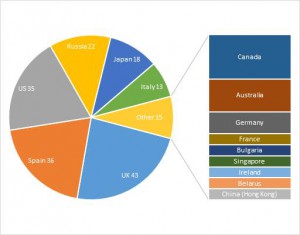
 Especialistas em segurança com relatório do Kaspersky Lab que uma marca nova estirpe do infame Trojan Zeus está batendo sistemas bancários todo o mundo. A nova ameaça Trojan-Banker.Win32.Chthonic, ou apenas Chthonic, já afetou cento e cinquenta bancos e vinte sistemas de pagamento em quinze países. Instituições financeiras na Espanha, Rússia, Itália, Japão e Reino Unido parecem ser os alvos principais do ataque ctônico.
Especialistas em segurança com relatório do Kaspersky Lab que uma marca nova estirpe do infame Trojan Zeus está batendo sistemas bancários todo o mundo. A nova ameaça Trojan-Banker.Win32.Chthonic, ou apenas Chthonic, já afetou cento e cinquenta bancos e vinte sistemas de pagamento em quinze países. Instituições financeiras na Espanha, Rússia, Itália, Japão e Reino Unido parecem ser os alvos principais do ataque ctônico.
O Caminho do Chthonic
Os autores do Chthonic o projetaram para explorar as funções do PC, juntamente com o teclado e a câmera da web, a fim de roubar credenciais de banco online, como senhas. Os criminosos também podem se conectar à máquina comprometida de um local remoto e comandá-la para concluir várias transações.
A arma preferida de Chthonic - injetores de teia, que pode permitir que a ameaça insira seu código malicioso e imagens no código da página da web do banco carregada diretamente do computador afetado. Isso permite que os criminosos coloquem as mãos nos PINs da vítima, número de telefone e senhas de uso único, junto com quaisquer detalhes de login (usuário e senha) que o usuário entrou.
Distribuição e infecção de Chthonic
Especialistas relatam que o principal método de infecção usado para distribuir o Trojan-Banker.Win32.Chthonic para a máquina visada é através de e-mails maliciosos contendo exploits. Nesse caso, o e-mail contém um documento anexado com uma extensão .DOC, cujo objetivo é estabelecer um backdoor para código malicioso. No anexo, há um documento RTF especialmente projetado que explora a vulnerabilidade CVE-2014-1761 em produtos Microsoft Office.
Enquanto a ameaça é baixada, código malicioso contendo um arquivo de configuração criptografado é inserido no processo msiexec.exe, o que resulta na instalação de vários módulos maliciosos no computador comprometido.
Esses módulos podem realizar as seguintes tarefas:
- Colete informações do sistema
- Permitir acesso remoto
- Roubar senhas que foram salvas
- Registrar teclas
- Grave som e vídeo usando o microfone e a webcam
Outra técnica empregada pelos atacantes para entregar o Chthonic é fazer o download da ameaça para a máquina da vítima por meio do bot Andromeda (também conhecido como Backdoor.Win32.Androm).
Vítimas de Chthonic
Especialistas relatam que, no caso de um banco japonês que foi atingido por Trojan-Banker.Win32.Chthonic, o malware conseguiu esconder os avisos do banco e injetar um script que permite que os criminosos concluam uma série de transações através da conta da vítima.
Outro novo exemplo é uma instituição financeira russa, cujos clientes foram apresentados a páginas bancárias falsas no momento em que estavam conectados. Para este efeito,, o cavalo de Tróia criou um iframe com uma cópia de phishing da página da web exatamente com o mesmo tamanho da janela original.
O Trojan-Banker.Win32.Chthonic é semelhante a outros Trojans em uso, por exemplo:
- Chthonic usa o mesmo downloader e criptografador que os bots Andromeda
- Usa uma máquina virtual que lembra aquela usada no malware KINS
- Tem a mesma técnica de criptografia que os cavalos de Troia Zeus V2 e Zeus AES
Felizmente, uma grande parte dos fragmentos de código empregados pela Chthonic para injeções na web não podem mais ser usados, por causa da rápida reação dos bancos. Em alguns casos, eles mudaram a estrutura de suas páginas e em outros - os domínios, também.
O analista sênior de malware da Kaspersky Lab, Yury Namestnikov afirma que a descoberta do Chthonic é um sinal claro de que o Trojan ZeuS ainda está evoluindo. Os criadores de malware estão empregando as técnicas mais recentes, que foram ajudados pelo vazamento do código-fonte do ZeuS. De acordo com o especialista, Chthonic é o próximo nível na evolução de ZeuS.
Spy Hunter GRÁTIS scanner somente detectar a ameaça. Se você quiser a ameaça de ser removido automaticamente, você precisa comprar a versão completa da ferramenta anti-malware. Saiba Mais Sobre SpyHunter Anti-Malware Ferramenta


