alle tjenester, der kan blokere .FileSlack Ransomware. Listen omfatter anti-virus produkter, firewalls, virtuel maskine værter og sandkasse miljøer.
Når ransomwaremotoren har fået adgang til systemet, kan den fortsætte med forskellige ændringer. En liste over de mest populære dem er følgende:
- Opstartsmuligheder - Ved at ændre standardstartindstillingerne kan .FileSlack ransomware starte automatisk, så snart computeren er tændt. Derudover fungerer manuelle gendannelsesinstruktioner muligvis ikke længere, da adgang til gendannelsesindstillingerne kan blokeres. I dette tilfælde er kun en anti-spywareløsning af høj kvalitet i stand til at afhjælpe infektionen.
- Windows-registreringsværdier Ændringer - Motoren kan få adgang til og ændre Windows-registreringsdatabasen ved både at oprette poster til sig selv og ændre eksisterende. Dette er særligt farligt, da enhver manipulation af operativsystemets strenge kan føre til alvorlige ydelsesproblemer til det punkt, at de ikke kan bruge computeren, medmindre malware fjernes fuldstændigt.. Ændringer af tredjepartsapplikationer kan resultere i pludselige applikationsfejl og lukkes ned.
- data, fjernelse - Motoren kan instrueres i at finde og slette følsomme filer, hvilket gør gendannelsen meget vanskelig: System Restore Points, Backups og Shadow Volume Kopier.
- Yderligere Payload Levering - Ransomware er i stand til at levere andre trusler mod de kompromitterede maskiner. Dette gøres, fordi ..FileSlack Ransomware måske allerede har omgået nøglesikkerhedsinfrastruktur gennem sit første sæt kommandoer, og den anden droppede virus vil være i stand til at udfolde alt sit potentiale.
Enhver anden ondsindet adfærd kan programmeres af kriminelle - sandsynligvis afhænger rækkevidden af de kommandoer, der skal udføres, af hackerkonfigurationen og de tilsigtede mål.

.FileSlack Ransomware - Krypteringsproces
Som andre populære vira vil .FileSlack ransomware starte krypteringsmotoren, når alle tidligere moduler er færdige med at køre. Det vil sandsynligvis bruge en indbygget liste over mål filtype extensions, som skal behandles af en stærk cipher. Et eksempel Listen kan omfatte følgende datatyper:
- Backups
- Databaser
- Arkiv
- Billeder
- Musik
- Videoer
Alle berørte filer vil modtage .FileSlack udvidelse og den tilhørende ransomware note vil blive kaldt Readme_Restore_Files.txt.

Fjern .FileSlack Ransomware, og prøv at gendanne data
Hvis din computer-system fik inficeret med .FileSlack ransomware virus, du skal have lidt erfaring med at fjerne malware. Du bør slippe af med denne ransomware så hurtigt som muligt, før det kan få mulighed for at sprede sig yderligere og inficere andre computere. Du bør fjerne ransomware og følg trin-for-trin instruktioner guide nedenfor.
- Trin 1
- Trin 2
- Trin 3
- Trin 4
- Trin 5
Trin 1: Scan efter .FileSlack ransomware med SpyHunter Anti-Malware Tool



Automatisk fjernelse af ransomware - Videoguide
Trin 2: Uninstall .FileSlack ransomware and related malware from Windows
Her er en metode i nogle få nemme trin, der bør være i stand til at afinstallere de fleste programmer. Uanset om du bruger Windows 10, 8, 7, Vista eller XP, disse skridt vil få arbejdet gjort. At trække det program eller dets mappe til papirkurven kan være en meget dårlig beslutning. Hvis du gør det, stumper og stykker af programmet er efterladt, og det kan føre til ustabile arbejde på din PC, fejl med filtypen foreninger og andre ubehagelige aktiviteter. Den rigtige måde at få et program fra din computer er at afinstallere det. For at gøre dette:


 Følg instruktionerne ovenfor, og du vil med succes slette de fleste uønskede og ondsindede programmer.
Følg instruktionerne ovenfor, og du vil med succes slette de fleste uønskede og ondsindede programmer.
Trin 3: Rens eventuelle registre, oprettet af .FileSlack ransomware på din computer.
De normalt målrettede registre af Windows-maskiner er følgende:
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion Run
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion Run
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion RunOnce
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion RunOnce
Du kan få adgang til dem ved at åbne Windows Registry Editor og slette eventuelle værdier, oprettet af .FileSlack ransomware der. Dette kan ske ved at følge trinene nedenunder:


 Tip: For at finde en virus-skabt værdi, du kan højreklikke på det og klikke "Modificere" at se, hvilken fil det er indstillet til at køre. Hvis dette er virus fil placering, fjerne værdien.
Tip: For at finde en virus-skabt værdi, du kan højreklikke på det og klikke "Modificere" at se, hvilken fil det er indstillet til at køre. Hvis dette er virus fil placering, fjerne værdien.
Inden start "Trin 4", be om boot tilbage til normal tilstand, hvis du er i øjeblikket i fejlsikret tilstand.
Dette vil gøre det muligt for dig at installere og brug SpyHunter 5 succesfuld.
Trin 4: Start din pc i fejlsikret tilstand for at isolere og fjerne .FileSlack ransomware





