Dit artikel zal u helpen te verwijderen Teeny Ransomware. Volg de instructies voor het verwijderen ransomware voorzien aan het einde van het artikel.
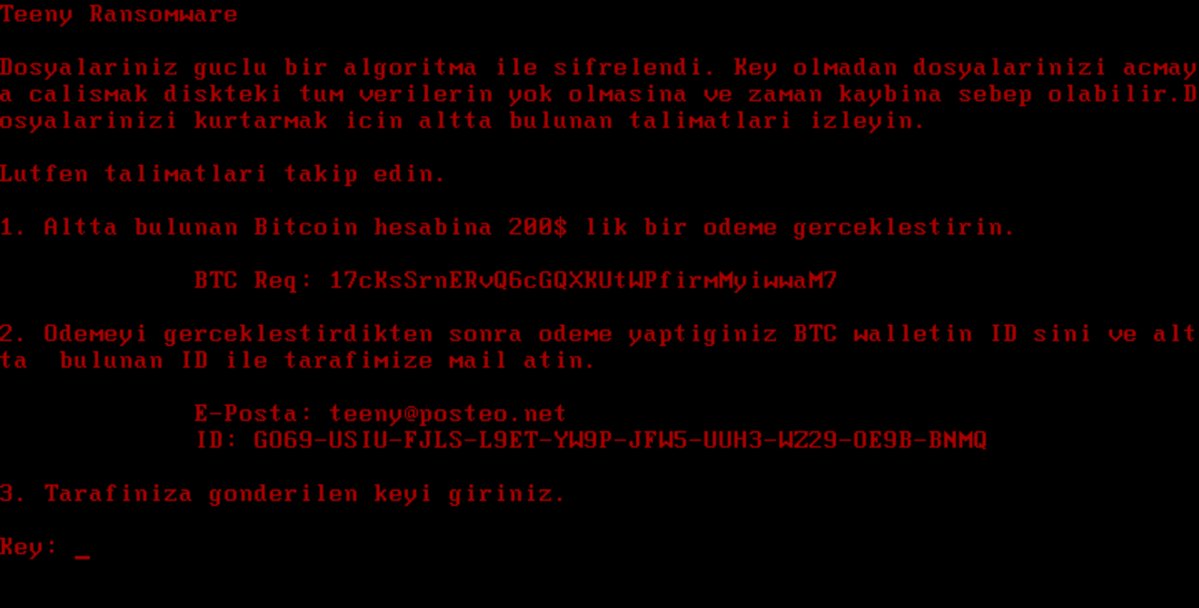
Teeny Ransomware is er een die je master boot record versleutelt (MBR) met en eist geld als losgeld om het hersteld te krijgen. Het Teeny Ransomware zal ransomware instructies als tekstbestand te verlaten. Houd bij het lezen van het artikel en zie hoe je zou kunnen proberen om potentieel te herstellen sommige van uw vergrendelde bestanden en gegevens.

bedreiging Samenvatting
| Naam | teeny ransomware |
| Type | Ransomware, Cryptovirus |
| Korte Omschrijving | De ransomware versleutelt het master-opstartrecord (MBR) op uw computer systeem en vraagt om een losgeld te betalen om ze naar verluidt herstellen. |
| Symptomen | De ransomware zal uw bestanden te versleutelen en laat een losgeld nota met betalingsinstructies. |
| Distributie Methode | Spam e-mails, E-mailbijlagen |
| Detection Tool |
Zien of je systeem is getroffen door malware
Download
Malware Removal Tool
|
Gebruikerservaring | Word lid van onze Forum om Teeny ransomware te bespreken. |
| Data Recovery Tool | Windows Data Recovery door Stellar Phoenix kennisgeving! Dit product scant uw schijf sectoren om verloren bestanden te herstellen en het kan niet herstellen 100% van de gecodeerde bestanden, maar slechts weinigen van hen, afhankelijk van de situatie en of u uw schijf hebt geformatteerd. |

