 Was ist der Varensky Virus? So entfernen Sie die Varensky Bedrohung? Wie funktioniert Varensky Virus Arbeit? Wie zu entfernen Varensky Virus von Ihrem Computer?
Was ist der Varensky Virus? So entfernen Sie die Varensky Bedrohung? Wie funktioniert Varensky Virus Arbeit? Wie zu entfernen Varensky Virus von Ihrem Computer?
Die Varensky Virus ist die Art der Malware, deren Hauptidee ist es, Sie zu erpressen. Diese Form der "Doxware" zielt darauf ab, erste Informationen für Ihr Computersystem und Netzwerke zu sammeln und Sie dann über schädlichen E-Mail-Spam infizieren. Dann, die Varensky Bedrohung Anzeigen aller Art Virus-Module, Leitgedanke dessen, um Sie auszuspionieren, insbesondere Ihre Kamera und das Mikrofon ermöglichen. Wenn Sie geschehen, zu glauben, dass Sie von dem Virus infiziert wurden Varensky, Wir empfehlen dringend, dass Sie diesen Artikel zu lesen, da es mehr Informationen darüber enthält plus, wie es von Ihrem Gerät zu entfernen.

Threat Zusammenfassung
| Name | Varensky Virus |
| Art | Trojan / Spyware |
| kurze Beschreibung | Schlittert auf Ihrem Computer still und zeichnet Sie während erwachsene Videos ansehen, um Sie online zu erpressen. |
| Symptome | wenn erkannt keine aktiven Symptome außer dem Virus. |
| Verteilungsmethode | Gebündelte Downloads. Web-Seiten, die sie werben können. |
| Detection Tool |
Überprüfen Sie, ob Ihr System von Malware betroffen ist
Herunterladen
Malware Removal Tool
|
Benutzererfahrung | Abonnieren Sie unseren Forum zu Besprechen Varensky Virus. |

Varensky Virus – Wie habe ich es und was tut sie?
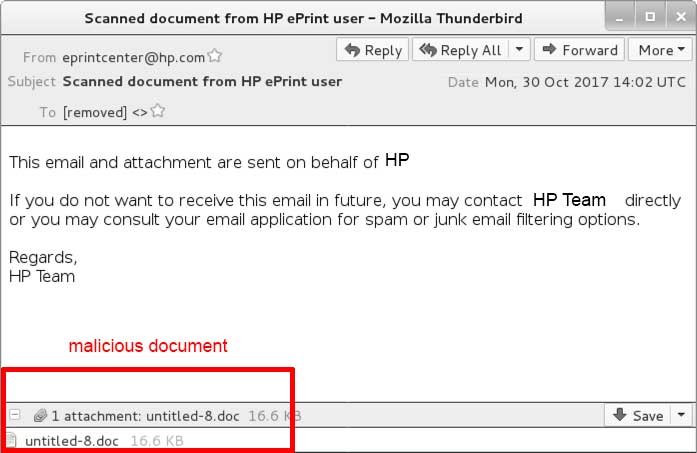
Die Varensky Virus zielt darauf ab, Computer zu infizieren, indem ein Spam-Bot mit. Solche Spam-Bots sind in der Lage zu senden 1500 automatisierte E-Mails pro Tag. Diese E-Mails sind in der Regel verschiedene Arten von E-Mail-Anhänge enthalten, die sich als Dokumente. Die E-Mails erscheinen oft überzeugend, wie das Beispiel unter Shows:
Sobald Sie das gefälschte Dokument zu öffnen an der E-Mail ausgetrickst in sind, Infektion mit Varensky Virus steht unmittelbar bevor.
Wenn Sie infiziert werden, mit der Varensky Virus, es kann beginnen die folgenden Informationen von Ihrem Computer zu sammeln:
- System Information.
- antiviren installiert.
- IP und Mac-Adresse.
- Ort und Sprachdaten.
- Windows-Version.
Sobald dies geschieht, die Varensky Virus kann damit beginnen, die folgenden Virus-Aktivitäten auf Ihrem Computer ausführen:
- erstellen mutexes.
- Erhalten Sie Administratorrechte.
- Melden Sie sich die Tastatureingaben Sie geben Sie Ihre Passwörter zu sehen.
- Installieren Sie andere Viruskomponenten.
- Tippen Sie in das Mikrofon und Kamera aufzeichnen Sie.
Die Varensky Virus hat ein Modul, das automatisch aktiviert werden, wenn Sie eine Seite für Erwachsene und verwenden diese Informationen, besuchen Sie zu erpressen. Die Cyber-Kriminelle können Sie auf der Kamera aufnehmen und dann Screenshots von Ihnen verwenden, um Ihnen zu zeigen, dass sie kein Witz. Im Gegenzug, sie wollen Sie Lösegeld zahlen und sonst drohen sie Ihre privaten Videos oder Fotos zu öffentlichen Foren und anderen Websites lecken. Das Virus wurde zuerst in Frankreich entdeckt, aber Berichte zeigen, dass es schnell verbreitet globalen Maßstab werden kann. Benutzern wird empfohlen, nicht auf die Cyber-Kriminellen zu erfüllen und immer ihre Kameras decken, und wenn Sie diesen Virus sehen, Sie sollten diese sofort entfernen.

