Este artigo foi criado para mostrar como você pode remover o GANDCRAB 5.0.1 vírus ransomware e como você pode tentar recuperar arquivos, criptografado por GANDCRAB 5.0.1 sem ter que pagar o resgate aos ciber-criminosos.
o GANDCRAB v5.0 ransomware acabou de ser atualizado em um 5.0.1 versão com algumas pequenas melhorias. O principal objetivo do vírus é entrar no PC da vítima sem ser percebido e criptografar os arquivos na máquina vitimada, depois disso, deixe para trás uma extensão de arquivo aleatória. O vírus em seguida, cai uma nota de resgate, começando com 5 letras e parecido com o seguinte – {5 símbolos aleatórios}-DECRYPT.txt, ao contrário da variante anterior, que usava um tipo de arquivo .html para sua nota. A nota de resgate de GANDCRAB 5.0.1 visa convencer as vítimas a pagar um resgate para que seus arquivos criptografados sejam restaurados ao estado de funcionamento. Caso seu computador tenha sido infectado pelo GANDCRAB 5.0.1 você deveria ler este artigo. O objetivo é ajudá-lo a entender mais sobre como GANDCRAB funciona e mostra métodos para apagar este vírus e tentar recuperar arquivos, criptografado por ele sem pagar resgate diretamente.
GANDCRAB 5.0.1 ransomware – detalhes
| Nome | GANDCRAB 5.0.1 vírus, também conhecido como UDS:Trojan.Win32.Chapak.gen, Resgate:Win32 / StopCrypt.KM!MTB, Win32:PWSX-gen [Trj], Win32:PWSX-gen [Trj], Uma variante do Win32 / GenKryptik.FHJB – mais detecções deste vírus em VirusTotal |
| Extensão de arquivo | GANDCRAB 5.0.1 |
| Tipo | ransomware, Cryptovirus |
| Pequena descrição | Os arquivos criptografa ransomware no seu sistema de computador e exige um resgate a ser pago para recuperá-los, alegadamente. |
| Os sintomas | o GANDCRAB 5.0.1 Vírus ransomware criptografará seus arquivos |
| Ransom Exigir Nota | _readme.txt |
| distribuição Método | Os e-mails de spam, Anexos de e-mail |
| Ferramenta de detecção |
Veja se o seu dispositivo foi afetado pelo GANDCRAB 5.0.1
Baixar
Remoção de Malware Ferramenta
|
GANDCRAB 5.0.1 – Métodos de distribuição
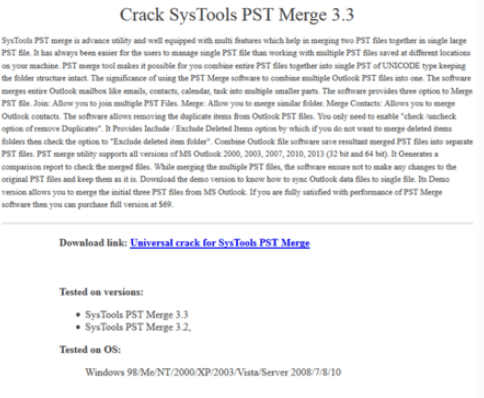
A última iteração de ransomware GANDCRAB não trapaceia no antigo método de ser replicado. O malware pode infectar por meio de sites comercializados, a ideia principal por trás disso é fingir que o programa que você procura online tem um crack que está disponível para download. Esses URLs falsos do site de download do WordPress estão se tornando uma prática cada vez mais comum, conforme detectamos nos últimos meses. Aqui está como um URL de crack falso da versão anterior do GandCrab aparece quando você procura as rachaduras para vários conversores, ferramentas do sistema e outros tipos de programas aparentemente úteis:
A lista completa de programas que são imitados pelo GandCrab pode ser vista na história relacionada abaixo:
relacionado: GandCrab 4 Rachaduras ransomware hoje infecta através do software
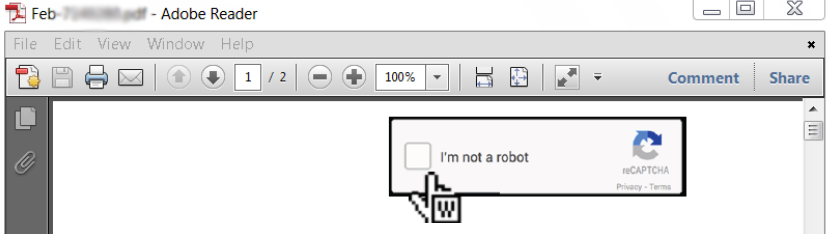
Mas esta não é a única fonte principal de propagação usada por GandCrab 5.0.1 ransomware, uma vez que o vírus também pode se espalhar através do método mais amplamente usado para espalhar vírus ransomware, que é através de mensagens de spam por e-mail. A iteração anterior do GandCrab costumava usar e-mails de spam que continham anexos de e-mail maliciosos, também conhecido como malspam. Este tipo de atividade foi usado para enganar as vítimas fazendo-as clicar em “Não sou um robô” após baixar um arquivo PDF e, em seguida, isso resulta em um arquivo do Microsoft Word que abre com macros maliciosas. Os e-mails podem ter a seguinte aparência:
De: “Brandon Clay” Brandon@cdkconstruction.org
Sujeito: Conta de eletricidade Fev-6509
Anexo: Fev-10451.pdf
Texto de corpo: Baixe o arquivo anexado.
O arquivo .PDF pode mostrar o seguinte após ser aberto:
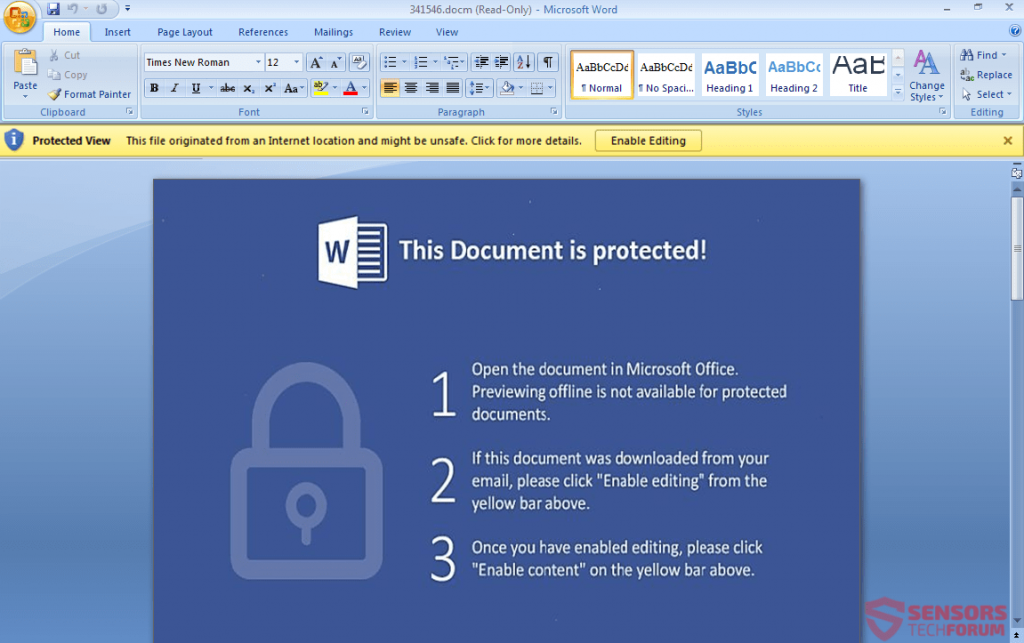
Depois disto, o usuário é induzido a clicar em “Habilitar Conteúdo” em um novo arquivo do Microsoft Word que deriva do arquivo .PDF e depois que isso for feito, GANDCRAB pode desencadear a infecção:

GANDCRAB 5.0.1 ransomware – Análise
Quando o PC da vítima é infectado com o ransomware GANDCRAB vírus, a 5.0.1 versão cai e ativa seu arquivo binário principal, que tem nomes diferentes e está localizado em uma pasta com nome aleatório no perfil “USUÁRIOS”:
→ C:\Comercial{Nome do usuário}\Área de Trabalho{Nome do arquivo de vírus GandCrab}.Exe
Após este tenha concluído, o ransomware GANDCRAB também pode descartar seu arquivo de nota de resgate, que se parece com a seguinte imagem:
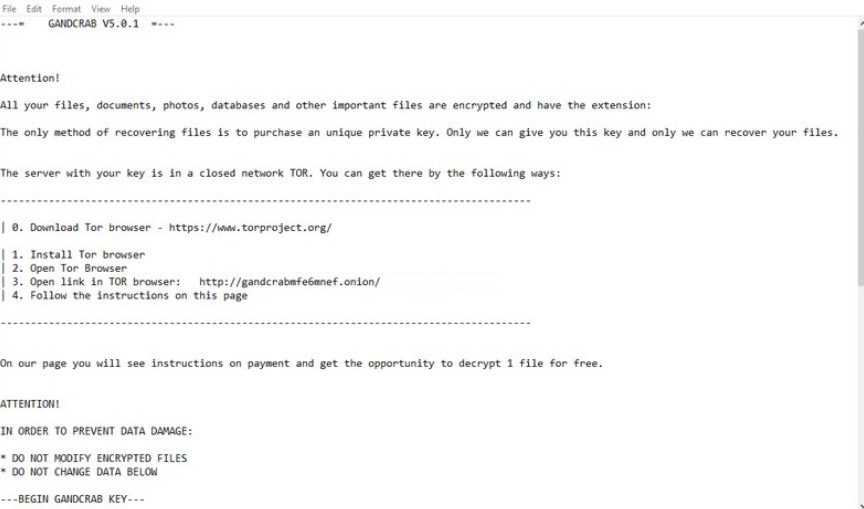
Texto da Imagem:
—= GANDCRAB V5.0.1 =—
Atenção!
Todos os seus arquivos, documentos, fotos, bases de dados e outros arquivos importantes são criptografadas e tem a extensão: {5 letras aleatórias}
O único método de recuperação de arquivos é a compra de uma chave privada única. Só podemos dar-lhe esta chave e só nós podemos recuperar seus arquivos.
