 Denne artikel er blevet oprettet for at forklare dig, hvad der er den Zombie Phish fidus og hvordan du kan fjerne dem, samt alle potentielt uønskede programmer leveret gennem dem.
Denne artikel er blevet oprettet for at forklare dig, hvad der er den Zombie Phish fidus og hvordan du kan fjerne dem, samt alle potentielt uønskede programmer leveret gennem dem.
Den Zombie Phish fidus er en ny farlig hacking strategi, der forsøger at snyde internetbrugere i at inficere sig selv med virus. Dette gøres via orkestrere mange e-mails, der beder dem til at klikke på links eller interagere med det viste indhold. Vores artikel giver en grundig forklaring på, hvordan det udbredes, og hvordan ofrene kan prøve at fjerne aktive infektioner.

Trussel Summary
| Navn | Zombie Phish fidus |
| Type | Phishing email fidus |
| Kort beskrivelse | Den zombie Phish fidus er et nyligt eksempel på den fidus taktik, der extorts målene i samspil med et fupnummer websted. |
| Symptomer | Ofre vil modtage e-mails, der indeholder phishing instruktioner. |
| Distributionsmetode | Phishing e-mails. |
| Værktøj Detection |
Se, om dit system er blevet påvirket af malware
Hent
Værktøj til fjernelse af malware
|
Brugererfaring | Tilmeld dig vores forum at diskutere Zombie Phish fidus. |

Zombie Phish fidus - Distribution måder
Den zombie Phish fidus er en ondsindet strategi, der bliver brugt af mange hacking grupper for at lokke modtagerne. Det spredes via e-mails ved hjælp af fælles orm taktik.
Denne særlige trussel er kendt for at drage fordel af det faktum, at modtagerne af de e-mails er meget tilbøjelige til at klikke på generiske skabeloner og meddelelser, der kan virke bekendt eller ligner meddelelser, der er sendt ind af kendte virksomheder eller tjenester.
En af de mest populære former, der modtages, er almindelig sms at læse følgende:
…
[Besked klippet] Se hele meddelelsen
Disse slags meddelelser kan være almindeligt modtages af legitime meddelelser eller filtreres direkte af e-mail-tjenester. For at se indholdet korrekt brugerne opfordres til at klikke på de interaktive links. De links, der er inkluderet er hostet på domæner, der automatisk genereres og bruge et mønster, der emulerer web-mail stil ord. Som et resultat er det meget vanskeligt at beskytte mod sådanne infektioner som tusindvis af vilkårlige domæner, der indeholder det cn blive lanceret på et øjeblik ved hacker grupper.

Zombie Phish fidus - Dybdegående Oversigt
Den zombie Phish fidus bruges til at skubbe forskellige trusler til offer maskiner. I de fleste tilfælde ofrene kan forvente en af følgende infektioner:
- Ransomware - Disse er blandt de mest almindelige virus, de søger at kryptere mål brugerdata med en stærk cipher og gøre data utilgængelige.
- Trojans - trojanske virus er lavet med henblik på at gøre det muligt for hackere at overtage kontrollen over værterne. Dette gøres ved at lancere et program eller script, der vil igangsætte og opretholde en forbindelse med en hacker-kontrolleret server. Dette gør det muligt for hackere ikke kun for at overtage kontrollen af maskinerne, men også stjæle data og implementere andre trusler.
- Browser Hijackers - E-mails kan bruges som en nyttelast bærer for flykaprere, der er ondsindede plugins lavet til de mest populære webbrowsere. Deres vigtigste mål er at omdirigere ofrene til en vis hacker-kontrolleret hjemmeside eller portal, der kan være vært for andre malware og føre til en lang række ondsindede handlinger. En anden konsekvens af at have dem installeret, er deres evne til at kapre alle data, der er indeholdt i programmerne: historie, bogmærker, cache og selv gemte kontooplysninger.
- Phishing sider - Disse e-mails kan tjene som en kanal for forskellige phishing strategier, der manipulerer modtagerne til at udlevere deres personlige oplysninger eller brugerkonti. Stederne kan hostes på domæner, der lyder meget ens eller næsten identiske med de legitime websteder.
Den zombie Phish fidus kan startes ved forskellige kriminelle kollektiver som teknikken kan nemt kopieres og tilpasses forskellige luftfartsselskaber. Dette omfatter mørke underjordiske markeder hvor ekspertise og ready-made kode kan deles mellem individer og grupper. Det er meget muligt, at kampagnerne er orkestreret på disse samfund og planlagt med henblik på at føre til en høj succes ratio.

