 O Readiness Team US Computer Emergency (CERT) emitiu um alerta na segunda-feira sobre uma campanha de e-mail malicioso entregar o Dyre Trojan bancário, aka Dyreza. As mensagens maliciosas foram detectados no meio do mês, e não há nenhum grupo demográfico específico visado pelos cibercriminosos.
O Readiness Team US Computer Emergency (CERT) emitiu um alerta na segunda-feira sobre uma campanha de e-mail malicioso entregar o Dyre Trojan bancário, aka Dyreza. As mensagens maliciosas foram detectados no meio do mês, e não há nenhum grupo demográfico específico visado pelos cibercriminosos.
O novo ataque Dyre explora a vulnerabilidade no Adobe Reader
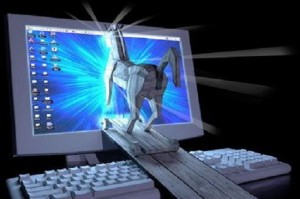
Várias variantes do ataque foram distinguidas até agora. Eles variam no tema do e-mail, o endereço do remetente e os exploits usados. Ainda, todos eles têm o mesmo objetivo - atrair o usuário a abrir o arquivo anexo corrompido que afirma ser uma fatura na forma de um arquivo PDF. O anexo malicioso, Invoice621785.pdf, contém exploits para vulnerabilidades no Adobe Reader. Isso torna os usuários de computador com versões mais antigas e não corrigidas do leitor o alvo perfeito.
CVE-2013-2729 é uma das vulnerabilidades que permite a execução de código arbitrário em versões do Adobe Acrobat e Reader anteriores 9.5.5, 10.1.7, 11.0.03.
A primeira vez que o cavalo de Troia bancário Dyre foi localizado foi em janeiro deste ano e tem sido associado a inúmeras campanhas maliciosas desde. Um dos mais populares é o ataque contra clientes Salesforce em setembro.
Período de teste de Dyre no verão
O principal objetivo do Trojan Dyre é coletar dados bancários de login e enviá-los ao operador. Alegadamente, foi adaptado para roubar também outros tipos de credenciais recentemente. O banco Dyre Em um ataque recente, o Trojan incluiu sites Bitcoin em sua lista de alvos no arquivo de configuração.
Campanhas, entregando o Trojan Dyre estiveram ativos durante todo o verão. A peça foi incluída em e-mails de phishing, alegando ter sido enviado pela instituição financeira JP Morgan. Outro e-mail de phishing supostamente uma notificação de mensagem de voz.
Os especialistas revelam que o Trojan foi aprimorado recentemente e atualmente está usando seu próprio certificado SSL que fornece comunicação segura com o C&Servidor C e ocultar tráfego malicioso.
Os usuários são aconselhados a ter cuidado extra ao receber e-mails não solicitados e estar atentos a erros de ortografia e gramática nas mensagens. Especialistas apontam que a presença do Google Update Service pode ser uma indicação de infecção.

