Computer viruses are rapidly evolving as hackers are devising new types of malware and delivery mechanisms. Despite the fact that most ordinary computer users perceive them as single executable files that execute a predefined script behavior, the current attack campaigns show an entirely different manner of handling files. The computer virus landscape is rapidly changing as next-generation malware pieces are being produced. In certain situations, the security analysts race against the hackers as infections can remain undetected for long periods of time. This article explores some of the contemporary computer virus design samples and the essential malware components that have become standard in the last few years.
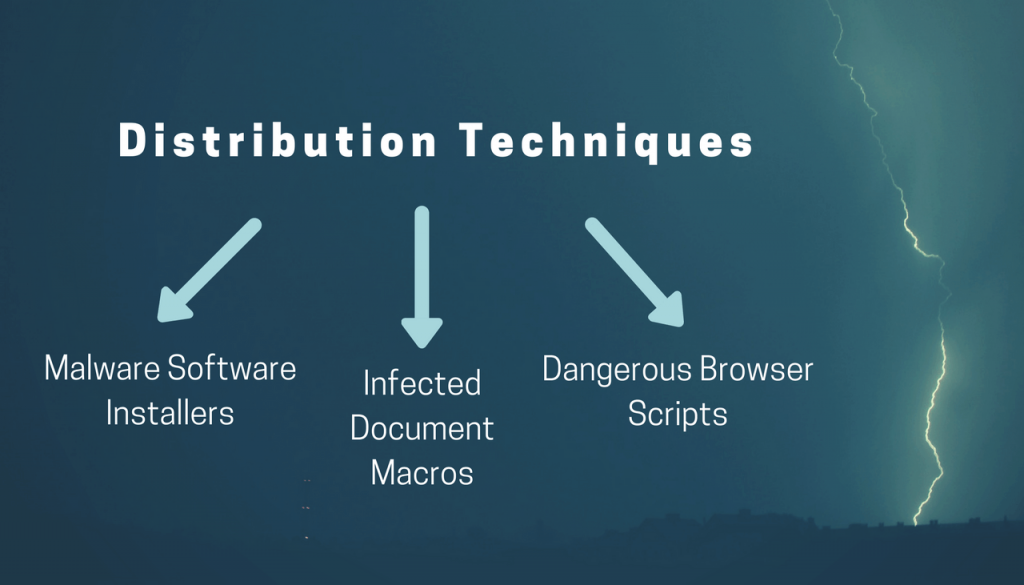
Malware Principles: Distribution Techniques
One of the most important aspects of the various attack campaigns is the planning stage. To a larger extent, the infection mechanism remains much more important than the actual malware components themselves. For a computer criminal, the most dangerous task is the initial intrusion phase as they need to uncover a way to hack into the intended targets. In the last few years, the distribution strategies have dramatically shifted as the criminals utilize a wide range of tools, web services, and advanced mechanisms.
Computer users can become victims of elaborate phishing scams that utilize multiple social engineering strategies. This may be done by sending links to hacker-controlled sites or a piece of malware file. Instead of relying on a single executable file that can easily be scanned with a simple real-time antivirus engine, the hackers can integrate downloadable modules that use a several stage delivery process. There are several strategies that have been found to be effective in deploying viruses on a worldwide scale.
- Malware Software Installers — The criminals can download legitimate software installers from the official vendor download pages. They are modified to include malware code, the resulting file is then distributed using a variety of ways: email messages, counterfeit download pages, P2P networks and etc.
- Infected Document Macros — These type of documents pose as legitimate documents of user interests and pose as invoices, notifications or letters. They can be of various types (rich text documents, spreadsheets or presentations) and launch a notification prompt which asks the victims to enable the built-in macros (scripts). If this is done the virus infection follows.
- Dangerous Browser Scripts — When the attacks involve counterfeit web browser plugins (also known as hijackers). Usually they redirect the victims to a hacker-operated site by changing the default settings. During the initial infection the virus sample can also be deployed on the victim computers.
Other direct ways of delivering virus infections involve the creation of malware sites. They use the same graphics and text as legitimate sites and usually pose as counterfeit copies of Internet services and download portals. The hackers register domain names that are similar to the legitimate sites, as a consequence many users fall victim to them.