Fjern Zombie Phish fidus fra Windows og din browser
Hvis du ønsker at fjerne Zombie Phish fidus fra din computer, Vi anbefaler kraftigt, at du følger fjernelse instruktioner bogført under denne artikel. De er blevet skabt med de vigtigste idé i tankerne til at hjælpe dig slette denne virus enten manuelt eller automatisk. Vær opmærksom på, at ifølge eksperter den bedste måde at forsøge at fjerne den software, der er årsag til Zombie Phish snydere pop-ups er at bruge et avanceret anti-malware-software. Et sådant program er skabt med den idé i tankerne til fuldt ud at scanne computeren og forsøge at fjerne ethvert spor af uønskede programmer og samtidig beskytte din computer mod fremtidige infektioner samt.
- Vinduer
- Mac OS X
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
- Safari
- Internet Explorer
- Stop push-pop op-vinduer
Sådan fjernes Zombie Phish Scam fra Windows.
Trin 1: Scan efter Zombie Phish-fidus med SpyHunter Anti-Malware Tool



Trin 2: Start din pc i fejlsikret tilstand





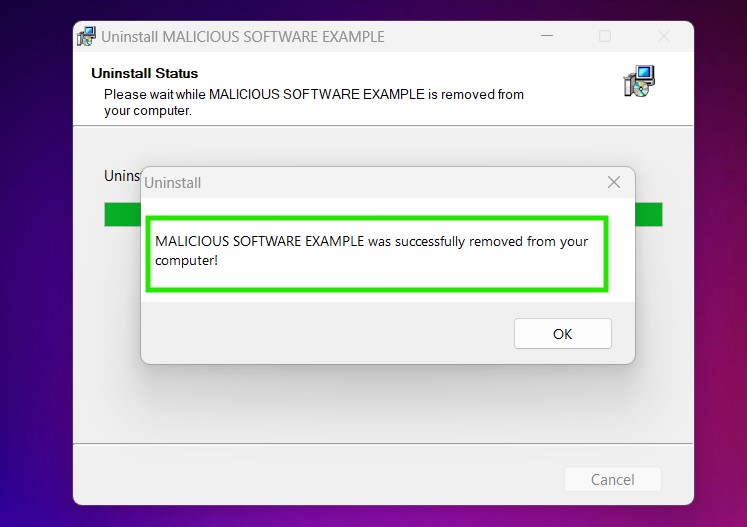
Trin 3: Afinstaller Zombie Phish Scam og relateret software fra Windows
Afinstaller Steps til Windows 11
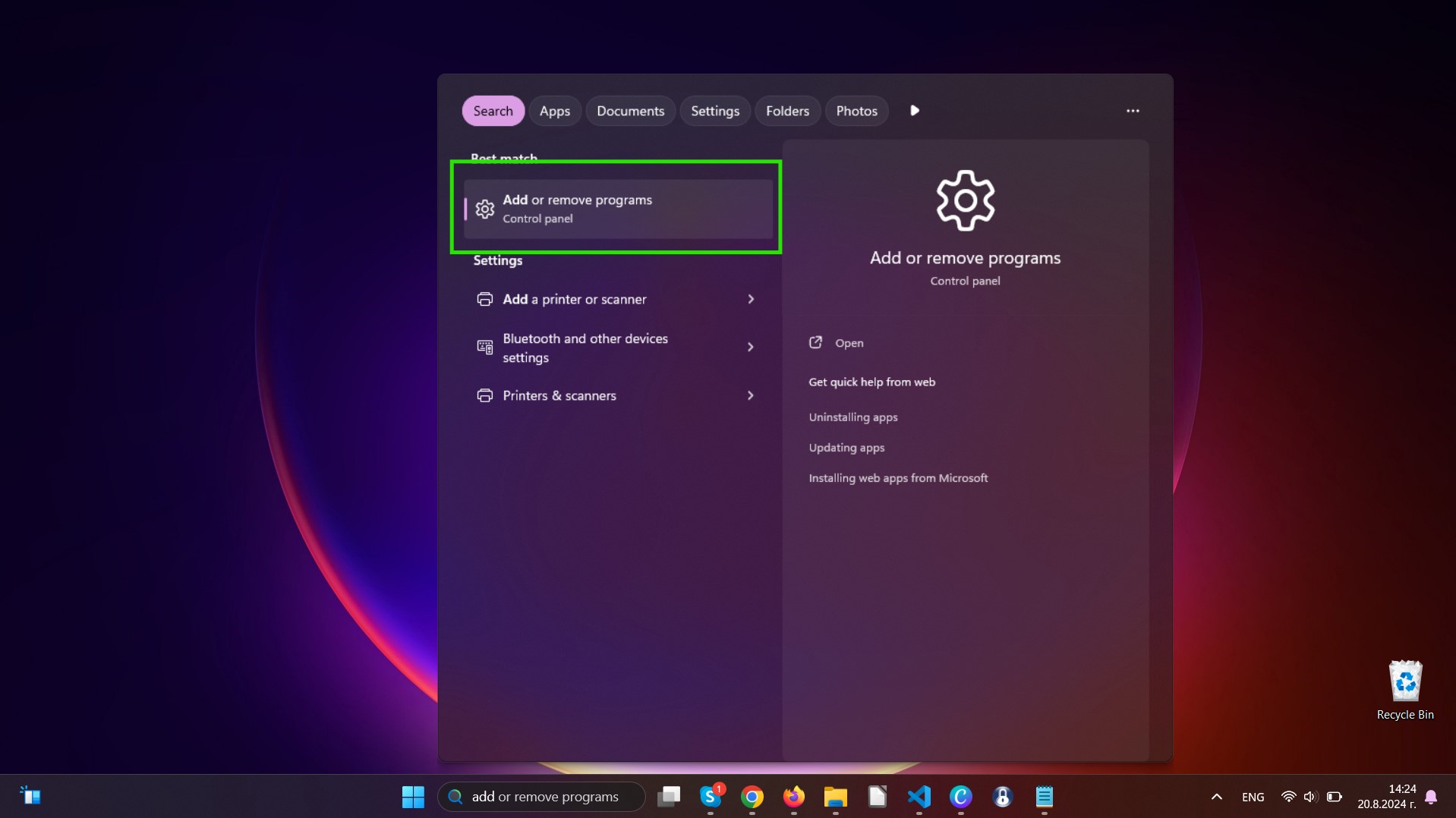
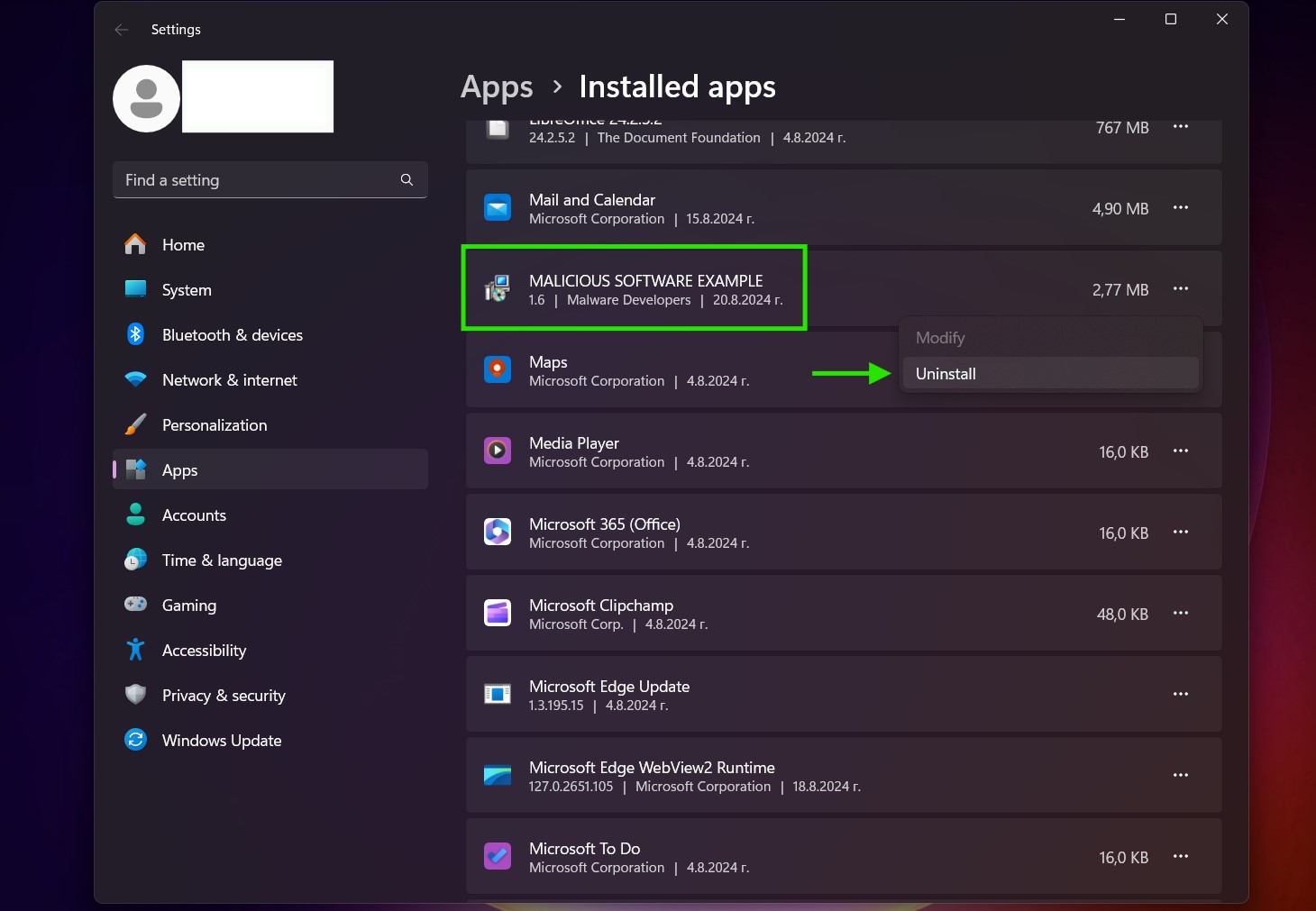
Afinstaller Steps til Windows 10 og ældre versioner
Her er en metode i nogle få nemme trin, der bør være i stand til at afinstallere de fleste programmer. Uanset om du bruger Windows 10, 8, 7, Vista eller XP, disse skridt vil få arbejdet gjort. At trække det program eller dets mappe til papirkurven kan være en meget dårlig beslutning. Hvis du gør det, stumper og stykker af programmet er efterladt, og det kan føre til ustabile arbejde på din PC, fejl med filtypen foreninger og andre ubehagelige aktiviteter. Den rigtige måde at få et program fra din computer er at afinstallere det. For at gøre dette:


 Følg anvisningerne ovenfor, og du vil afinstallere de fleste programmer.
Følg anvisningerne ovenfor, og du vil afinstallere de fleste programmer.
Trin 4: Rens eventuelle registre, Created by Zombie Phish Scam on Your PC.
De normalt målrettede registre af Windows-maskiner er følgende:
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion Run
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion Run
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion RunOnce
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion RunOnce
Du kan få adgang til dem ved at åbne Windows Registry Editor og slette eventuelle værdier, skabt af Zombie Phish Scam der. Dette kan ske ved at følge trinene nedenunder:


 Tip: For at finde en virus-skabt værdi, du kan højreklikke på det og klikke "Modificere" at se, hvilken fil det er indstillet til at køre. Hvis dette er virus fil placering, fjerne værdien.
Tip: For at finde en virus-skabt værdi, du kan højreklikke på det og klikke "Modificere" at se, hvilken fil det er indstillet til at køre. Hvis dette er virus fil placering, fjerne værdien.
Video Removal Guide for Zombie Phish Scam (Vinduer).
Slip af med Zombie Phish Scam fra Mac OS X.
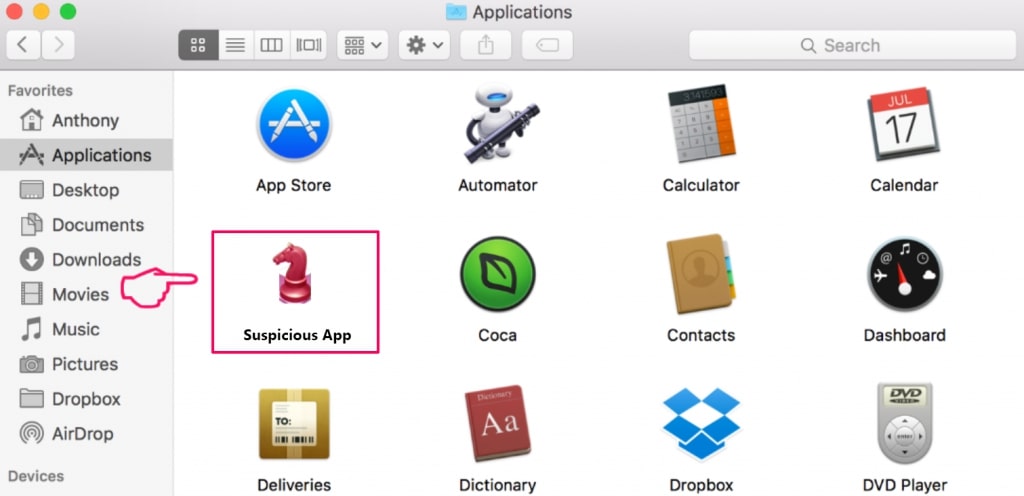
Trin 1: Uninstall Zombie Phish Scam and remove related files and objects
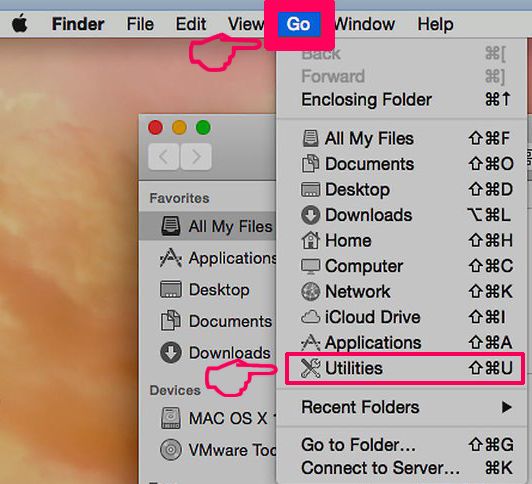
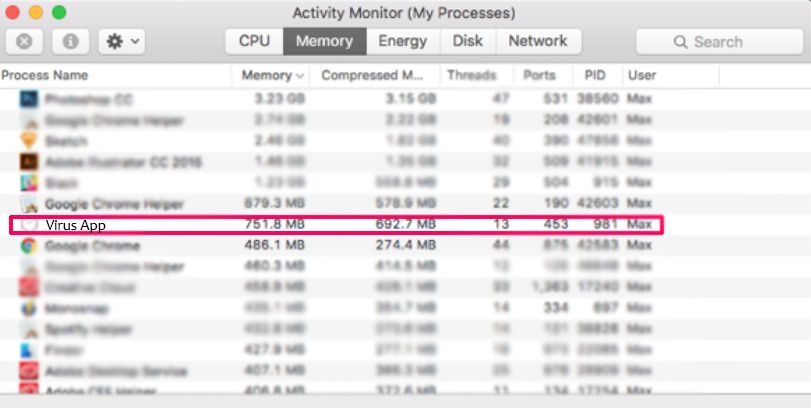
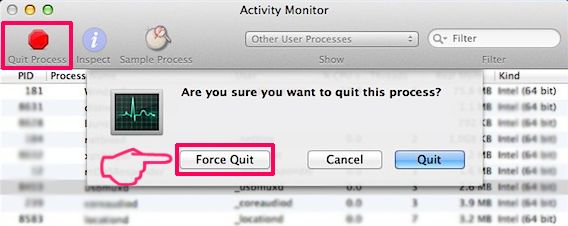
Din Mac vil så vise dig en liste over emner, starte automatisk når du logger ind. Kig efter eventuelle mistænkelige apps, der er identiske med eller ligner Zombie Phish Scam. Tjek den app, du ønsker at stoppe i at køre automatisk, og vælg derefter på Minus ("-") ikonet for at skjule det.
- Gå til Finder.
- I søgefeltet skriv navnet på den app, du vil fjerne.
- Over søgefeltet ændre to rullemenuerne til "System Files" og "Er Inkluderet" så du kan se alle de filer, der er forbundet med det program, du vil fjerne. Husk på, at nogle af filerne kan ikke være relateret til den app, så være meget forsigtig, hvilke filer du sletter.
- Hvis alle filerne er relateret, hold ⌘ + A knapperne til at vælge dem og derefter køre dem til "Affald".
