Uma nova e melhorada da variante CryptoWall ransomware foi infectar computadores em todo o mundo nos últimos dias. O novo CryptoWall 3.0 usa uma mensagem de resgate localizada e passa o tráfego para um site onde as vítimas podem pagar para a chave de decodificação necessária para desbloquear seus arquivos através de redes Tor e I2P anônimos.
CryptoWall é um tipo de ameaça-Encrypting File, que uma vez ativado na máquina infectada criptografa determinados arquivos nele e exige uma multa de $500 a fim de proporcionar a vítima com a chave de decodificação. O resgate deve ser pago em moeda digital Bitcoin no primeiro 168 horas.

Resumo ameaça
| Nome | CryptoWall 3.0 |
| Tipo | ransomware |
| Pequena descrição | os arquivos do usuário são criptografados e inutilizável. |
| Os sintomas | Uma nota de resgate é exibida à vítima. |
| distribuição Método | Via anexos maliciosos. |
| Ferramenta de detecção |
Veja se o seu sistema foi afetado por malware
Baixar
Remoção de Malware Ferramenta
|
| Experiência de usuário | Participe do nosso fórum para discutir CryptoWall 3.0. |
Os novos recursos de CryptoWall 3.0
New Tor para gateways Web são utilizados pela nova versão do CryptoWall: torman2.com, torforall.com, torroadsters.com, e torwoman.com. Qualquer um deles redireciona a vítima para a mesma página web que contém as instruções de pagamento, mas os IDs para rastrear os pagamentos são únicos.
O prazo de pagamento é alargado de cinco dias para uma semana inteira, após o qual a taxa é elevada para $1000.
Os criminosos criaram arquivos adicionais contendo informações sobre o pagamento e a restauração dos dados criptografados:
- HELP_DECRYPT.HTML: usa o seu navegador da Web para exibir informações sobre a ameaça, métodos de criptografia e de pagamento
- HELP_DECRYPT.PNG: contém detalhes sobre CryptoWall 3.0
- HELP_DECRYPT.TXT: o mesmo que o anterior, mas em texto simples
- HELP_DECRYPT.URL: usa seu navegador atual para exibir o CryptoWall 3.0 Serviço Decrypt quando o Windows é carregado
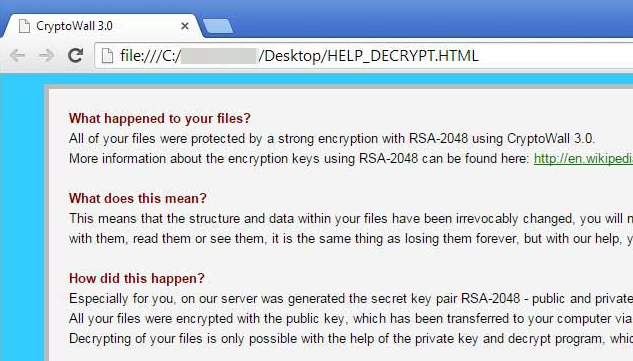
A mensagem de resgate exibido pelo CryptoWall 3.0 lê:
O que aconteceu com seus arquivos?
Todos os seus arquivos eram protegidos por uma criptografia forte com RSA-2048 usando CryptoWall 3.0.
Mais informações sobre as chaves de criptografia usando RSA-2048 pode ser encontrada aqui: https://en.wikipedia.org/wiki/RSA_(cryptosystem)O que isto significa?
Isto significa que a estrutura e os dados dentro de seus arquivos foram irrevogavelmente mudou, você não será capaz de trabalhar com eles, lê-los ou vê-los, é a mesma coisa que perdê-los para sempre, mas com a nossa ajuda, você pode restaurá-los.Como isso aconteceu?
Especialmente para você, no nosso servidor foi gerado o par chave secreta RSA-2048 – público e privado.
Todos os seus arquivos foram criptografados com a chave pública, que foi transferido para o seu computador através da Internet.
Descriptografia de seus arquivos só é possível com a ajuda da chave privada e programa de descriptografar, que é em nosso servidor secreto.
O que eu faço?
ai, se você não tomar as medidas necessárias para o tempo especificado, em seguida, as condições para obter a chave privada será alterado.
Se você realmente valoriza os seus dados, então sugerimos que você não perca valioso tempo pesquisando para outras soluções, porque eles não existem.
Uma vez que o processo de arquivo de criptografia é longo, os arquivos originais são excluídos. No caso de você não tem um backup de seus arquivos, você poderia usar um software confiável para restaurá-los ou parte deles a partir das cópias de sombra do Windows. Abaixo você encontrará instruções detalhadas sobre como fazê-lo.
Conexão com I2P falha
A nova versão do CryptoWall foi detectado por especialistas em segurança da Microsoft e do pesquisador francês Kafeine, que relatou que a comunicação com o C&C (Comando e controle) servidor é codificada com o algoritmo RC4 e usa o protocolo I2P.
Como Kafeine tentou testar a amostra da nova ameaça, ele recebeu uma mensagem de erro cada vez que ele tentou se conectar aos proxies. a notificação, o pesquisador recebeu, afirmou que o site do I2P não estava disponível devido a várias razões - incapacidade de se conectar a sistemas ou a rede está congestionada. Os hackers pareciam estar pronto para casos como este, porque eles têm fornecido instruções detalhadas sobre como obter acesso ao serviço de decodificação na rede Tor.