O servidor com a chave está em uma rede fechada TOR. Você pode chegar lá pelas seguintes formas:———————————————————————–
| 0. Baixar navegador Tor - https://www.torproject.org/| 1. Instalar Tor Navegador
| 2. Abrir Tor Navegador
| 3. Abrir link no navegador TOR https://gandcrabmfe6mnef.onion/{identificação única da vítima}
| 4. Siga as instruções nesta páginaEm nossa página você vai ver instruções sobre o pagamento e ter a oportunidade para descriptografar 1 arquivo de graça.
ATENÇÃO!
Danosos, a fim de evitar que dados:
• NÃO MODIFICAR ARQUIVOS CRIPTOGRAFADOS
• NÃO ALTERE OS DADOS ABAIXO
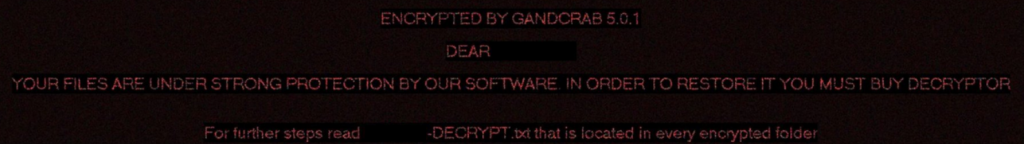
A nota de resgate leva a vítima a visitar uma página da web baseada no Tor, que é semelhante às outras versões do GandCrab, aparecendo como a imagem abaixo mostra:

Para garantir que a vítima não perca a notificação, GANDCRAB 5.0.1 também define o papel de parede para o seguinte:
Além de garantir que a vítima saiba de sua presença, GANDCRAB 5.0.1 faz muito mais do que apenas isso. O vírus também pode realizar outras atividades no PC do usuário, como adicionar valores de registro em muitas subchaves de registro do Windows. Tão longe, GANDCRAB 5.0.1 é relatado para acessar as seguintes subchaves no banco de dados do Registro do Windows:
→ HKEY_CURRENT_USER Control Panel International
HKEY_CURRENT_USER SOFTWARE keys_data data
HKEY_LOCAL_MACHINE HARDWARE DESCRIPTION System CentralProcessor 0
HKEY_LOCAL_MACHINE SOFTWARE Microsoft Wbem CIMOM
HKEY_LOCAL_MACHINE SOFTWARE Microsoft Windows NT CurrentVersion
HKEY_LOCAL_MACHINE SOFTWARE ex_data data
HKEY_LOCAL_MACHINE SYSTEM CurrentControlSet Services Tcpip Parameters
o GANDCRAB 5.0.1 também cria os seguintes mutexes no computador infectado:
→ Global 8A5BA8BEE36925045F5C.lock
Global XIAKFoxSKGOfSGOoSFOOFNOLPE
Mas os principais indicadores de comprometimento são as conexões feitas por esta iteração do ransomware GandCrab, que são relatados em VMRay ser os seguintes endereços IP:
GANDCRAB 5.0.1 ransomware – Processo de criptografia
o 5.0.1 versão de ransomware GANDCRAB acredita-se que o vírus utiliza o Salsa20 Algoritmo de criptografia. Ao contrário das versões anteriores do GandCrab, este modo de criptografia é muito mais rápido em seu processo de criptografia, de modo que é mais difícil de ser interrompido. o ransomware GANDCRAB pode realizar o processo de infecção nas seguintes etapas cronológicas:
- Degrau 1