I tilfælde af at du ikke kan fjerne Zombie Phish Scam via Trin 1 over:
I tilfælde af at du ikke finde virus filer og objekter i dine programmer eller andre steder, vi har vist ovenfor, kan du manuelt søge efter dem i bibliotekerne i din Mac. Men før du gør dette, læs den fulde ansvarsfraskrivelse nedenfor:
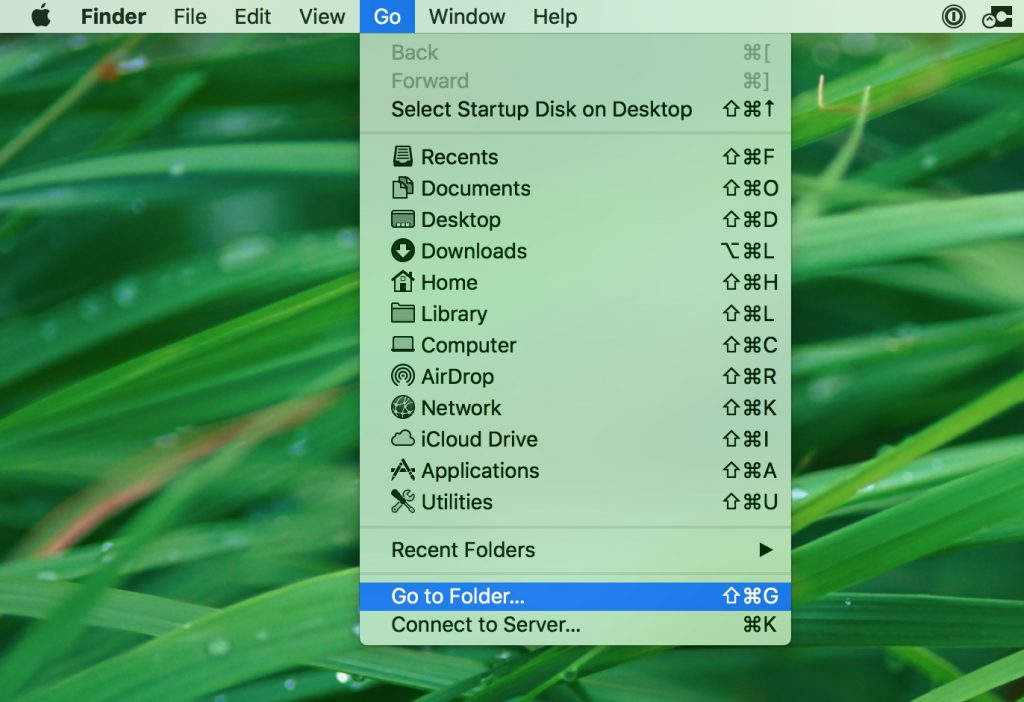
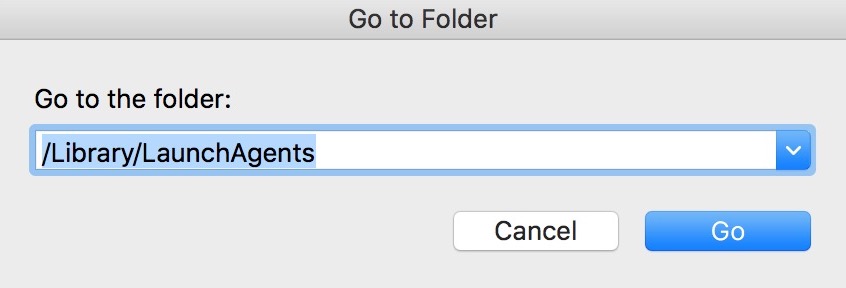
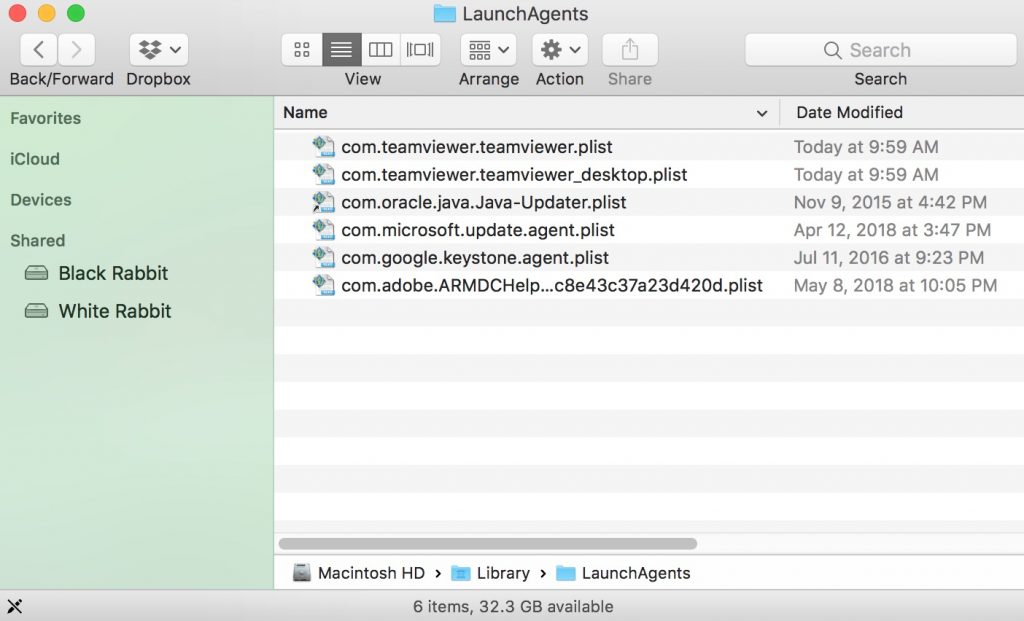
Du kan gentage den samme procedure med den følgende anden Bibliotek mapper:
→ ~ / Library / LaunchAgents
/Bibliotek / LaunchDaemons
Tip: ~ er der med vilje, fordi det fører til flere LaunchAgents.
Trin 2: Scan for and remove Zombie Phish Scam files from your Mac
Når du står over for problemer på din Mac som følge af uønskede scripts og programmer såsom Zombie Phish Scam, den anbefalede måde at eliminere truslen er ved hjælp af en anti-malware program. SpyHunter til Mac tilbyder avancerede sikkerhedsfunktioner sammen med andre moduler, der forbedrer din Mac's sikkerhed og beskytter den i fremtiden.
Video Removal Guide for Zombie Phish Scam (Mac)
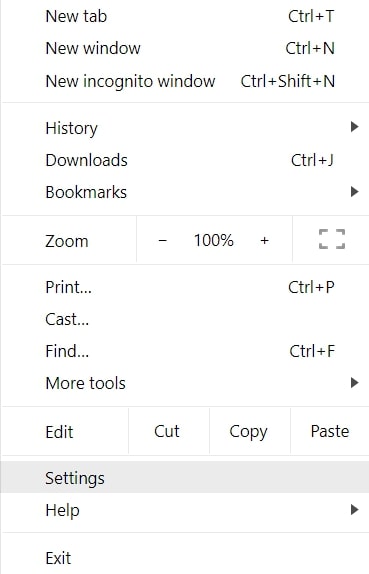
Fjern Zombie Phish Scam fra Google Chrome.
Trin 1: Start Google Chrome, og åbn dropmenuen
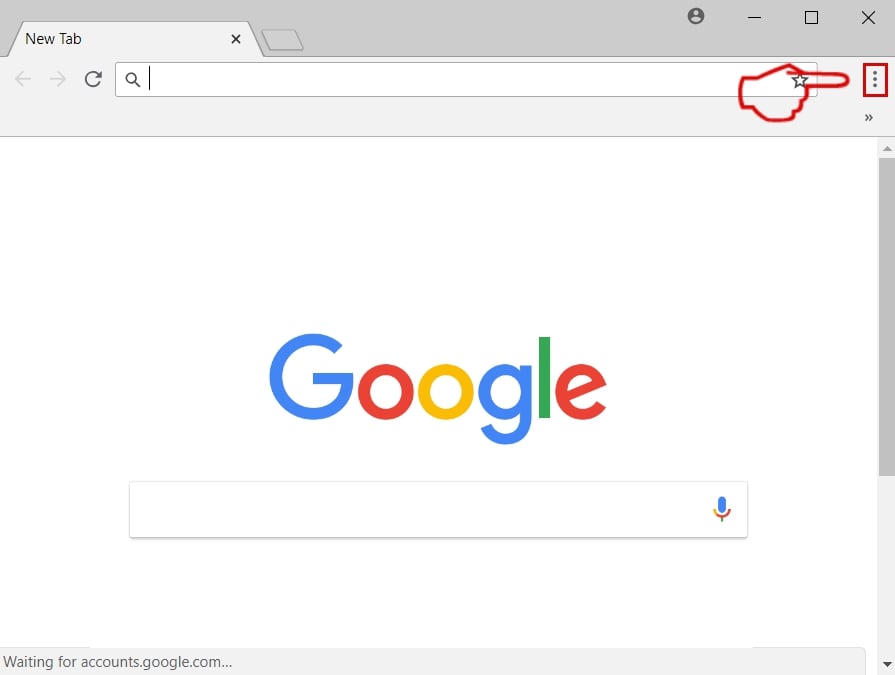
Trin 2: Flyt markøren hen over "Værktøj" og derefter fra den udvidede menu vælge "Udvidelser"
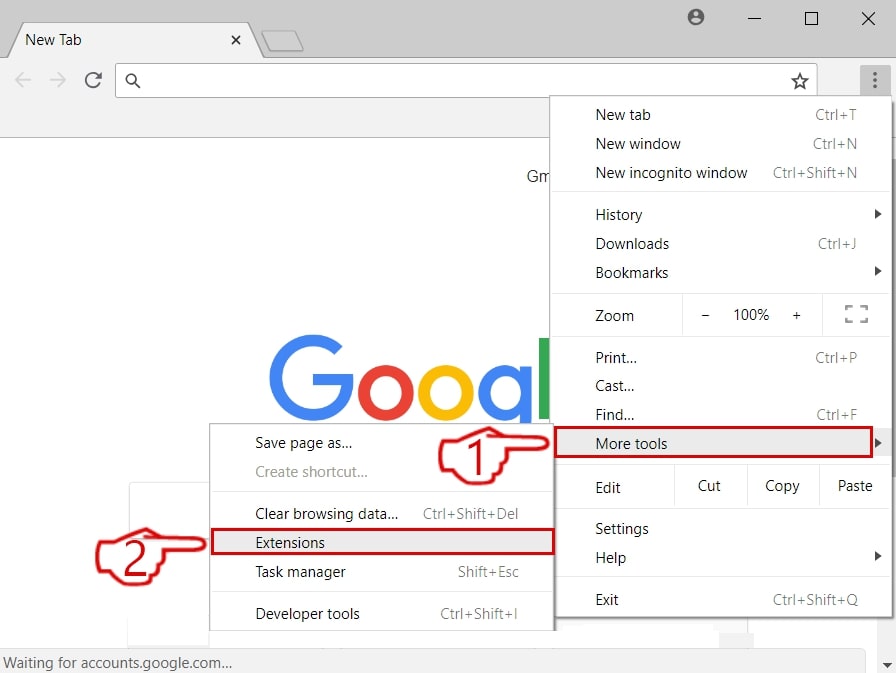
Trin 3: Fra den åbnede "Udvidelser" Menuen lokalisere den uønskede udvidelse og klik på dens "Fjerne" knap.