Cryptowall 3.0 Novos métodos de distribuição (setembro 4, 2015)
Como é Cryptowall 3.0 largados no sistema?
ransomware Cryptowall tem sido em torno de tempo suficiente para pesquisadores para reunir informações detalhadas sobre seus métodos. O ransomware é distribuída principalmente via e-mails com anexos .ZIP. O último conter arquivos executáveis mascarados como PDFs. Os arquivos em questão pode ser qualquer forma de comunicação empresarial como:
- Faturas
- Ordens de compra (OP)
- Contas
- reclamações
Uma vez que o PDF malicioso é lançado, CryptoWall será instalado no sistema. Os arquivos maliciosos será localizado em uma das duas pastas %Dados do aplicativo% ou %temp%. Então, a ameaça vai começar a digitalizar os drivers do sistema para encontrar arquivos para criptografar. Todas as letras de unidade será digitalizado, unidades de remoção, compartilhamentos de rede e Dropbox mapeamento incluiu. Qualquer letra de unidade no sistema infectado serão verificados para arquivos de dados.
Aqui está uma lista de todos os locais onde CryptoWall 3.0 pode ser situado:
- %temp%
- C:\[aleatória]\[aleatória].Exe
- %Dados do aplicativo%
- %Dados do Programa%
- %LocalAppData%

Posso encontrar os arquivos criptografados por CryptoWall 3.0?
Arquivos criptografados por CryptoWall 3.0 serão armazenados juntamente com os seus caminhos no Registro do Windows. A localização subchave está no seguinte formato:
→HKCU Software [ID de computador exclusivo]\[aleatório ID]
Um exemplo olhares reais como essa:
→HKCU Software 03DA0C0D2383CCC2BC8232DD0AAAD117 01133428ABDEEEFF
O processo será repetido para cada arquivo criptografado na chave mencionado.
ListCwall pode ser usado como bem. É uma ferramenta criada por Bleeping computador para automatizar a descoberta e exportação de arquivos criptografados. A ferramenta também pode fazer o backup dos arquivos bloqueados para outro local, no caso do usuário precisa arquivá-los e reformatar o PC.
Além disso, aqui está uma lista com as extensões de arquivo que CryptoWall 3.0 procura para criptografar:
→ .3dm, .3ds, .3fr, .mcmeta, .vfs0, .mpqge, .kdb, .DB0, .dba, .rofl, .hkx, .Barra, .UPK, .o, .iwi, .litemod, .de ativos, .forja, .ltx, .BSA, .apk, .RE4, .sav, .lbf, .SLM, .bik, .epk, .rgss3a, .em seguida, .grande, carteira, .wotreplay, .xxx, .desc, .py, .m3u, .flv, .js, .css, .rb, .png, .jpeg, .TXT, .P7C, .P7B, .p12, .pfx, .estab, .crt, .cer, .o, .X3F, .SRW, .PFE, .ptx, .r3d, .RW2, .RWL, .cru, .raf, .ORF, .NRW, .mrwref, .mef, .erf, .kdc, .dcr, .CR2, .CRW, .baía, .SR2, .SRF, .ganho dia, .3fr, .DNG, .3g2, .3gp, .3por, .7de, .AB4, .ACCDB, .sql, .mp4, .7de, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .fecho eclair, .eles, .soma, .iBank, .t13, .t12, .QDF, .gdb, .imposto, .pkpass, .bc6, .BC7, .PKP, .QIC, .bkf, .SIDN, .são, .mddata, .itl, .ITDB, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .syncdb, .gho, .caso, .SVG, .mapa, .OMM, .ITM, .sb, .fos, .mov, .vdf, .ztmp, .sis, .sid, .NCF, .cardápio, .traçado, .dmp, .gota, .esm, .vcf, .VTF, .dazip, .fpk, .MLX, .KF, .IWD, .vpk, .tor, .psk, .aro, .w3x, .FSH, .NTL, .arch00, .lvl, .SNX, .cf., .ff, .vpp_pc, .LRF, .m2, .JPE, .jpg, .cdr, .indd, .para, .eps, .pdf, .PDD, .psd, .dbf, .mdf, .WB2, .rtf, .wpd, .dxg, .xf, .dwg, .PST, .ACCDB, .mdb, .pptm, .PPTX, .ppt, .XLK, .xlsb, .xlsm, .xlsx, .xls, .wps, .docm, .docx, .doutor, .odb, .episódio, .odm, .responder, .ods, .odt, .ACCDE, .accdr, .accdt, .mas, .acr, .Aja, .adb

