 Quels sont virus BestBuy? Est un virus BestBuy dangereux? Comment supprimer un virus BestBuy à partir de votre ordinateur?
Quels sont virus BestBuy? Est un virus BestBuy dangereux? Comment supprimer un virus BestBuy à partir de votre ordinateur?
les infections virales BestBuy peuvent se produire à travers de multiples façons. Ils profitent du nom du site commercial afin de se promouvoir. Les différentes attaques de virus sont exploités par différents groupes de hacking et de particuliers - nous avons reçu des rapports de nombreuses campagnes qui utilisent le nom BestBuy dans différents éléments. La plupart d'entre eux sont liés à des scripts malveillants qui se trouvent dans les redirections et les pop-ups, ainsi que des annonces intrusives. La lecture de cet article vous aidera à vous protéger des sites BestBuy et fausses infections virales.

Menace Résumé
| Nom | Virus BestBuy |
| Type | Malware |
| brève description | Virus qui profite du site commercial légitime et célèbre BestBuy. |
| Symptômes | Les symptômes peuvent être ALLANT de voir réoriente à avoir Trojan symptômes moins sur votre ordinateur. |
| Méthode de distribution | Téléchargements groupés. pages Web qui peuvent l'annoncer. |
| Detection Tool |
Voir si votre système a été affecté par des logiciels malveillants
Télécharger
Malware Removal Tool
|
Expérience utilisateur | Rejoignez notre Forum Virus pour discuter BestBuy. |

BestBuy Virus - Comment ai-je ce?
des échantillons de virus BestBuy peuvent se propager en utilisant une multitude de façons en fonction de leur type exact. Divers groupes hacking peuvent créer leurs propres versions et les envoyer en utilisant des méthodes de distribution multiples. Cela signifie que plusieurs itérations du virus BestBuy peuvent être actifs en même temps. Habituellement, la technique la plus courante est la coordination des campagnes de phishing qui sont principalement envoyés par messages électroniques. Les pirates usurper l'identité des entreprises et des services bien connus et préparer le contenu nécessaire qui infecte les destinataires par le virus BestBuy. L'autre technique qui est souvent utilisé est la création de nombreux sites. Ils posent les pages officielles ou filiale de ces sociétés et afin de tromper les utilisateurs en leur faisant croire qu'ils ont accédé au site réel qu'ils peuvent utiliser de vol ou de contenu faux. Les pages sont hébergées sur des adresses qui sont presque identiques et les sites peuvent inclure des certificats de sécurité qui sont auto-signés ou volés.
Les pages peuvent être annoncés en utilisant d'autres méthodes aussi bien, un populaire est la distribution de les pirates de navigateur qui sont des plugins dangereux rendus compatibles avec les navigateurs web les plus populaires. Ils sont généralement chargés dans les référentiels pertinents à l'aide des informations d'identification de développeur faux ou volés. Les descriptions élaborées affichées peuvent inclure des vidéos et commentaires des utilisateurs ainsi que des promesses de l'ajout de nouvelles fonctionnalités nouvelles qui peuvent être liés aux caractéristiques du site BestBuy. Ces extensions peuvent également promettre des codes de réduction ou d'autres extras séduisants.
Dans de nombreux cas, les fichiers exécutables peuvent être générés qui conduira à des infections virales BestBuy, la plupart d'entre eux peuvent être classés en deux groupes principaux:
- Documents malicieuses - Les pirates peuvent concevoir des documents macro-infectés qui peuvent aller de feuilles de calcul, présentations, bases de données et des fichiers texte. Dès qu'ils sont ouverts par les victimes une invite sera donné naissance à demander aux victimes de permettre au contenu intégré afin d'afficher correctement le document. Si cela est fait alors l'infection par le virus suivra.
- Les installateurs d'application - Le code d'installation du virus peut être placé à l'intérieur d'installation d'applications qui sont souvent par des utilisations finales. Ils peuvent se propager sur les méthodes de phishing et des e-mails, ainsi que téléchargé au partage de fichiers réseaux comme BitTorrent.
A tout moment, les techniques de distribution peuvent se déplacer et d'autres méthodes peuvent être employées. Cela inclut la livraison par d'autres logiciels malveillants qui ont déjà eu un impact les hôtes cibles.

BestBuy Virus - Que faut-il faire?
Comme il existe de nombreuses variantes du virus BestBuy et aucune analyse unique peut être une menace représentative de toute la famille dans cet article, nous présentons la majorité des actions malveillantes qui sont souvent exécutées.
Les infections peuvent commencer par un Module de récolte de données qui est capable de pirater des informations sensibles qui peuvent exposer l'identité des victimes. Il peut également générer un profil des composants matériels installés. Ces données peuvent être introduit dans un autre module qui peut générer un identifiant unique qui est associé à chaque ordinateur.
Sur la base de ces données, le moteur peut alors procéder à l'intrusion réelle en le définissant comme menace persistante ce qui signifie qu'il va commencer dès que l'ordinateur est sous tension. Des échantillons de virus avancés peuvent également bloquer l'accès aux options de démarrage de récupération rendant ainsi impossible de suivre la plupart des guides d'enlèvement de manuel utilisateur.
À la suite de l'infection réussie du virus BestBuy peut alors procéder à d'autres les modifications du système. Ils peuvent aller de modifications du Registre Windows aux changements dans les fichiers de configuration. Cela peut conduire à de graves problèmes de performances, l'incapacité d'exécuter certaines fonctions et la perte de données.
Gardez à l'esprit que si l'infection est venue par un pirate de navigateur puis le code peut récupérer toutes les informations stockées et rediriger les utilisateurs à ouvrir toujours le site de virus Bestbuy faux contrôlé pirate désigné.
Ce qui est plus dangereux est le fait que les infections actives peuvent être utilisées pour déployer d'autres logiciels malveillants pour les systèmes d'aide aux victimes. les POPULAIRES sont les suivantes:
- Ransomware - Ces fichiers cryptant virus traitera les données utilisateur sur la base d'une liste intégrée des extensions de type de fichier cible. Un chiffre fort WLL être utilisé pour chiffrer tous et les utilisateurs des victimes sera extorqué de payer une redevance de rançon.
- Les chevaux de Troie - Ces virus permettront aux criminels d'établir une connexion sécurisée et persistante à un serveur contrôlé hacker. Elle permettra aux pirates d'espionner les victimes en temps réel, prendre le contrôle de leurs ordinateurs et voler tout fichier à tout moment.
- mineurs - mineurs sont parmi les crypto-monnaie virus les plus dangereux qui peuvent même être sous la forme de scripts simples. Ils télécharger de nombreuses tâches mathématiques de petite taille qui place un lourd tribut sur la performance du système. Ils profiteront des ressources comme le CPU, la mémoire et de l'espace de disque dur. Dès que l'un d'entre eux est signalé comme complète les pirates recevront un revenu à titre de compensation qui sera câblé directement à leur porte-monnaie numérique.
- Adware - Le virus BestBuy peut également implanter plusieurs logiciels publicitaires sur les ordinateurs infectés. Cela signifie que tout en naviguant sur les sites ordinaires les utilisateurs des victimes peuvent tomber sur des annonces et des bannières qui n'ont pas vus avant. Ceci est soit une manipulation en temps réel des navigateurs web ou tout autre comportement dangereux qui est observée par les utilisateurs.
L'un des effets les plus dangereux d'avoir un tel virus installé sur un ordinateur donné est le fait que les infections peuvent en être utilisées pour recueillir tous les fichiers sensibles que les pirates peuvent considérer comme utile. modules malveillants existants peuvent être utilisés pour supprimer des informations telles que les sauvegardes, points de restauration et des copies de volume d'ombre.
Si l'infection est liée à la création d'un faux site qui imite le vrai portail achats BestBuy les utilisateurs peuvent être présentés avec des offres de phishing et les invites de connexion. Cela signifie que les utilisateurs peuvent être incités à entrer dans leurs informations de connexion sur le site BestBuy.
Comme ce virus semble cibler le site e-commerce, il peut être lié à Les chevaux de Troie bancaires. Ce sont des programmes malveillants de petite taille qui surveillera si les victimes d'accéder aux services bancaires en ligne et les applications financières. les frappes, souris mouvement et toute entrée de l'utilisateur seront capturés dans le but d'avoir accès à leurs comptes. informations de transfert bancaire peut être modifié à l'insu des utilisateurs qui fera automatiquement le virement sur le compte des criminels.
Dans certains cas, les informations obtenues peuvent être réticulés avec d'autres bases de données et référentiels des pouvoirs volés. Ceci est particulièrement utile si les attaques sont comanded d'un groupe criminel, les informations récoltées peuvent ensuite être triés par eux et vendus aux parties intéressées ou abusée plus. Dans de nombreux cas, en fonction des informations recueillies les pirates peuvent lancer diverses campagnes d'ingénierie sociale ou de chantage contre les victimes.

Retirer BestBuy virus de votre machine
Afin d'être en mesure d'éliminer le virus BestBuy, vous devez savoir où il est des fichiers et des objets sont cachés. L'idée principale est de suivre les étapes de déplacement ci-dessous. Ils sont faits pour vous aider à isoler le virus et détecter et supprimer les fichiers malveillants. Pour la détection et l'enlèvement des Virus BestBuy, cependant, nous vous suggérons fortement de télécharger et d'exécuter un scan gratuit avec un logiciel anti-malware avancée. Cet outil identifie automatiquement et d'éliminer tous les fichiers de virus et d'objets, lié à un virus BestBuy de votre ordinateur ainsi que le protéger dans le futur.
- Fenêtres
- Mac OS X
- Google Chrome
- Mozilla Firefox
- Microsoft bord
- Safari
- Internet Explorer
- Arrêter les pop-ups push
Comment supprimer BestBuy Virus de Windows.