Teeny Ransomware - Distributietechnieken
De Teeny-ransomware kan via verschillende mechanismen worden verspreid, de genomen monsters zijn erg laag om te bepalen wat de primaire methode is.
Gewoonlijk worden ransomware-bedreigingen zoals deze verzonden via e-mail phishing-berichten waarin de monsters direct kunnen worden bevestigd of gekoppeld. De inhoud van het lichaam kan verschillende soorten inhoud dienen: pop-ups, redirects, afbeeldingen die bij interactie kunnen leiden tot de virusinfectie.
Een vergelijkbare strategie is wanneer de criminelen kwaadaardige websites waarmee nepkopieën van bekende bedrijven worden gemaakt, services en bestemmingspagina's. Ze worden meestal gehost op vergelijkbaar klinkende domeinnamen als de originele - als de gebruikers een bepaald adres verkeerd typen, kunnen ze op een neppe copycat terechtkomen zonder het te merken. In veel van de voorbeelden worden vergelijkbare webdesigns en zelfs beveiligingscertificaten geïmplementeerd.
Een van de meest populaire manieren om ransomware te verspreiden, is door het installatiescript in te sluiten in carrier-bestanden - er zijn twee hoofdtypen:
- Application Installateurs - De installatie-instructies van de Teeny ransomware kunnen worden ingesloten in installatiebestanden van populaire software die vaak wordt gedownload en geïnstalleerd door eindgebruikers. Voorbeelden omvatten systeemnut, productiviteit en kantoorsuites en zelfs games. Zodra de uitvoerbare bestanden worden uitgevoerd, wordt de Teeny-ransomware geïnstalleerd.
- document bestanden - Het virusinstallatiescript kan in documenten van alle populaire typen worden geplaatst: spreadsheets, presentaties, databases en tekstbestanden. Wanneer ze worden geopend, verschijnt er een meldingsframe waarin de slachtoffers worden gevraagd om de ingebouwde macro's in te schakelen om het bestand te bekijken. Als dit is gebeurd, wordt de installatie geactiveerd.
Deze ladingsdragers kunnen worden verspreid via bestandsuitwisselingsnetwerken zoals BitTorrent die vaak worden gebruikt om zowel illegale als legitieme inhoud te verspreiden. Geïnfecteerde installatieprogramma's en virusbestanden zijn de meest voorkomende varianten die kunnen worden verkregen via de trackers.
De Teeny ransomware kan ook worden verspreid via browser plugins, alternatief als kapers. Ze zijn kwaadaardig van aard en worden geüpload naar de relevante repositories met gebruikersrecensies en ontwikkelaarsreferenties. De beschrijvingen bieden nieuwe functies en prestatieverbeteringen, maar in werkelijkheid wordt alleen de slechte code geïnjecteerd.