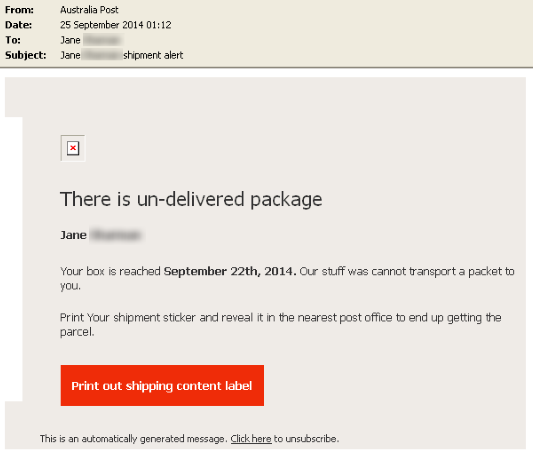
Comportamento do usuário e ransomware. Os golpes de phishing
O que descrevemos sobre os métodos de distribuição até agora só pode significar uma coisa - os criminosos apenas contar com a interação do usuário com o spam malicioso. O método é conhecido como phishing - uma forma de engenharia social, muitas vezes implantado a malware propagação ou as credenciais do usuário a cobrar. Este é um e-mail exemplar de como o esquema pode aparecer para os usuários:
image Source: Symantec

Dicas precaução Cryptowall
Para infecções maliciosas de bypass, evitar o download de arquivos de arquivo, tais como .fecho eclair, .jarra, .leva, .7de, .msi, e executável / script arquivos como .com, .Exe, .scr, .bastão, .js, .JSE, .vb, .vbe, .wsf, .wsh, .cmd. Tenha sempre em mente que as empresas reais seria evitar o envio de tais tipos de arquivos, a menos que você tinha um conjunto de marcação prévia.
Além disso, você pode usar serviços de classificação website online, tais como Norton Safe Web para determinar se um site é seguro ou inseguro para visita. Com ameaças de arquivos com criptografia, o melhor conselho de precaução é muito simples. Faça back up de seus arquivos. Aways acha dessa, especialmente quando seus dados são valiosos e você manter um monte de documentos de negócios em seu PC.
Você também pode conferir o dicas gerais de precaução temos em nosso fórum sobre ransomware, que vêm com força total para CryptoWall 3.0 também.
- IMPORTANTE
CryptoWall 3.0 pode criptografar arquivos em um compartilhamento de rede no caso de ser mapeada como uma letra de unidade. Se o compartilhamento de rede não está mapeada como tal, CryptoWall 3.0 não afetará os arquivos localizados lá. Para garantir ações abertas, os usuários podem permitir acesso somente gravável para os grupos de usuários necessário ou usuários autorizados. A ponta é muito importante quando se trata de ameaças como CryptoWall.

Remover CryptoWall 3.0 e restaurar os arquivos criptografados
Siga as instruções fornecidas abaixo para remover todos os vestígios deste ransomware. Tenha em mente que a melhor e mais segura maneira de fazer isso é usando um programa anti-malware forte.
- Degrau 1
- Degrau 2
- Degrau 3
- Degrau 4
- Degrau 5
Degrau 1: Scan for CryptoWall 3.0 com SpyHunter Anti-Malware Ferramenta



Remoção automática de ransomware - Guia de Vídeo
Degrau 2: Desinstalar CryptoWall 3.0 e malware relacionado do Windows
Aqui é um método em alguns passos simples que deve ser capaz de desinstalar a maioria dos programas. Não importa se você estiver usando o Windows 10, 8, 7, Vista ou XP, esses passos vai começar o trabalho feito. Arrastando o programa ou a sua pasta para a lixeira pode ser um muito má decisão. Se você fizer isso, pedaços e peças do programa são deixados para trás, e que pode levar a um trabalho instável do seu PC, erros com as associações de tipo de arquivo e outras atividades desagradáveis. A maneira correta de obter um programa fora de seu computador é para desinstalá-lo. Fazer isso:


 Siga as instruções acima e você excluirá com sucesso a maioria dos programas maliciosos e indesejados.
Siga as instruções acima e você excluirá com sucesso a maioria dos programas maliciosos e indesejados.
Degrau 3: Limpe quaisquer registros, criado por CryptoWall 3.0 no seu computador.
Os registros normalmente alvo de máquinas Windows são os seguintes:
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion Run
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion Run
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion RunOnce
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion RunOnce
Você pode acessá-los abrindo o editor de registro do Windows e excluir quaisquer valores, criado por CryptoWall 3.0 lá. Isso pode acontecer, seguindo os passos abaixo:


 Gorjeta: Para encontrar um valor criado-vírus, você pode botão direito do mouse sobre ela e clique "Modificar" para ver qual arquivo é definido para ser executado. Se este é o local do arquivo de vírus, remover o valor.
Gorjeta: Para encontrar um valor criado-vírus, você pode botão direito do mouse sobre ela e clique "Modificar" para ver qual arquivo é definido para ser executado. Se este é o local do arquivo de vírus, remover o valor.
Antes de começar "Degrau 4", por favor Arrancar de novo para o modo Normal, no caso em que você está no Modo de Segurança.
Isto irá permitir-lhe instalar e uso SpyHunter 5 com sucesso.
Degrau 4: Inicializar o PC Em modo de segurança para isolar e remover CryptoWall 3.0





