virus termite est un ransomware récemment découvert qui contient du code tiré de diverses armes de pirates informatiques populaires. Il utilise un chiffrement fort pour traiter les données utilisateur selon une liste intégrée des types de fichiers cible, ils sont renommés avec l'extension .aaaaaa. Notre article donne un aperçu des opérations de virus et il peut également être utile pour tenter de supprimer le virus.

Menace Résumé
| Nom | virus termite |
| Type | Ransomware, Cryptovirus |
| brève description | Le ransomware crypte les informations sensibles sur votre système informatique avec l'extension .aaaaaa et exige le paiement d'une rançon pour prétendument les récupérer.. |
| Symptômes | Le ransomware va chiffrer vos fichiers avec un algorithme de cryptage. |
| Méthode de distribution | spams, Email Attachments |
| Detection Tool |
Voir si votre système a été affecté par des logiciels malveillants
Télécharger
Malware Removal Tool
|
Expérience utilisateur | Rejoignez notre Forum pour discuter du virus Termite. |
| Outil de récupération de données | Windows Data Recovery Stellar Phoenix Avis! Ce produit numérise vos secteurs d'entraînement pour récupérer des fichiers perdus et il ne peut pas récupérer 100% des fichiers cryptés, mais seulement quelques-uns d'entre eux, en fonction de la situation et si oui ou non vous avez reformaté votre lecteur. |

Virus Termite - Moyens de distribution
Le virus Termite a été repéré lors d'une campagne de tests limitée. Il semble que les attaques actuelles semblent cibler les utilisateurs d'ordinateurs du monde entier. Les criminels peuvent utiliser diverses techniques afin de maximiser le nombre d'hôtes infectés.
Une méthode populaire est de coordonner campagnes de spam contenant diverses tactiques d'ingénierie sociale. Ils sont conçus pour apparaître comme des notifications légitimes telles que des rappels de mot de passe, messages de mise à jour du logiciel et etc.. Les fichiers de virus Termite associés peuvent être directement attachés ou liés dans le contenu du corps.
Une autre technique est l'utilisation de portails de téléchargement qui imitent les sites de téléchargement des fournisseurs légitimes et les portails Internet populaires.
Avec les e-mails, ces deux méthodes sont les principales méthodes de diffusion porteurs de charge utile infectés. Deux exemples de types sont les suivants:
- Documents macro-Infected - Les pirates peuvent intégrer la charge utile du virus dans des fichiers de documents de différents types: présentations, riches fichiers texte, feuilles de calcul et bases de données. Chaque fois qu'ils sont ouverts, une invite de notification apparaîtra leur demandant d'activer les scripts intégrés. Si cela est fait l'infection par le virus commencera.
- Les installateurs d'application - Les scripts menant à l'infection par le virus Termite peuvent être regroupés dans des programmes d'installation pour des applications populaires, mises à jour, plugins et etc. Les criminels choisissent souvent des logiciels populaires auprès des utilisateurs finaux: suites de créativité, utilitaires système et etc.
Les fausses pages de téléchargement, les e-mails et autres contenus susceptibles de diffuser la menace peuvent utiliser divers scripts - réoriente, pop-ups, bannières, en ligne et des liens, etc..
Des campagnes d'infection avancées peuvent être réalisées grâce à l'installation de redirections navigateur - ce sont des plugins malveillants conçus pour les navigateurs Web les plus populaires. Les criminels les diffusent généralement sur les différents référentiels ou téléchargent des portails. Les pirates publient les entrées avec de faux avis d'utilisateurs ou des informations d'identification de développeur afin de contraindre les utilisateurs à les télécharger.. Une méthode habituelle consiste à leur promettre de nouvelles fonctionnalités ou des améliorations de navigateur qui ne se trouvent généralement pas sur les navigateurs standard.. L'une des premières actions effectuées après l'infection est de rediriger les utilisateurs victimes vers un site contrôlé par un pirate informatique.. Cela se fait en modifiant les paramètres par défaut - page d'accueil, moteur de recherche et nouvelle page onglets. Après cela, les fichiers de virus seront déployés sur les systèmes.