Étape 1: Virus Scan for BestBuy avec SpyHunter Anti-Malware outil



Étape 2: Démarrez votre PC en mode sans échec





Étape 3: Désinstaller BestBuy Virus et logiciels connexes à partir de Windows
Étapes de désinstallation pour Windows 11
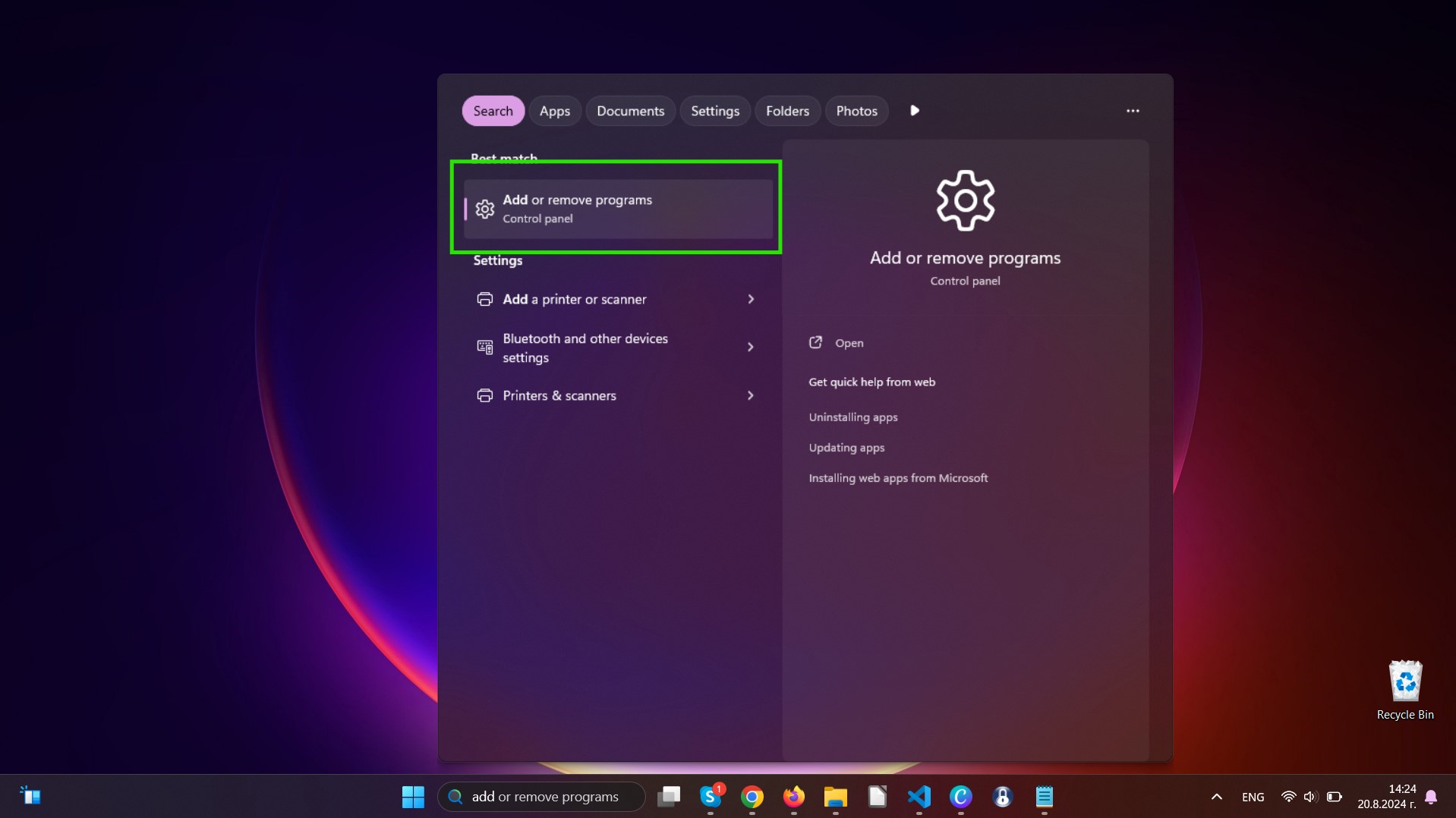
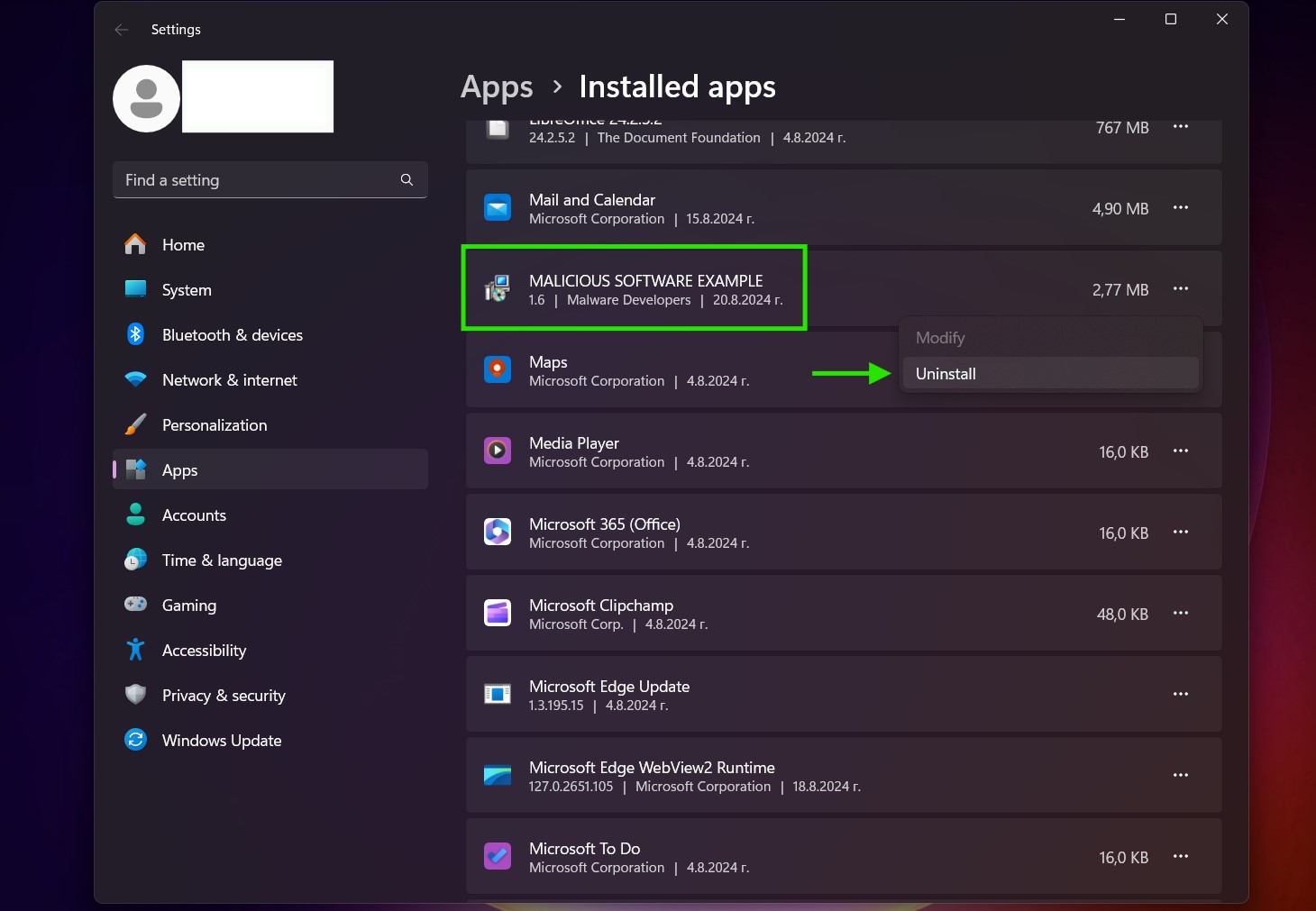
Étapes de désinstallation pour Windows 10 et versions plus anciennes
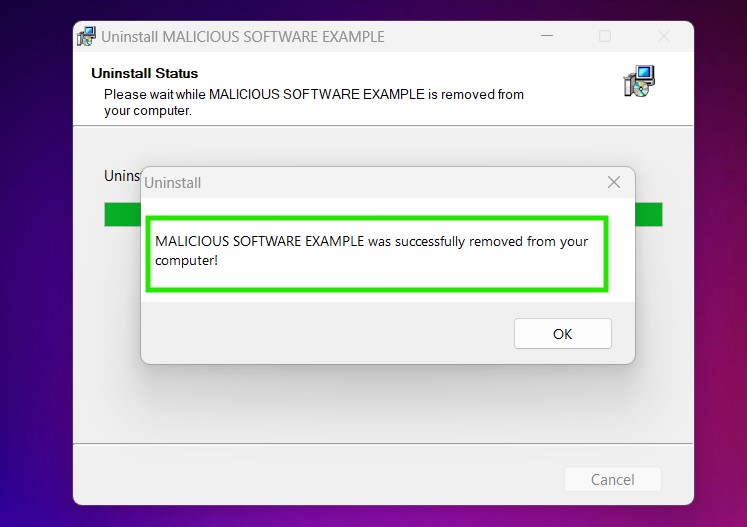
Voici une méthode en quelques étapes simples qui devraient pouvoir désinstaller la plupart des programmes. Peu importe si vous utilisez Windows 10, 8, 7, Vista ou XP, ces mesures seront faire le travail. Faire glisser le programme ou de son dossier à la corbeille peut être un très mauvaise décision. Si vous faites cela, des morceaux du programme sont laissés, et qui peut conduire à un travail instable de votre PC, erreurs avec les associations de types de fichiers et d'autres activités désagréables. La bonne façon d'obtenir un programme sur votre ordinateur est de le désinstaller. Pour ce faire,:


 Suivez les instructions ci-dessus et vous désinstaller avec succès la plupart des programmes.
Suivez les instructions ci-dessus et vous désinstaller avec succès la plupart des programmes.
Étape 4: Nettoyer tous les registres, Created by BestBuy Virus on Your PC.
Les registres généralement ciblés des machines Windows sont les suivantes:
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion Run
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion Run
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion RunOnce
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion RunOnce
Vous pouvez y accéder en ouvrant l'éditeur de Registre Windows et la suppression de toutes les valeurs, Virus créé par BestBuy il. Cela peut se produire en suivant les étapes ci-dessous:


 Pointe: Pour trouver une valeur créée virus, vous pouvez faire un clic droit dessus et cliquez "Modifier" pour voir quel fichier il est configuré pour exécuter. Si cela est l'emplacement du fichier de virus, supprimer la valeur.
Pointe: Pour trouver une valeur créée virus, vous pouvez faire un clic droit dessus et cliquez "Modifier" pour voir quel fichier il est configuré pour exécuter. Si cela est l'emplacement du fichier de virus, supprimer la valeur.
Video Removal Guide for BestBuy Virus (Fenêtres).
Débarrassez-vous de BestBuy Virus de Mac OS X.
Étape 1: Uninstall BestBuy Virus and remove related files and objects
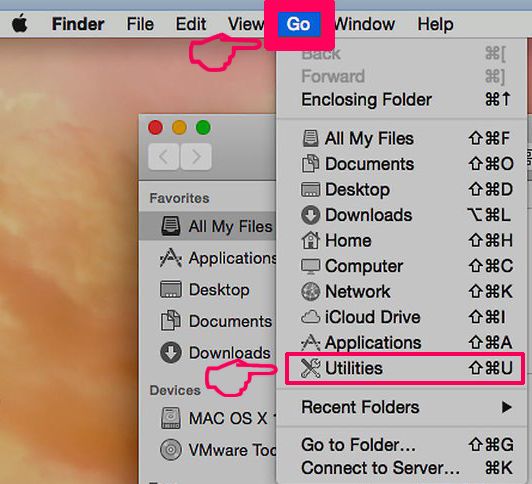
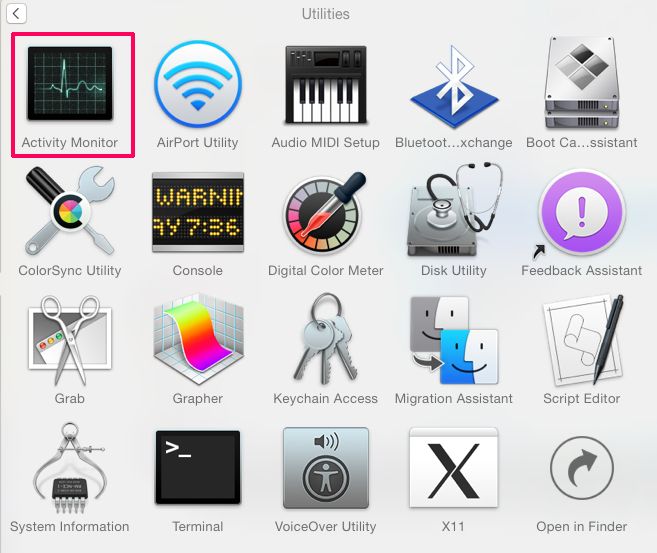
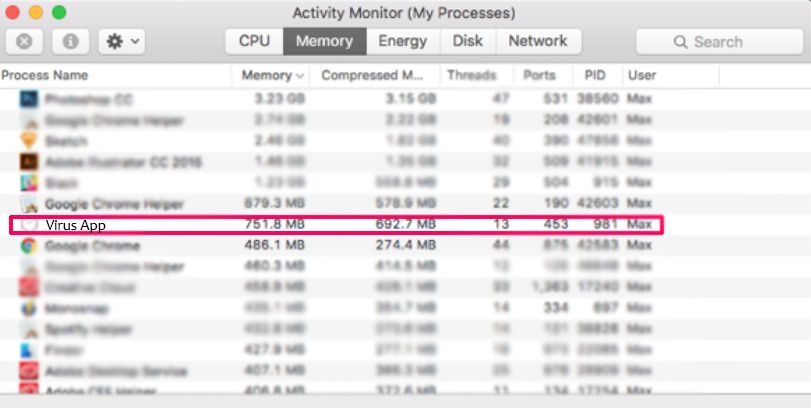
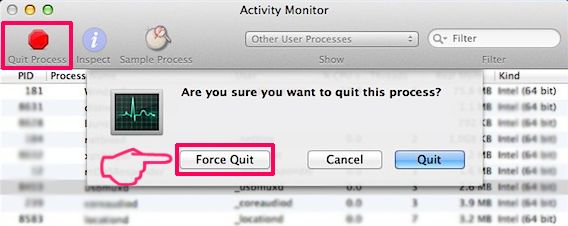
Votre Mac vous affichera une liste des éléments qui démarrent automatiquement lorsque vous vous connectez. Recherchez les applications suspectes identiques ou similaires à virus BestBuy. Vérifiez l'application que vous voulez arrêter de courir automatiquement puis sélectionnez sur le Moins ("-") icône pour cacher.