Degrau 5: Tente restaurar arquivos criptografados por CryptoWall 3.0.
Método 1: Use o STOP Decrypter da Emsisoft.
Nem todas as variantes deste ransomware pode ser descriptografado gratuitamente, mas nós adicionamos o decryptor utilizado por pesquisadores que é frequentemente atualizado com as variantes que se tornam, eventualmente descriptografado. Você pode tentar e descriptografar seus arquivos usando as instruções abaixo, mas se eles não funcionam, então, infelizmente, a sua variante do vírus ransomware não é decryptable.
Siga as instruções abaixo para usar o decrypter Emsisoft e descriptografar os arquivos de graça. Você pode baixar a ferramenta de decodificação Emsisoft ligados aqui e depois seguir os passos apresentados abaixo:
1 Botão direito do mouse na decrypter e clique em Executar como administrador como mostrado abaixo:

2. Concordo com os termos de licença:

3. Clique em "Adicionar pasta" e em seguida, adicione as pastas onde deseja que os arquivos descriptografado como debaixo mostrado:

4. Clique em "Decrypt" e esperar por seus arquivos para ser decodificado.

Nota: Crédito para o decryptor vai para pesquisadores Emsisoft que fizeram a descoberta com este vírus.
Método 2: Use software de recuperação de dados
infecções ransomware e CryptoWall 3.0 apontar para criptografar seus arquivos usando um algoritmo de criptografia que podem ser muito difíceis de decifrar. É por isso que sugeriram um método de recuperação de dados que podem ajudá-lo a ir descriptografia torno direta e tentar restaurar seus arquivos. Tenha em mente que este método pode não ser 100% eficaz, mas também pode ajudá-lo um pouco ou muito em situações diferentes.
Basta clicar no link e nos menus do site na parte superior, escolher Recuperação de dados - Assistente de Recuperação de Dados para Windows ou Mac (dependendo do seu SO), e depois baixe e execute a ferramenta.
CryptoWall 3.0-FAQ
O que é CryptoWall 3.0 ransomware?
CryptoWall 3.0 é um ransomware infecção - o software malicioso que entra no computador silenciosamente e bloqueia o acesso ao próprio computador ou criptografa seus arquivos.
Muitos vírus ransomware usam algoritmos de criptografia sofisticados para tornar seus arquivos inacessíveis. O objetivo das infecções por ransomware é exigir que você pague um pagamento por resgate para ter acesso aos seus arquivos de volta.
What Does CryptoWall 3.0 Ransomware Do?
O ransomware em geral é um software malicioso que é projetado para bloquear o acesso ao seu computador ou arquivos até que um resgate seja pago.
Os vírus ransomware também podem danificar seu sistema, corromper dados e excluir arquivos, resultando na perda permanente de arquivos importantes.
How Does CryptoWall 3.0 Infectar?
De várias maneiras.CryptoWall 3.0 O ransomware infecta computadores sendo enviados através de e-mails de phishing, contendo anexo de vírus. Esse anexo geralmente é mascarado como um documento importante, gostar uma fatura, documento bancário ou até mesmo uma passagem de avião e parece muito convincente para os usuários.
Another way you may become a victim of CryptoWall 3.0 is if you baixe um instalador falso, crack ou patch de um site de baixa reputação ou se você clicar em um link de vírus. Muitos usuários relatam ter recebido uma infecção por ransomware baixando torrents.
How to Open .CryptoWall 3.0 arquivos?
Vocês can't sem um descriptografador. Neste ponto, a .CryptoWall 3.0 arquivos são criptografado. Você só pode abri-los depois de descriptografados usando uma chave de descriptografia específica para o algoritmo específico.
O que fazer se um descriptografador não funcionar?
Não entre em pânico, e faça backup dos arquivos. Se um decodificador não decifrar seu .CryptoWall 3.0 arquivos com sucesso, então não se desespere, porque esse vírus ainda é novo.
posso restaurar ".CryptoWall 3.0" arquivos?
sim, às vezes os arquivos podem ser restaurados. Sugerimos vários métodos de recuperação de arquivos isso poderia funcionar se você quiser restaurar .CryptoWall 3.0 arquivos.
Esses métodos não são de forma alguma 100% garantido que você será capaz de recuperar seus arquivos. Mas se você tiver um backup, suas chances de sucesso são muito maiores.
How To Get Rid of CryptoWall 3.0 Vírus?
A maneira mais segura e eficiente de remover esta infecção por ransomware é o uso de um programa anti-malware profissional.
Ele irá procurar e localizar CryptoWall 3.0 ransomware e, em seguida, remova-o sem causar nenhum dano adicional ao seu .CryptoWall importante 3.0 arquivos.
Posso denunciar ransomware às autoridades?
Caso seu computador tenha sido infectado por uma infecção de ransomware, você pode denunciá-lo aos departamentos de polícia locais. Ele pode ajudar as autoridades em todo o mundo a rastrear e determinar os autores do vírus que infectou seu computador.