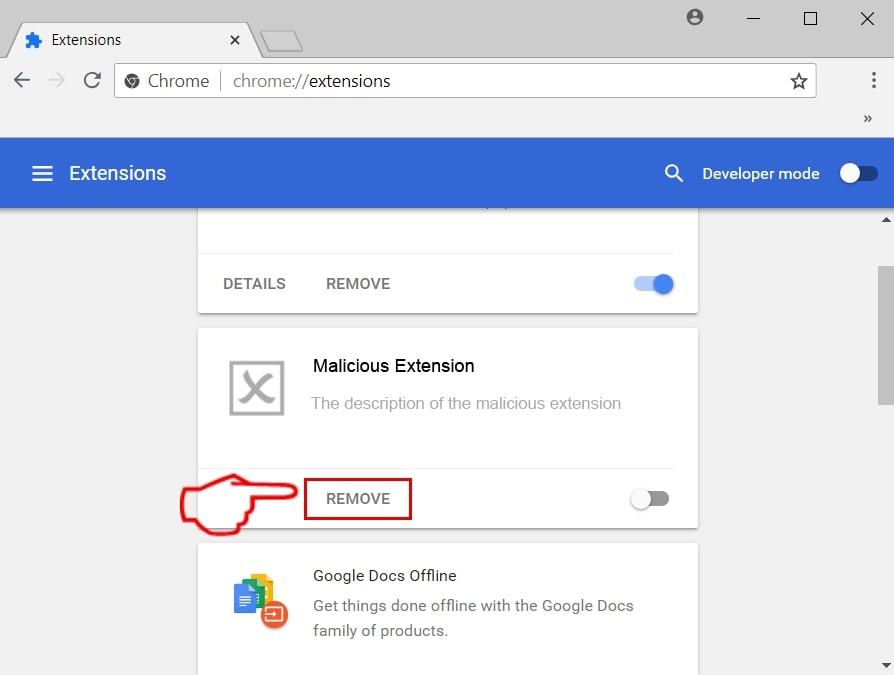
Trin 4: Efter udvidelsen er fjernet, genstarte Google Chrome ved at lukke det fra den røde "X" knappen i øverste højre hjørne, og starte den igen.
Slet Zombie Phish-fidus fra Mozilla Firefox.
Trin 1: Start Mozilla Firefox. Åbn menuen vindue:
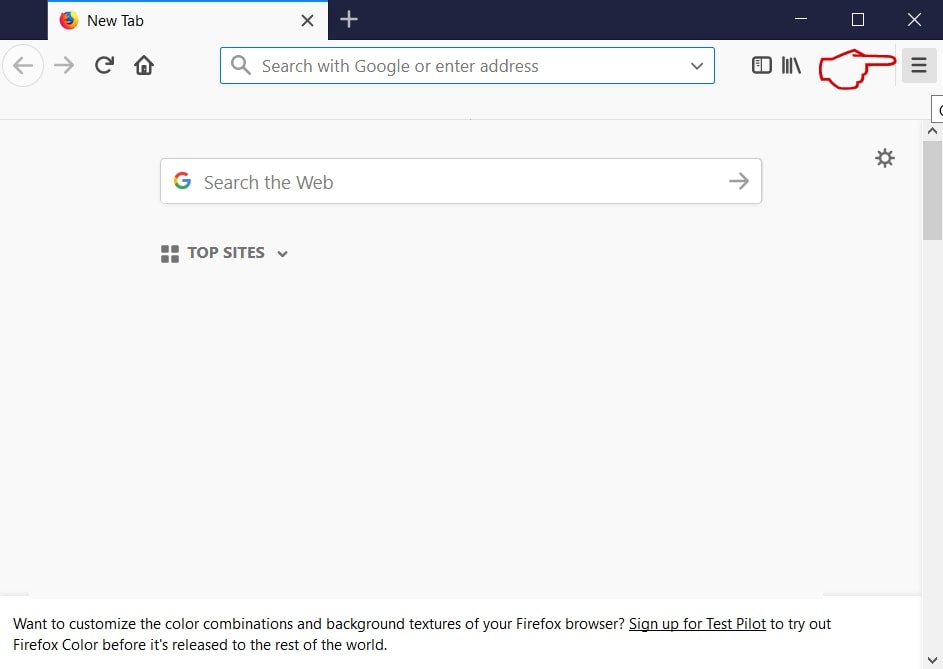
Trin 2: Vælg "Add-ons" ikon fra menuen.
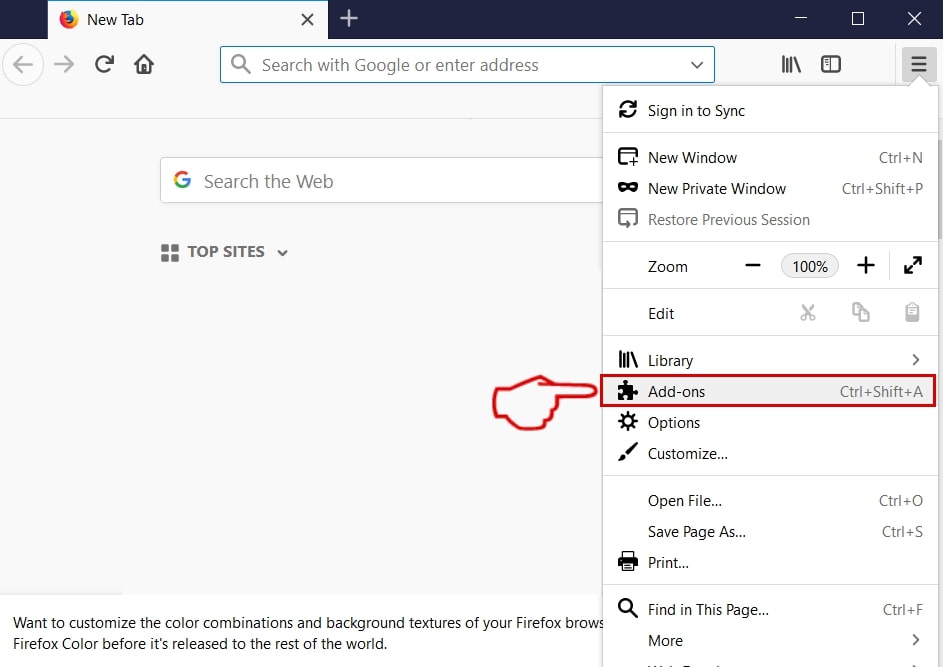
Trin 3: Vælg den uønskede udvidelse og klik "Fjerne"

Trin 4: Efter udvidelsen er fjernet, genstarte Mozilla Firefox ved at lukke det fra den røde "X" knappen i øverste højre hjørne, og starte den igen.
Afinstaller Zombie Phish Scam fra Microsoft Edge.
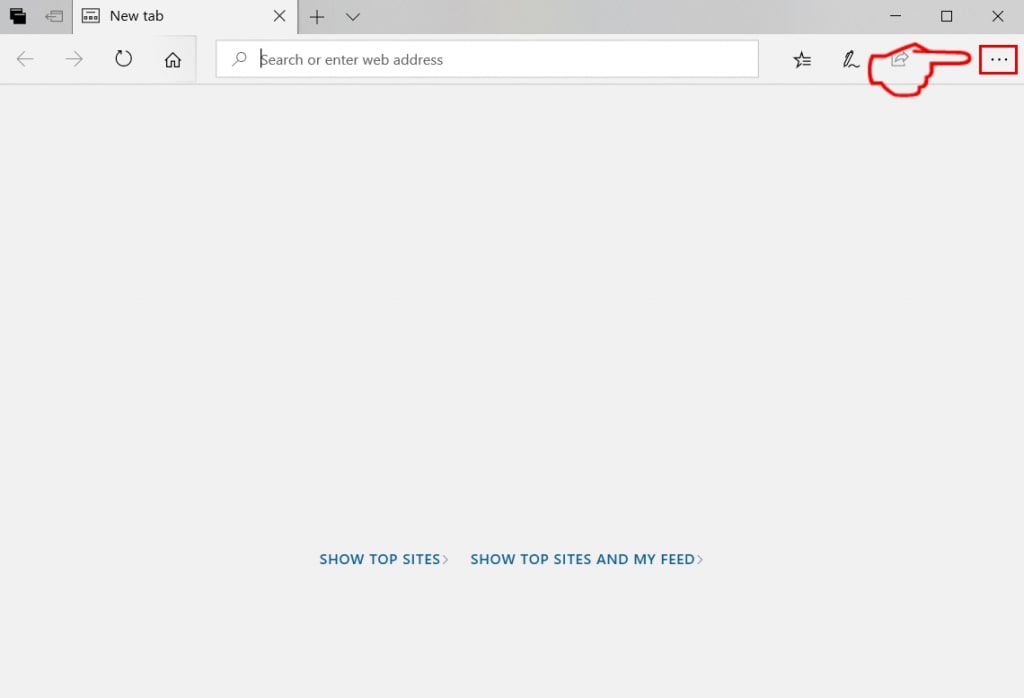
Trin 1: Start Edge-browser.
Trin 2: Åbn drop-menuen ved at klikke på ikonet i øverste højre hjørne.
