Los virus informáticos están evolucionando rápidamente a medida que los piratas informáticos están diseñando nuevos tipos de mecanismos de malware y entrega. A pesar del hecho de que los usuarios de ordenadores más comunes los perciben como archivos ejecutables individuales que ejecutan un comportamiento de comandos predefinido, las campañas de ataque actuales muestran una manera totalmente diferente de manejar archivos. El paisaje virus informático está cambiando rápidamente a medida que se producen piezas de malware de nueva generación. En determinadas situaciones, la carrera de los analistas de seguridad contra los piratas informáticos como infecciones puede no ser detectados por largos períodos de tiempo. Este artículo explora algunas de las muestras de virus informáticos de diseño contemporáneo y los componentes esenciales de malware que se han convertido en estándar en los últimos años.
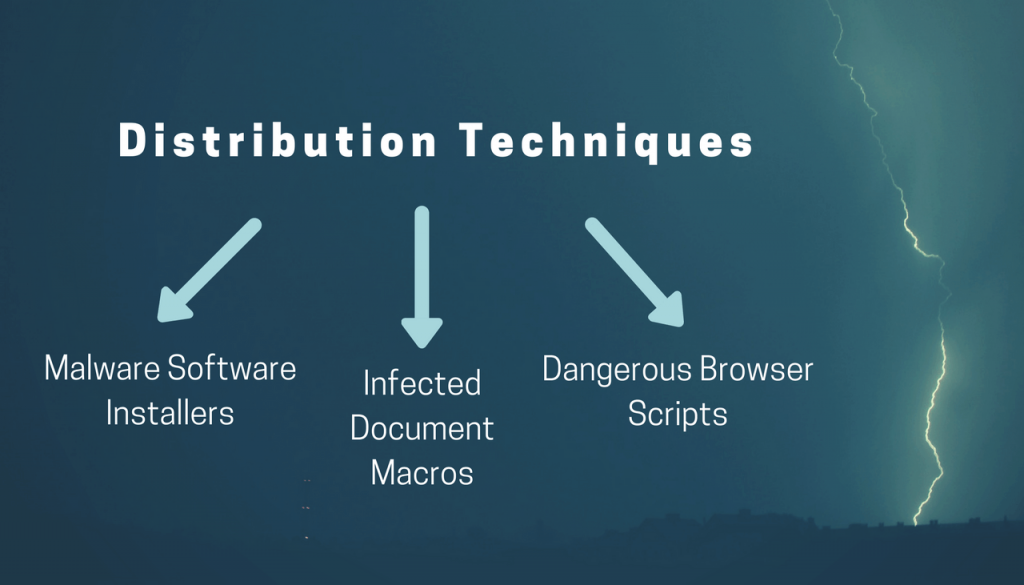
Principios de malware: Técnicas de distribución
Uno de los aspectos más importantes de las diversas campañas de ataque es la etapa de planificación. En mayor medida, El mecanismo de infección sigue siendo mucho más importante que los propios componentes del malware.. Para un delincuente informático, La tarea más peligrosa es la fase de intrusión inicial, ya que necesitan descubrir una forma de piratear los objetivos previstos.. En los últimos años, las estrategias de distribución han cambiado drásticamente a medida que los delincuentes utilizan una amplia gama de herramientas, servicios web, y mecanismos avanzados.
Los usuarios de ordenadores pueden ser víctimas de estafas de phishing elaborados que utilizan múltiples estrategias de ingeniería social. Esto se puede hacer mediante el envío de enlaces a sitios de hackers controlado o una pieza de software malicioso archivo. En lugar de depender de un solo archivo ejecutable que se puede escanear fácilmente con un motor antivirus en tiempo real simple, los piratas informáticos pueden integrar módulos descargables que utilizan un proceso de entrega de varias etapas. Hay varias estrategias que se han encontrado para ser eficaz en los virus que despliegan a escala mundial.