Virus Termite - Analyse approfondie
L'analyse de sécurité du virus Termite montre que le code contient des échantillons de diverses menaces différentes: un mineur de pièces générique, le ransomware XiaaoBa et les opérations virales typiques. Cela montre que les criminels derrière cela peuvent avoir personnalisé leur propre variante ou l'avoir commandée sur les marchés clandestins des pirates informatiques.. L'inclusion du code XiaoBa montre que l'un des groupes cibles peut être des utilisateurs parlant chinois. Cependant, à cette date, les infections semblent cibler les utilisateurs à l'échelle mondiale.
Le moteur modulaire peut être affiné en fonction de chaque campagne. Il contient plusieurs composants différents appelés par étapes. L'une des premières actions menées par elle est une détournement d'informations commander. Il peut rechercher et identifier des chaînes regroupées en deux catégories principales:
- Renseignements personnels - Le moteur peut être programmé pour récolter des données qui peuvent révéler l'identité des victimes. Les informations collectées se composent généralement de leur nom, adresse, numéro de téléphone, emplacement et les informations d'identification de compte stockées. Les données peuvent être utilisées pour divers crimes de vol d'identité et d'abus financier.
- Mesures de la campagne - L'analyse montre que le moteur antivirus Termite recherche également les valeurs spécifiques du système d'exploitation et les composants matériels installés.
L'analyse montre que le moteur intégré peut présenter certains protection furtive Caractéristiques. Cela signifie qu'il recherche la présence de certains programmes antivirus, environnements de bac à sable ou des hôtes de machines virtuelles. Leurs moteurs en temps réel seront bloqués ou entièrement supprimés pour échapper à la découverte potentielle de l'infection.
Suite à cela, le moteur antivirus pourra commettre librement divers les modifications du système. Ils incluent des connexions à des processus système ou d'application qui permettent au virus Termite de récolter et de manipuler des chaînes et des commandes utilisateur.. D'autres manipulations peuvent inclure des modifications du Registre de Windows. Cela peut affecter à la fois les applications installées par l'utilisateur et le système d'exploitation dans son ensemble. Cela peut entraîner l'incapacité d'exécuter certains processus ou entraîner des problèmes de performances globales. Lorsqu'il est combiné avec les modifications du menu de démarrage, il peut conduire à un état persistant de l'installation - cela signifie qu'il démarrera automatiquement une fois l'ordinateur allumé. Habituellement, cela entraîne également l'incapacité de démarrer le menu de récupération, ce qui rend de nombreuses instructions de suppression manuelle inutiles.
De nombreuses infections peuvent être programmées en suppression des fichiers de restauration du système - les clichés instantanés de volume et les points de restauration peuvent être supprimés. Des opérations de restauration efficaces ne peuvent être effectuées que lorsqu'elles sont utilisées en combinaison avec une solution de restauration de qualité professionnelle. Reportez-vous à nos instructions pour plus de détails.
Le virus Termite peut également interagir avec le Windows Volume Manager - cela lui permet d'accéder à tous les périphériques de stockage amovibles et aux partages réseau. En conséquence, cela peut être utilisé comme une méthode puissante pour infecter des réseaux entiers. S'il est configuré de manière à ce que le ransomware puisse également fournir un Cheval de Troie infection. Il peut configurer une connexion sécurisée à un serveur contrôlé par un pirate informatique. Il permet aux criminels d'espionner les victimes en temps réel, Steel données des utilisateurs et prendre le contrôle de leurs machines.
L'analyse de sécurité montre que certaines infections par le virus Termite peuvent conduire au déploiement de minres de crypto-monnaie. Ce sont des applications spéciales qui tirent parti des ressources système disponibles pour réaliser des infections complexes. Lorsqu'ils sont signalés à un serveur spécial (piscine minière) les opérateurs de hackers recevront des récompenses sous forme de monnaie numérique (Bitcoin, Monero et d'autres).