Abaixo, preparamos uma lista com sites governamentais, onde você pode registrar uma denúncia caso seja vítima de um cibercrime:
Autoridades de segurança cibernética, responsável por lidar com relatórios de ataque de ransomware em diferentes regiões em todo o mundo:
Alemanha - Portal oficial da polícia alemã
Estados Unidos - IC3 Internet Crime Complaint Center
Reino Unido - Polícia de Fraude de Ação
França - Ministro do interior
Itália - Polícia Estadual
Espanha - Policia Nacional
Países Baixos - Aplicação da lei
Polônia - Polícia
Portugal - Polícia Judiciária
Grécia - Unidade de crime cibernético (Polícia Helênica)
Índia - Polícia de Mumbai - Célula de investigação do CyberCrime
Austrália - Centro de crime de alta tecnologia australiano
Os relatórios podem ser respondidos em prazos diferentes, dependendo das autoridades locais.
Você pode impedir que o ransomware criptografe seus arquivos?
sim, você pode prevenir o ransomware. A melhor maneira de fazer isso é garantir que o sistema do seu computador esteja atualizado com os patches de segurança mais recentes, use um programa anti-malware confiável e firewall, faça backup de seus arquivos importantes com frequência, e evite clicar em links maliciosos ou baixando arquivos desconhecidos.
Can CryptoWall 3.0 Ransomware Steal Your Data?
sim, na maioria dos casos ransomware roubará suas informações. It is a form of malware that steals data from a user's computer, criptografa isso, e depois exige um resgate para descriptografá-lo.
Em muitos casos, a autores de malware ou invasores ameaçarão excluir os dados ou publicá-lo on-line a menos que o resgate seja pago.
O ransomware pode infectar WiFi?
sim, ransomware pode infectar redes WiFi, como agentes mal-intencionados podem usá-lo para obter o controle da rede, roubar dados confidenciais, e bloquear usuários. Se um ataque de ransomware for bem-sucedido, pode levar a uma perda de serviço e/ou dados, e em alguns casos, perdas financeiras.
Devo Pagar Ransomware?
Não, você não deve pagar extorsionários de ransomware. Pagá-los apenas incentiva os criminosos e não garante que os arquivos ou dados sejam restaurados. A melhor abordagem é ter um backup seguro de dados importantes e estar atento à segurança em primeiro lugar.
What Happens If I Don't Pay Ransom?
If you don't pay the ransom, os hackers ainda podem ter acesso ao seu computador, dados, ou arquivos e pode continuar ameaçando expô-los ou excluí-los, ou mesmo usá-los para cometer crimes cibernéticos. Em alguns casos, eles podem até continuar a exigir pagamentos de resgate adicionais.
Um ataque de ransomware pode ser detectado?
sim, ransomware pode ser detectado. Software antimalware e outras ferramentas de segurança avançadas pode detectar ransomware e alertar o usuário quando está presente em uma máquina.
É importante manter-se atualizado sobre as medidas de segurança mais recentes e manter o software de segurança atualizado para garantir que o ransomware possa ser detectado e evitado.
Os criminosos de ransomware são pegos?
sim, criminosos de ransomware são pegos. Agências de aplicação da lei, como o FBI, A Interpol e outras empresas tiveram sucesso em rastrear e processar criminosos de ransomware nos EUA e em outros países. Como as ameaças de ransomware continuam a aumentar, o mesmo acontece com a atividade de fiscalização.
Sobre o CryptoWall 3.0 Pesquisa
O conteúdo que publicamos em SensorsTechForum.com, esta CryptoWall 3.0 guia de como fazer a remoção incluído, é o resultado de uma extensa pesquisa, trabalho árduo e a dedicação de nossa equipe para ajudá-lo a remover o malware específico e restaurar seus arquivos criptografados.
Como conduzimos a pesquisa sobre este ransomware?
Nossa pesquisa é baseada em uma investigação independente. Estamos em contato com pesquisadores de segurança independentes, e como tal, recebemos atualizações diárias sobre as definições de malware e ransomware mais recentes.
além disso, a pesquisa por trás do CryptoWall 3.0 ameaça de ransomware é apoiada com VirusTotal e a projeto NoMoreRansom.
Para entender melhor a ameaça do ransomware, por favor, consulte os seguintes artigos que fornecem detalhes conhecedores.
Como um site dedicado a fornecer instruções gratuitas de remoção de ransomware e malware desde 2014, A recomendação do SensorsTechForum é preste atenção apenas a fontes confiáveis.
Como reconhecer fontes confiáveis:
- Sempre verifique "Sobre nós" página da web.
- Perfil do criador do conteúdo.
- Certifique-se de que pessoas reais estejam por trás do site e não nomes e perfis falsos.
- Verifique o Facebook, Perfis pessoais no LinkedIn e no Twitter.