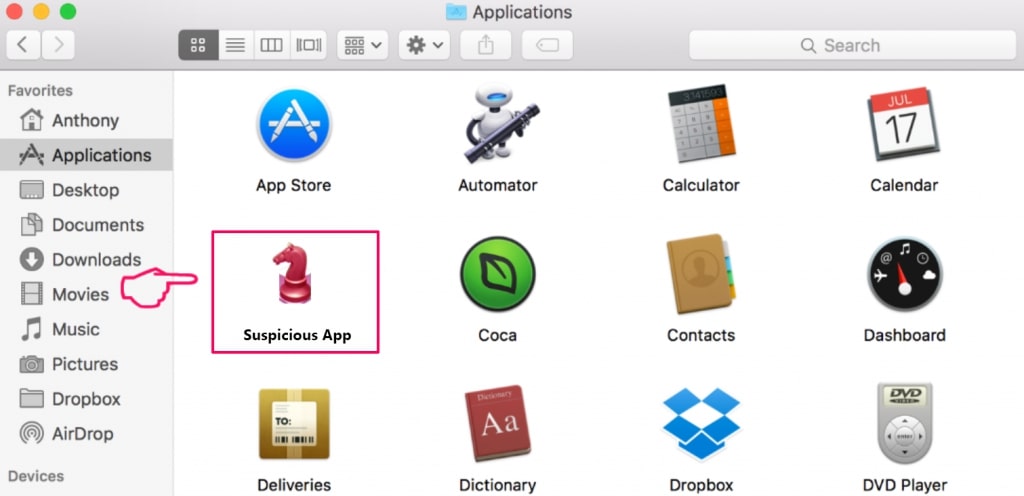
- Aller à Chercheur.
- Dans la barre de recherche tapez le nom de l'application que vous souhaitez supprimer.
- Au-dessus de la barre de recherche changer les deux menus déroulants à "Fichiers système" et "Sont inclus" de sorte que vous pouvez voir tous les fichiers associés à l'application que vous souhaitez supprimer. Gardez à l'esprit que certains des fichiers ne peuvent pas être liés à l'application de manière très attention quels fichiers vous supprimez.
- Si tous les fichiers sont liés, tenir la ⌘ + A boutons pour les sélectionner, puis les conduire à "Poubelle".
Si vous ne pouvez pas supprimer le virus BestBuy via Étape 1 au dessus:
Si vous ne trouvez pas les fichiers de virus et des objets dans vos applications ou d'autres endroits que nous avons indiqués ci-dessus, vous pouvez rechercher manuellement pour eux dans les bibliothèques de votre Mac. Mais avant de faire cela, s'il vous plaît lire l'avertissement ci-dessous:
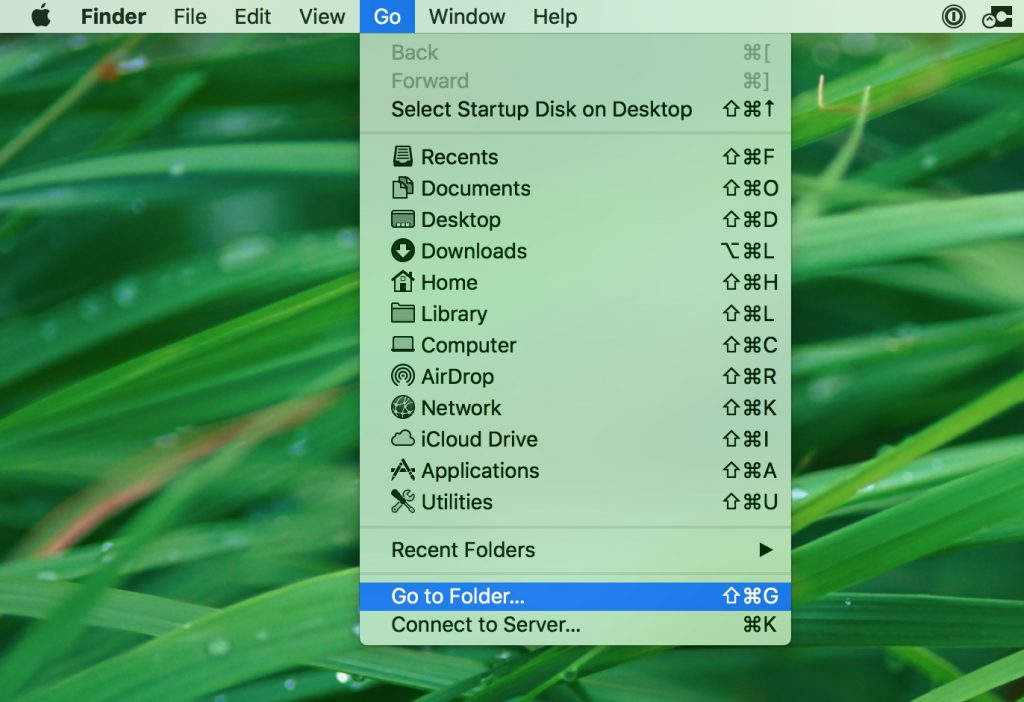
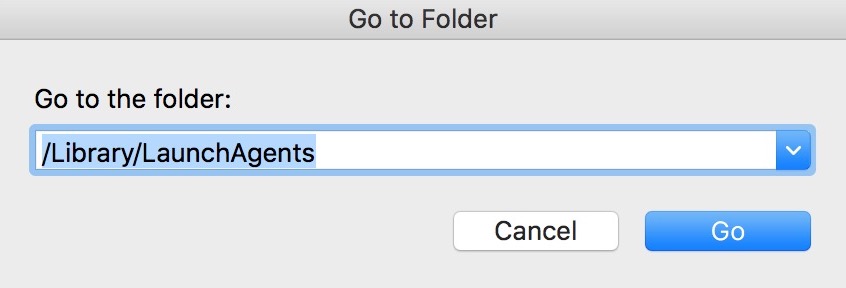
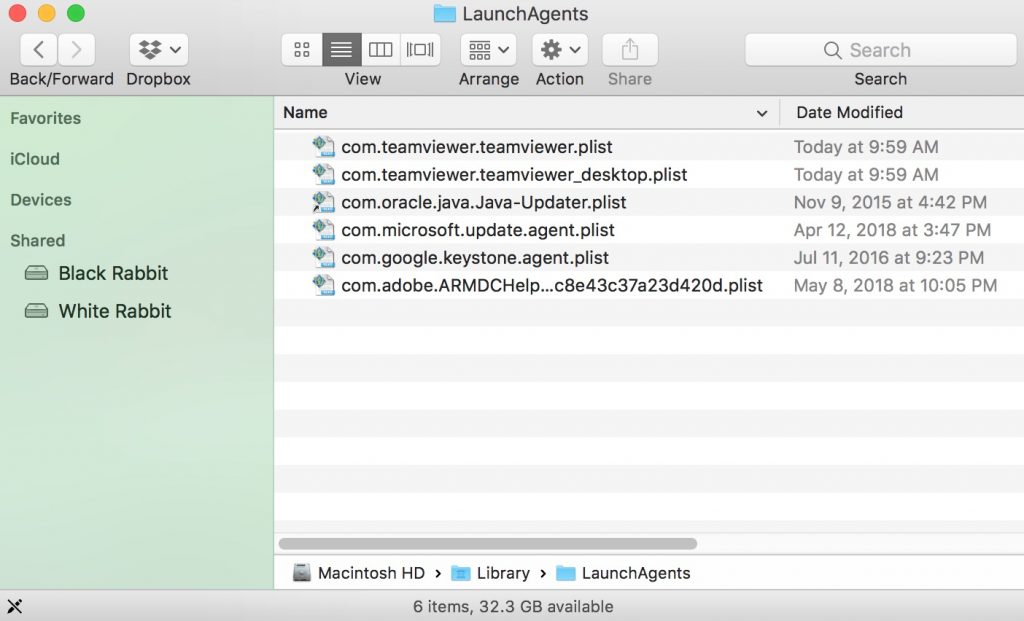
Vous pouvez répéter la même procédure avec les autres Bibliothèque répertoires:
→ ~ / Library / LaunchAgents
/Bibliothèque / LaunchDaemons
Pointe: ~ est-il sur le but, car elle conduit à plus LaunchAgents.
Étape 2: Scan for and remove BestBuy Virus files from your Mac
Lorsque vous faites face à des problèmes sur votre Mac en raison de scripts et de programmes indésirables tels que les virus BestBuy, la méthode recommandée pour éliminer la menace est à l'aide d'un programme anti-malware. SpyHunter pour Mac propose des fonctionnalités de sécurité avancées ainsi que d'autres modules qui amélioreront la sécurité de votre Mac et le protégeront à l'avenir.
Video Removal Guide for BestBuy Virus (Mac)
Supprimer BestBuy Virus de Google Chrome.