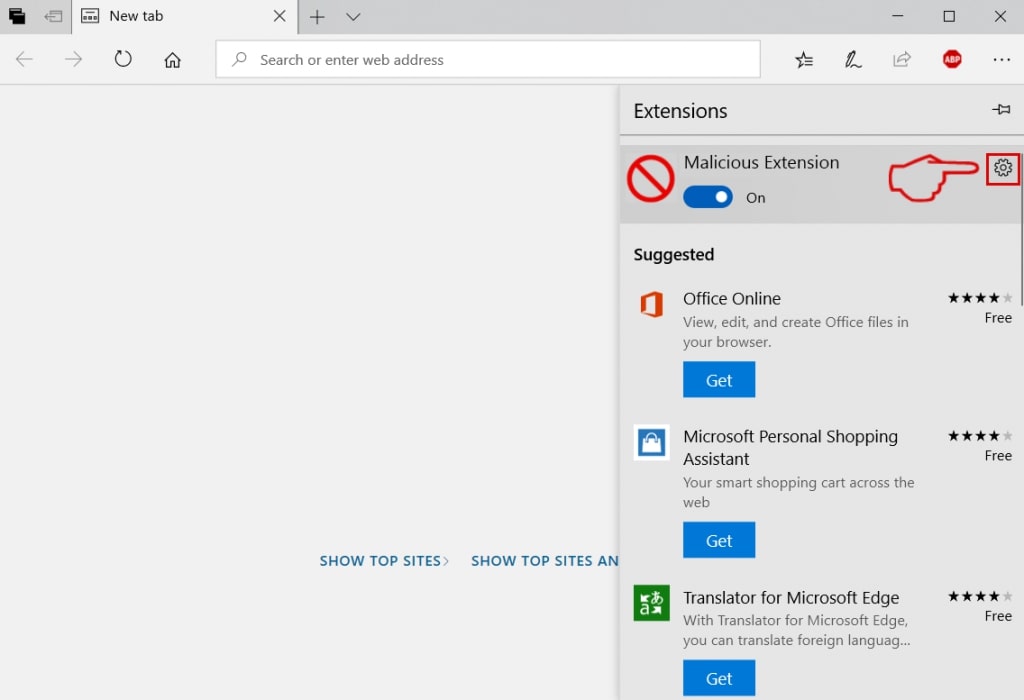
Trin 3: Fra drop-menuen vælg "Udvidelser".
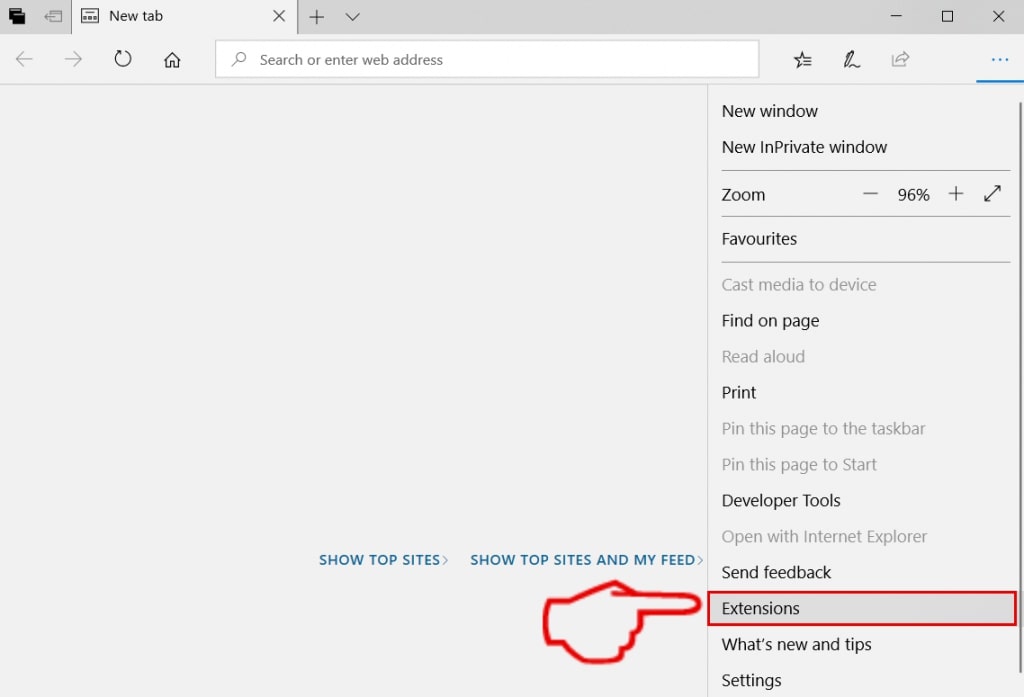
Trin 4: Vælg den formodede ondsindede udvidelse, du vil fjerne, og klik derefter på tandhjulsikonet.
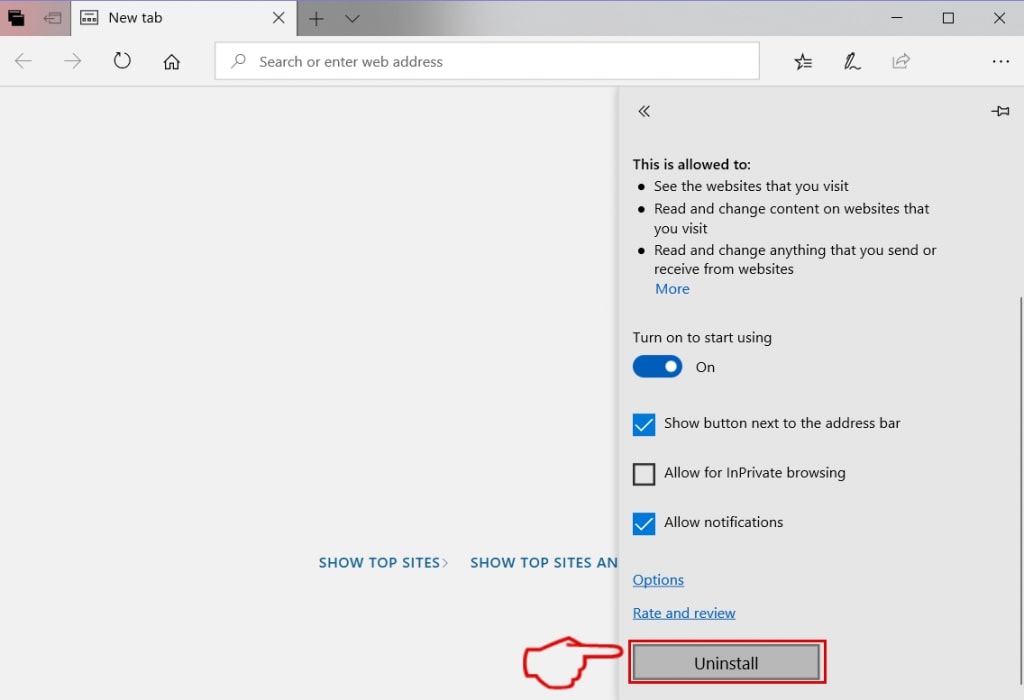
Trin 5: Fjern den ondsindede udvidelse ved at rulle ned og derefter klikke på Afinstaller.
Fjern Zombie Phish Scam fra Safari
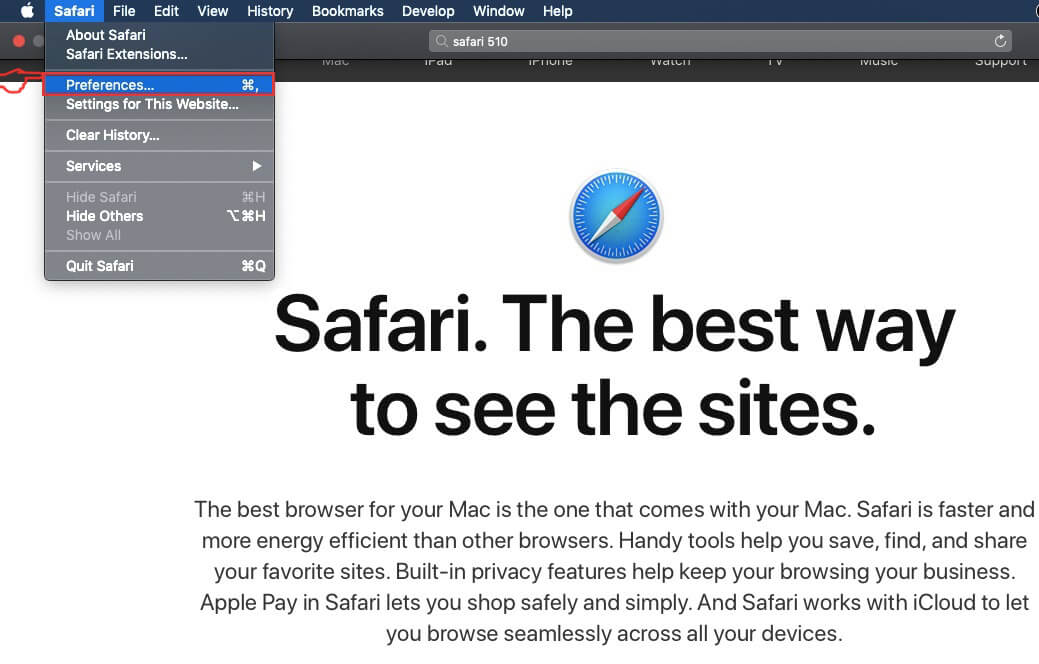
Trin 1: Start Safari-appen.
Trin 2: Efter at holde musen markøren til toppen af skærmen, klik på Safari-teksten for at åbne dens rullemenu.
Trin 3: Fra menuen, Klik på "Indstillinger".
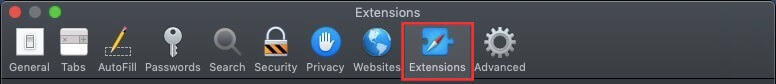
Trin 4: Efter at, vælg fanen 'Udvidelser'.
Trin 5: Klik én gang på udvidelse, du vil fjerne.
Trin 6: Klik på 'Afinstaller'.
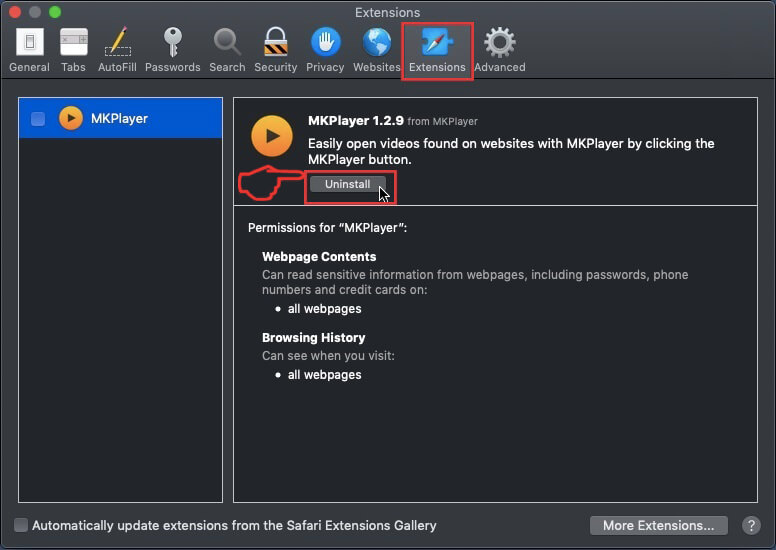
Et pop-up vindue vises beder om bekræftelse til at afinstallere forlængelsen. Vælg 'Fjern' igen, og Zombie Phish Scam vil blive fjernet.