- Degrau 2
- Degrau 3
- Degrau 4
- Degrau 5
Degrau 1: Scan for GANDCRAB 5.0.1 com SpyHunter Anti-Malware Ferramenta



Remoção automática de ransomware - Guia de Vídeo
Degrau 2: GANDCRAB Uninstall 5.0.1 e malware relacionado do Windows
Aqui é um método em alguns passos simples que deve ser capaz de desinstalar a maioria dos programas. Não importa se você estiver usando o Windows 10, 8, 7, Vista ou XP, esses passos vai começar o trabalho feito. Arrastando o programa ou a sua pasta para a lixeira pode ser um muito má decisão. Se você fizer isso, pedaços e peças do programa são deixados para trás, e que pode levar a um trabalho instável do seu PC, erros com as associações de tipo de arquivo e outras atividades desagradáveis. A maneira correta de obter um programa fora de seu computador é para desinstalá-lo. Fazer isso:


 Siga as instruções acima e você excluirá com sucesso a maioria dos programas maliciosos e indesejados.
Siga as instruções acima e você excluirá com sucesso a maioria dos programas maliciosos e indesejados.
Degrau 3: Limpe quaisquer registros, criado por GANDCRAB 5.0.1 no seu computador.
Os registros normalmente alvo de máquinas Windows são os seguintes:
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion Run
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion Run
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion RunOnce
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion RunOnce
Você pode acessá-los abrindo o editor de registro do Windows e excluir quaisquer valores, criado por GANDCRAB 5.0.1 lá. Isso pode acontecer, seguindo os passos abaixo:


 Gorjeta: Para encontrar um valor criado-vírus, você pode botão direito do mouse sobre ela e clique "Modificar" para ver qual arquivo é definido para ser executado. Se este é o local do arquivo de vírus, remover o valor.
Gorjeta: Para encontrar um valor criado-vírus, você pode botão direito do mouse sobre ela e clique "Modificar" para ver qual arquivo é definido para ser executado. Se este é o local do arquivo de vírus, remover o valor.
Antes de começar "Degrau 4", por favor Arrancar de novo para o modo Normal, no caso em que você está no Modo de Segurança.
Isto irá permitir-lhe instalar e uso SpyHunter 5 com sucesso.
Degrau 4: Inicializar o PC em modo de segurança GANDCRAB isolado e remover 5.0.1





Degrau 5: Tente restaurar arquivos criptografados por GANDCRAB 5.0.1.
Método 1: Use o STOP Decrypter da Emsisoft.