grande informação! Eu estava infectado com o “3,0 CRYPTOWALL” vírus recentemente, foi baixado da minha necessidade de download do Google Chrome e as últimas Chromecast. Ele continuou a baixar malware que foi muito perturbador. Se você já ouviu falar sobre isso acontecer quando o Google Chrome foi instalado, você poderia por favor dá-lo a todos os seus seguidores.
Obrigado e cumprimentos!
greg
Olá a todos aqui é uma solução, como proteger seus arquivos e documentos deste vírus CryptoWall
youtube.com/ watch?v = kRpJEpJzK1U
há Anticryptowall,
Tem a certeza de que seu método funciona?
Oi Milena Dimitrova
eu fiz essa experiência tantas vezes em discos de imagem por vários vírus especialmente por vírus de criptografia eo resultado foi sempre positivo…
Oi de novo,
E sobre CryptoWall 3.0, em particular?
meu chefe foi atingido e sua memory stick foi criptografado. ele comprou um novo cartão de memória da SanDisk que veio com uma assinatura de um ano para “RescuePRO”e ele foi solicitado a recuperar arquivos-ele inseriu sua vara infectada eo software restaurado seus arquivos para sua nova vara e agora seus arquivos estão em um cofre seguro na nova vara.
por favor deixe-me saber se há alguma solução. I também foi pego por este ao tentar atualizar o Chrome. Eu estou na necessidade desesperada de uma solução como eu não tem nenhum backups. arquivo de cada Microsoft está infectado e descodificada
eu também. todos os meus arquivos não pode ser aberto.
Também comigo e eu também não restaure porque este recurso não está ligado no meu computador.
Por favor, alguém?
por favor, helppppppppp todos os meus arquivos foram protegidos por uma criptografia forte com RSA-2048.
Olá, Tony!
CryptoWall é realmente um pesadelo e lamentamos a ler que você tem sido afetado por ela. algoritmo RSA foi implantado por muitas ameaças ransomware. Você pode ter certeza que muitos usuários e especialistas em segurança têm vindo a tentar quebrar a criptografia RSA-2048. Mais informações sobre a chave de criptografia RSA-2048 que tem sido alvo computadores encontrar aqui: sensorstechforum.com/remove-rsa-2048-encryption-key-from-cryptowall-3-0/
RSA-2048 pode ser quebrado se alguém encontrar uma maneira de criar colisões que inerentemente reduzir o número esperado de combinações para quebrar a cifra. Sendo uma cifra, a RSA-2048 algoritmo pode ser quebrada pela força bruta. força bruta fissuração pode ser descrito como uma técnica de tentativa e erro empregado por programas de decifrar dados criptografados, como senhas e DES (Data Encryption Standard) chaves via amplo esforço em vez de força intelectual.
criptografia RSA é um tipo de linguagem que altera o Código normal do arquivo com uma chave única. Essa chave pode ser decifrado através de software específico, mas requer uma máquina poderosa. Mais sobre o tema criptografia RSA e como remover manualmente CryptoWall: sensorstechforum.com/restore-files-encrypted-via-rsa-encryption-remove-cryptowall-and-other-ransomware-manually/
Finalmente, a nossa equipa de investigação compilou alguns passos simples a seguir para proteger seus arquivos de ameaças ransomware: sensorstechforum.com/cryptowall-aaa-files-ransomware-description-protection-and-removal/
Além disso, se você quiser saber mais sobre os métodos empregados por CryptoWall e os criminosos por trás dele, você pode se referir a este artigo: blog.trendmicro.com/trendlabs-security-intelligence/cryptowall-3-0-ransomware-partners-with-fareit-spyware/
obrigado, Eu removi o vírus com SpyHunter mas meus arquivos ainda estão corrompidos e eu não posso abri-los. Por favor me ajude… como consertá-los????
TODOS VOCÊS SOOO PARAFUSOU…
Com arquivo original, arquivo criptografar e chave pública usada para criptografar arquivos, você pode decifrar outros arquivos que usou essa chave pública?
Eu tenho todas as minhas unidades de dados criptografados por cryptowall 3.0 através ransomware(conhost) e tinha enda criptografar meu backup gendanelsespunkter ea única maneira que eu tenho o meu perfil sua volta estava usando Recuva desde arquivo original sleter cryptowall e substitui-los com um criptografado
Tenho arquivos que não podem ser abertos também.
Estou indo para pagar o resgate hoje ou amanhã.
Ouvi dizer que, se pagar o resgate das desbloquear todos os arquivos com certeza (99% certo).
Eles não querem que os arquivos. Eles só querem o dinheiro.
I tentar de tudo para desbloquear meus arquivos. Mesmo novo software karpersky. Nada funciona.
Será que alguém tem a mesma experiência?
Será que alguém pagar o resgate antes?
O que aconteceu?
Vou deixar a minha experiência aqui em breve.
João oi,
Em primeiro lugar, muito em ouvir que você sofreu um CryptoWall 3.0 ataque!