Fjern Zombie Phish-fidus fra Internet Explorer.
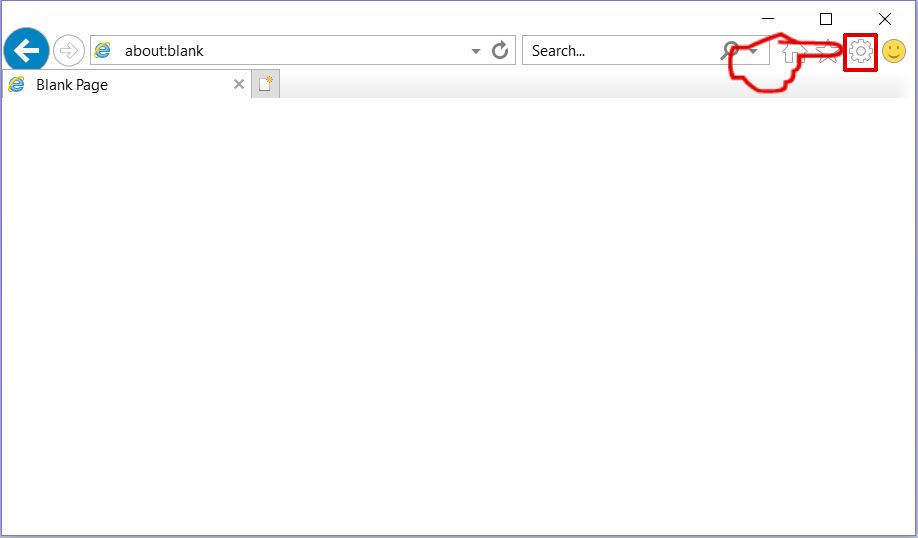
Trin 1: Start Internet Explorer.
Trin 2: Klik på tandhjulsikonet mærket 'Værktøjer' for at åbne drop-menuen og vælg 'Administrer tilføjelser'
Trin 3: I vinduet 'Administrer tilføjelser'.
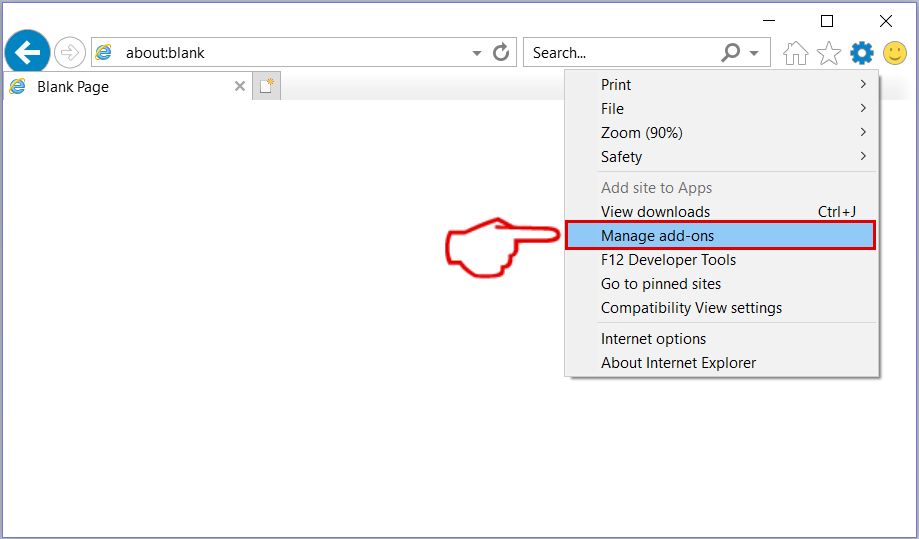
Trin 4: Vælg den udvidelse, du vil fjerne, og klik derefter på 'Deaktiver'. Et pop-up vindue vises for at informere dig om, at du er ved at deaktivere den valgte udvidelse, og nogle flere tilføjelser kan være deaktiveret så godt. Lad alle boksene kontrolleret, og klik på 'Deaktiver'.
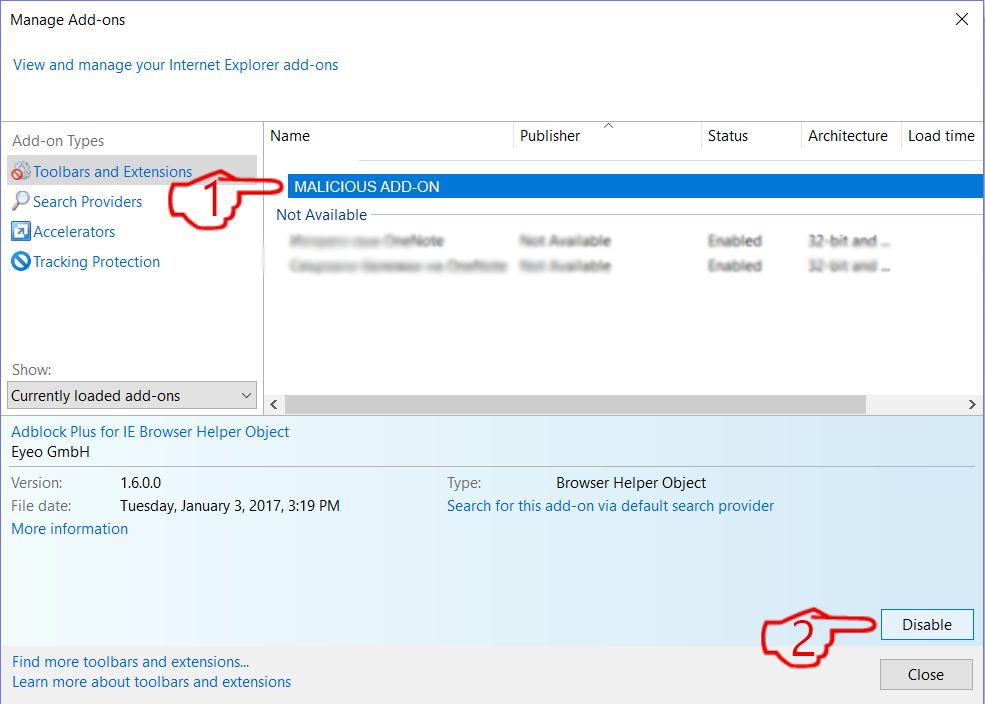
Trin 5: Efter den uønskede udvidelse er blevet fjernet, genstart Internet Explorer ved at lukke den fra den røde 'X'-knap i øverste højre hjørne, og start den igen.
Fjern push-meddelelser fra dine browsere
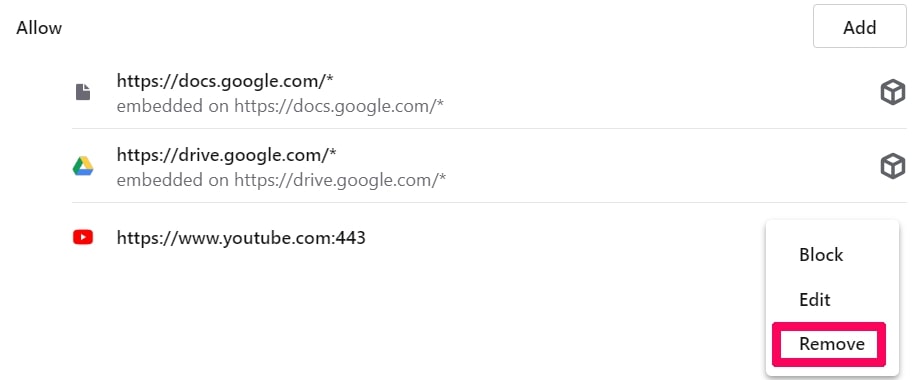
Sluk for push-meddelelser fra Google Chrome
Sådan deaktiveres push-meddelelser fra Google Chrome-browseren, Følg nedenstående trin:
Trin 1: Gå til Indstillinger i Chrome.
