El troyano venganza es un arma peligrosa utilizado en contra de los usuarios de computadoras en todo el mundo. Infecta principalmente a través de instaladores de software infectados. Nuestro artículo da una visión general de su comportamiento en función de las muestras recogidas e informes disponibles, También puede ser útil en el intento de eliminar el virus.

Resumen de amenazas
| Nombre | La venganza de Troya |
| Escribe | Trojan |
| Descripción breve | El troyano Revenge es un virus informático diseñado para infiltrarse silenciosamente en los sistemas informáticos.. |
| Los síntomas | Las víctimas no pueden experimentar síntomas aparentes de infección. |
| Método de distribución | Las vulnerabilidades de software, Instalaciones de dominio público, paquetes combinados, Guiones y otros. |
| Herramienta de detección |
Ver si su sistema ha sido afectado por malware
Descargar
Herramienta de eliminación de software malintencionado
|
| Experiencia de usuario | Unirse a nuestro foro hablar sobre el troyano Revenge. |

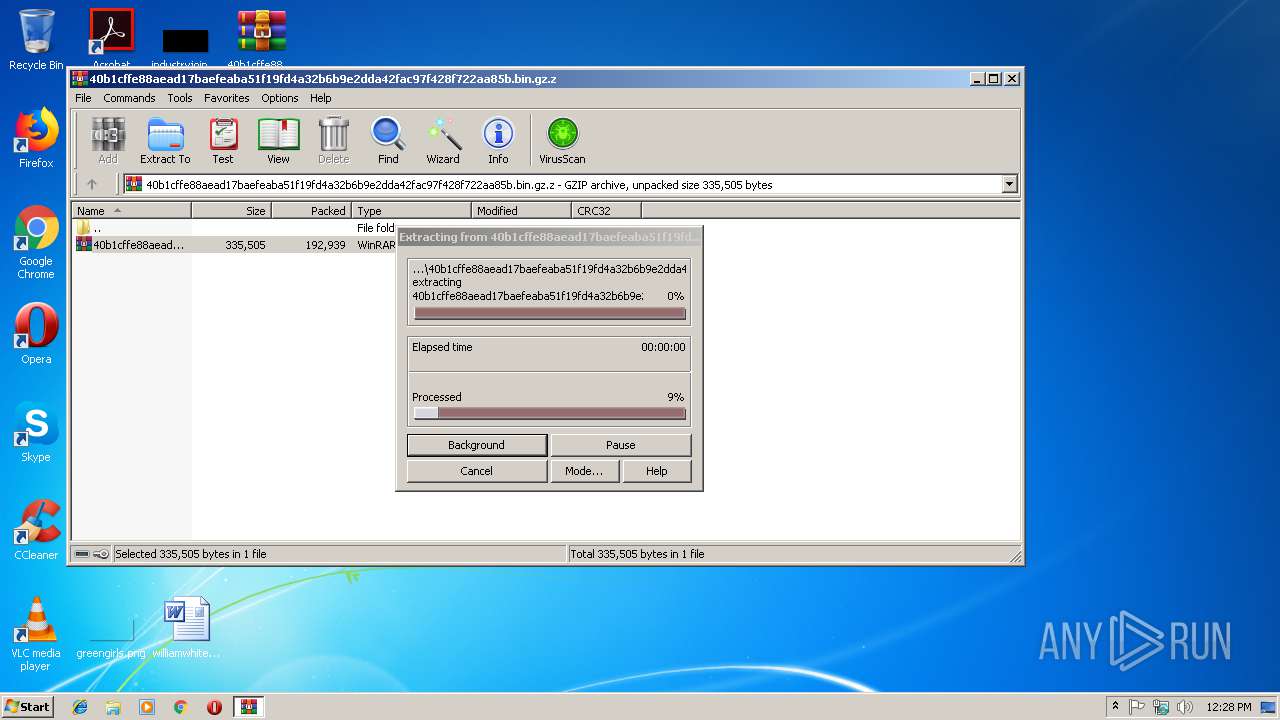
Troyano Revenge: métodos de distribución
El troyano Revenge ha sido detectado en una campaña de ataque reciente.. Un colectivo de piratas informáticos desconocido está detrás de los ataques en curso, por el momento no hay información sobre su identidad. Las muestras capturadas se identificaron como malware a través de uno de los mecanismos de intrusión más comunes: documentos infectados. El código de instalación de virus forma parte de macros que están incrustadas en los documentos de carga útil, que pueden ser de cualquiera de los tipos populares: documentos de texto, hojas de cálculo, presentaciones y bases de datos. Una vez que sean abiertos por los usuarios víctimas, aparecerá un mensaje pidiéndoles a las víctimas que habiliten el contenido.. La ventana generalmente indicará que esto es necesario para ver correctamente los archivos..