Wie Entfernen Varensky Virus
Um diesen Virus zu entfernen, Sie müssen ihre Komponenten identifizieren. Sie können sie durch den Anblick verdächtige EXE und andere Prozesse erkennen im Hintergrund runing. einmal gefunden, Sie können diese Komponenten von Windows Task-Manager deaktivieren. Die folgenden Anweisungen weisen Schritt-für-Schritt-Anleitung, wie die manuell erfassen und entfernen, Varensky Virus von Ihrem Computer. Wenn Sie jedoch die Virus-Dateien von Varensky Malware nicht finden können,, dann empfehlen wir dringend, dass Sie eine professionelle Anti-Spyware-Software, die alle Spuren automatisch erkennen und entfernen wird der Varensky Virus für Sie und Sie gegen zukünftige Infektionen aller Art schützen.
Vorbereitung vor Varensky Virus zu entfernen.
Vor dem eigentlichen Entfernungsprozess starten, Wir empfehlen Ihnen die folgenden Vorbereitungsschritte zu tun.
- Stellen Sie sicher, dass Sie diese Anweisungen haben immer offen und vor Ihren Augen.
- Führen Sie eine Sicherung aller Dateien, selbst wenn sie beschädigt werden könnten. Sie sollten Ihre Daten mit einer Cloud-Backup-Lösung und sichern Sie Ihre Dateien gegen jede Art von Verlust sichern, selbst von den schwersten Bedrohungen.
- Seien Sie geduldig, da dies könnte eine Weile dauern.
- Nach Malware durchsuchen
- Register reparieren
- Entfernen Sie Virendateien
Schritt 1: Scan for Varensky Virus mit SpyHunter Anti-Malware-Tool



Schritt 2: Reinigen Sie alle Register, von Varensky Virus auf Ihrem Computer erstellt.
Die in der Regel gezielt Register von Windows-Rechnern sind die folgenden:
- HKEY_LOCAL_MACHINE Software Microsoft Windows Currentversion Run
- HKEY_CURRENT_USER Software Microsoft Windows Currentversion Run
- HKEY_LOCAL_MACHINE Software Microsoft Windows Currentversion RunOnce
- HKEY_CURRENT_USER Software Microsoft Windows Currentversion RunOnce
Sie können auf sie zugreifen, indem Sie den Windows-Registrierungs-Editor und löschen Sie alle Werte öffnen, erstellt dort von Varensky Virus. Dies kann passieren, darunter indem Sie die Schritte:


 Spitze: Um einen Virus erstellten Wert zu finden, Sie können sich auf der rechten Maustaste und klicken Sie auf "Ändern" um zu sehen, welche Datei es wird ausgeführt. Ist dies der Virus Speicherort, Entfernen Sie den Wert.
Spitze: Um einen Virus erstellten Wert zu finden, Sie können sich auf der rechten Maustaste und klicken Sie auf "Ändern" um zu sehen, welche Datei es wird ausgeführt. Ist dies der Virus Speicherort, Entfernen Sie den Wert.Schritt 3: Find virus files created by Varensky Virus on your PC.
1.Für Windows- 8, 8.1 und 10.
Für neuere Windows-Betriebssysteme
1: Auf Ihrer Tastatur drücken + R und schreibe explorer.exe im Lauf Textfeld ein und klicken Sie dann auf die Ok Taste.

2: Klicke auf Ihren PC von der schnellen Zugriffsleiste. Dies ist in der Regel ein Symbol mit einem Monitor und sein Name ist entweder "Mein Computer", "Mein PC" oder "Dieser PC" oder was auch immer Sie haben es benannt.

3: Navigieren Sie zum Suchfeld oben rechts auf dem Bildschirm Ihres PCs und geben Sie ein "Dateierweiterung:" und wonach geben Sie die Dateierweiterung. Wenn Sie böswillige exe-Dateien suchen, Ein Beispiel kann sein, "Dateierweiterung:exe". Nachdem ich, dass, einen Raum verlassen und den Dateinamen, den Sie sich die Malware glauben geben Sie erstellt. Hier ist, wie es scheinen mag, wenn Ihre Datei gefunden wurde,:

NB. We recommend to wait for the green loading bar in the navigation box to fill up in case the PC is looking for the file and hasn't found it yet.
2.Für Windows XP, Aussicht, und 7.
Für Ältere Windows-Betriebssysteme
In älteren Windows-Betriebssystemen sollte der herkömmliche Ansatz der effektive sein:
1: Klicken Sie auf die Startmenü Symbol (in der Regel auf der linken unteren) und wählen Sie dann die Suche Vorliebe.

2: Nachdem das Suchfenster erscheint, wählen Weitere Optionen von der Suchassistent Box. Eine andere Möglichkeit ist, indem Sie auf Alle Dateien und Ordner.