- Malware instaladores de software - Los delincuentes pueden descargar los instaladores de software legítimo de las páginas oficiales de descarga proveedor. Ellos son modificados para incluir código malicioso, el archivo resultante se distribuye a continuación, utilizando una variedad de maneras: mensajes de correo electrónico, páginas falsificación de descarga, Las redes P2P y etc..
- Las macros de documentos infectados - Este tipo de documentos plantean documentos legítimos de los intereses del usuario y se hacen pasar por facturas, notificaciones o letras. Pueden ser de varios tipos (documentos de texto enriquecido, hojas de cálculo o presentaciones) y lanzar una pronta notificación por la que pide a las víctimas habilitar las macros integradas (guiones). Si esto se hace de la infección por el virus sigue.
- Los scripts de navegador peligrosos - Cuando los ataques implican la falsificación de los plugins del navegador Web (también conocido como secuestradores). Por lo general, las víctimas redirigen a un sitio pirata informático que funciona cambiando la configuración predeterminada. Durante la infección inicial de la muestra de virus también se puede implementar en los ordenadores victima.
Otras formas directas de la entrega de las infecciones por virus implican la creación de sitios de malware. Utilizan los mismos gráficos y de texto como sitios legítimos y por lo general se presentan como copias falsificadas de servicios de Internet y portales de descarga. Los piratas informáticos registrar nombres de dominio que son similares a los sitios legítimos, como consecuencia muchos usuarios son víctimas de ellas.
Últimamente, Los virus también se distribuyen utilizando mensajes de redes sociales de perfiles falsos., programas de chat, y foros web. Esto va más allá de un chat en el juego, comunidades de juegos (tal como vapor) y otras aplicaciones relacionadas.
Mecanismos Virus infección inicial
Una vez que los virus se han desplegado a la víctima anfitriones se inicia la primera etapa de la infección. En general, la mayoría de las amenazas de malware encienden sus motores tan pronto como se hace esto, que es el comportamiento predeterminado. El software anti-malware tiene la capacidad de estar atento a este comportamiento y puede indicar inmediatamente al software de escaneo que ejecute un análisis profundo del archivo potencialmente dañino.. Como resultado, estas cepas pueden evitar los motores en tiempo real. Esto se relaciona con la la protección de sigilo capacidades que contrarrestan el comportamiento esperado. También pueden pasar por el sistema en busca de otro software de seguridad. Si se encuentra alguna que pueden incumplirse totalmente o totalmente eliminadas. Los virus también pueden ser programados para eliminar a sí mismos y evitar su detección.
El siguiente paso sería instituir una recopilación de información módulo. Se utiliza un módulo separado que es capaz de extraer una gran cantidad de datos de los equipos comprometidos. Los expertos en seguridad de la información generalmente se clasifican en dos grupos principales:
- Las métricas anónimas - Son utilizados por los delincuentes para juzgar la eficacia de la campaña de ataque es. Normalmente, los datos consisten en datos de la versión del sistema operativo y la información relacionada.
- Datos de Identificación Personal - Este tipo es extraído por medio de una instrucción especial que busca cadenas relacionadas con la identidad usuarios. Como resultado, los piratas informáticos pueden obtener información tal como el nombre de la víctima, dirección, teléfono, intereses, credenciales de cuenta y contraseñas.
Esta información puede ser transmitida a los operadores de hackers que utilizan una conexión de una sola vez. En otros casos, Se puede establecer una conexión constante con los controladores criminales a través de un servidor de comando y control.. En general, Las conexiones cifradas son la norma y los piratas informáticos pueden utilizarlas para enviar comandos arbitrarios a las víctimas.. En algunos casos, También se puede utilizar para generar amenazas de malware adicionales.. La infección de Troya puede seguir, lo que permitiría a los operadores de piratas informáticos espiar a las víctimas en tiempo real y tomar el control de las máquinas en cualquier momento dado.
