 Wat is de Varensky virus? Hoe het verwijderen Varensky bedreiging? hoe werkt Varensky Virus werk? Hoe te verwijderen Varensky virus vanaf uw computer?
Wat is de Varensky virus? Hoe het verwijderen Varensky bedreiging? hoe werkt Varensky Virus werk? Hoe te verwijderen Varensky virus vanaf uw computer?
Het Varensky virus is het type malware, waarvan het belangrijkste idee is om je af te persen. Deze vorm van "Doxware" heeft tot doel de eerste informatie te verzamelen voor uw computersysteem en netwerk en vervolgens te infecteren met u opnemen via kwaadaardige e-mail spam. Dan, de Varensky dreiging advertenties allerlei virus modules, waarvan het belangrijkste idee is om bespioneren, meer in het bijzonder in staat stellen uw camera en microfoon. Als je toevallig om te geloven dat u besmet door de Varensky virus, Wij raden u aan dit artikel te lezen, want het bevat meer informatie over plus hoe u uit uw machine te halen.

bedreiging Samenvatting
| Naam | Varensky Virus |
| Type | Trojan / spyware |
| Korte Omschrijving | Glijdt op uw computer stil en registreert u tijdens het kijken naar video's voor volwassenen om u online af te persen. |
| Symptomen | Geen actieve symptomen naast het virus als gedetecteerd. |
| Distributie Methode | Gebundeld downloads. Webpagina's die zij kunnen adverteren. |
| Detection Tool |
Zien of je systeem is getroffen door malware
Download
Malware Removal Tool
|
Gebruikerservaring | Word lid van onze Forum om Varensky Virus Bespreek. |

Varensky Virus – How Did I Get It en wat doet het?
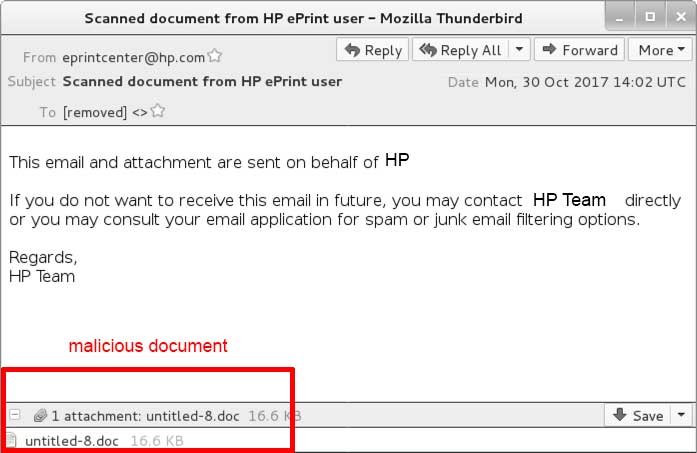
Het Varensky Virus is gericht op computers te infecteren met behulp van een spam bot. Dergelijke spam bots in staat zijn het verzenden van ongeveer 1500 geautomatiseerde e-mails per dag. Deze e-mails hebben de neiging om verschillende soorten e-mail bijlagen bevatten, die zich voordeed als documenten. De e-mails vaak verschijnen overtuigend, zoals in het voorbeeld hieronder shows:
Zodra u bent misleid in het openen van de nep-document gehecht aan de e-mail, infectie met Varensky Virus Is dreigende.
Als je besmet met de Varensky virus, kan het beginnen met de volgende informatie van uw computer verzamelen:
- Systeem informatie.
- antivirusprogramma's geïnstalleerd.
- IP- en MAC-adres.
- Locatie en taal gegevens.
- Windows-versie.
Zodra dit gebeurt, de Varensky virus kunnen beginnen om de volgende virus activiteiten op uw computer uit te voeren:
- Maak mutexes.
- Het verkrijgen van beheerdersrechten.
- Log de toetsaanslagen u typt om uw wachtwoorden te zien.
- Installeer andere viruscomponenten.
- Maak gebruik van uw microfoon en camera om u op te nemen.
Het Varensky Virus heeft een module die automatisch kan activeren wanneer u een volwassen site te bezoeken en deze informatie gebruiken om u af te persen. De cyber-criminelen kunt u opnemen op uw camera en gebruik dan screenshots van je om te laten zien dat ze geen grap. In ruil, ze willen dat je om losgeld te betalen en anders worden ze dreigen om je privé video's of foto's lekken naar openbare forums en andere sites. Het virus werd voor het eerst gespot in Frankrijk, maar rapporten geven aan dat het snel op grote schaal kan worden om een wereldwijde schaal. Gebruikers wordt geadviseerd om niet te voldoen aan de cyber-criminelen en altijd bedekken hun camera's en als je ziet dit virus, moet u onmiddellijk verwijderen.

