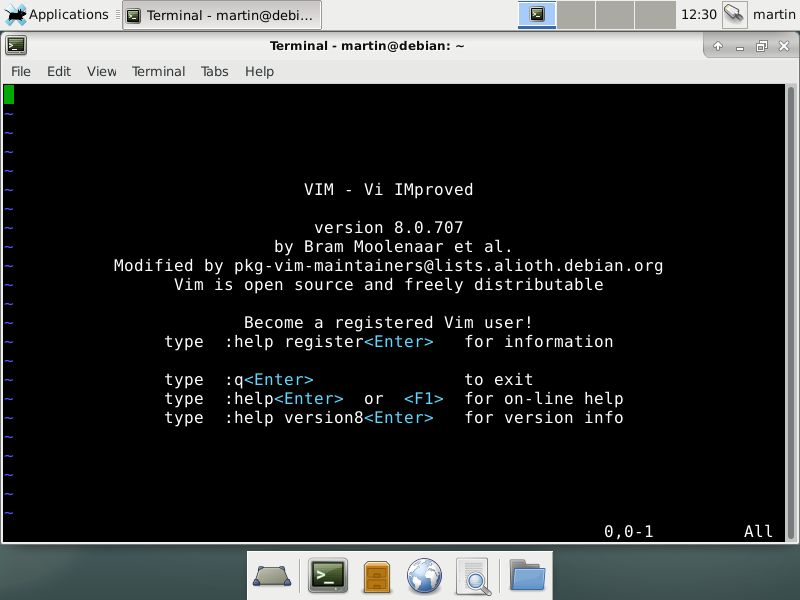
Den populære Linux-redaktører Vim og Neovim har vist sig at indeholde en meget farlig fejl, som spores i CVE-2019-12.735 rådgivende. Dets udnyttelse gør det muligt for hackere at udføre vilkårlig kode på det pågældende operativsystem.
Den Vim og uautoriseret teksteditorer til Linux har vist sig at have en stor svaghed gør det muligt for hackere at udføre vilkårlig kode, denne fejl bliver sporet i CVE-2019-12.735 rådgivende. Grunden til dette er et stort problem, fordi de er bredt forudinstalleret på offer-systemer. De bruges både af slutbrugere, administratorer og udviklere for at redigere tekst og ringe til andre tredjeparts værktøjer og scripts.
Ved selv Vim og Neovim er en af de mest populære værktøjer, som de er polyvalent værktøjer og kan interagere med systemet ved hjælp af forskellige kroge og funktioner. Problemet i sig selv kommer fra den måde redaktionen interagerer med den såkaldte “modelines” - en funktion, som er indstillet til automatisk at finde og anvende brugerdefinerede indstillinger i dokumenterne. Sikkerheden fejl i Linux-versioner af Vim og Neovim viste sig at indeholde et usikkert udtryk giver ondsindede operatører at omgå programmets sandkasse.
Ved design applikationerne gør omfatte en sandkasse, som vil begrænse de programmer til at køre programmer, der er inde i et virtuelt isoleret miljø. Fejlen dokumenteret i CVE-2019-12.735 rådgivende viser, hvordan hackere kan overvinde det. Ifølge sikkerhedseksperter er der to mulige proof-of-concept udnytter, som kan dokumenteres i den virkelige verden scenarier. Konsekvenserne af disse trin er, at malware operatørerne kan vinde en omvendt shell. Alt de behøver er at gøre ofrene åbne en fil, der tidligere er blevet ændret. I god tid udviklerne har frigivet sikkerhedsopdateringer til applikationerne. Brugere bør opdatere deres ansøgninger så hurtigt som muligt. Men for at sikre, at de er beskyttet til det maksimale de sikkerhedseksperter tyder også på, at følgende handlinger er iværksat:
- deaktivere modelines har
- deaktivere “modelineexpr”
- ansætte securemodelines plugin i stedet for de indbyggede modelines