Lo que es más peligroso es que también se pueden emplear otras tácticas similares. Uno de los casos comunes es cuando los piratas informáticos incorporan las instrucciones de instalación del virus en archivos de configuración de software. Se dirigen a aplicaciones que los usuarios finales descargan popularmente, como las utilidades del sistema., suites creatividad, de productividad de oficina y aplicaciones y etc..
Tanto los archivos de virus en sí mismos como estos dos tipos de carga útil generalmente se propagan a través de métodos que pueden infectar a miles de usuarios a la vez.. Hay varios métodos como los siguientes:
- Los mensajes de correo electrónico SPAM - Los piratas informáticos pueden crear correos electrónicos de phishing que aparezcan como notificaciones enviadas por servicios legítimos.. Esto se hace utilizando su propio diseño de diseño y contenido del cuerpo del texto.. Los mensajes de phishing de correo electrónico falsos vincularán los archivos en enlaces de texto o contenidos interactivos. Alternativamente, pueden adjuntarse directamente a los mensajes..
- Páginas web maliciosas - Una estrategia relacionada es crear páginas web que imiten servicios legítimos., portales de descarga, y páginas de destino, etc.. Están alojados en nombres de dominio que suenan similares y, en algunos casos, utilizan certificados de seguridad robados o generados por piratas informáticos..
- Sitios de intercambio de archivos - Tanto los archivos independientes como las cargas útiles infectadas están ampliamente disponibles en redes como BitTorrent, donde tanto el contenido legítimo como el pirata se comparte libremente entre los usuarios de Internet..
- Los secuestradores de navegador - Los delincuentes pueden crear complementos de navegador web peligrosos que se hacen compatibles con los navegadores web más populares y se cargan en los repositorios relevantes.. Están acompañadas de reseñas de usuarios falsas y credenciales de desarrollador robadas o creadas por piratas informáticos para confundir a las víctimas haciéndoles pensar que la extensión es segura.. Sus descripciones prometen la adición de nuevas funciones u optimizaciones de rendimiento..
Además, se pueden utilizar otras tácticas en los próximos ataques y las próximas versiones del troyano Revenge..

Troyano Revenge - Descripción detallada
El troyano Revenge parece ser una creación original que no utiliza ningún fragmento de código de amenazas anteriores.. Al momento de escribir este artículo, hay información sobre la identidad del grupo detrás de los ataques en curso.. Suponemos que la amenaza es de naturaleza modular y que se pueden agregar varios módulos.
La instancia capturada del troyano Revenge parece lanzar un motor principal que se conecta a un servidor controlado por piratas informáticos y permite a los operadores criminales espiar a las víctimas.. A través de esta conexión segura, tienen la capacidad de tomar el control de las máquinas afectadas., robar sus datos y realizar todo tipo de acciones maliciosas.
Se lanza un script basado en PowerShell que permite agregar todo tipo de componentes. Los troyanos como este suelen incluir un determinado conjunto de patrones de comportamiento comunes. Una lista de ellos es el siguiente:
- Recuperación de información - El motor se puede programar para extraer información confidencial que se puede utilizar para generar una identificación única que es específica para cada computadora individual. Esto se realiza mediante un algoritmo que toma sus parámetros de entrada de conjuntos de datos como la lista de piezas de los componentes de hardware instalados., ajustes de usuario, preferencias regionales y otras métricas relacionadas. La otra mecánica peligrosa utilizada por los troyanos es la exposición de información personal que se realiza programando las cadenas para buscar cadenas que contengan directamente revelar a las víctimas. Los comunes incluyen su nombre, dirección, número de teléfono, intereses y las credenciales de la cuenta almacenados. Si el troyano interactúa con el Administrador de volumen de Windows, también puede buscar los dispositivos de almacenamiento extraíbles y los recursos compartidos de red disponibles.. Los conjuntos de datos obtenidos se pueden utilizar para varios delitos, incluido el robo de identidad., chantaje y abuso financiero.