Trin 5: Prøv at gendanne filer krypteret af .FileSlack ransomware.
Metode 1: Brug STOP Decrypter af Emsisoft.
Ikke alle varianter af denne ransomware kan dekrypteres gratis, men vi har tilføjet den decryptor bruges af forskere, der ofte opdateret med de varianter, der i sidste ende blive dekrypteret. Du kan prøve og dekryptere dine filer ved hjælp nedenstående vejledning, men hvis de ikke arbejde, så desværre din variant af ransomware virus er ikke dekrypteres.
Følg instruktionerne nedenfor for at bruge Emsisoft Decrypter og dekryptere dine filer gratis. Du kan downloade Emsisoft dekryptering værktøj knyttet her og derefter følge trinene nedenfor tilvejebragte:
1 Højreklik på Decrypter og klik på Kør som administrator som vist nedenfor:

2. Enig med licensbetingelserne:

3. Klik på "Tilføj mappe" og derefter tilføje de mapper, hvor du ønsker filerne dekrypteret som vist nedenunder:

4. Klik på "Dekryptér" og vente på dine filer, der skal afkodes.

Note: Kredit til decryptor går til Emsisoft forskere, der har gjort det gennembrud med denne virus.
Metode 2: Brug datagendannelsessoftware
Ransomware infektioner og .FileSlack ransomware sigter mod at kryptere dine filer ved hjælp af en krypteringsalgoritme, som det kan være meget vanskeligt at dekryptere. Det er derfor, vi har foreslået en data recovery metode, der kan hjælpe dig med at gå rundt direkte dekryptering og forsøge at gendanne dine filer. Husk, at denne metode ikke kan være 100% effektiv, men kan også hjælpe dig lidt eller meget i forskellige situationer.
Du skal blot klikke på linket og på hjemmesidens menuer øverst, vælge data Recovery - Guiden til gendannelse af data til Windows eller Mac (afhængigt af dit operativsystem), og download og kør derefter værktøjet.
.FileSlack ransomware-FAQ
What is .FileSlack ransomware Ransomware?
.FileSlack ransomware er en ransomware infektion - den ondsindede software, der lydløst kommer ind på din computer og blokerer enten adgang til selve computeren eller krypterer dine filer.
Mange ransomware-vira bruger sofistikerede krypteringsalgoritmer til at gøre dine filer utilgængelige. Målet med ransomware-infektioner er at kræve, at du betaler en løsepenge-betaling for at få adgang til dine filer tilbage.
What Does .FileSlack ransomware Ransomware Do?
Ransomware er generelt en ondsindet software der er designet for at blokere adgangen til din computer eller filer indtil en løsesum er betalt.
Ransomware-virus kan også beskadige dit system, korrupte data og slette filer, resulterer i permanent tab af vigtige filer.
How Does .FileSlack ransomware Infect?
Via flere måder..FileSlack ransomware Ransomware inficerer computere ved at blive sendt via phishing-e-mails, indeholder virus vedhæftning. Denne vedhæftning maskeres normalt som et vigtigt dokument, lignende En faktura, bankdokument eller endda en flybillet og det ser meget overbevisende ud for brugerne.
Another way you may become a victim of .FileSlack ransomware is if you download et falsk installationsprogram, crack eller patch fra et websted med lavt omdømme eller hvis du klikker på et viruslink. Mange brugere rapporterer at få en ransomware-infektion ved at downloade torrents.
How to Open ..FileSlack ransomware files?
Du can't uden en dekryptering. På dette tidspunkt, den ..FileSlack ransomware filer er krypteret. Du kan kun åbne dem, når de er dekrypteret ved hjælp af en specifik dekrypteringsnøgle til den bestemte algoritme.
Hvad skal man gøre, hvis en dekryptering ikke virker?
Gå ikke i panik, og sikkerhedskopiere filerne. Hvis en dekrypter ikke dekrypterede din ..FileSlack ransomware filer med succes, så fortvivl ikke, fordi denne virus stadig er ny.
Kan jeg gendanne "..FileSlack ransomware" Filer?
Ja, undertiden kan filer gendannes. Vi har foreslået flere filgendannelsesmetoder det kunne fungere, hvis du vil gendanne ..FileSlack ransomware filer.
Disse metoder er på ingen måde 100% garanteret, at du vil være i stand til at få dine filer tilbage. Men hvis du har en sikkerhedskopi, dine chancer for succes er meget større.
How To Get Rid of .FileSlack ransomware Virus?
Den sikreste måde og den mest effektive til fjernelse af denne ransomware-infektion er brugen a professionelt anti-malware program.
Det vil scanne efter og finde .FileSlack ransomware ransomware og derefter fjerne det uden at forårsage yderligere skade på dine vigtige ..FileSlack ransomware filer.
Kan jeg rapportere Ransomware til myndigheder?
Hvis din computer blev inficeret med en ransomware-infektion, du kan rapportere det til de lokale politiafdelinger. Det kan hjælpe myndigheder overalt i verden med at spore og bestemme gerningsmændene bag den virus, der har inficeret din computer.