Trin 2: I Indstillinger, Vælg "Avancerede indstillinger":
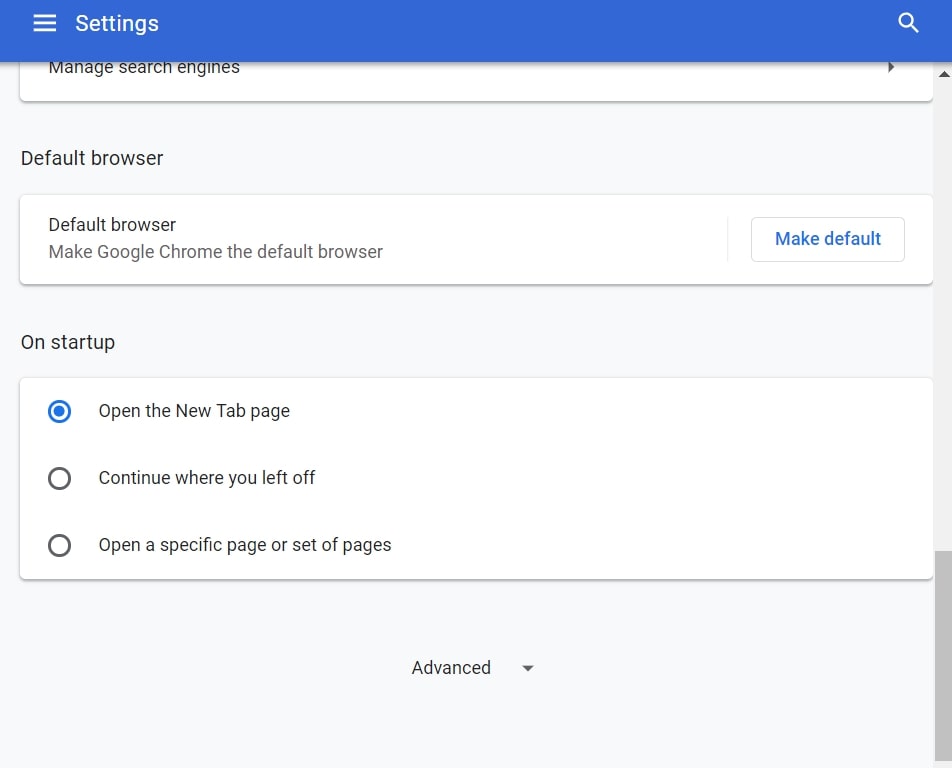
Trin 3: Klik på “Indstillinger for indhold":
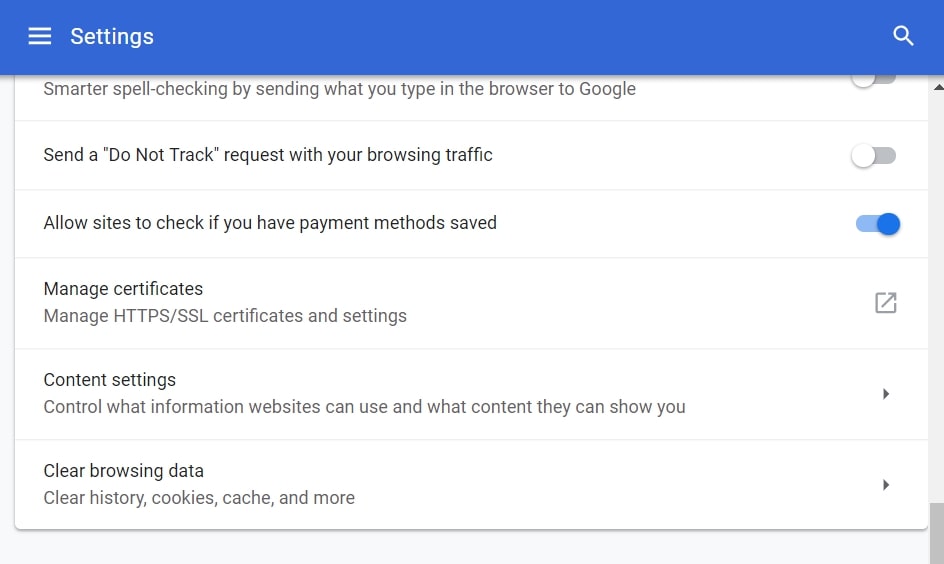
Trin 4: Åbn “underretninger":
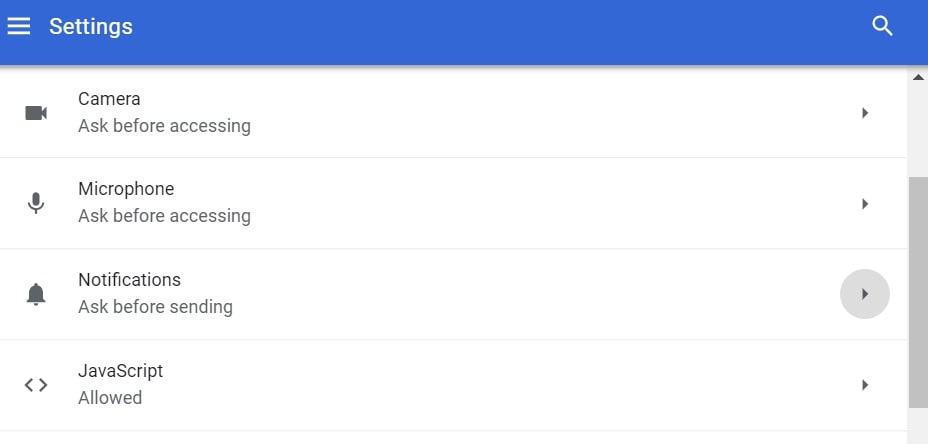
Trin 5: Klik på de tre prikker, og vælg Bloker, Rediger eller fjern muligheder:

Fjern Push Notifications på Firefox
Trin 1: Gå til Firefox-indstillinger.
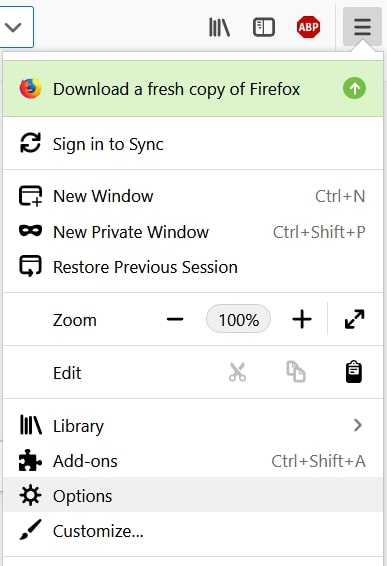
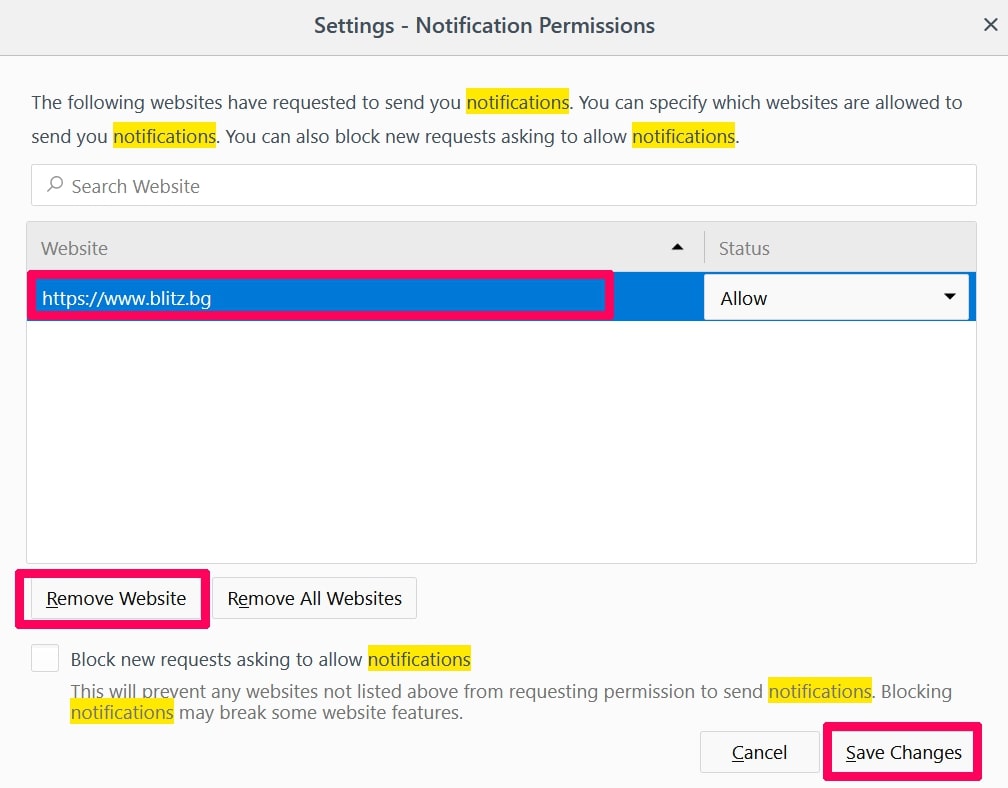
Trin 2: Gå til "Indstillinger", skriv "notifikationer" i søgefeltet, og klik "Indstillinger":
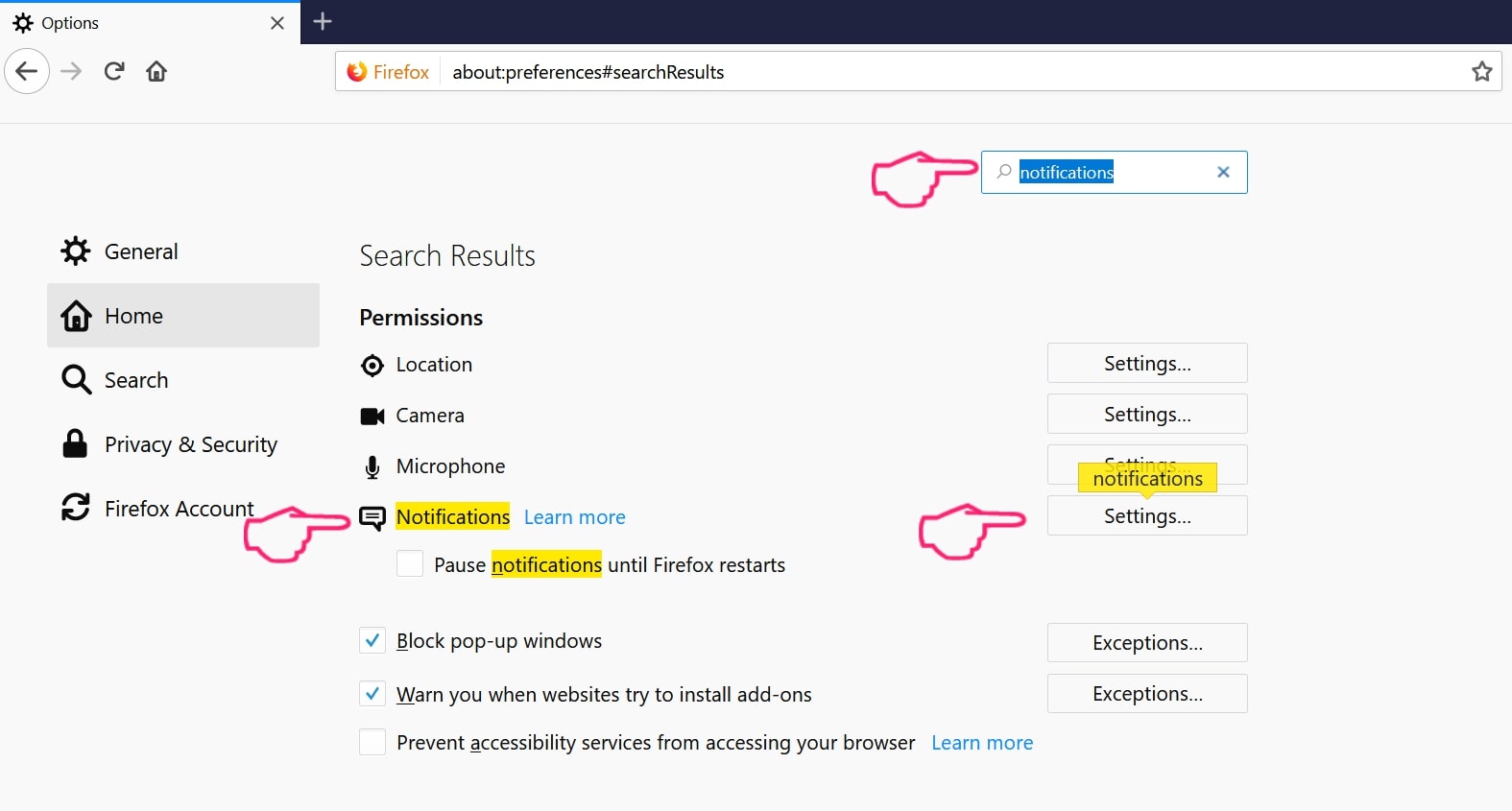
Trin 3: Klik på "Fjern" på ethvert websted, hvor du ønsker, at meddelelser er væk, og klik på "Gem ændringer"
Stop push-meddelelser på Opera
Trin 1: I opera, presse ALT+P for at gå til Indstillinger.