Você pode por favor iniciar um tópico no nosso fórum – sensorstechforum.com/fóruns / malware-remoção-perguntas-e-guias /? Vamos tentar ajudá-lo com tudo o que pudermos. Os fóruns são mais convenientes para tais discussões :)
Fique ligado,
a equipe STF
João oi,
Você pagá-lo? Qual o resultado?
Eu tenho o mesmo problema, mas eu estou tentando resolvê-lo..
Olá João, trabalho como técnico em uma empresa e um dos gerentes, Ela foi atacada por este vírus, Gostaria de saber se você poderia recuperar a informação depois de fazer o pagamento, ea quantidade de informações, poderia recuperar?
ter pago-los >?? e recuperou seus arquivos ou não ?
boa tarde, meu caso é que o computador foi infectado com o vírus, formatar o computador, mas toda a informação aberta. Tenho informações de vida e morte e insta me recuperar. alguém que pode me ajudar. por favor
Hmm..
você pode devolver o sistema de volta, mas é apenas possível ter backup de destino antes.
Não é- Você pode baixar Quelch do programa de Recuperação como Recuva ,getdatabach ou diskdrill..però, Infelizmente, esse tipo de software não é o recuperanno 100% ,Apenas os dados apagados recentemente . aqui está um desses programas cleverfiles.com/disk-drill-windows.html
Você pode ajudá-lo,
Olá, Fornerino
No caso de ter sido infectado com Cryptowall, é importante saber que ele usa um algoritmo MUITO forte, chamado RSA-2048. Sua descriptografia pode levar anos para ser concluído. Aconselhamo-lo a tentar restaurar seus arquivos por ir a um especialista em recuperação de dados profissional ou tentar usar em uma das ferramentas aftermentioned:
Kaspersky Reitor Decryptor
Esta ferramenta de decodificação é muito simples de usar e
support.kaspersky.com/viruses/utility#rectordecryptor” support.kaspersky.com/viruses/utility#rectordecryptor
EaseUS Data Recovery Wizard grátis
Aqui é um programa gratuito que utiliza métodos diferentes para procurar através do seu computador e recuperar arquivos que estão ainda excluídos além de toda a poupança. Não é nenhuma garantia de que ele vai trabalhar, mas alguns dizem terem recuperado pelo menos 10 por cento dos seus arquivos e alguns outros arquivos foram parcialmente quebrado. Assim, no caso de você querer experimentá-lo, aqui está o link de download para a ferramenta:
easyus.com/datarecoverywizard/free-data-recovery-software.htm
easyus.com/datarecoverywizard/free-data-recovery-software.htm
Explorador sombra
Assim como você pode tentar executar Sombra Explorer no caso de você ter Arquivo Histórico ou backup habilitado. Você pode baixá-lo aqui, Mas note que TeslaCrypt pode também ter scripts maliciosos que excluir quaisquer cópias de segurança e versões de arquivos anteriores. Aqui está o link para download Sombra Explorador:
shadowexplorer.com/downloads.html
shadowexplorer.com/downloads.html
Procure a versão mais recente e você pode também baixar a um portátil, uma vez que poupa tempo.
Isto é, tanto quanto eu posso sugerir, experimentá-lo e responder se quer ou não ter sido bem sucedida. Novamente, não há absolutamente nenhuma garantia de que qualquer um dos métodos estão trabalhando, mas estamos falando de arquivos criptografados aqui, depois de tudo por isso pode ser vale a pena tentar.
Meus todos os arquivos são criptografados com RSA-4096.
Eu não posso abrir qualquer file.They estão pedindo 500 USD para chave de decodificação. Por favor, alguém pode me ajudar a decifrar meus arquivos como eu não tenho restaurar qualquer backup.
o Trabalho,
Primeiro, você pode por favor me diga como você tem que saber que RSA-4096 foi usada no seu caso?
SLT Milena!
Como você está indo? Eu gostaria de algumas idéias sobre criptografia, como ele vai, tem um caso prático!
Agradecemos antecipadamente! Deixo meu e-mail ou se eu posso ter seu que eu serei uma grande utilidade
oi Milena..
Eu encontrei um arquivo ransomware em cada minha pasta…
o Trabalho, olhando para o seu caso como nós falamos!
Caro Milena,
Esperando por sua ajuda….a sua resposta anterior será favorável.
obrigado
o Trabalho,
Um tópico foi iniciada em nosso fórum sobre a criptografia especial: sensorstechforum.com/forums/malware-removal-questions-and-guides/help!-meus-arquivos-foram-criptografados-com-criptografia-rsa-4096-forte!/msg679 / # msg679
Por favor, nos fornecer as seguintes informações não (é mais fácil discutir no fórum do que aqui) – Seu sistema, extensões de arquivo exatas adicionados aos arquivos criptografados, notas de resgate, etc. Além disso, tê-lo removido do Trojan que caiu o ransomware?
Olá SERAS,
Eu estou bem, mas muito triste de ver tantas pessoas caem vítimas ransomware. Você pode nos enviar informações sobre seu caso de ransomware em idunn0 @ abv.bg.
Todos os meus arquivos estão com extensão vvv decrypting não sei como eu estou muito preocupado por favor ajudar a remover Cryptowall e ter todas as minhas informações criptografadas 20 anos de trabalho ajuda por favor