Virus Termite - Chiffrement
À la fin de tous les modules précédents, le moteur de ransomware sera démarré. Comme la plupart des souches typiques, il utilise une liste intégrée de données cibles qui doivent être chiffrées avec un chiffrement fort. Une liste typique ciblera les types de fichiers suivants:
- Archives
- Bases de données
- sauvegardes
- Images
- Vidéos
- la musique
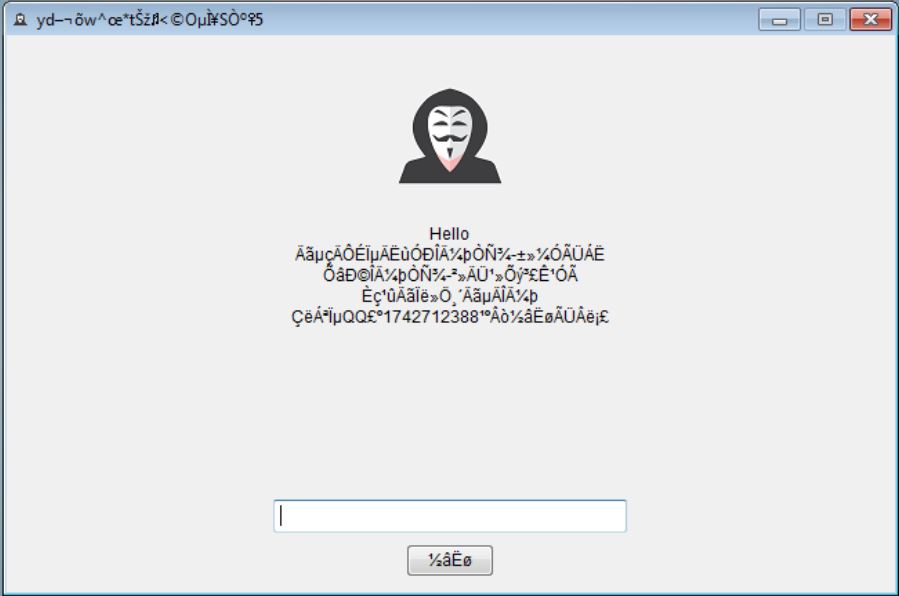
Toutes les données sur les victimes seront rebaptisés avec le .aaaaaa. Au lieu d'une note de ransomware traditionnelle, la menace présentera une instance de lockscreen. Il peut bloquer l'interaction ordinaire avec l'ordinateur jusqu'à ce qu'il soit supprimé.

Supprimer le virus Termite et restaurer les fichiers cryptés
Si votre ordinateur a été infecté par le Termite Virus, vous devriez avoir un peu d'expérience dans l'élimination des logiciels malveillants. Vous devriez vous débarrasser de cette ransomware le plus rapidement possible avant qu'il puisse avoir la chance de se propager plus loin et infecter d'autres ordinateurs. Vous devez retirer le ransomware et suivez le guide d'instructions étape par étape ci-dessous.
- Étape 1
- Étape 2
- Étape 3
- Étape 4
- Étape 5
Étape 1: Rechercher le virus Termite avec SpyHunter Anti-Malware Tool



Suppression automatique des rançongiciels - Guide vidéo
Étape 2: Uninstall Termite virus and related malware from Windows
Voici une méthode en quelques étapes simples qui devraient pouvoir désinstaller la plupart des programmes. Peu importe si vous utilisez Windows 10, 8, 7, Vista ou XP, ces mesures seront faire le travail. Faire glisser le programme ou de son dossier à la corbeille peut être un très mauvaise décision. Si vous faites cela, des morceaux du programme sont laissés, et qui peut conduire à un travail instable de votre PC, erreurs avec les associations de types de fichiers et d'autres activités désagréables. La bonne façon d'obtenir un programme sur votre ordinateur est de le désinstaller. Pour ce faire,:


 Suivez les instructions ci-dessus et vous supprimerez avec succès la plupart des programmes indésirables et malveillants.
Suivez les instructions ci-dessus et vous supprimerez avec succès la plupart des programmes indésirables et malveillants.
Étape 3: Nettoyer les registres, créé par le virus Termite sur votre ordinateur.
Les registres généralement ciblés des machines Windows sont les suivantes:
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion Run
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion Run
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion RunOnce
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion RunOnce
Vous pouvez y accéder en ouvrant l'éditeur de Registre Windows et la suppression de toutes les valeurs, créé par le virus Termite là-bas. Cela peut se produire en suivant les étapes ci-dessous:


 Pointe: Pour trouver une valeur créée virus, vous pouvez faire un clic droit dessus et cliquez "Modifier" pour voir quel fichier il est configuré pour exécuter. Si cela est l'emplacement du fichier de virus, supprimer la valeur.
Pointe: Pour trouver une valeur créée virus, vous pouvez faire un clic droit dessus et cliquez "Modifier" pour voir quel fichier il est configuré pour exécuter. Si cela est l'emplacement du fichier de virus, supprimer la valeur.
Avant de commencer "Étape 4", S'il vous plaît démarrer en mode normal, dans le cas où vous êtes actuellement en mode sans échec.
Cela vous permettra d'installer et utilisation SpyHunter 5 avec succès.
Étape 4: Démarrez votre PC en mode sans échec pour isoler et supprimer le virus Termite





Étape 5: Essayez de restaurer des fichiers cryptés par le virus Termite.
Méthode 1: Utilisez STOP Decrypter par Emsisoft.
Toutes les variantes de ce ransomware peuvent être décryptées gratuitement, mais nous avons ajouté le décrypteur utilisé par des chercheurs qui est souvent mis à jour avec les variantes qui finissent par devenir décryptés. Vous pouvez essayer de décrypter vos fichiers en utilisant les instructions ci-dessous, mais si elles ne fonctionnent pas, puis, malheureusement, votre variante du virus ransomware n'est pas déchiffrable.
Suivez les instructions ci-dessous pour utiliser le décrypteur Emsisoft et décrypter vos fichiers gratuitement. Tu peux télécharger l'outil de décryptage Emsisoft liée ici puis suivez les étapes indiquées ci-dessous:
1 Clic-droit sur le décrypteur et cliquez sur Exécuter en tant qu'administrateur comme indiqué ci-dessous:

2. D'accord avec les termes de la licence:

3. Cliquer sur "Ajouter le dossier" puis ajoutez les dossiers où vous voulez que les fichiers décryptés comme indiqué ci-dessous:

4. Cliquer sur "Décrypter" et attendez que vos fichiers à décoder.

Note: Crédit pour le décrypteur va EMSISOFT chercheurs qui ont fait la percée avec ce virus.
Méthode 2: Utiliser un logiciel de récupération de données
Les infections de ransomware et le virus Termite visent à crypter vos fichiers à l'aide d'un algorithme de cryptage qui peut être très difficile à décrypter. Voilà pourquoi nous avons proposé une méthode de récupération de données qui peuvent vous aider à faire le tour de décryptage direct et essayer de restaurer vos fichiers. Gardez à l'esprit que cette méthode ne peut pas être 100% efficace, mais peut aussi vous aider un peu ou beaucoup dans différentes situations.
Cliquez simplement sur le lien et sur les menus du site en haut, choisir Récupération de données - Assistant de récupération de données pour Windows ou Mac (en fonction de votre système d'exploitation), puis téléchargez et exécutez l'outil.
Termite virus-FAQ
What is Termite virus Ransomware?
Le virus des termites est un ransomware infection - les logiciels malveillants qui pénètrent silencieusement dans votre ordinateur et bloquent l'accès à l'ordinateur lui-même ou chiffrent vos fichiers.
De nombreux virus rançongiciels utilisent des algorithmes de cryptage sophistiqués pour rendre vos fichiers inaccessibles. Le but des infections par rançongiciels est d'exiger que vous payiez un paiement de rançon pour avoir accès à vos fichiers..
What Does Termite virus Ransomware Do?
Les ransomwares en général sont un logiciel malveillant qui est conçu pour bloquer l'accès à votre ordinateur ou à vos fichiers jusqu'à ce qu'une rançon soit payée.
Les virus Ransomware peuvent également endommager votre système, corrompre les données et supprimer des fichiers, entraînant la perte permanente de fichiers importants.
How Does Termite virus Infect?
Par plusieurs moyens.Termite virus Ransomware infecte les ordinateurs en étant envoyé par e-mails de phishing, contenant un virus attaché. Cette pièce jointe est généralement masquée comme un document important, comme une facture, un document bancaire ou encore un billet d'avion et cela semble très convaincant aux utilisateurs.
Another way you may become a victim of Termite virus is if you télécharger un faux installateur, crack ou correctif provenant d'un site Web de mauvaise réputation ou si vous cliquez sur un lien de virus. De nombreux utilisateurs signalent avoir contracté un ransomware en téléchargeant des torrents.
How to Open .Termite virus files?
Toi can't sans décrypteur. À ce point, la .virus termite les fichiers sont crypté. Vous ne pouvez les ouvrir qu'une fois qu'ils ont été déchiffrés à l'aide d'une clé de déchiffrement spécifique à un algorithme particulier..
Que faire si un décrypteur ne fonctionne pas?
Ne panique pas, et sauvegarder les fichiers. Si un déchiffreur n'a pas déchiffré votre .virus termite fichiers avec succès, alors ne désespérez pas, parce que ce virus est encore nouveau.
Puis-je restaurer ".virus termite" dossiers?
Oui, parfois les fichiers peuvent être restaurés. Nous avons proposé plusieurs méthodes de récupération de fichiers cela pourrait fonctionner si vous souhaitez restaurer .virus termite fichiers.
Ces méthodes ne sont en aucun cas 100% garanti que vous pourrez récupérer vos fichiers. Mais si vous avez une sauvegarde, vos chances de succès sont bien plus grandes.
How To Get Rid of Termite virus Virus?
Le moyen le plus sûr et le plus efficace pour supprimer cette infection par rançongiciel est d'utiliser un programme anti-malware professionnel.
Il recherchera et localisera le ransomware de virus Termite, puis le supprimera sans causer de dommages supplémentaires à vos fichiers de virus .Termite importants.
Puis-je signaler un ransomware aux autorités?
Au cas où votre ordinateur serait infecté par une infection ransomware, vous pouvez le signaler aux services de police locaux. Il peut aider les autorités du monde entier à suivre et à déterminer les auteurs du virus qui a infecté votre ordinateur.
Dessous, nous avons préparé une liste de sites Web gouvernementaux, où vous pouvez déposer un rapport au cas où vous seriez victime d'un cybercriminalité:
Autorités de cybersécurité, responsable de la gestion des rapports d'attaque de ransomware dans différentes régions du monde:
Allemagne - Portail officiel de la police allemande
États Unis - IC3 Centre de plaintes contre la criminalité sur Internet
Royaume-Uni - Action Fraud Police
France - Ministère de l'Intérieur
Italie - Police d'État
Espagne - Police nationale