Nem todas as variantes deste ransomware pode ser descriptografado gratuitamente, mas nós adicionamos o decryptor utilizado por pesquisadores que é frequentemente atualizado com as variantes que se tornam, eventualmente descriptografado. Você pode tentar e descriptografar seus arquivos usando as instruções abaixo, mas se eles não funcionam, então, infelizmente, a sua variante do vírus ransomware não é decryptable.
Siga as instruções abaixo para usar o decrypter Emsisoft e descriptografar os arquivos de graça. Você pode baixar a ferramenta de decodificação Emsisoft ligados aqui e depois seguir os passos apresentados abaixo:
1 Botão direito do mouse na decrypter e clique em Executar como administrador como mostrado abaixo:

2. Concordo com os termos de licença:

3. Clique em "Adicionar pasta" e em seguida, adicione as pastas onde deseja que os arquivos descriptografado como debaixo mostrado:

4. Clique em "Decrypt" e esperar por seus arquivos para ser decodificado.

Nota: Crédito para o decryptor vai para pesquisadores Emsisoft que fizeram a descoberta com este vírus.
Método 2: Use software de recuperação de dados
infecções ransomware e GANDCRAB 5.0.1 apontar para criptografar seus arquivos usando um algoritmo de criptografia que podem ser muito difíceis de decifrar. É por isso que sugeriram um método de recuperação de dados que podem ajudá-lo a ir descriptografia torno direta e tentar restaurar seus arquivos. Tenha em mente que este método pode não ser 100% eficaz, mas também pode ajudá-lo um pouco ou muito em situações diferentes.
Basta clicar no link e nos menus do site na parte superior, escolher Recuperação de dados - Assistente de Recuperação de Dados para Windows ou Mac (dependendo do seu SO), e depois baixe e execute a ferramenta.
GANDCRAB 5.0.1-FAQ
O que é GANDCRAB 5.0.1 ransomware?
GANDCRAB 5.0.1 é um ransomware infecção - o software malicioso que entra no computador silenciosamente e bloqueia o acesso ao próprio computador ou criptografa seus arquivos.
Muitos vírus ransomware usam algoritmos de criptografia sofisticados para tornar seus arquivos inacessíveis. O objetivo das infecções por ransomware é exigir que você pague um pagamento por resgate para ter acesso aos seus arquivos de volta.
What Does GANDCRAB 5.0.1 Ransomware Do?
O ransomware em geral é um software malicioso que é projetado para bloquear o acesso ao seu computador ou arquivos até que um resgate seja pago.
Os vírus ransomware também podem danificar seu sistema, corromper dados e excluir arquivos, resultando na perda permanente de arquivos importantes.
How Does GANDCRAB 5.0.1 Infectar?
De várias maneiras. GANDCRAB 5.0.1 O ransomware infecta computadores sendo enviados através de e-mails de phishing, contendo anexo de vírus. Esse anexo geralmente é mascarado como um documento importante, gostar uma fatura, documento bancário ou até mesmo uma passagem de avião e parece muito convincente para os usuários.
Another way you may become a victim of GANDCRAB 5.0.1 is if you baixe um instalador falso, crack ou patch de um site de baixa reputação ou se você clicar em um link de vírus. Muitos usuários relatam ter recebido uma infecção por ransomware baixando torrents.
How to Open .GANDCRAB 5.0.1 arquivos?
Vocês can't sem um descriptografador. Neste ponto, a .GANDCRAB 5.0.1 arquivos são criptografado. Você só pode abri-los depois de descriptografados usando uma chave de descriptografia específica para o algoritmo específico.
O que fazer se um descriptografador não funcionar?
Não entre em pânico, e faça backup dos arquivos. Se um decodificador não decifrar seu .GANDCRAB 5.0.1 arquivos com sucesso, então não se desespere, porque esse vírus ainda é novo.
posso restaurar ".GANDCRAB 5.0.1" arquivos?
sim, às vezes os arquivos podem ser restaurados. Sugerimos vários métodos de recuperação de arquivos isso poderia funcionar se você quiser restaurar .GANDCRAB 5.0.1 arquivos.
Esses métodos não são de forma alguma 100% garantido que você será capaz de recuperar seus arquivos. Mas se você tiver um backup, suas chances de sucesso são muito maiores.