oi Jorge,
Lamento profundamente para que você saiba que, sem uma cópia limpa de seus arquivos, você provavelmente não será capaz de restaurar suas informações. Você pode tentar usar TeslaDecoder e Rakhnidecryptor. Contudo, relatórios indicam que estes decodificadores não vai ajudar com a extensão .vvv que pertence a TeslaCrypt ransomware: sensorstechforum.com/remove-teslacrypt-and-restore-vvv-encrypted-files/
Você removeu o ransomware com um programa anti-malware?
E’ aconteceu-me. o problema’ que cada arquivo tem uma extensão diferente 0A / 0A1 / OMF ECC
você pode’ fazer alguma coisa?
Oi, Eu também peguei esse vírus, mas foi só muito tarde que eu percebi isso e agora todos os meus arquivos são criptografados com RSA-2048. As extensões de arquivo foram alteradas e parece que a extensão para cada arquivo é diferente de qualquer outro e nenhum é o mesmo. Alguns do arquivo extensões que vejo agora são .p468t,.16G, .n7r0, .Us7m, .25sq, .xo3r4 e tantos mais. eu preciso de ajuda.
Olá @dbgn
Isto é típico para infecções ransomware como CTB Locker e CryptoWall 4.0. A fim para mim ser capaz de fornecê-lo adequadamente com a ajuda Eu gostaria que você me envie um recorte ou uma captura de tela de qualquer mensagem de resgate que você pode ver. Pode ser um arquivo .txt em seu desktop ou uma imagem.
sensorstechforum.com/forums/malware-removal-questions-and-guides/files-encrypted-with-random-file-extensions/
Olá , Os arquivos invierei , mas eu não sei ‘ como conectá-la a esta mensagem
Olá Vencislav
mz laptop está infectado com vírus ti teslacrzpt e todos os arquivos de mz são encrzpted com RSA-4096 key
poderia Zou ajuda me_ por favor
Oi, Amigos! Meu PC foi infectado, eu eliminar ransomware usando SpyHunter, mas os arquivos muy permanecer criptografados com .MICRO extensão. ¿Como posso descriptografar os arquivos? obrigado!!
Olá Ter,
Você foi infectado com uma variante do TeslaCrypt. Para mais informações confira o seguinte artigo:
sensorstechforum.com/remove-teslacrypt-3-0-and-restore-micro-encrypted-files/
Você também pode enviar arquivos para que possamos tentar ajudar a decifrar-los. Aqui é o endereço:
idunn0 @ abv.bg
Vamos divulgar seus arquivos e enviá-los de volta para você se decifrada com sucesso. Tenha em mente que uma vez que recebem uma grande quantidade de arquivos que ele pode levar algum tempo.
oi Milena , um dos nosso sistema foi infectado com este cryptowall 3 e criptografado os arquivos com extensão .micro. Eu era capaz de remover o malware, mas depois de dois dias, um de nossos armazenamento anexado à rede foi afetada também. Agora eu estou querendo saber como isso é possível ? Eu pensei que apenas os arquivos pessoais foi afetada por este script.
Olá Shihas,
Ransomware é frequentemente usado em ataques a empresas. A má notícia é que ainda não há solução para .micro arquivos criptografados. Nós asseguramo-lo, porém, que os especialistas em segurança (nós incluídos) estão fazendo o seu melhor para combater esta ameaça e bater sua criptografia.
instalei um software. depois do meu .jpg,.Os arquivos mp4 são alterados para uma extensão .micro .pls ajudam a como obter meu formato de arquivo antigo .
oi Nani,
Infelizmente, você tem sido atacado pela última versão do TeslaCrypt ransomware. Ainda estamos tentando descobrir como decifrar arquivos criptografados por ela. Uma vez que encontrar uma solução, vamos compartilhá-lo.
Você removeu o ransomware do computador infectado?
Olá! Meu laptop está infectado com Cryptowall3.0. Eu limpo-o, mas todos os meus arquivos são criptografados. Qualquer notícia sobre como dectrypt-los?
Obrigado!
Deve-se notar que a Europol tomou conhecimento do problema do ransomware e agora oferece um portal online para ajudar as vítimas secuweb.fr/europol-portail-lutter-ransomwares
muito obrigado :)
Eu removi o ransomware mas os arquivos agora eu tenho criptografados terminando com .albigec. Alguém agora como para descriptografar os arquivos? (Cryptowall 3.0)
Meus arquivos são criptografados com RSA2048 algoritmo ransomware. Eu preciso de um decodificador para este imediatamente. Por favor ajude
Oi,
Meus arquivos foram criptografados no caminho de volta 2015 ( por Cryptowall 3.0) Eu ainda tenho os arquivos com me e as instruções para pagar e recuperar meus arquivos. Existe alguma maneira de recuperar esses arquivos através de meios gratuitos ou pagos?
oi Naveen,
Infelizmente, Neste caso ransomware permanece sem solução, como nenhuma decrypter oficial foi lançado até hoje.
Oi, existe uma boa solução para criptografar meus arquivos antes de enviá-los aos meus colaboradores, como você sabe que somos obrigados a trabalhar em casa ? Muito Obrigado.