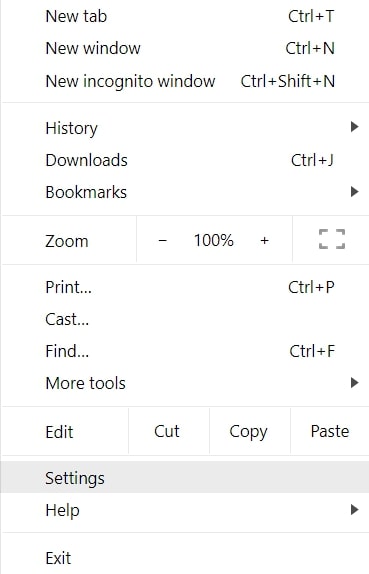
Étape 1: Démarrez Google Chrome et ouvrez le menu déroulant
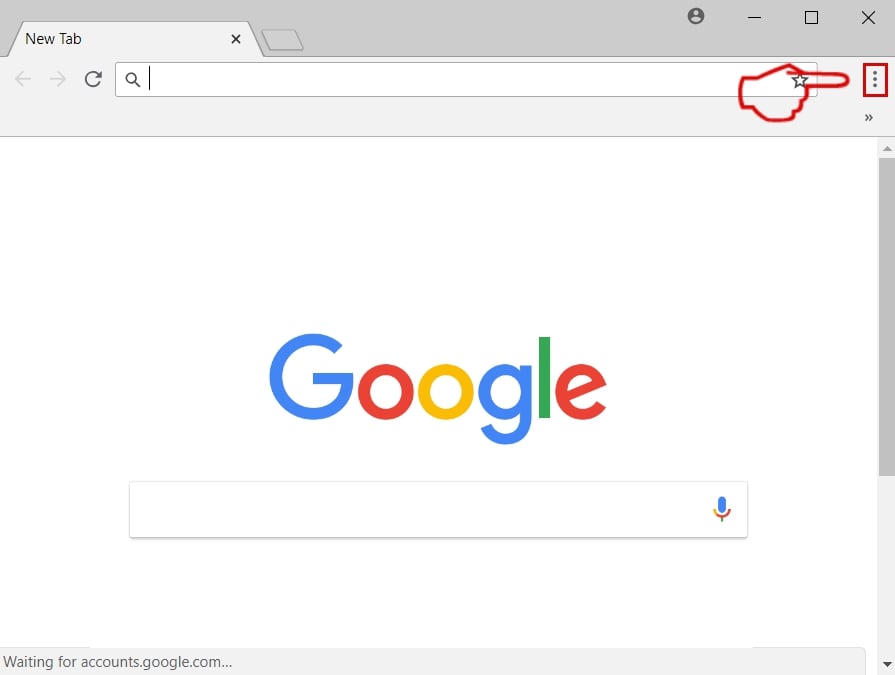
Étape 2: Déplacez le curseur sur "Outils" et puis dans le menu étendu choisir "Extensions"
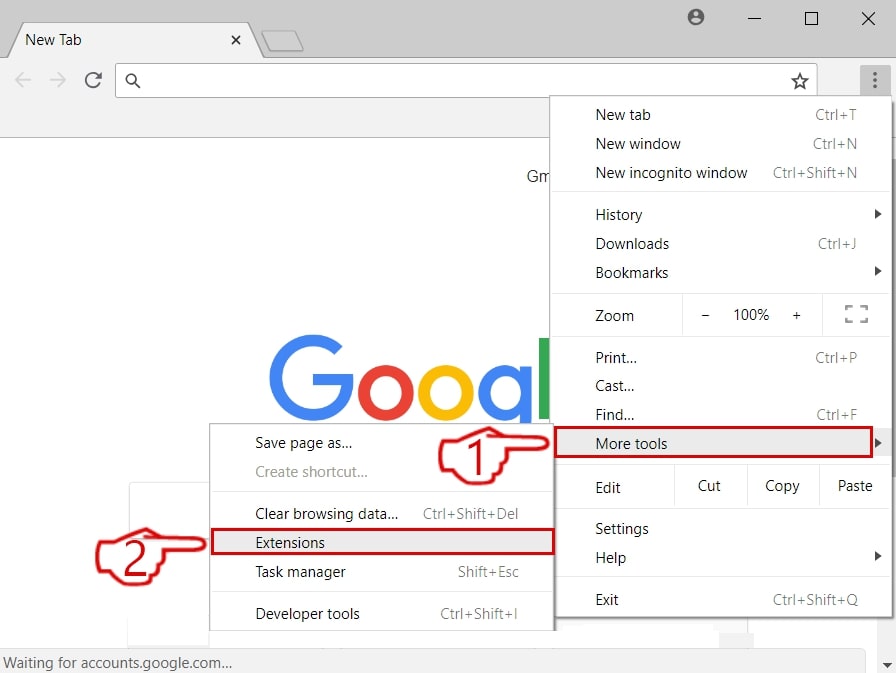
Étape 3: De l'ouverture "Extensions" Menu localiser l'extension indésirable et cliquez sur son "Supprimer" bouton.
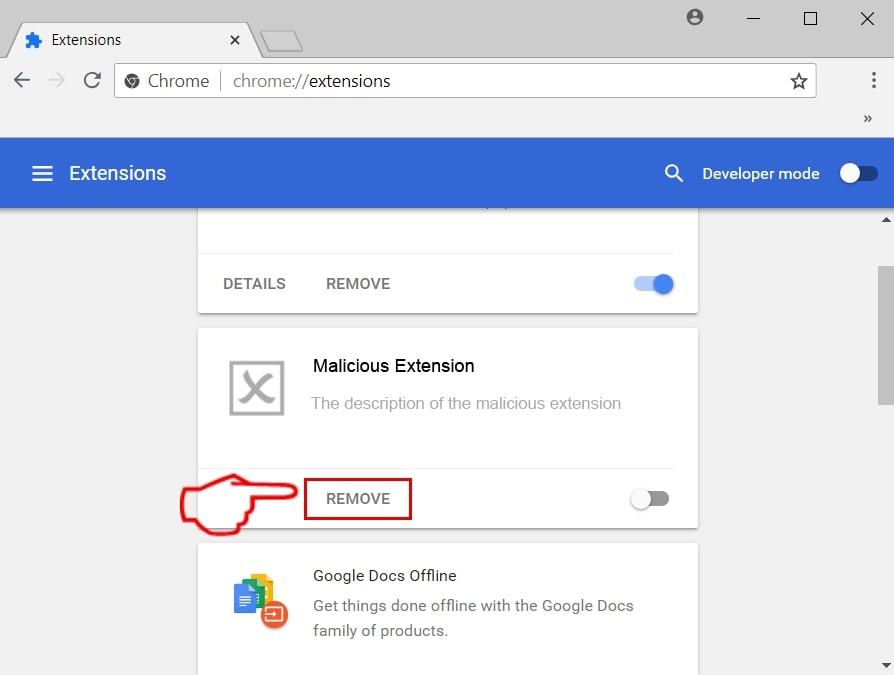
Étape 4: Une fois l'extension retirée, redémarrer Google Chrome en la fermant du rouge "X" bouton dans le coin supérieur droit et commencer à nouveau.
Effacer BestBuy Virus de Mozilla Firefox.
Étape 1: Lancer Mozilla Firefox. Ouvrez la fenêtre de menu:
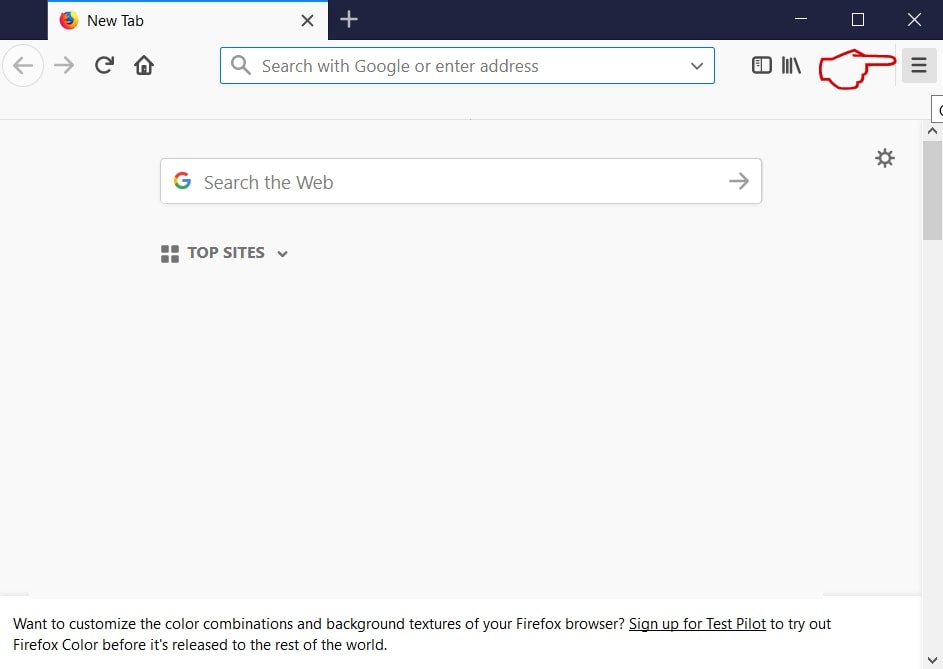
Étape 2: Sélectionnez le "Add-ons" icône dans le menu.
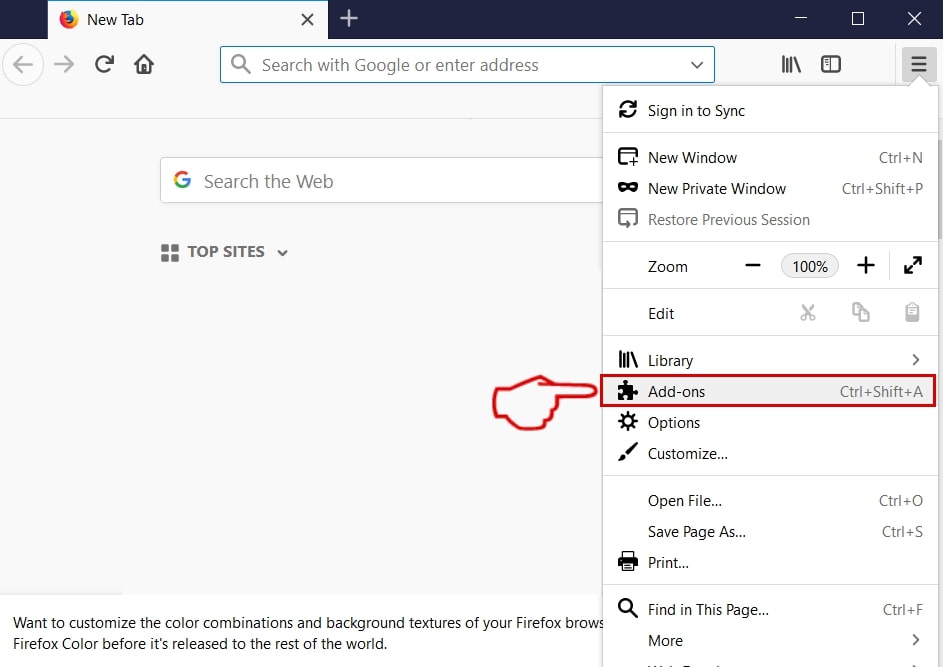
Étape 3: Sélectionnez l'extension indésirable et cliquez sur "Supprimer"

Étape 4: Une fois l'extension retirée, redémarrer Mozilla Firefox par fermeture du rouge "X" bouton dans le coin supérieur droit et commencer à nouveau.
Désinstaller BestBuy Virus de Microsoft Edge.