Pays-Bas - Forces de l'ordre
Pologne - Police
le Portugal - Police judiciaire
Grèce - Unité de la cybercriminalité (Police hellénique)
Inde - Police de Mumbai - Cellule d'enquête sur la cybercriminalité
Australie - Australian High Tech Crime Center
Les rapports peuvent recevoir une réponse dans des délais différents, selon vos autorités locales.
Pouvez-vous empêcher les ransomwares de crypter vos fichiers?
Oui, vous pouvez empêcher les ransomwares. La meilleure façon de le faire est de vous assurer que votre système informatique est mis à jour avec les derniers correctifs de sécurité., utiliser un programme anti-malware réputé et pare-feu, sauvegardez fréquemment vos fichiers importants, et évitez de cliquer sur liens malveillants ou télécharger des fichiers inconnus.
Can Termite virus Ransomware Steal Your Data?
Oui, dans la plupart des cas, un rançongiciel va voler vos informations. It is a form of malware that steals data from a user's computer, le crypte, puis demande une rançon pour le décrypter.
Dans de nombreux cas,, la auteurs de logiciels malveillants ou les attaquants menaceront de supprimer les données ou le publier en ligne à moins que la rançon est payée.
Un ransomware peut-il infecter le WiFi?
Oui, un ransomware peut infecter les réseaux WiFi, car des acteurs malveillants peuvent l'utiliser pour prendre le contrôle du réseau, voler des données confidentielles, et verrouiller les utilisateurs. Si une attaque de ransomware réussit, cela pourrait entraîner une perte de service et/ou de données, et dans certains cas, pertes financières.
Dois-je payer un rançongiciel?
Aucun, vous ne devriez pas payer les extorqueurs de rançongiciels. Les payer ne fait qu'encourager les criminels et ne garantit pas que les fichiers ou les données seront restaurés. La meilleure approche consiste à disposer d'une sauvegarde sécurisée des données importantes et à être vigilant quant à la sécurité en premier lieu.
What Happens If I Don't Pay Ransom?
If you don't pay the ransom, les pirates peuvent toujours avoir accès à votre ordinateur, données, ou des fichiers et peut continuer à menacer de les exposer ou de les supprimer, ou même les utiliser pour commettre des cybercrimes. Dans certains cas,, ils peuvent même continuer à exiger des paiements de rançon supplémentaires.
Une attaque de ransomware peut-elle être détectée?
Oui, les rançongiciels peuvent être détectés. Logiciel anti-malware et autres outils de sécurité avancés peut détecter les ransomwares et alerter l'utilisateur quand il est présent sur une machine.
Il est important de se tenir au courant des dernières mesures de sécurité et de maintenir les logiciels de sécurité à jour pour s'assurer que les ransomwares peuvent être détectés et empêchés..
Les criminels du ransomware se font-ils prendre?
Oui, les criminels rançongiciels se font prendre. Les organismes d'application de la loi, comme le FBI, Interpol et d'autres ont réussi à traquer et à poursuivre les criminels de ransomware aux États-Unis et dans d'autres pays.. Alors que les menaces de rançongiciels continuent d'augmenter, il en va de même pour l'activité d'application.
About the Termite virus Research
Le contenu que nous publions sur SensorsTechForum.com, this Termite virus how-to removal guide included, est le résultat de recherches approfondies, le travail acharné et le dévouement de notre équipe pour vous aider à supprimer les logiciels malveillants spécifiques et à restaurer vos fichiers cryptés.
Comment avons-nous mené la recherche sur ce ransomware?
Notre recherche est basée sur une enquête indépendante. Nous sommes en contact avec des chercheurs indépendants en sécurité, et en tant que tel, nous recevons des mises à jour quotidiennes sur les dernières définitions de logiciels malveillants et de ransomwares.
En outre, the research behind the Termite virus ransomware threat is backed with VirusTotal et l' projet NoMoreRansom.
Pour mieux comprendre la menace des ransomwares, veuillez vous référer aux articles suivants qui fournissent des détails bien informés.
En tant que site dédié à fournir des instructions de suppression gratuites pour les ransomwares et les malwares depuis 2014, La recommandation de SensorsTechForum est de ne prêter attention qu'aux sources fiables.
Comment reconnaître des sources fiables:
- Vérifiez toujours "À propos de nous" page web.
- Profil du créateur de contenu.
- Assurez-vous que de vraies personnes sont derrière le site et non de faux noms et profils.
- Vérifiez Facebook, Profils personnels LinkedIn et Twitter.