3: Nach dieser Art für den Namen der Datei, suchen Sie und klicken Sie auf die Schaltfläche Suchen. Dies könnte einige Zeit dauern, nach der Ergebnisse werden angezeigt. Wenn Sie die bösartige Datei gefunden, Sie können ihre Lage zu kopieren oder zu öffnen, indem Sie Rechtsklick auf sie.
Jetzt sollten Sie jede Datei unter Windows, so lange zu entdecken können, wie es auf der Festplatte ist und nicht über eine spezielle Software verborgen.
Varensky Virus FAQ
What Does Varensky Virus Trojan Do?
The Varensky Virus Trojan ist ein bösartiges Computerprogramm entworfen, um zu stören, Schaden, oder sich unbefugten Zugriff verschaffen an ein Computersystem. Es kann verwendet werden, um sensible Daten zu stehlen, Kontrolle über ein System erlangen, oder andere böswillige Aktivitäten starten.
Können Trojaner Passwörter stehlen??
Ja, Trojaner, like Varensky Virus, kann Passwörter stehlen. Diese Schadprogramme are designed to gain access to a user's computer, Opfer ausspionieren und vertrauliche Informationen wie Bankdaten und Passwörter stehlen.
Can Varensky Virus Trojan Hide Itself?
Ja, es kann. Ein Trojaner kann sich verschiedener Techniken bedienen, um sich zu maskieren, einschließlich Rootkits, Verschlüsselung, und Verschleierungs, um sich vor Sicherheitsscannern zu verstecken und der Entdeckung zu entgehen.
Kann ein Trojaner durch Zurücksetzen auf die Werkseinstellungen entfernt werden??
Ja, Ein Trojaner kann durch Zurücksetzen Ihres Geräts auf die Werkseinstellungen entfernt werden. Dies liegt daran, dass das Gerät in seinen ursprünglichen Zustand zurückversetzt wird, Entfernen von möglicherweise installierter Schadsoftware. Bedenken Sie, dass es ausgefeiltere Trojaner gibt, die Hintertüren hinterlassen und selbst nach einem Zurücksetzen auf die Werkseinstellungen erneut infizieren.
Can Varensky Virus Trojan Infect WiFi?
Ja, Es ist möglich, dass ein Trojaner WiFi-Netzwerke infiziert. Wenn sich ein Benutzer mit dem infizierten Netzwerk verbindet, Der Trojaner kann sich auf andere verbundene Geräte ausbreiten und auf vertrauliche Informationen im Netzwerk zugreifen.
Können Trojaner gelöscht werden?
Ja, Trojaner können gelöscht werden. Dies geschieht normalerweise durch Ausführen eines leistungsstarken Antiviren- oder Anti-Malware-Programms, das darauf ausgelegt ist, bösartige Dateien zu erkennen und zu entfernen. In einigen Fällen, Gegebenenfalls ist auch eine manuelle Löschung des Trojaners erforderlich.
Können Trojaner Dateien stehlen??
Ja, Trojaner können Dateien stehlen, wenn sie auf einem Computer installiert sind. Dies geschieht durch Zulassen der Malware-Autor oder Benutzer, sich Zugriff auf den Computer zu verschaffen und dann die darauf gespeicherten Dateien zu stehlen.
Welche Anti-Malware kann Trojaner entfernen?
Anti-Malware-Programme wie z SpyHunter sind in der Lage, Ihren Computer nach Trojanern zu durchsuchen und diese zu entfernen. Es ist wichtig, Ihre Anti-Malware auf dem neuesten Stand zu halten und Ihr System regelmäßig auf schädliche Software zu scannen.
Können Trojaner USB infizieren?
Ja, Trojaner können infizieren USB Geräte. USB-Trojaner verbreitet sich in der Regel über bösartige Dateien, die aus dem Internet heruntergeladen oder per E-Mail geteilt werden, allowing the hacker to gain access to a user's confidential data.
About the Varensky Virus Research
Die Inhalte, die wir auf SensorsTechForum.com veröffentlichen, this Varensky Virus how-to removal guide included, ist das Ergebnis umfangreicher Recherchen, harte Arbeit und die Hingabe unseres Teams, um Ihnen bei der Beseitigung des spezifischen Trojanerproblems zu helfen.
How did we conduct the research on Varensky Virus?
Bitte beachten Sie, dass unsere Forschung auf einer unabhängigen Untersuchung basiert. Wir stehen in Kontakt mit unabhängigen Sicherheitsforschern, Dank dessen erhalten wir täglich Updates zu den neuesten Malware-Definitionen, einschließlich der verschiedenen Arten von Trojanern (hintertür, Downloader, infostealer, Lösegeld, usw.)
Weiter, the research behind the Varensky Virus threat is backed with Virustotal.
Um die Bedrohung durch Trojaner besser zu verstehen, Bitte lesen Sie die folgenden Artikel, die sachkundige Details bieten.