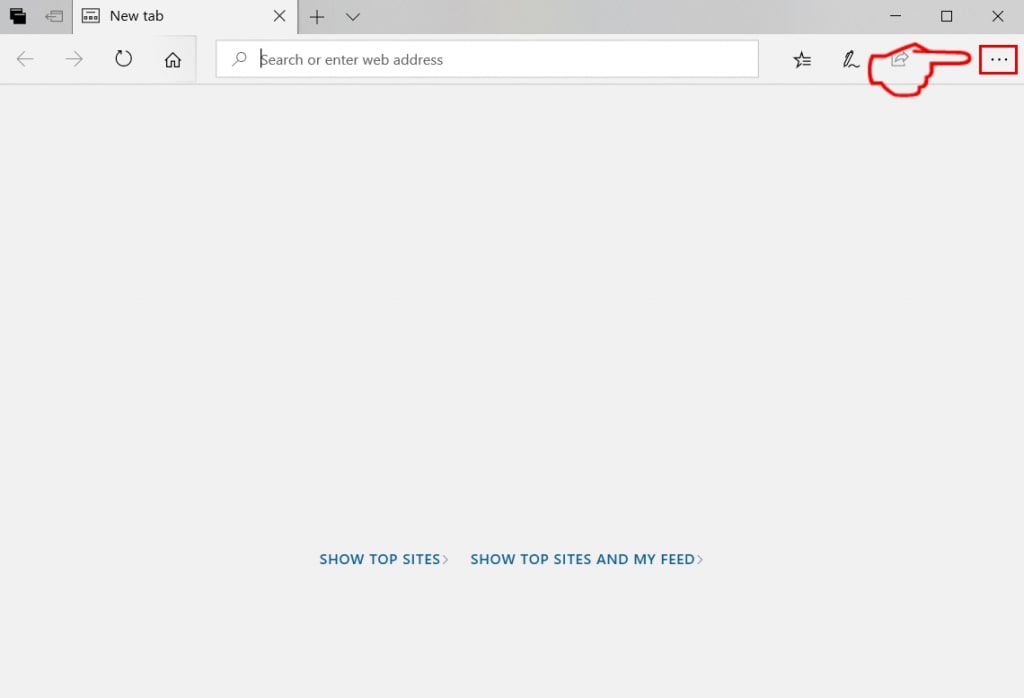
Étape 1: Démarrer le navigateur Edge.
Étape 2: Ouvrez le menu déroulant en cliquant sur l'icône en haut à droite.
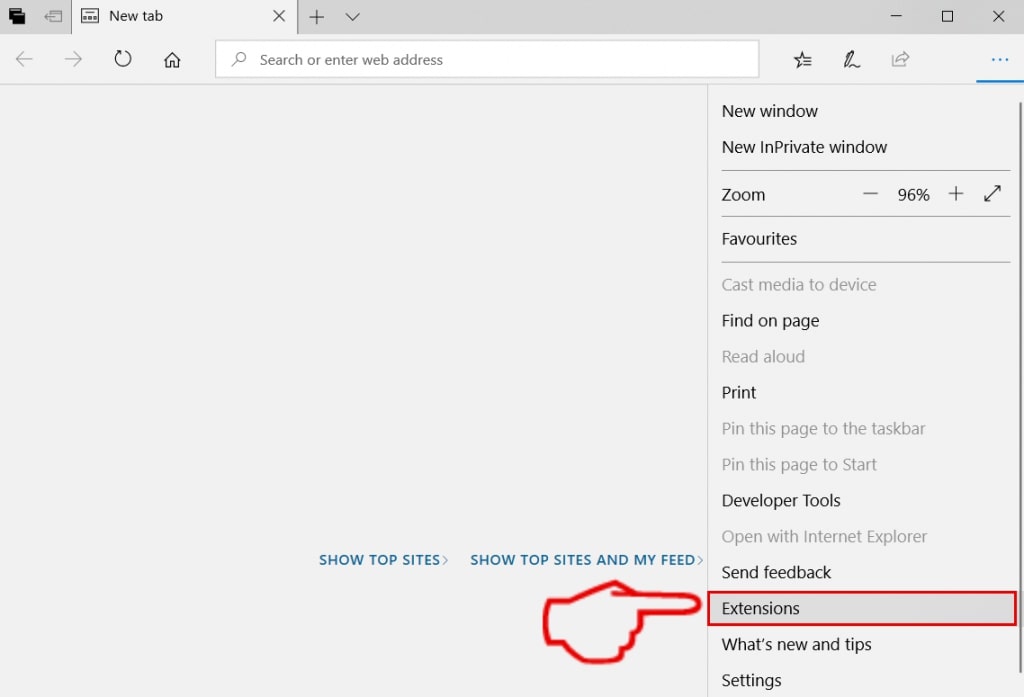
Étape 3: Dans le menu de liste déroulante, sélectionnez "Extensions".
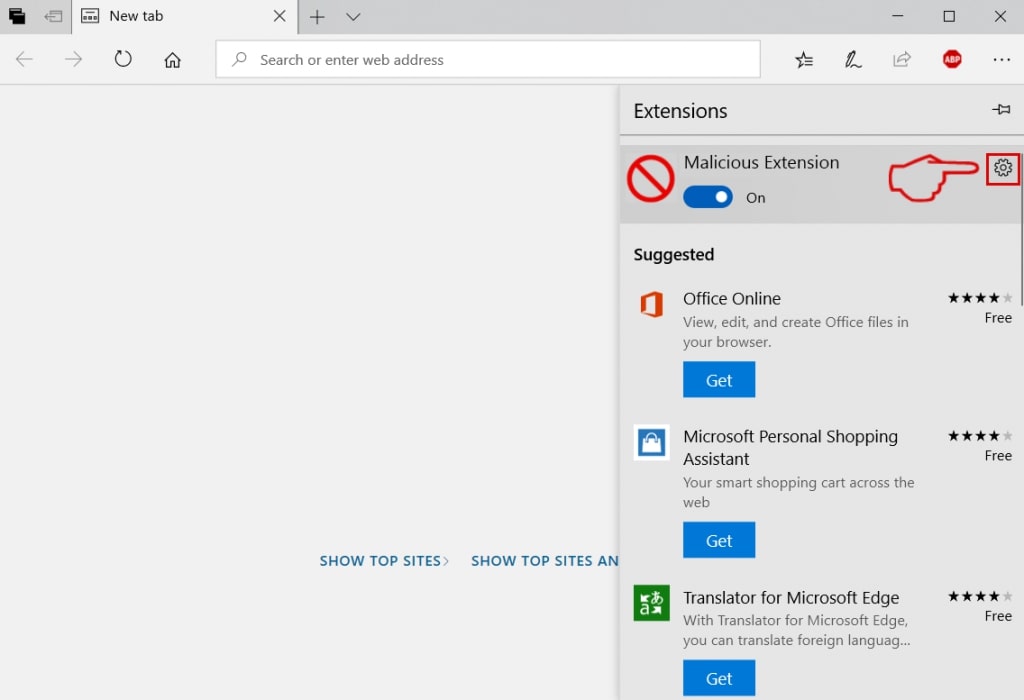
Étape 4: Choisissez l'extension suspecte que vous souhaitez supprimer, puis cliquez sur l'icône d'engrenage.
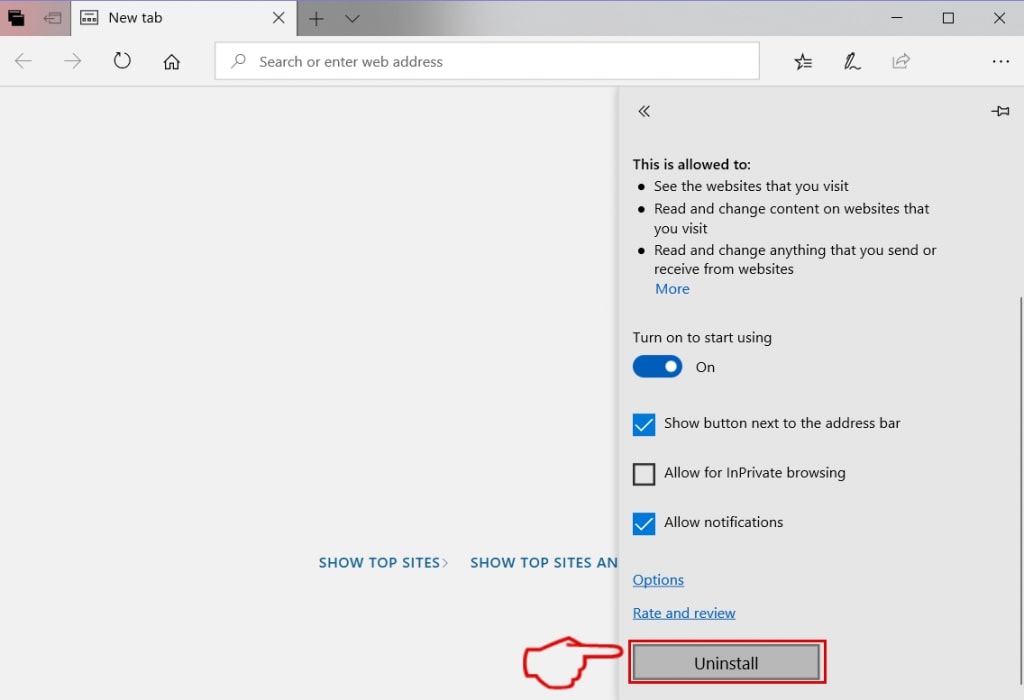
Étape 5: Supprimez l'extension malveillante en faisant défiler vers le bas puis en cliquant sur Désinstaller.
Supprimer BestBuy Virus de Safari
Étape 1: Démarrez l'application Safari.
Étape 2: Après avoir plané le curseur de la souris vers le haut de l'écran, cliquez sur le texte Safari pour ouvrir son menu déroulant.
Étape 3: Dans le menu, cliquer sur "Préférences".
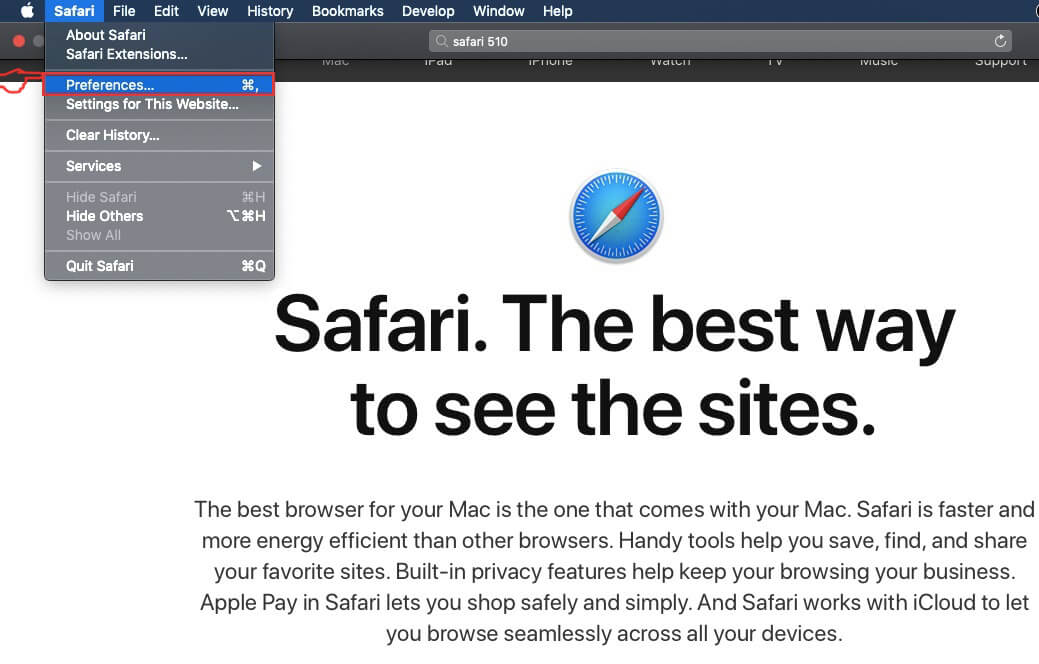
Étape 4: Après cela, Sélectionnez l'onglet Extensions.