En una forma similar ransomware los virus se pueden implementar en los ordenadores victima. Una vez que se han infiltrado en el sistema sus motores de malware comienzan a procesar los archivos sensibles de los usuarios de acuerdo a una lista integrada de extensiones de archivos. Los usuarios son entonces chantajeados a pagar una cuota de rescate a los piratas informáticos utilizando una criptomoneda.
Virus tendencias de diseño - Consecuencias de las infecciones avanzadas
En los últimos años, Los piratas informáticos han implementado conceptos más nuevos que amplían aún más las capacidades de las campañas de ataques de malware en curso.. Una adición que se ha vuelto estándar es el mecanismo de entrega de varias etapas. Una vez que los delincuentes han sido capaces de penetrar en los ordenadores de la red que pueden utilizar la segunda etapa para iniciar varios tipos de cambios en el sistema.
Por ejemplo la modificación de la Registro de Windows puede desactivar ciertos servicios y también es la causa de fallo de aplicación. En general, tales cambios se realizan con el fin de causar una persistente estado de ejecución. Este tipo de infiltración puede monitorear las acciones del sistema y de usuario con el fin de protegerse de la eliminación. Tras la instalación de software malicioso que puede contrarrestar activamente este tipo de acciones mediante la manipulación del sistema y conectar a los procesos del sistema. Los archivos de virus se colocan en la carpeta del sistema de Windows y renombrados como componentes legítimos, esto se hace con el fin de no levantar sospechas. malware avanzado también puede eliminar la Instantáneas de volumen lo cual hace que sea difícil para las víctimas para restaurar sus datos. cepas ransomware también pueden interactuar con el Volume Manager lo que hace posible el acceso a todo el almacenamiento extraíble y recursos compartidos de red disponibles. Uno de los hechos peligrosos es que los usuarios de malware tienden a utilizar estas instrucciones de malware avanzada con mineros criptomoneda. Representan código malicioso que se aprovecha de los componentes de hardware disponibles con el fin de generar ingresos para los operadores.
En otros casos las cepas de virus designados pueden incluir botnet código. Este es un tipo muy peligroso de malware que puede superar a un control completo del sistema y conectarlo a una red zombi en todo el mundo. Los operadores de hackers detrás de la infección pueden entonces utilizar el poder combinado de todos los nodos (también conocido como “los robots”) a ataques de denegación de servicio ataques devastadores de.
Cuando los operadores de malware buscan para reunir información acerca de los usuarios en las campañas de chantaje potenciales que pueden optar por integrar una keylogger utilidad en el código. Se transmitirá constantemente todas las salidas de teclado, así como el movimiento del ratón a una base de datos operada por los piratas informáticos. Cuando se utiliza en combinación con una instancia de Troya los piratas informáticos también pueden ver todas las acciones de las víctimas en tiempo real.
Cómo manejar infecciones de virus informáticos
En muchos casos los usuarios de computadoras pueden no ser conscientes de que han sido infiltradas por un virus. Los analistas de seguridad en cuenta que hay un aumento de la red de bots y las muestras de sigilo que no dan una indicación visible de que las máquinas se han visto afectados. Como se explicó anteriormente sus motores de malware tienen la capacidad de conectar a los procesos del sistema y como tal no es visible incluso si los usuarios intentan investigar una posible intrusión.
Combinado con el hecho de que muchos de los ejemplos avanzados en su totalidad puedan evitar o eliminar el software antivirus existente, sólo el uso de una solución anti-spyware de la calidad puede proteger los usuarios y eliminar las infecciones encontradas. Es muy recomendable que todos los usuarios de ordenadores escanear su sistema en busca de virus.
Escáner Spy Hunter sólo detectará la amenaza. Si desea que la amenaza se elimine de forma automática, usted necesita comprar la versión completa de la herramienta anti-malware.Obtenga más información sobre la herramienta de SpyHunter Anti-Malware / Cómo desinstalar SpyHunter