Hoe te verwijderen Varensky Virus
In staat zijn om dit virus te verwijderen, je nodig hebt om de componenten ervan te identificeren. Je kunt ze herkennen door het zien van verdachte .exe en andere processen runing op de achtergrond. eenmaal gevonden, kunt u deze componenten uit Windows Taakbeheer uitschakelen. De onderstaande instructies hebben stap-voor-stap handleiding over hoe u handmatig detecteren en verwijderen van de Varensky virus van uw machine. Als u echter niet het virus bestanden van Varensky malware kan vinden, dan raden we u aan een professionele het verwijderen van spyware software die automatisch detecteert en verwijdert alle sporen van Varensky Virus voor u en u te beschermen tegen toekomstige infecties van alle soorten.
Voorbereiding voor het verwijderen van het Varensky-virus.
Voor het eigenlijke verwijdering, Wij raden u aan de volgende voorbereidende stappen te doen.
- Zorg ervoor dat u deze instructies altijd open en in de voorkant van je ogen.
- Doe een back-up van al uw bestanden, zelfs als ze konden worden beschadigd. U moet een back-up van uw gegevens met een cloud backup oplossing en verzekeren van uw bestanden tegen elke vorm van verlies, zelfs van de meest ernstige bedreigingen.
- Wees geduldig als deze een tijdje zou kunnen nemen.
- Scannen op malware
- Registers repareren
- Verwijder virusbestanden
Stap 1: Scan op Varensky Virus met SpyHunter Anti-Malware Tool



Stap 2: Verwijder eventuele registers, gemaakt door Varensky Virus op uw computer.
De doorgaans gericht registers van Windows-machines zijn de volgende:
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion Run
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion Run
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion RunOnce
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion RunOnce
U kunt ze openen door het openen van het Windows-register-editor en met weglating van alle waarden, gemaakt door Varensky Virus daar. Dit kan gebeuren door de stappen onder:


 Tip: Om een virus gecreëerd waarde te vinden, U kunt met de rechtermuisknop op te klikken en klik op "Wijzigen" om te zien welk bestand het is ingesteld om te werken. Als dit het virus bestand locatie, Verwijder de waarde.
Tip: Om een virus gecreëerd waarde te vinden, U kunt met de rechtermuisknop op te klikken en klik op "Wijzigen" om te zien welk bestand het is ingesteld om te werken. Als dit het virus bestand locatie, Verwijder de waarde.Stap 3: Find virus files created by Varensky Virus on your PC.
1.Voor Windows 8, 8.1 en 10.
Voor nieuwere Windows-besturingssystemen
1: Op het toetsenbord druk + R en schrijf explorer.exe in de Rennen tekstvak en klik dan op de OK knop.

2: Klik op uw pc uit de snelle toegang bar. Dit is meestal een icoon met een monitor en de naam is ofwel "Mijn computer", "My PC" of "Deze PC" of hoe je het hebt genoemd.

3: Navigeer naar het zoekvak in de rechterbovenhoek van het scherm van uw pc en typ "echter in meerdere contexten:" en waarna typt u de bestandsextensie. Als u op zoek bent naar kwaadaardige executables, Een voorbeeld kan zijn "echter in meerdere contexten:exe". Na het doen van dat, laat een spatie en typ de bestandsnaam die u denkt dat de malware is gemaakt. Hier is hoe het kan verschijnen als het bestand is gevonden:

NB. We recommend to wait for the green loading bar in the navigation box to fill up in case the PC is looking for the file and hasn't found it yet.
2.Voor Windows XP, Uitzicht, en 7.
Voor oudere Windows-besturingssystemen
In oudere Windows-besturingssystemen zou de conventionele aanpak de effectieve moeten zijn:
1: Klik op de Start Menu icoon (meestal op uw bottom-links) en kies vervolgens de Zoeken voorkeur.

2: Na het zoekvenster verschijnt, kiezen Meer geavanceerde opties van de search assistent doos. Een andere manier is door te klikken op Alle bestanden en mappen.