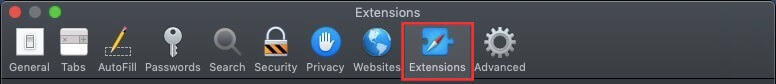
Étape 5: Cliquez une fois sur l'extension que vous souhaitez supprimer.
Étape 6: Cliquez sur 'Désinstaller'.
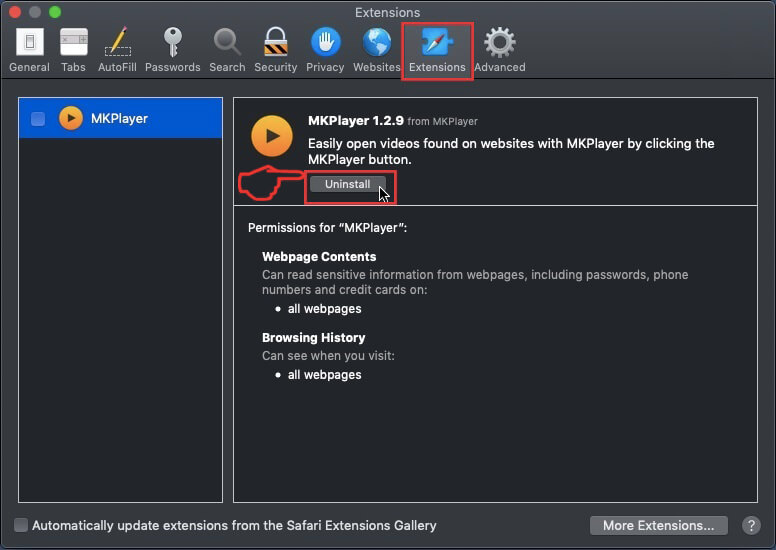
Une fenêtre pop-up apparaîtra vous demandant de confirmer désinstaller l'extension. Sélectionner «Désinstaller» encore, et le virus BestBuy sera supprimé.
Éliminer BestBuy Virus d'Internet Explorer.
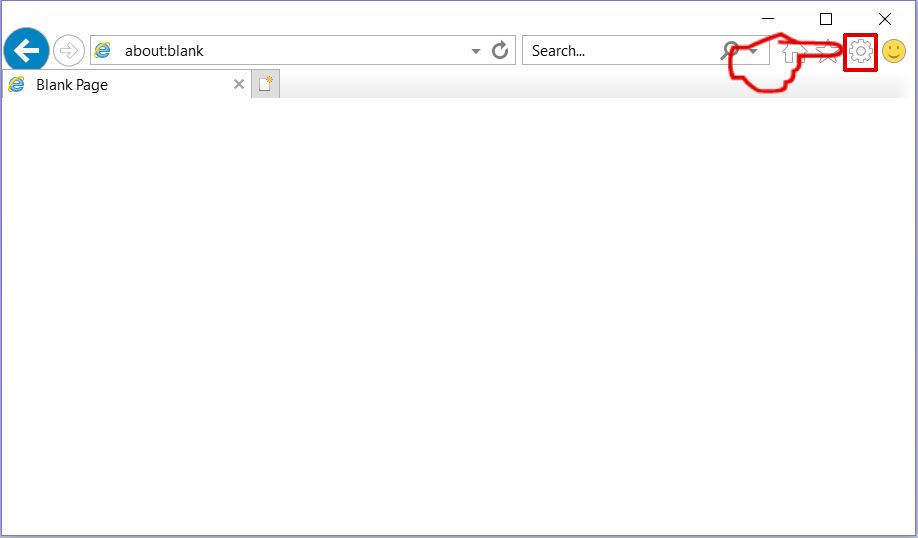
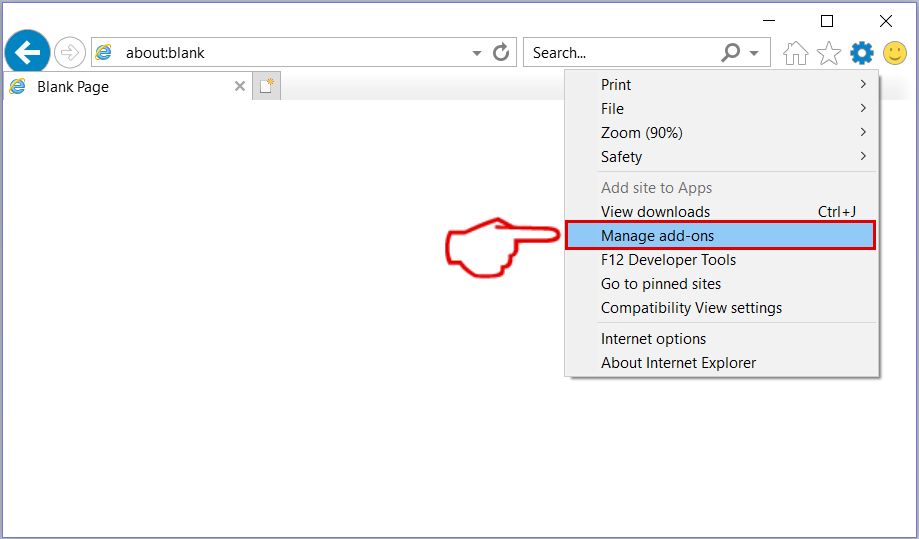
Étape 1: Démarrez Internet Explorer.
Étape 2: Cliquez sur l'icône d'engrenage intitulée « Outils » pour ouvrir le menu déroulant et sélectionnez « Gérer les modules complémentaires »
Étape 3: Dans la fenêtre « Gérer les modules complémentaires ».
Étape 4: Sélectionnez l'extension que vous souhaitez supprimer, puis cliquez sur « Désactiver ». Une fenêtre pop-up apparaîtra pour vous informer que vous êtes sur le point de désactiver l'extension sélectionnée, et quelques autres add-ons peuvent être désactivées et. Laissez toutes les cases cochées, et cliquez sur 'Désactiver'.
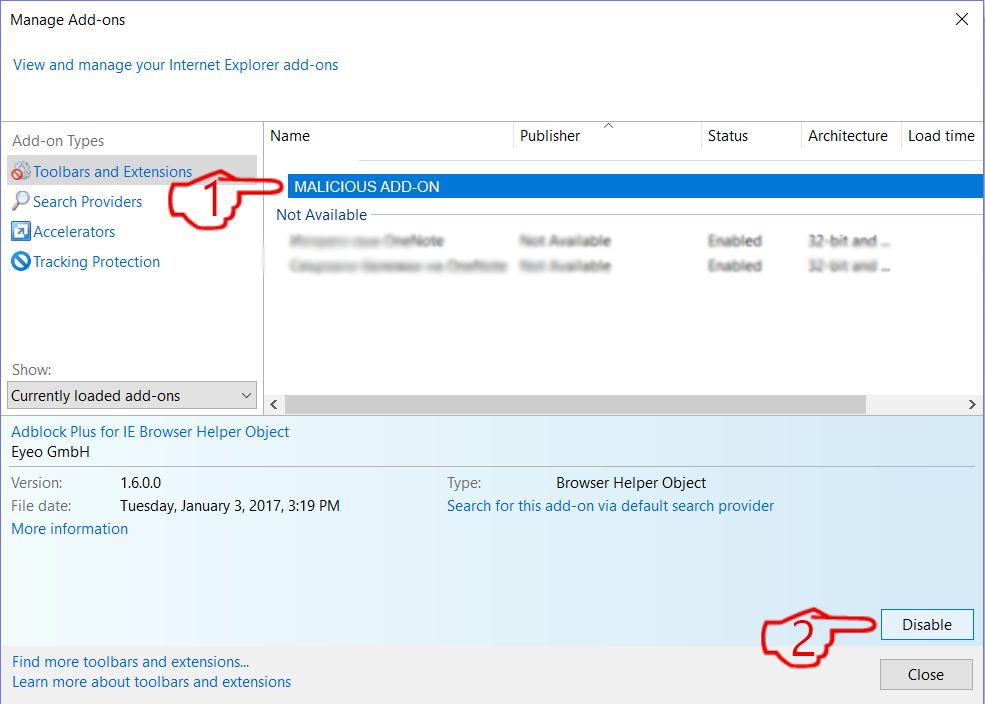
Étape 5: Après l'extension indésirable a été supprimé, redémarrez Internet Explorer en le fermant à partir du bouton rouge 'X' situé dans le coin supérieur droit et redémarrez-le.
Supprimez les notifications push de vos navigateurs
Désactiver les notifications push de Google Chrome
Pour désactiver les notifications push du navigateur Google Chrome, s'il vous plaît suivez les étapes ci-dessous:
Étape 1: Aller à Paramètres dans Chrome.