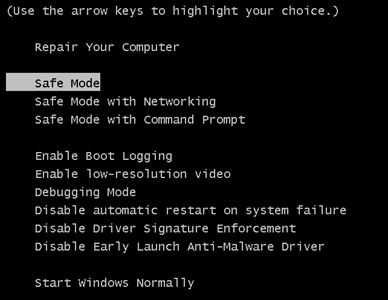
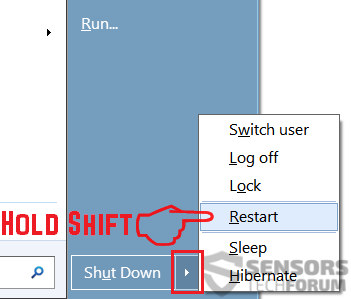
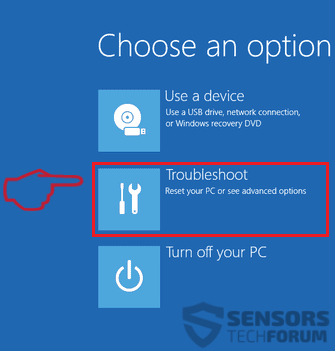
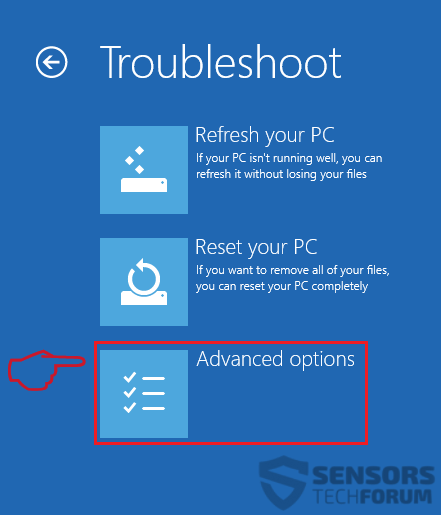
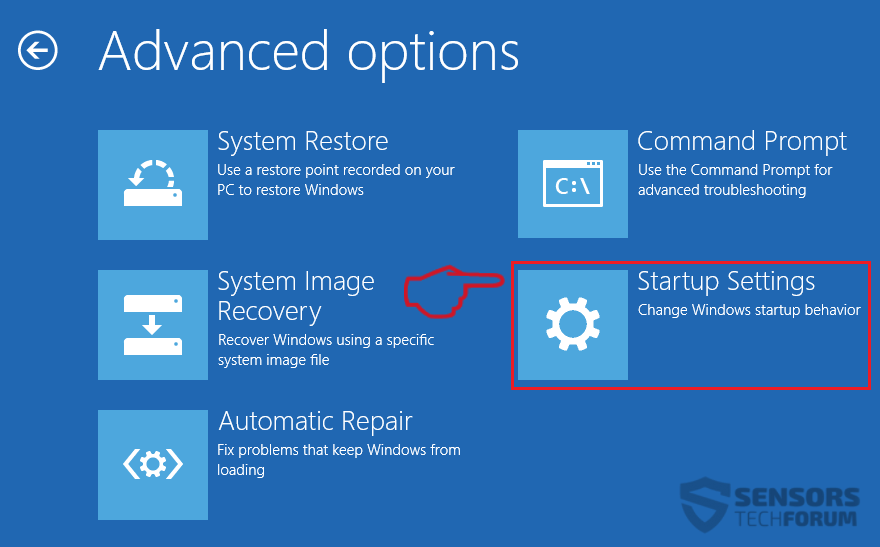
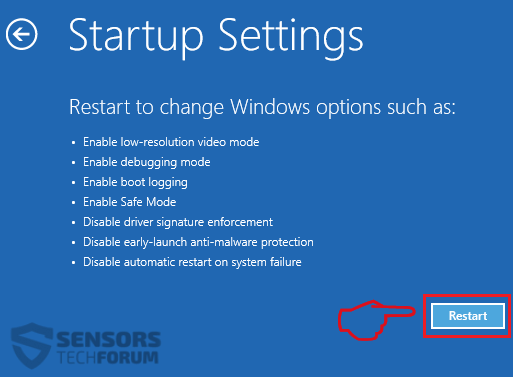
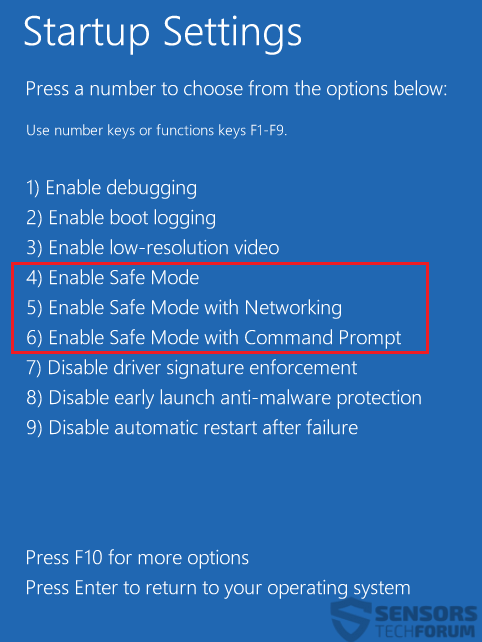
- Modificación de opciones de inicio - Un mecanismo popular que forma parte de la mayoría de los troyanos., posiblemente incluyendo futuras variantes del troyano Revenge, es la capacidad de modificar las opciones de arranque y los archivos de configuración que lo configurarán para que se inicie automáticamente una vez que la computadora esté encendida. Esto también puede deshabilitar la mayoría de las guías de recuperación de usuario manuales, ya que dependen del acceso a los menús de inicio de recuperación..
- Registro de Cambios de Windows - El módulo troyano es capaz de acceder a los registros del Registro no solo para crear cadenas para sí mismo sino también para