Lately, viruses are also distributed using social media messages from fake profiles, chat programs, and web forums. This goes on further in in-game chats, gaming communities (such as Steam) and other related applications.
Initial Virus Infection Mechanisms
Once the viruses have been deployed to the victim hosts the first stage of the infection is started. Usually, most malware threats start their engines as soon as this is done which is the default behavior. Anti-malware software have the ability to watch out for this behavior and can immediately signal the scanning software to run a deep analysis of the potentially harmful file. As a result, these strains can bypass real-time engines. This is related to the stealth protection capabilities that counter the expected behavior. They can also go through the system searching for other security software. If any are found they can be entirely bypassed or altogether removed. The viruses can also be programmed to delete themselves and avoid detection.
The next step would be institute an information gathering module. It uses a separate module that is able to extract a lot of data from the compromised hosts. The security experts usually classify the information into two main groups:
- Anonymous Metrics — They are used by the criminals to judge how effective the attack campaign is. Normally the data consists of operating system version data and related information.
- Personally-Identifiable Data — This type is extracted using a special instruction that seeks strings related to the users identity. As a result the hackers can obtain information such as the victim’s name, address, phone, interests, account credentials and passwords.
This information can be relayed to the hacker operators using a one-time connection. In other cases, a constant connection can be made with the criminal controllers via a command and control server. Usually, encrypted connections are the norm and hackers can utilize them to send arbitrary commands to the victims. In certain cases, it can also be used to deliver additional malware threats. A Trojan infection can follow which would allow the hacker operators to spy on the victims in real-time as well as take over control of the machines at any given time.
In a similar way ransomware viruses can be deployed to the victim computers. Once they have infiltrated system their malware engines start to process sensitive user files according to a built-in list of file type extensions. The users are then blackmailed to pay a ransom fee to the hackers using a cryptocurrency.
Virus Design Trends — Implications of Advanced Infections
In the last few years, computer hackers have implemented newer concepts that further extend the capabilities of the ongoing malware attack campaigns. An addition that has become standard is the several step delivery mechanism. Once the criminals have been able to penetrate the network computers they can use the second stage to initiate various types of system changes.
For example the modification of the Windows Registry can disable certain services and it is also the cause of application failure. Usually, such changes are made in order to cause a persistent state of execution. This type of infiltration can monitor the system and user actions in order to protect itself from removal. Following the malware installation it can actively counter such actions by manipulating the system and hooking up to system processes. The virus files are placed in the Windows system folder and renamed as legitimate components, this is done in order not to raise suspicion. Advanced malware can also delete the Shadow Volume Copies which makes it hard for the victims to restore their data. Ransomware strains can also interact with the Volume Manager which makes it possible to access all removable storage and available network shares. One of the dangerous facts is that malware users tend to use these advanced malware instructions with cryptocurrency miners. They represent malware code that takes advantage of the available hardware components in order to generate income for the operators.
In other cases the designated virus strains can include botnet code. This is a very dangerous type of malware that can overtake complete control of the system and connect it to a worldwide zombie network. The hacker operators behind the infection can then use the combined power of all nodes (also known as “bots”) to launch devastating denial of service attacks.
When the malware operators seek out to gather intelligence about the users in prospective blackmail campaigns they can opt to integrate a keylogger utility in the code. It will constantly transmit all keyboard output as well as mouse movement to a database operated by the hackers. When used in combination with a Trojan instance the hackers can also view all victim actions in real time.
How To Handle Computer Virus Infections
In many cases computer users may be unaware that they have been infiltrated by a virus. The security analysts note that there is a rise in the botnet and stealth samples that do not give out a visible indication that the machines have been impacted. As explained above their malware engines have the ability to hook up to system processes and as such is not visible even if the users attempt to investigate a potential intrusion.
Combined with the fact that a lot of the advanced samples can entirely bypass or remove the existing anti-virus software, only the use of a quality anti-spyware solution can protect the users and remove found infections. We highly recommend that all computers users scan their system for viruses.
Spy Hunter scanner will only detect the threat. If you want the threat to be automatically removed, you need to purchase the full version of the anti-malware tool.Find Out More About SpyHunter Anti-Malware Tool / How to Uninstall SpyHunter