Étape 2: Dans les paramètres, sélectionnez «Réglages avancés":
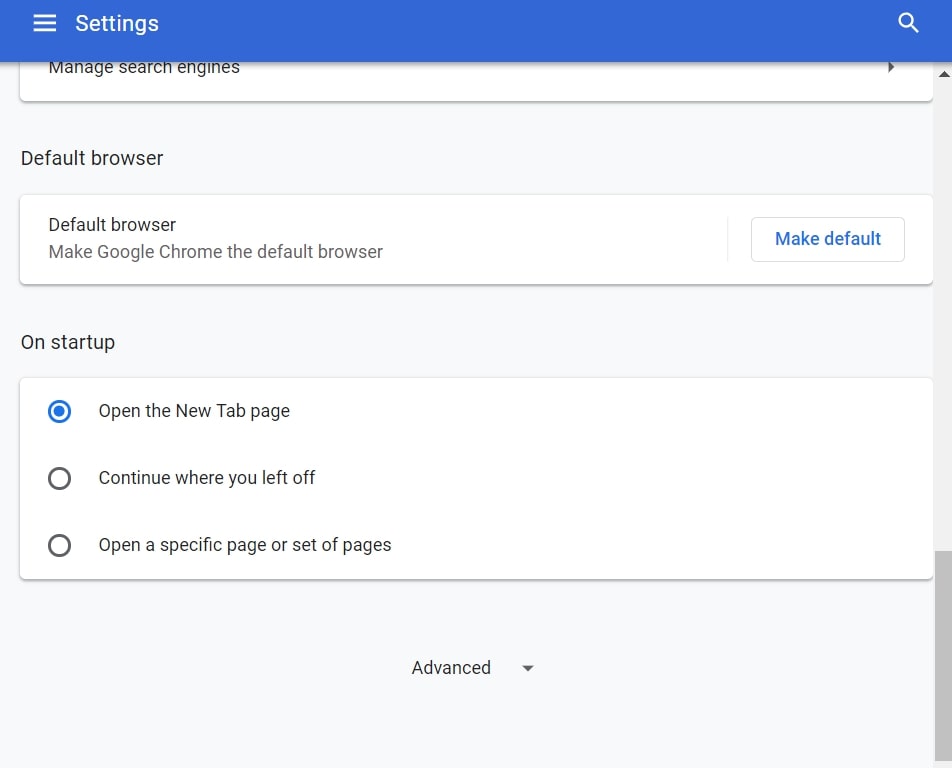
Étape 3: Cliquez sur "Paramètres de contenu":
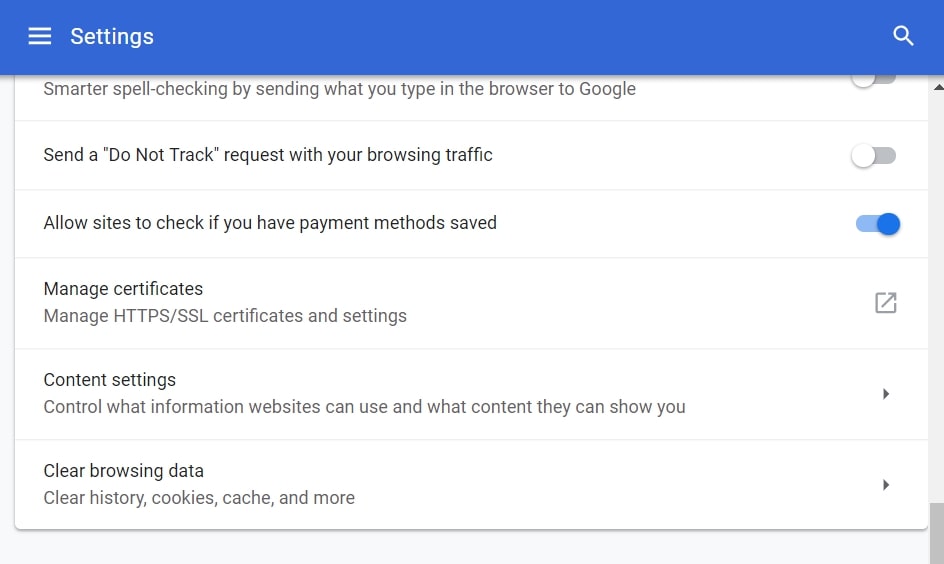
Étape 4: Ouvert "notifications":
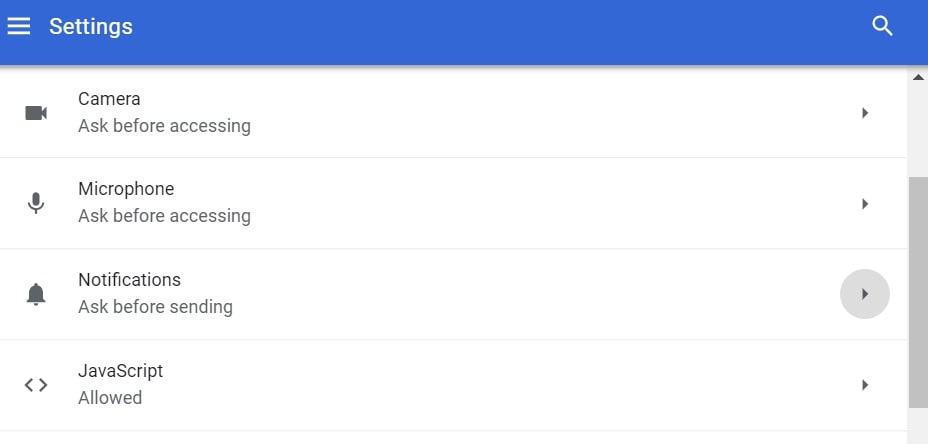
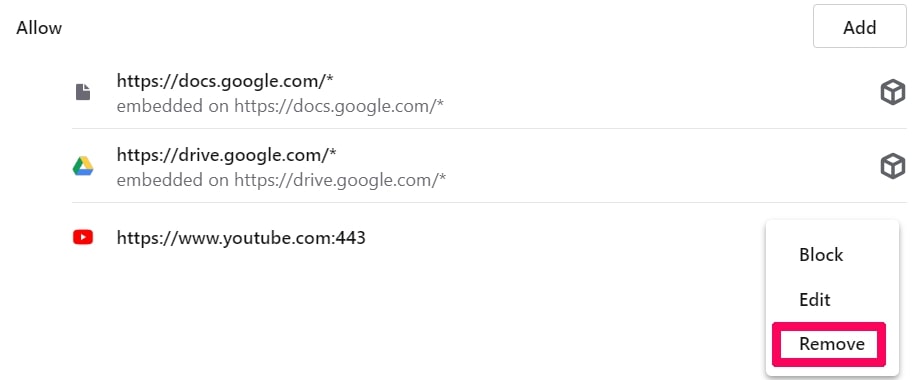
Étape 5: Cliquez sur les trois points et choisissez Bloquer, Modifier ou supprimer des options:

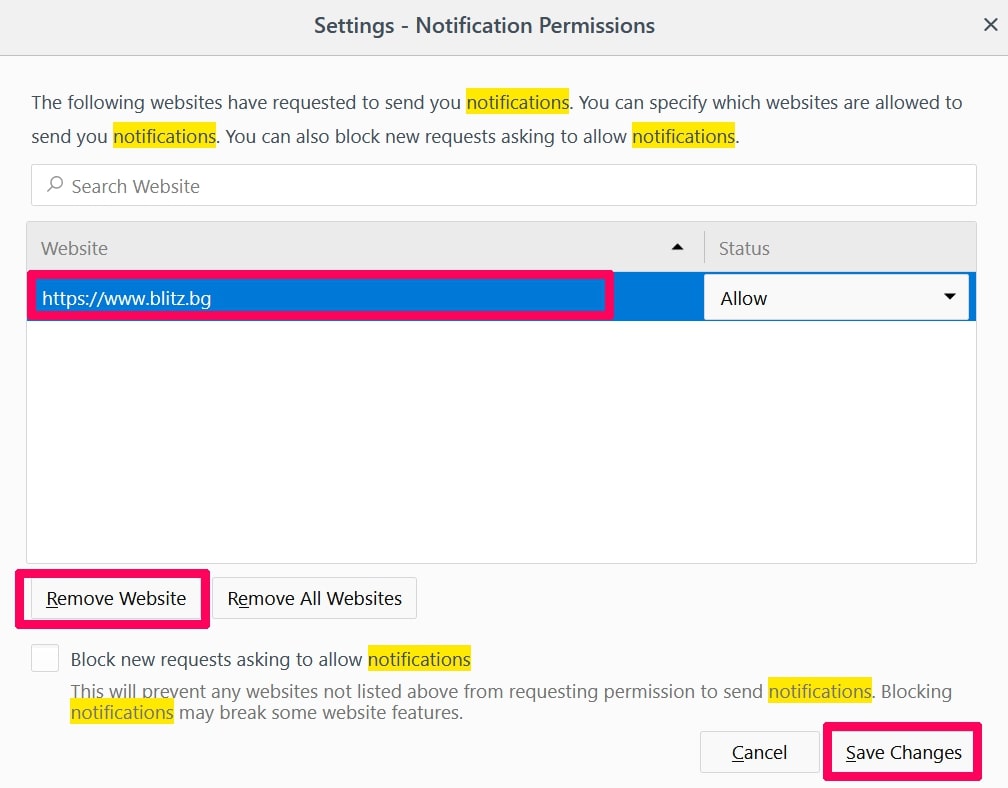
Supprimer les notifications push sur Firefox
Étape 1: Accédez aux options de Firefox.
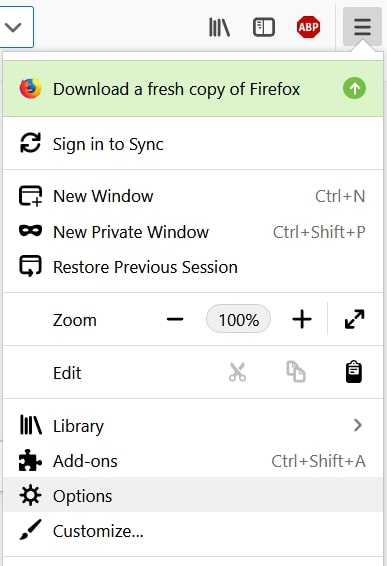
Étape 2: Aller aux paramètres", saisissez "notifications" dans la barre de recherche et cliquez sur "Paramètres":
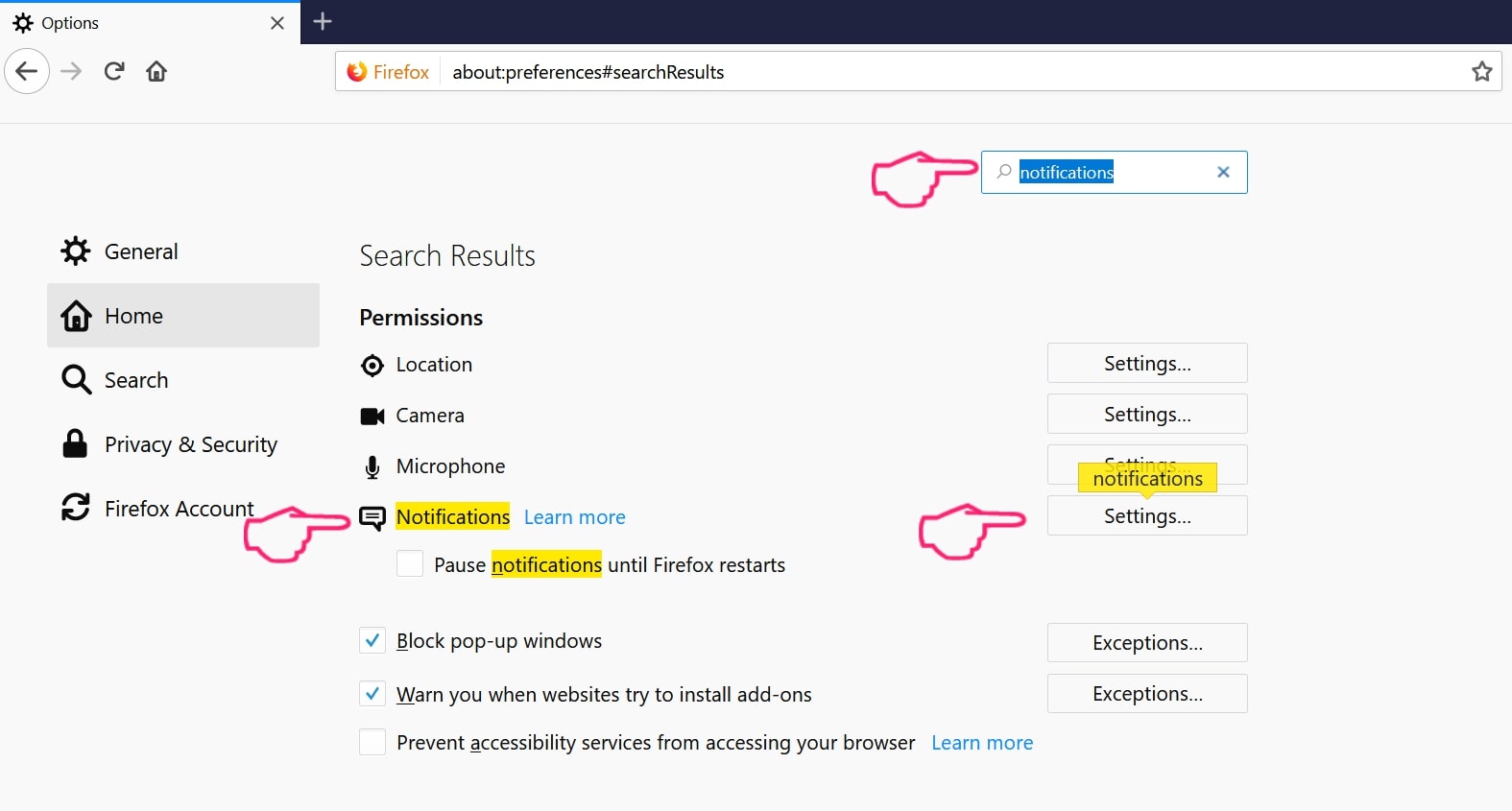
Étape 3: Cliquez sur "Supprimer" sur n'importe quel site pour lequel vous souhaitez que les notifications disparaissent et cliquez sur "Enregistrer les modifications"
Arrêter les notifications push sur Opera
Étape 1: À l'opéra, presse ALT + P pour aller dans les paramètres.