modificar las existentes.. Si los valores que utiliza el sistema operativo se ven afectados, los usuarios víctimas no podrán acceder a determinados servicios y pueden experimentar graves problemas de rendimiento.. Los cambios en las cadenas utilizadas por aplicaciones de terceros pueden provocar errores inesperados.
- La eliminación de datos confidenciales - El motor se puede programar para localizar y eliminar archivos confidenciales que pueden interrumpir gravemente el procedimiento de recuperación habitual. Esto se hace apuntando a los puntos de restauración del sistema, Las copias de seguridad, Instantáneas de volumen y etc.. En este caso, las víctimas necesitarán ver una combinación de una utilidad anti-spyware de nivel profesional y un programa de recuperación de datos..
- Las cargas útiles adicionales de entrega - Se puede indicar al troyano Revenge que inserte otras amenazas maliciosas en las máquinas comprometidas..
Las campañas del troyano Future Revenge pueden recibir instrucciones para llevar a cabo otras acciones configuradas por los piratas informáticos..

Eliminar el troyano Revenge
Si su sistema informático fue infectado con el La venganza de Troya, usted debe tener un poco de experiencia en la eliminación de software malintencionado. Usted debe deshacerse de este troyano lo más rápido posible antes de que pueda tener la oportunidad de propagarse e infectar más otros ordenadores. Debe eliminar el troyano y seguir la guía de instrucciones paso a paso se proporciona a continuación.
Nota! Su sistema informático puede verse afectada por La venganza de Troya y otras amenazas.
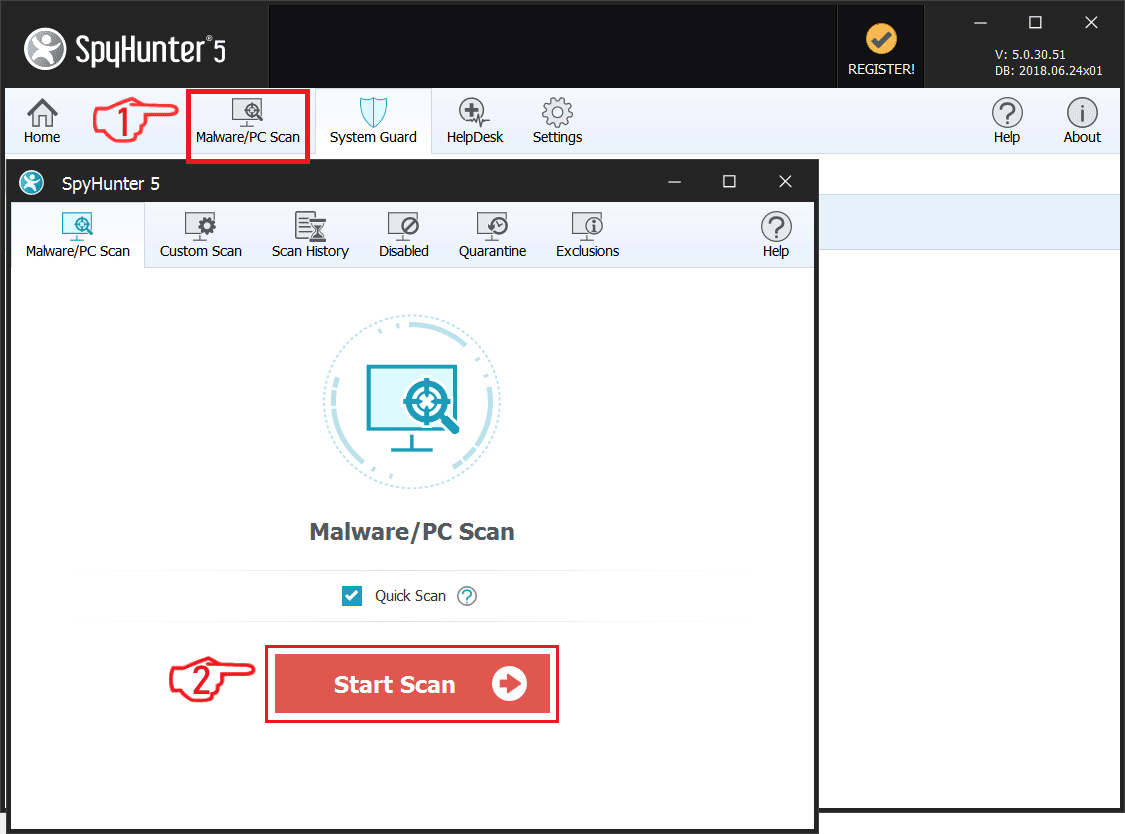
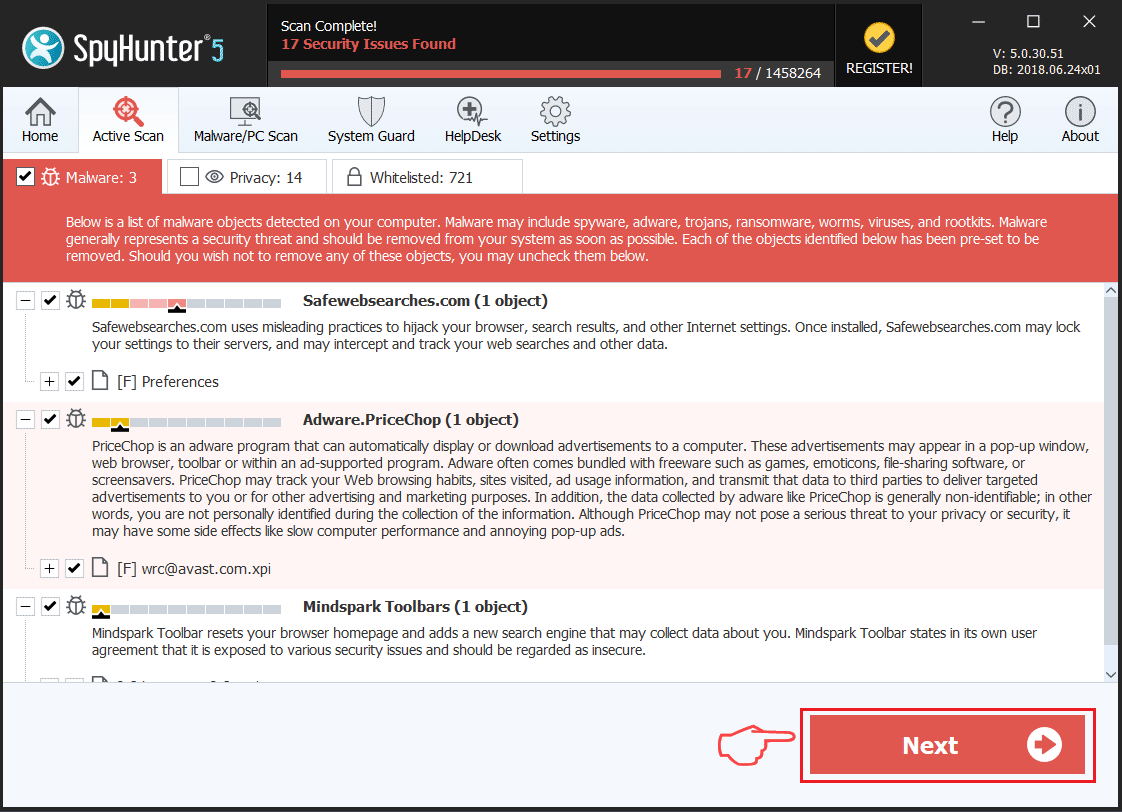
Escanear su PC con SpyHunter
SpyHunter es una poderosa herramienta de eliminación de malware diseñado para ayudar a los usuarios con el análisis de la seguridad del sistema en profundidad, detección y eliminación de La venganza de Troya.