Nedenfor, Vi har udarbejdet en liste med offentlige websteder, hvor du kan indgive en rapport, hvis du er offer for en cyberkriminalitet:
Cybersikkerhedsmyndigheder, ansvarlig for håndtering af ransomware-angrebsrapporter i forskellige regioner over hele verden:
Tyskland - Officiel portal for det tyske politi
Forenede Stater - IC3 Internet Crime Complaint Center
Storbritannien - Action svig politi
Frankrig - Indenrigsministeriet
Italien - Statens politi
Spanien - Nationalt politi
Holland - Retshåndhævelse
Polen - Politi
Portugal - Justitspolitiet
Grækenland - Enhed om cyberkriminalitet (Hellenske politi)
Indien - Mumbai-politiet - CyberCrime-undersøgelsescelle
Australien - Australsk High Tech Crime Center
Rapporter kan besvares inden for forskellige tidsrammer, afhængigt af dine lokale myndigheder.
Kan du stoppe Ransomware i at kryptere dine filer?
Ja, du kan forhindre ransomware. Den bedste måde at gøre dette på er at sikre, at dit computersystem er opdateret med de nyeste sikkerhedsrettelser, bruge et velrenommeret anti-malware program og firewall, sikkerhedskopiere dine vigtige filer ofte, og undgå at klikke videre ondsindede links eller downloade ukendte filer.
Can .FileSlack ransomware Ransomware Steal Your Data?
Ja, i de fleste tilfælde ransomware vil stjæle dine oplysninger. It is a form of malware that steals data from a user's computer, krypterer det, og kræver derefter en løsesum for at dekryptere den.
I mange tilfælde, den malware forfattere eller angribere vil true med at slette data eller udgive det online medmindre løsesummen er betalt.
Kan Ransomware inficere WiFi?
Ja, ransomware kan inficere WiFi-netværk, da ondsindede aktører kan bruge det til at få kontrol over netværket, stjæle fortrolige data, og låse brugere ud. Hvis et ransomware-angreb lykkes, det kan føre til tab af service og/eller data, og i nogle tilfælde, økonomiske tab.
Skal jeg betale Ransomware?
Nej, du bør ikke betale ransomware-afpressere. At betale dem opmuntrer kun kriminelle og garanterer ikke, at filerne eller dataene bliver gendannet. Den bedre tilgang er at have en sikker backup af vigtige data og være opmærksom på sikkerheden i første omgang.
What Happens If I Don't Pay Ransom?
If you don't pay the ransom, hackerne kan stadig have adgang til din computer, data, eller filer og kan fortsætte med at true med at afsløre eller slette dem, eller endda bruge dem til at begå cyberkriminalitet. I nogle tilfælde, de kan endda fortsætte med at kræve yderligere løsepengebetalinger.
Kan et Ransomware-angreb opdages?
Ja, ransomware kan detekteres. Anti-malware-software og andre avancerede sikkerhedsværktøjer kan opdage ransomware og advare brugeren når det er til stede på en maskine.
Det er vigtigt at holde sig ajour med de seneste sikkerhedsforanstaltninger og at holde sikkerhedssoftware opdateret for at sikre, at ransomware kan opdages og forhindres.
Bliver ransomware-kriminelle fanget?
Ja, ransomware-kriminelle bliver fanget. Retshåndhævende myndigheder, såsom FBI, Interpol og andre har haft succes med at opspore og retsforfølge ransomware-kriminelle i USA og andre lande. I takt med at ransomware-trusler fortsætter med at stige, det samme gør håndhævelsesaktiviteten.
About the .FileSlack ransomware Research
Indholdet udgiver vi på SensorsTechForum.com, this .FileSlack ransomware how-to removal guide included, er resultatet af omfattende forskning, hårdt arbejde og vores teams hengivenhed til at hjælpe dig med at fjerne den specifikke malware og gendanne dine krypterede filer.
Hvordan udførte vi undersøgelsen af denne ransomware?
Vores forskning er baseret på en uafhængig undersøgelse. Vi er i kontakt med uafhængige sikkerhedsforskere, og som sådan, vi modtager daglige opdateringer om de seneste malware- og ransomware-definitioner.
Endvidere, the research behind the .FileSlack ransomware ransomware threat is backed with VirusTotal og NoMoreRansom projekt.
For bedre at forstå ransomware-truslen, Se venligst følgende artikler, som giver kyndige detaljer.
Som et sted, der siden har været dedikeret til at levere gratis fjernelsesinstruktioner for ransomware og malware 2014, SensorsTechForum's anbefaling er at Vær kun opmærksom på pålidelige kilder.
Sådan genkendes pålidelige kilder:
- Kontroller altid "Om os" hjemmeside.
- Profil af indholdsskaberen.
- Sørg for, at rigtige mennesker er bag webstedet og ikke falske navne og profiler.
- Bekræft Facebook, LinkedIn og Twitter personlige profiler.