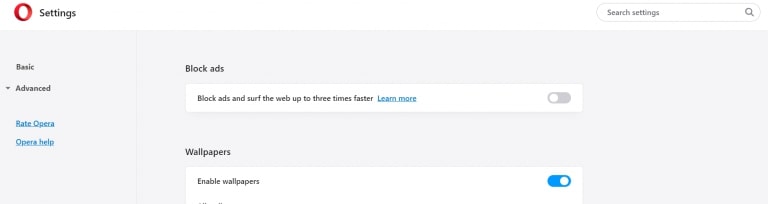
Étape 2: Dans la recherche de paramètres, tapez "Contenu" pour accéder aux paramètres de contenu.
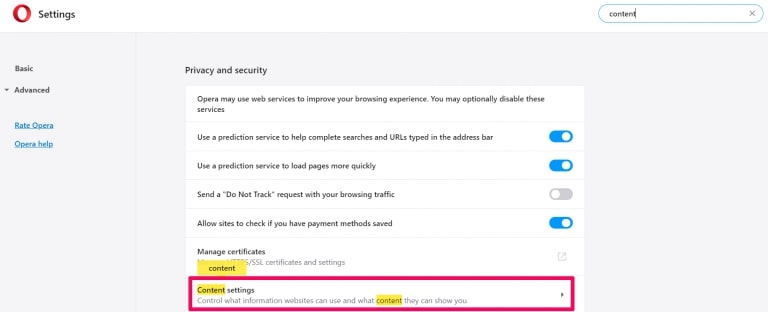
Étape 3: Notifications ouvertes:
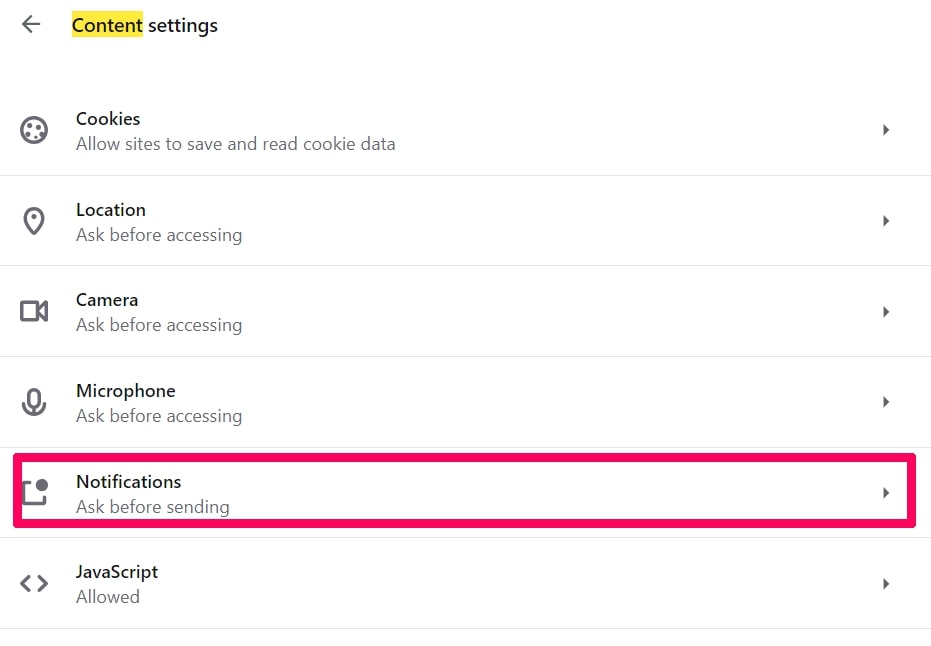
Étape 4: Faites la même chose que vous avez fait avec Google Chrome (expliqué ci-dessous):
Éliminez les notifications push sur Safari
Étape 1: Ouvrez les préférences Safari.
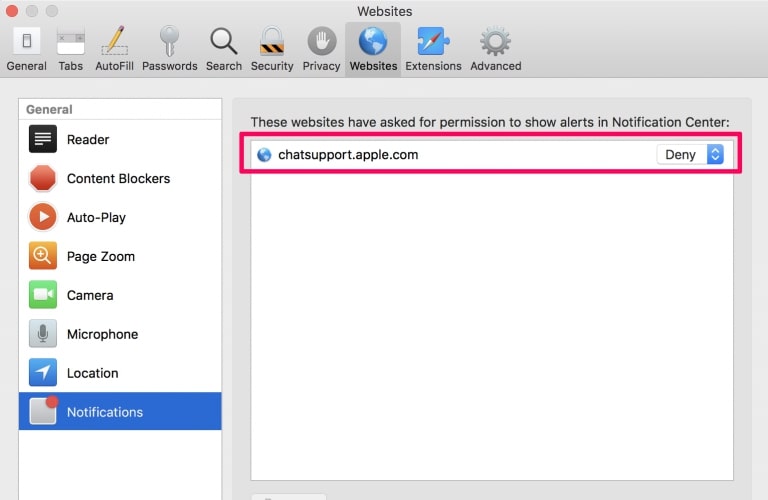
Étape 2: Choisissez le domaine à partir duquel vous souhaitez que les pop-ups push disparaissent et passez à "Refuser" de "Permettre".
BestBuy Virus-FAQ
What Is BestBuy Virus?
The BestBuy Virus threat is adware or navigateur virus de redirection.
Cela peut ralentir considérablement votre ordinateur et afficher des publicités. L'idée principale est que vos informations soient probablement volées ou que davantage d'annonces apparaissent sur votre appareil.
Les créateurs de ces applications indésirables travaillent avec des systèmes de paiement au clic pour amener votre ordinateur à visiter des sites Web risqués ou différents types de sites Web susceptibles de générer des fonds.. C'est pourquoi ils ne se soucient même pas des types de sites Web qui apparaissent sur les annonces.. Cela rend leurs logiciels indésirables indirectement risqués pour votre système d'exploitation.
What Are the Symptoms of BestBuy Virus?
Il y a plusieurs symptômes à rechercher lorsque cette menace particulière et les applications indésirables en général sont actives:
Symptôme #1: Votre ordinateur peut devenir lent et avoir des performances médiocres en général.
Symptôme #2: Vous avez des barres d'outils, des modules complémentaires ou des extensions sur vos navigateurs Web que vous ne vous souvenez pas avoir ajoutés.
Symptôme #3: Vous voyez tous les types d'annonces, comme les résultats de recherche financés par la publicité, pop-ups et redirections pour apparaître au hasard.
Symptôme #4: Vous voyez les applications installées sur votre Mac s'exécuter automatiquement et vous ne vous souvenez pas de les avoir installées.
Symptôme #5: Vous voyez des processus suspects en cours d'exécution dans votre gestionnaire de tâches.
Si vous voyez un ou plusieurs de ces symptômes, alors les experts en sécurité vous recommandent de vérifier la présence de virus sur votre ordinateur.
Quels types de programmes indésirables existe-t-il?
Selon la plupart des chercheurs en malwares et experts en cybersécurité, les menaces qui peuvent actuellement affecter votre appareil peuvent être logiciel antivirus malveillant, adware, les pirates de navigateur, cliqueurs, faux optimiseurs et toutes formes de PUP.
Que faire si j'ai un "virus" like BestBuy Virus?
Avec quelques actions simples. Tout d'abord, il est impératif que vous suiviez ces étapes:
Étape 1: Trouvez un ordinateur sûr et connectez-le à un autre réseau, pas celui dans lequel votre Mac a été infecté.
Étape 2: Changer tous vos mots de passe, à partir de vos mots de passe de messagerie.
Étape 3: Activer authentification à deux facteurs pour la protection de vos comptes importants.
Étape 4: Appelez votre banque au modifier les détails de votre carte de crédit (code secret, etc) si vous avez enregistré votre carte de crédit pour faire des achats en ligne ou avez effectué des activités en ligne avec votre carte.
Étape 5: Assurez-vous de appelez votre FAI (Fournisseur Internet ou opérateur) et demandez-leur de changer votre adresse IP.
Étape 6: Change ton Mot de passe WiFi.
Étape 7: (En option): Assurez-vous de rechercher les virus sur tous les appareils connectés à votre réseau et répétez ces étapes pour eux s'ils sont affectés.
Étape 8: Installer un anti-malware logiciel avec protection en temps réel sur chaque appareil que vous possédez.
Étape 9: Essayez de ne pas télécharger de logiciels à partir de sites dont vous ne savez rien et restez à l'écart sites Web à faible réputation en général.
Si vous suivez ces recommandations, votre réseau et tous les appareils deviendront beaucoup plus sécurisés contre les menaces ou les logiciels invasifs et seront également exempts de virus et protégés à l'avenir.
How Does BestBuy Virus Work?
Une fois installé, BestBuy Virus can collecter des données en utilisant traqueurs. Ces données concernent vos habitudes de navigation sur le Web, tels que les sites Web que vous visitez et les termes de recherche que vous utilisez. Elles sont ensuite utilisées pour vous cibler avec des publicités ou pour vendre vos informations à des tiers..
BestBuy Virus can also télécharger d'autres logiciels malveillants sur votre ordinateur, tels que les virus et les logiciels espions, qui peut être utilisé pour voler vos informations personnelles et diffuser des publicités à risque, qui peut rediriger vers des sites de virus ou des escroqueries.
Is BestBuy Virus Malware?
La vérité est que les PUP (adware, les pirates de navigateur) ne sont pas des virus, mais peut être tout aussi dangereux car ils peuvent vous montrer et vous rediriger vers des sites Web malveillants et des pages frauduleuses.
De nombreux experts en sécurité classent les programmes potentiellement indésirables comme des logiciels malveillants. Cela est dû aux effets indésirables que les PUP peuvent causer, telles que l'affichage de publicités intrusives et la collecte de données utilisateur à l'insu de l'utilisateur ou sans son consentement.
About the BestBuy Virus Research
Le contenu que nous publions sur SensorsTechForum.com, this BestBuy Virus how-to removal guide included, est le résultat de recherches approfondies, le travail acharné et le dévouement de notre équipe pour vous aider à éliminer les, problème lié aux logiciels publicitaires, et restaurez votre navigateur et votre système informatique.
How did we conduct the research on BestBuy Virus?
Veuillez noter que notre recherche est basée sur une enquête indépendante. Nous sommes en contact avec des chercheurs indépendants en sécurité, grâce auquel nous recevons des mises à jour quotidiennes sur les derniers malwares, adware, et définitions des pirates de navigateur.
En outre, the research behind the BestBuy Virus threat is backed with VirusTotal.
Pour mieux comprendre cette menace en ligne, veuillez vous référer aux articles suivants qui fournissent des détails bien informés.