Teeny Ransomware - Gedetailleerde analyse
De momenteel vastgelegde monsters die verband houden met de Teeny-ransomware-dreiging zijn zeer laag in aantal, wat suggereert dat de aanvankelijke aanvalscampagne niet groot is. Het is mogelijk dat dit een vroege testrelease of een ontwikkelingsversie is, aangezien er geen modules beschikbaar zijn naast de ransomware-engine. Er is geen code gevonden die afkomstig is van de beroemde malwarefamilies en suggereert ook dat de code is ontwikkeld door de aanvallers zelf.
Het is mogelijk dat toekomstige versies populaire toevoegingen gaan bundelen, zoals de volgende componenten:
- Boot Options Manipulatie - Door de belangrijkste opstartopties opnieuw te configureren, configuratiebestanden en systeeminstellingen kan de Teeny ransomware worden gestart elke keer dat de computer wordt ingeschakeld. Hierdoor kunnen de handmatige gebruikersherstelgidsen niet werken, omdat de toegang tot de herstelopties kan worden geblokkeerd.
- informatie Diefstal - De engine kan worden geconfigureerd om de inhoud van de lokale harde schijf te scannen op zowel machine-identificatiegegevens als persoonlijke gebruikersinformatie. Dit wordt gedaan om een uniek computer-ID te genereren dat onderscheid kan maken tussen alle geïnfecteerde computers. De verzamelde gebruikersinformatie kan hun identiteit direct onthullen door naar hun naam te zoeken, adres, telefoonnummer, interesses en zelfs opgeslagen accountreferenties - combinaties van gebruikersnamen, wachtwoorden en e-mailadressen.
- Windows-register Wijzigingen - Door het Windows-register te openen en te wijzigen, kan de virusengine ernstige stabiliteitsproblemen veroorzaken. Manipulatie van strings die worden gebruikt door besturingssysteemservices en toepassingen van derden, kan leiden tot onverwacht afsluiten en fouten.
- Extra Payload Delivery - Deze infectie kan worden gebruikt om andere bedreigingen naar de gecompromitteerde machines te laden.
- beveiliging Bypass - De Teeny-ransomware kan zoeken naar geïnstalleerde beveiligingsapplicaties en deze uitschakelen. Dit geldt ook voor anti-virus programma's, zandbak en debug-omgevingen, firewalls en virtual machine hosts.
Toekomstige versies van de Teeny-ransomware kunnen ook worden geüpgraded met andere opties.

Teeny Ransomware - Versleutelingsproces
Zodra alle voorgaande modules zijn voltooid, wordt de ransomware-engine gestart. In plaats van gebruikersbestanden te verwerken, versleutelt het de master-bootrecord (MBR) en chanteren de slachtoffers om hen een decoderingsvergoeding te betalen. Het bericht is in het Turks geschreven, waardoor we denken dat het uit dat land komt. Toekomstige versies kunnen ook gebruikersgegevens versleutelen volgens een ingebouwde lijst met extensies van het doelbestandstype.

Verwijder Teeny Ransomware en probeer gegevens te herstellen
Als uw computersysteem raakte besmet met het teeny ransomware virus, moet je een beetje ervaring hebben in het verwijderen van malware. U dient zich te ontdoen van deze ransomware krijgen zo snel mogelijk voordat het de kans om verder te verspreiden en andere computers te infecteren kan hebben. U moet de ransomware te verwijderen en volg de stap-voor-stap instructies handleiding hieronder.
- Stap 1
- Stap 2
- Stap 3
- Stap 4
- Stap 5
Stap 1: Scannen op Teeny ransomware met SpyHunter Anti-Malware Tool



Ransomware Automatische verwijdering - Videogids
Stap 2: Uninstall Teeny ransomware and related malware from Windows
Hier is een methode om in een paar eenvoudige stappen die moeten in staat zijn om de meeste programma's te verwijderen. Geen probleem als u Windows 10, 8, 7, Vista of XP, die stappen zal de klus te klaren. Slepen van het programma of de map naar de prullenbak kan een zeer slechte beslissing. Als je dat doet, stukjes van het programma worden achtergelaten, en dat kan leiden tot een instabiel werk van uw PC, fouten met het bestandstype verenigingen en andere onaangename activiteiten. De juiste manier om een programma te krijgen van je computer is deze ook te verwijderen. Om dat te doen:


 Volg de bovenstaande instructies en u zult met succes de meeste ongewenste en kwaadaardige programma's verwijderen.
Volg de bovenstaande instructies en u zult met succes de meeste ongewenste en kwaadaardige programma's verwijderen.
Stap 3: Verwijder eventuele registers, gemaakt door Teeny ransomware op uw computer.
De doorgaans gericht registers van Windows-machines zijn de volgende:
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion Run
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion Run
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion RunOnce
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion RunOnce
U kunt ze openen door het openen van het Windows-register-editor en met weglating van alle waarden, gemaakt door Teeny ransomware daar. Dit kan gebeuren door de stappen onder:


 Tip: Om een virus gecreëerd waarde te vinden, U kunt met de rechtermuisknop op te klikken en klik op "Wijzigen" om te zien welk bestand het is ingesteld om te werken. Als dit het virus bestand locatie, Verwijder de waarde.
Tip: Om een virus gecreëerd waarde te vinden, U kunt met de rechtermuisknop op te klikken en klik op "Wijzigen" om te zien welk bestand het is ingesteld om te werken. Als dit het virus bestand locatie, Verwijder de waarde.
Voor het starten "Stap 4", alsjeblieft laars terug in de normale modus, in het geval dat u op dit moment in de Veilige modus.
Dit stelt u in staat om te installeren en gebruik SpyHunter 5 geslaagd.
Stap 4: Start uw pc op in de veilige modus om Teeny-ransomware te isoleren en te verwijderen





Stap 5: Probeer bestanden te herstellen die zijn versleuteld door Teeny ransomware.
Methode 1: Gebruik STOP Decrypter van Emsisoft.
Niet alle varianten van deze ransomware kan worden ontsleuteld gratis, maar we hebben de decryptor gebruikt door onderzoekers die vaak wordt bijgewerkt met de varianten die uiteindelijk gedecodeerd toegevoegd. U kunt proberen en decoderen van uw bestanden met behulp van de onderstaande instructies, maar als ze niet werken, dan helaas uw variant van de ransomware virus is niet decryptable.
Volg de onderstaande instructies om de Emsisoft decrypter gebruiken en decoderen van uw bestanden gratis. Je kan Download de Emsisoft decryptiehulpmiddel hier gekoppeld en volg de stappen hieronder:
1 Klik met de rechtermuisknop op de decrypter en klik op Als administrator uitvoeren zoals hieronder getoond:

2. Ben het eens met de licentievoorwaarden:

3. Klik op "Map toevoegen" en voeg vervolgens de mappen waarin u bestanden gedecodeerd zoals hieronder afgebeeld:

4. Klik op "decoderen" en wacht tot uw bestanden te decoderen.

Aantekening: Krediet voor de decryptor gaat naar onderzoekers die de doorbraak hebben gemaakt met dit virus Emsisoft.
Methode 2: Gebruik software voor gegevensherstel
Ransomware-infecties en Teeny-ransomware hebben tot doel uw bestanden te versleutelen met behulp van een versleutelingsalgoritme dat erg moeilijk te ontsleutelen kan zijn. Dit is de reden waarom we een data recovery-methode die u kunnen helpen rond gaan direct decryptie en proberen om uw bestanden te herstellen hebben gesuggereerd. Houd er rekening mee dat deze methode niet kan worden 100% effectief, maar kan ook u helpen een veel of weinig in verschillende situaties.
Klik gewoon op de link en op de websitemenu's bovenaan, kiezen Data herstel - Data Recovery Wizard voor Windows of Mac (afhankelijk van uw besturingssysteem), en download en voer vervolgens de tool uit.
Teeny ransomware-FAQ
What is Teeny ransomware Ransomware?
Teeny ransomware is een ransomware infectie - de schadelijke software die geruisloos uw computer binnenkomt en de toegang tot de computer zelf blokkeert of uw bestanden versleutelt.
Veel ransomware-virussen gebruiken geavanceerde versleutelingsalgoritmen om uw bestanden ontoegankelijk te maken. Het doel van ransomware-infecties is om te eisen dat u een losgeld betaalt om toegang te krijgen tot uw bestanden.
What Does Teeny ransomware Ransomware Do?
Ransomware is in het algemeen een kwaadaardige software dat is ontworpen om de toegang tot uw computer of bestanden te blokkeren totdat er losgeld wordt betaald.
Ransomware-virussen kunnen dat ook uw systeem beschadigen, corrupte gegevens en verwijder bestanden, resulterend in het permanent verlies van belangrijke bestanden.
How Does Teeny ransomware Infect?
Via verschillende manieren. Teeny ransomware Ransomware infecteert computers door te worden verzonden via phishing-e-mails, met virusbijlage. Deze bijlage is meestal gemaskeerd als een belangrijk document, zoals een factuur, bankdocument of zelfs een vliegticket en het ziet er erg overtuigend uit voor gebruikers.
Another way you may become a victim of Teeny ransomware is if you download een nep-installatieprogramma, crack of patch van een website met een lage reputatie of als u op een viruslink klikt. Veel gebruikers melden dat ze een ransomware-infectie hebben opgelopen door torrents te downloaden.
How to Open .Teeny ransomware files?
U can't zonder decryptor. Op dit punt, de .teeny ransomware bestanden zijn versleutelde. U kunt ze pas openen nadat ze zijn gedecodeerd met een specifieke decoderingssleutel voor het specifieke algoritme.
Wat te doen als een decryptor niet werkt?
Raak niet in paniek, en maak een back-up van de bestanden. Als een decryptor uw niet heeft gedecodeerd .teeny ransomware bestanden succesvol, wanhoop dan niet, omdat dit virus nog steeds nieuw is.
Kan ik herstellen ".teeny ransomware" Bestanden?
Ja, soms kunnen bestanden worden hersteld. We hebben er verschillende voorgesteld bestandsherstelmethoden dat zou kunnen werken als je wilt herstellen .teeny ransomware bestanden.
Deze methoden zijn op geen enkele manier 100% gegarandeerd dat u uw bestanden terug kunt krijgen. Maar als je een back-up hebt, uw kansen op succes zijn veel groter.
How To Get Rid of Teeny ransomware Virus?
De veiligste en meest efficiënte manier voor het verwijderen van deze ransomware-infectie is het gebruik van een professioneel antimalwareprogramma.
Het scant en lokaliseert de Teeny ransomware ransomware en verwijdert het vervolgens zonder verdere schade toe te brengen aan uw belangrijke .Teeny ransomware bestanden.
Kan ik ransomware melden aan de autoriteiten??
In het geval dat uw computer is geïnfecteerd met een ransomware-infectie, u kunt dit melden bij de lokale politie. Het kan autoriteiten over de hele wereld helpen de daders van het virus dat uw computer heeft geïnfecteerd, op te sporen en te achterhalen.
Onder, we hebben een lijst met overheidswebsites opgesteld, waar u aangifte kunt doen als u slachtoffer bent van een cybercrime:
Cyberbeveiligingsautoriteiten, verantwoordelijk voor het afhandelen van ransomware-aanvalsrapporten in verschillende regio's over de hele wereld:
Duitsland - Officieel portaal van de Duitse politie
Verenigde Staten - IC3 Internet Crime Complaint Center