Tenga en cuenta, que el escáner del SpyHunter es sólo para la detección de malware. Si SpyHunter detecta malware en su PC, usted tendrá que comprar herramienta de eliminación de malware de SpyHunter para eliminar las amenazas de malware. Leer nuestra SpyHunter 5 opinión. Haga clic en los enlaces correspondientes para comprobar de SpyHunter EULA, política de privacidad y Criterios de evaluación de amenazas.
Para eliminar el troyano Revenge sigue estos pasos:
Utilizar SpyHunter para detectar programas maliciosos y no deseados
Preparation before removing Revenge Trojan.
Antes de iniciar el proceso de eliminación real, se recomienda que usted hace los siguientes pasos de preparación.
- Asegúrate de que tienes estas instrucciones siempre abierto y delante de sus ojos.
- Hacer una copia de seguridad de todos sus archivos, aunque pudieran ser dañados. Debe hacer una copia de seguridad de sus datos con una solución de copia de nube y asegurar sus archivos contra cualquier tipo de pérdida, incluso de las amenazas más graves.
- Ser paciente ya que esto podría tomar un tiempo.
- Escanear en busca de malware
- Arreglar registros
- Eliminar archivos de virus
Paso 1: Analizar en busca de troyano Revenge con la herramienta de SpyHunter Anti-Malware



Paso 2: Limpiar los registros, creado por Revenge Trojan en su computadora.
Los registros normalmente dirigidos de máquinas Windows son los siguientes:
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion Run
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion Run
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion RunOnce
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion RunOnce
Puede acceder a ellos abriendo el editor del registro de Windows y eliminar cualquier valor, creado por el troyano Revenge allí. Esto puede ocurrir siguiendo los pasos debajo:


 Propina: Para encontrar un valor creado por virus, usted puede hacer clic derecho sobre él y haga clic "Modificar" para ver qué archivo que está configurado para ejecutarse. Si esta es la ubicación del archivo de virus, quitar el valor.
Propina: Para encontrar un valor creado por virus, usted puede hacer clic derecho sobre él y haga clic "Modificar" para ver qué archivo que está configurado para ejecutarse. Si esta es la ubicación del archivo de virus, quitar el valor.Paso 3: Find virus files created by Revenge Trojan on your PC.
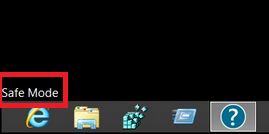
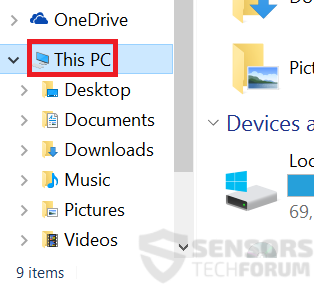
1.Para Windows 8, 8.1 y 10.
Para más nuevos sistemas operativos Windows
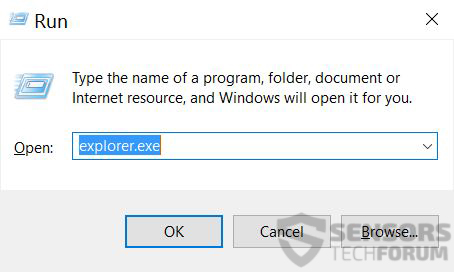
1: En su teclado de prensa + R y escribe explorer.exe en el Carrera cuadro de texto y haga clic en el OK botón.

2: Haga clic en su PC en la barra de acceso rápido. Esto suele ser un icono con un monitor y su nombre es ya sea "Mi computadora", "Mi PC" o "Este PC" o lo que sea que usted ha nombrado.