3: Na dat type de naam van het bestand dat u zoekt en klik op de knop Zoeken. Dit kan enige tijd duren, waarna de resultaten worden weergegeven. Als u het kwaadaardig bestand hebt gevonden, u kunt kopiëren of openen de locatie door rechtermuisknop te klikken ben ermee bezig.
Nu moet je in staat om elk bestand op Windows ontdekken zolang het op uw harde schijf en is niet verborgen via speciale software.
Varensky Virus FAQ
What Does Varensky Virus Trojan Do?
The Varensky Virus Trojaans is een kwaadaardig computerprogramma ontworpen om te ontwrichten, schade, of ongeautoriseerde toegang verkrijgen naar een computersysteem. Het kan worden gebruikt om gevoelige gegevens te stelen, controle krijgen over een systeem, of andere kwaadaardige activiteiten starten.
Kunnen Trojaanse paarden wachtwoorden stelen??
Ja, Trojans, like Varensky Virus, kan wachtwoorden stelen. Deze kwaadaardige programma's are designed to gain access to a user's computer, slachtoffers bespioneren en gevoelige informatie zoals bankgegevens en wachtwoorden stelen.
Can Varensky Virus Trojan Hide Itself?
Ja, het kan. Een Trojaans paard kan verschillende technieken gebruiken om zichzelf te maskeren, inclusief rootkits, encryptie, en verduistering, om zich te verbergen voor beveiligingsscanners en detectie te omzeilen.
Kan een Trojaans paard worden verwijderd door Factory Reset?
Ja, een Trojaans paard kan worden verwijderd door uw apparaat terug te zetten naar de fabrieksinstellingen. Dit komt omdat het het apparaat in de oorspronkelijke staat zal herstellen, het verwijderen van schadelijke software die mogelijk is geïnstalleerd. Houd er rekening mee dat er geavanceerdere Trojans zijn die achterdeurtjes achterlaten en opnieuw infecteren, zelfs na een fabrieksreset.
Can Varensky Virus Trojan Infect WiFi?
Ja, het is mogelijk dat een trojan wifi-netwerken infecteert. Wanneer een gebruiker verbinding maakt met het geïnfecteerde netwerk, de Trojan kan zich verspreiden naar andere aangesloten apparaten en kan toegang krijgen tot gevoelige informatie op het netwerk.
Kunnen Trojaanse paarden worden verwijderd?
Ja, Trojaanse paarden kunnen worden verwijderd. Dit wordt meestal gedaan door een krachtig antivirus- of antimalwareprogramma uit te voeren dat is ontworpen om schadelijke bestanden te detecteren en te verwijderen. In sommige gevallen, handmatige verwijdering van de Trojan kan ook nodig zijn.
Kunnen Trojaanse paarden bestanden stelen?
Ja, Trojaanse paarden kunnen bestanden stelen als ze op een computer zijn geïnstalleerd. Dit wordt gedaan door de malware auteur of gebruiker om toegang te krijgen tot de computer en vervolgens de bestanden te stelen die erop zijn opgeslagen.
Welke anti-malware kan Trojaanse paarden verwijderen?
Antimalwareprogramma's zoals SpyHunter zijn in staat om Trojaanse paarden op uw computer te scannen en van uw computer te verwijderen. Het is belangrijk om uw anti-malware up-to-date te houden en uw systeem regelmatig te scannen op schadelijke software.
Kunnen Trojaanse paarden USB infecteren?
Ja, Trojaanse paarden kunnen infecteren USB apparaten. USB-trojans wordt meestal verspreid via schadelijke bestanden die van internet zijn gedownload of via e-mail zijn gedeeld, allowing the hacker to gain access to a user's confidential data.
About the Varensky Virus Research
De inhoud die we publiceren op SensorsTechForum.com, this Varensky Virus how-to removal guide included, is het resultaat van uitgebreid onderzoek, hard werken en de toewijding van ons team om u te helpen het specifieke trojan-probleem op te lossen.
How did we conduct the research on Varensky Virus?
Houd er rekening mee dat ons onderzoek is gebaseerd op een onafhankelijk onderzoek. We hebben contact met onafhankelijke beveiligingsonderzoekers, waardoor we dagelijks updates ontvangen over de nieuwste malwaredefinities, inclusief de verschillende soorten trojans (achterdeur, downloader, infostealer, losgeld, etc.)
Bovendien, the research behind the Varensky Virus threat is backed with VirusTotal.
Om de dreiging van trojans beter te begrijpen, raadpleeg de volgende artikelen die deskundige details bieden:.