Verenigd Koninkrijk - Actie Fraude Politie
Frankrijk - Ministerie van Binnenlandse Zaken
Italië - Staatspolitie
Spanje - Nationale politie
Nederland - Politie
Polen - Politie
Portugal - Gerechtelijke politie
Griekenland - Cyber Crime Unit (Griekse politie)
India - Mumbai politie - Cel voor onderzoek naar cybercriminaliteit
Australië - Australisch High Tech Crime Centre
Op rapporten kan in verschillende tijdsbestekken worden gereageerd, afhankelijk van uw lokale autoriteiten.
Kunt u voorkomen dat ransomware uw bestanden versleutelt??
Ja, u kunt ransomware voorkomen. De beste manier om dit te doen, is ervoor te zorgen dat uw computersysteem is bijgewerkt met de nieuwste beveiligingspatches, gebruik een gerenommeerd anti-malwareprogramma en firewall, maak regelmatig een back-up van uw belangrijke bestanden, en klik niet op kwaadaardige links of het downloaden van onbekende bestanden.
Can Teeny ransomware Ransomware Steal Your Data?
Ja, in de meeste gevallen ransomware zal uw gegevens stelen. It is a form of malware that steals data from a user's computer, versleutelt het, en eist vervolgens losgeld om het te decoderen.
In veel gevallen, de malware-auteurs of aanvallers zullen dreigen de gegevens of te verwijderen publiceer het online tenzij het losgeld wordt betaald.
Kan ransomware WiFi infecteren??
Ja, ransomware kan WiFi-netwerken infecteren, aangezien kwaadwillende actoren het kunnen gebruiken om controle over het netwerk te krijgen, vertrouwelijke gegevens stelen, en gebruikers buitensluiten. Als een ransomware-aanval succesvol is, dit kan leiden tot verlies van service en/of gegevens, en in sommige gevallen, financiële verliezen.
Moet ik ransomware betalen?
Geen, je moet geen afpersers van ransomware betalen. Betalen moedigt criminelen alleen maar aan en geeft geen garantie dat de bestanden of gegevens worden hersteld. De betere aanpak is om een veilige back-up van belangrijke gegevens te hebben en in de eerste plaats waakzaam te zijn over de beveiliging.
What Happens If I Don't Pay Ransom?
If you don't pay the ransom, de hackers hebben mogelijk nog steeds toegang tot uw computer, gegevens, of bestanden en kunnen blijven dreigen deze openbaar te maken of te verwijderen, of ze zelfs gebruiken om cybercriminaliteit te plegen. In sommige gevallen, ze kunnen zelfs doorgaan met het eisen van extra losgeld.
Kan een ransomware-aanval worden gedetecteerd??
Ja, ransomware kan worden gedetecteerd. Antimalwaresoftware en andere geavanceerde beveiligingstools kan ransomware detecteren en de gebruiker waarschuwen wanneer het op een machine aanwezig is.
Het is belangrijk om op de hoogte te blijven van de nieuwste beveiligingsmaatregelen en om beveiligingssoftware up-to-date te houden om ervoor te zorgen dat ransomware kan worden gedetecteerd en voorkomen.
Worden ransomware-criminelen gepakt?
Ja, ransomware-criminelen worden gepakt. Wetshandhavingsinstanties, zoals de FBI, Interpol en anderen zijn succesvol geweest in het opsporen en vervolgen van ransomware-criminelen in de VS en andere landen. Naarmate ransomware-bedreigingen blijven toenemen, dat geldt ook voor de handhavingsactiviteiten.
Over het Teeny ransomware-onderzoek
De inhoud die we publiceren op SensorsTechForum.com, deze Teeny ransomware how-to verwijderingsgids inbegrepen, is het resultaat van uitgebreid onderzoek, hard werken en de toewijding van ons team om u te helpen de specifieke malware te verwijderen en uw versleutelde bestanden te herstellen.
Hoe hebben we het onderzoek naar deze ransomware uitgevoerd??
Ons onderzoek is gebaseerd op een onafhankelijk onderzoek. We hebben contact met onafhankelijke beveiligingsonderzoekers, en als zodanig, we ontvangen dagelijkse updates over de nieuwste malware- en ransomware-definities.
Bovendien, het onderzoek achter de Teeny ransomware-ransomware-dreiging wordt ondersteund door: VirusTotal en NoMoreRansom project.
Om de ransomware-dreiging beter te begrijpen, raadpleeg de volgende artikelen die deskundige details bieden:.
Als een site die sindsdien is toegewijd aan het verstrekken van gratis verwijderingsinstructies voor ransomware en malware 2014, De aanbeveling van SensorsTechForum is let alleen op betrouwbare bronnen.
Hoe betrouwbare bronnen te herkennen:
- Controleer altijd "Over ons" webpagina.
- Profiel van de maker van de inhoud.
- Zorg ervoor dat er echte mensen achter de site staan en geen valse namen en profielen.
- Controleer Facebook, LinkedIn en Twitter persoonlijke profielen.