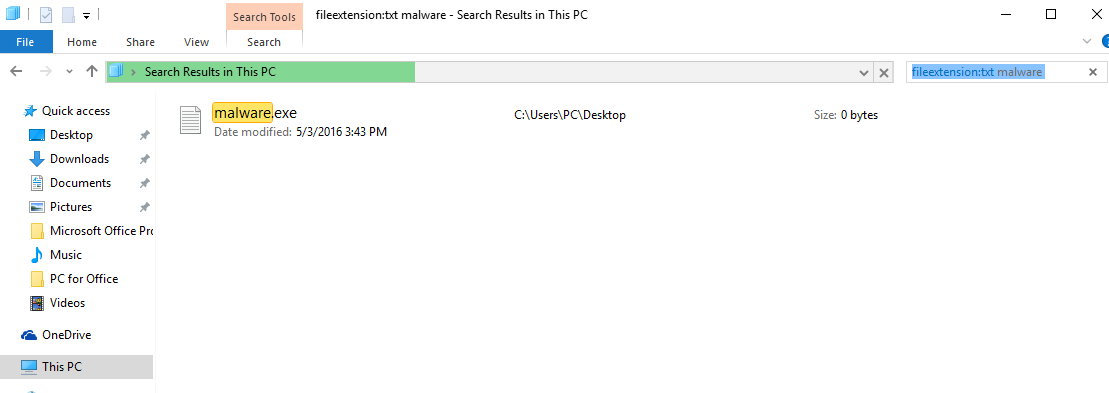
3: Navegue hasta el cuadro de búsqueda en la esquina superior derecha de la pantalla de su PC y escriba "FileExtension:" y después de lo cual escriba la extensión de archivo. Si usted está buscando para ejecutables maliciosos, Un ejemplo puede ser "FileExtension:exe". Después de hacer eso, dejar un espacio y escriba el nombre del archivo que cree que el malware ha creado. Aquí es cómo puede aparecer si se ha encontrado el archivo:

N.B. We recommend to wait for the green loading bar in the navigation box to fill up in case the PC is looking for the file and hasn't found it yet.
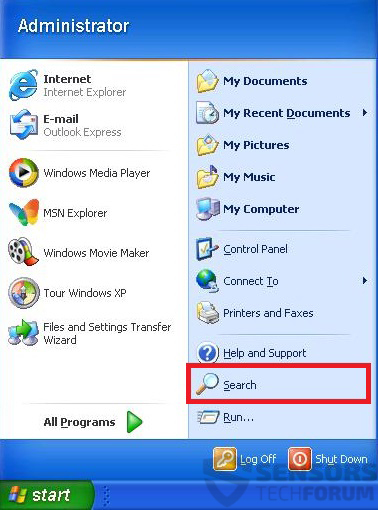
2.Para Windows XP, Vista, y 7.
Para más viejos sistemas operativos Windows
En los sistemas operativos Windows más antiguos, el enfoque convencional debería ser el efectivo:
1: Haga clic en el Menu de inicio icono (por lo general en su parte inferior izquierda) y luego elegir el Búsqueda preferencia.

2: Después de que aparezca la ventana de búsqueda, escoger Más opciones avanzadas Del cuadro de asistente de búsqueda. Otra forma es haciendo clic en Todos los archivos y carpetas.

3: Después de ese tipo el nombre del archivo que está buscando y haga clic en el botón Buscar. Esto puede llevar algún tiempo después del cual aparecerán resultados. Si usted ha encontrado el archivo malicioso, usted puede copiar o abrir por su ubicación botón derecho del ratón en eso.
Ahora usted debería ser capaz de descubrir cualquier archivo en Windows, siempre y cuando se encuentra en su disco duro y no se oculta a través de un software especial.
Revenge Trojan FAQ
What Does Revenge Trojan Trojan Do?
The Revenge Trojan Trojan es un programa informático malicioso diseñado para interrumpir, dañar, u obtener acceso no autorizado a un sistema informático. Se puede utilizar para robar datos confidenciales., obtener el control de un sistema, o lanzar otras actividades maliciosas.
¿Pueden los troyanos robar contraseñas??
Sí, Troyanos, like Revenge Trojan, puede robar contraseñas. Estos programas maliciosos are designed to gain access to a user's computer, espiar a las víctimas y robar información confidencial como datos bancarios y contraseñas.
Can Revenge Trojan Trojan Hide Itself?
