The popular Linux editors Vim and Neovim have been found to contain a very dangerous flaw which is tracked in the CVE-2019-12735 advisory. Its exploitation allows the hackers to execute arbitrary code on the affected operating system.
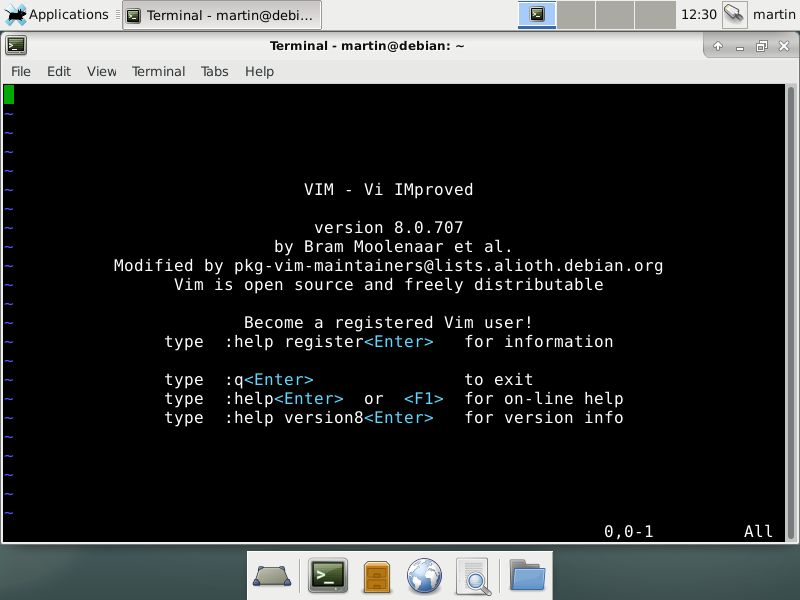
The Vim and Neovim text editors for Linux have been found to have a major weakness allowing the hackers to execute arbitrary code, this bug is being tracked in the CVE-2019-12735 advisory. The reason why this is a major issue is because they are widely pre-installed on victim systems. They are used both by end users, administrators and developers in order to edit text and call other third-party tools and scripts.
By themselves Vim and Neovim are one of the most popular tools as they are multipurpose tools and can interact with the system using various hooks and functions. The problem itself comes from the way the editors interact with the so-called “modelines” — a feature which is set to automatically find and apply custom preferences in the documents. The security bug in the Linux versions of Vim and Neovim were found to contain an unsafe expression allowing malicious operators to bypass the application’s sandbox.
By design the applications do include a sandbox which will limit the programs into running programs that are inside a virtual isolated environment. The flaw documented in the CVE-2019-12735 advisory shows how hackers can overcome it. According to the security researchers there are two possible proof-of-concept exploits that can be demonstrated in real-world scenarios. The consequences of these steps is that the malware operators can gain a reverse shell. All they need is to make the victims open up a file that was previously altered. In due time the developers have released security patches for the applications. Users should update their applications as soon as possible. However to make sure that they are protected to the maximum the security researchers also suggests that the following actions are undertaken:
- disable modelines feature
- disable “modelineexpr”
- employ the securemodelines plugin instead of the built-in modelines