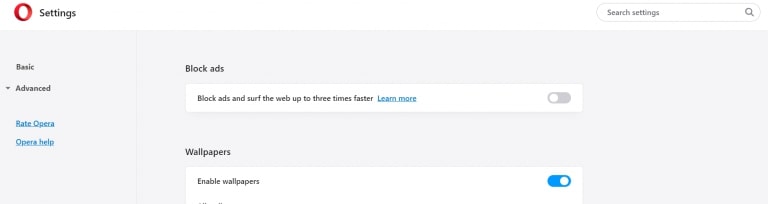
Trin 2: I Indstilling af søgning, skriv "Indhold" for at gå til Indholdsindstillinger.
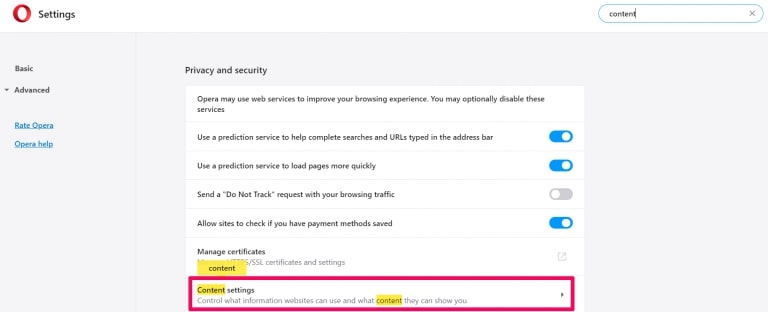
Trin 3: Åbn underretninger:
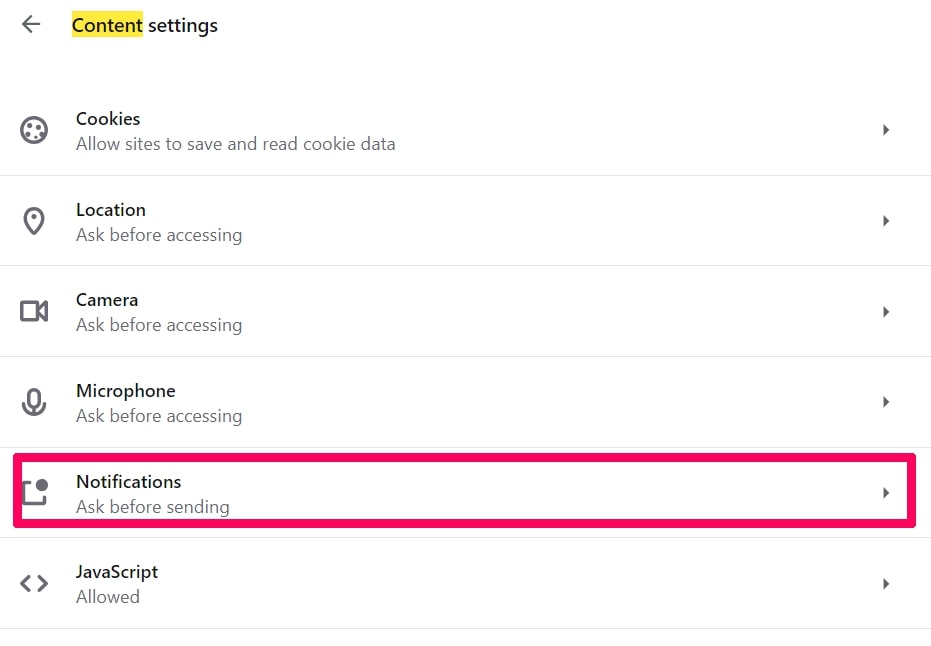
Trin 4: Gør det samme som du gjorde med Google Chrome (forklaret nedenfor):
Fjern Push-underretninger på Safari
Trin 1: Åbn Safari-indstillinger.
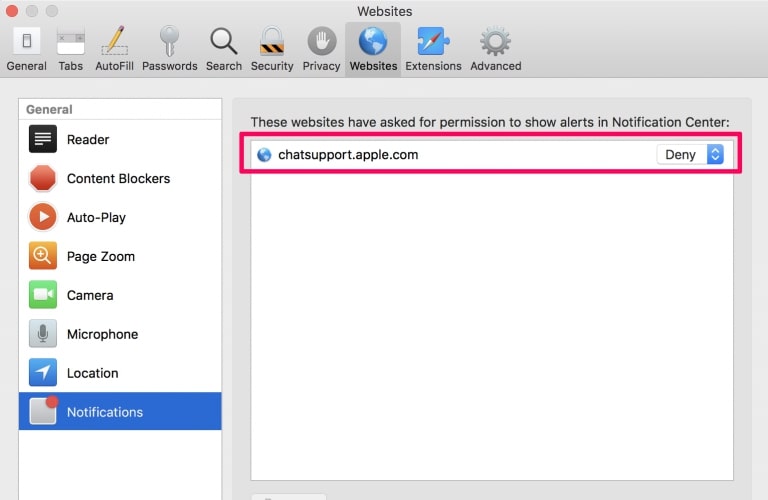
Trin 2: Vælg det domæne, hvorfra du kan lide pop-op-pop op, og skift til "Nægte" fra "Give lov til".
Zombie Phish Scam-FAQ
What Is Zombie Phish Scam?
The Zombie Phish Scam threat is adware or browser omdirigering virus.
Det kan gøre din computer langsommere og vise reklamer. Hovedideen er, at dine oplysninger sandsynligvis bliver stjålet, eller at der vises flere annoncer på din enhed.
Skaberne af sådanne uønskede apps arbejder med ordninger for betaling pr. Klik for at få din computer til at besøge risikable eller forskellige typer websteder, der kan generere dem midler. Dette er grunden til, at de ikke engang er ligeglade med, hvilke typer websteder der vises på annoncerne. Dette gør deres uønskede software indirekte risikabelt for dit operativsystem.
What Are the Symptoms of Zombie Phish Scam?
Der er flere symptomer at se efter, når denne særlige trussel og også uønskede apps generelt er aktive:
Symptom #1: Din computer kan blive langsom og generelt have dårlig ydeevne.
Symptom #2: Du har værktøjslinjer, tilføjelser eller udvidelser på dine webbrowsere, som du ikke kan huske at have tilføjet.
Symptom #3: Du ser alle typer annoncer, som annoncesupporterede søgeresultater, pop op-vinduer og omdirigeringer vises tilfældigt.
Symptom #4: Du ser installerede apps på din Mac køre automatisk, og du kan ikke huske at have installeret dem.
Symptom #5: Du ser mistænkelige processer køre i din Jobliste.
Hvis du ser et eller flere af disse symptomer, så anbefaler sikkerhedseksperter, at du tjekker din computer for virus.
Hvilke typer uønskede programmer findes der?
Ifølge de fleste malware-forskere og cybersikkerhedseksperter, de trusler, der i øjeblikket kan påvirke din enhed, kan være useriøs antivirus-software, adware, browser hijackers, klikkere, falske optimizere og enhver form for PUP'er.
Hvad skal jeg gøre, hvis jeg har en "virus" like Zombie Phish Scam?
Med få enkle handlinger. Først og fremmest, det er bydende nødvendigt, at du følger disse trin:
Trin 1: Find en sikker computer og tilslut det til et andet netværk, ikke den, som din Mac blev inficeret i.
Trin 2: Skift alle dine passwords, fra dine e-mail-adgangskoder.
Trin 3: Aktiver to-faktor-autentificering til beskyttelse af dine vigtige konti.
Trin 4: Ring til din bank til ændre dine kreditkortoplysninger (hemmelig kode, etc.) hvis du har gemt dit kreditkort til nethandel eller har lavet online aktiviteter med dit kort.
Trin 5: Sørg for at ring til din internetudbyder (Internetudbyder eller operatør) og bed dem om at ændre din IP-adresse.
Trin 6: Skift din Wi-Fi-adgangskode.
Trin 7: (Valgfri): Sørg for at scanne alle enheder, der er tilsluttet dit netværk for vira, og gentag disse trin for dem, hvis de er berørt.
Trin 8: Installer anti-malware software med realtidsbeskyttelse på alle enheder, du har.
Trin 9: Prøv ikke at downloade software fra websteder, du ikke ved noget om, og hold dig væk fra websteder med lav omdømme i almindelighed.
Hvis du følger disse anbefalinger, dit netværk og alle enheder bliver betydeligt mere sikre mod enhver trussel eller informationsinvasiv software og også være virusfri og beskyttet i fremtiden.
How Does Zombie Phish Scam Work?
Når det er installeret, Zombie Phish Scam can indsamle data ved brug af trackere. Disse data handler om dine web-browsing-vaner, såsom de websteder, du besøger, og de søgetermer, du bruger. Det bruges derefter til at målrette dig med annoncer eller til at sælge dine oplysninger til tredjeparter.
Zombie Phish Scam can also download anden skadelig software til din computer, såsom virus og spyware, som kan bruges til at stjæle dine personlige oplysninger og vise risikable annoncer, der kan omdirigere til virussider eller svindel.
Is Zombie Phish Scam Malware?
Sandheden er, at PUP'er (adware, browser hijackers) er ikke vira, men kan være lige så farligt da de muligvis viser dig og omdirigerer dig til malware-websteder og svindelsider.
Mange sikkerhedseksperter klassificerer potentielt uønskede programmer som malware. Dette er på grund af de uønskede virkninger, som PUP'er kan forårsage, såsom at vise påtrængende annoncer og indsamle brugerdata uden brugerens viden eller samtykke.
About the Zombie Phish Scam Research
Indholdet udgiver vi på SensorsTechForum.com, this Zombie Phish Scam how-to removal guide included, er resultatet af omfattende forskning, hårdt arbejde og vores teams hengivenhed for at hjælpe dig med at fjerne det specifikke, adware-relateret problem, og gendan din browser og computersystem.
How did we conduct the research on Zombie Phish Scam?
Bemærk venligst, at vores forskning er baseret på uafhængig undersøgelse. Vi er i kontakt med uafhængige sikkerhedsforskere, takket være, at vi modtager daglige opdateringer om den seneste malware, adware, og browser hijacker definitioner.
Endvidere, the research behind the Zombie Phish Scam threat is backed with VirusTotal.
For bedre at forstå denne online trussel, Se venligst følgende artikler, som giver kyndige detaljer.