Sí, puede. Un troyano puede usar varias técnicas para enmascararse, incluyendo rootkits, cifrado, y ofuscación, para esconderse de los escáneres de seguridad y evadir la detección.
¿Se puede eliminar un troyano restableciendo los valores de fábrica??
Sí, un troyano se puede eliminar restableciendo los valores de fábrica de su dispositivo. Esto se debe a que restaurará el dispositivo a su estado original., eliminando cualquier software malicioso que pueda haber sido instalado. Tenga en cuenta que hay troyanos más sofisticados que dejan puertas traseras y vuelven a infectar incluso después de un restablecimiento de fábrica..
Can Revenge Trojan Trojan Infect WiFi?
Sí, es posible que un troyano infecte redes WiFi. Cuando un usuario se conecta a la red infectada, el troyano puede propagarse a otros dispositivos conectados y puede acceder a información confidencial en la red.
¿Se pueden eliminar los troyanos??
Sí, Los troyanos se pueden eliminar. Esto generalmente se hace ejecutando un poderoso programa antivirus o antimalware que está diseñado para detectar y eliminar archivos maliciosos.. En algunos casos, también puede ser necesaria la eliminación manual del troyano.
¿Pueden los troyanos robar archivos??
Sí, Los troyanos pueden robar archivos si están instalados en una computadora. Esto se hace permitiendo que el autor de malware o usuario para obtener acceso a la computadora y luego robar los archivos almacenados en ella.
¿Qué antimalware puede eliminar troyanos??
Programas anti-malware como SpyHunter son capaces de buscar y eliminar troyanos de su computadora. Es importante mantener su anti-malware actualizado y escanear regularmente su sistema en busca de cualquier software malicioso..
¿Pueden los troyanos infectar USB??
Sí, Los troyanos pueden infectar USB dispositivos. Troyanos USB normalmente se propaga a través de archivos maliciosos descargados de Internet o compartidos por correo electrónico, allowing the hacker to gain access to a user's confidential data.
About the Revenge Trojan Research
El contenido que publicamos en SensorsTechForum.com, this Revenge Trojan how-to removal guide included, es el resultado de una extensa investigación, trabajo duro y la dedicación de nuestro equipo para ayudarlo a eliminar el problema específico de los troyanos.
How did we conduct the research on Revenge Trojan?
Tenga en cuenta que nuestra investigación se basa en una investigación independiente. Estamos en contacto con investigadores de seguridad independientes, gracias a lo cual recibimos actualizaciones diarias sobre las últimas definiciones de malware, incluidos los diversos tipos de troyanos (puerta trasera, downloader, Infostealer, rescate, etc)
Además, the research behind the Revenge Trojan threat is backed with VirusTotal.
Para comprender mejor la amenaza que representan los troyanos, Consulte los siguientes artículos que proporcionan detalles informados..


 1. Para Windows XP, Vista y 7.
1. Para Windows XP, Vista y 7. 2. Para Windows 8, 8.1 y 10.
2. Para Windows 8, 8.1 y 10. entradas de registro Fix creadas por el malware y PUP en su PC.
entradas de registro Fix creadas por el malware y PUP en su PC.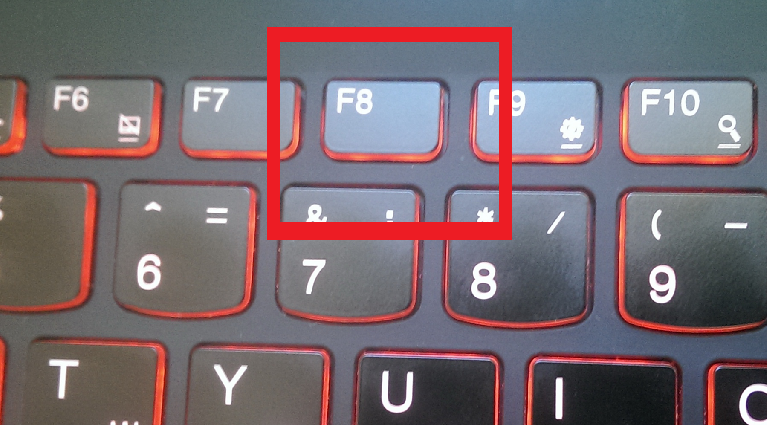
 1. Instale SpyHunter para buscar el troyano Revenge y elimínelos.
1. Instale SpyHunter para buscar el troyano Revenge y elimínelos.