How To Get Rid of GANDCRAB 5.0.1 Vírus?
A maneira mais segura e eficiente de remover esta infecção por ransomware é o uso de um programa anti-malware profissional.
Ele irá procurar e localizar o GANDCRAB 5.0.1 ransomware e, em seguida, remova-o sem causar nenhum dano adicional ao seu .GANDCRAB importante 5.0.1 arquivos.
Posso denunciar ransomware às autoridades?
Caso seu computador tenha sido infectado por uma infecção de ransomware, você pode denunciá-lo aos departamentos de polícia locais. Ele pode ajudar as autoridades em todo o mundo a rastrear e determinar os autores do vírus que infectou seu computador.
Abaixo, preparamos uma lista com sites governamentais, onde você pode registrar uma denúncia caso seja vítima de um cibercrime:
Autoridades de segurança cibernética, responsável por lidar com relatórios de ataque de ransomware em diferentes regiões em todo o mundo:
Alemanha - Portal oficial da polícia alemã
Estados Unidos - IC3 Internet Crime Complaint Center
Reino Unido - Polícia de Fraude de Ação
França - Ministro do interior
Itália - Polícia Estadual
Espanha - Policia Nacional
Países Baixos - Aplicação da lei
Polônia - Polícia
Portugal - Polícia Judiciária
Grécia - Unidade de crime cibernético (Polícia Helênica)
Índia - Polícia de Mumbai - Célula de investigação do CyberCrime
Austrália - Centro de crime de alta tecnologia australiano
Os relatórios podem ser respondidos em prazos diferentes, dependendo das autoridades locais.
Você pode impedir que o ransomware criptografe seus arquivos?
sim, você pode prevenir o ransomware. A melhor maneira de fazer isso é garantir que o sistema do seu computador esteja atualizado com os patches de segurança mais recentes, use um programa anti-malware confiável e firewall, faça backup de seus arquivos importantes com frequência, e evite clicar em links maliciosos ou baixando arquivos desconhecidos.
Can GANDCRAB 5.0.1 Ransomware Steal Your Data?
sim, na maioria dos casos ransomware roubará suas informações. It is a form of malware that steals data from a user's computer, criptografa isso, e depois exige um resgate para descriptografá-lo.
Em muitos casos, a autores de malware ou invasores ameaçarão excluir os dados ou publicá-lo on-line a menos que o resgate seja pago.
O ransomware pode infectar WiFi?
sim, ransomware pode infectar redes WiFi, como agentes mal-intencionados podem usá-lo para obter o controle da rede, roubar dados confidenciais, e bloquear usuários. Se um ataque de ransomware for bem-sucedido, pode levar a uma perda de serviço e/ou dados, e em alguns casos, perdas financeiras.
Devo Pagar Ransomware?
Não, você não deve pagar extorsionários de ransomware. Pagá-los apenas incentiva os criminosos e não garante que os arquivos ou dados sejam restaurados. A melhor abordagem é ter um backup seguro de dados importantes e estar atento à segurança em primeiro lugar.
What Happens If I Don't Pay Ransom?
If you don't pay the ransom, os hackers ainda podem ter acesso ao seu computador, dados, ou arquivos e pode continuar ameaçando expô-los ou excluí-los, ou mesmo usá-los para cometer crimes cibernéticos. Em alguns casos, eles podem até continuar a exigir pagamentos de resgate adicionais.
Um ataque de ransomware pode ser detectado?
sim, ransomware pode ser detectado. Software antimalware e outras ferramentas de segurança avançadas pode detectar ransomware e alertar o usuário quando está presente em uma máquina.
É importante manter-se atualizado sobre as medidas de segurança mais recentes e manter o software de segurança atualizado para garantir que o ransomware possa ser detectado e evitado.
Os criminosos de ransomware são pegos?
sim, criminosos de ransomware são pegos. Agências de aplicação da lei, como o FBI, A Interpol e outras empresas tiveram sucesso em rastrear e processar criminosos de ransomware nos EUA e em outros países. Como as ameaças de ransomware continuam a aumentar, o mesmo acontece com a atividade de fiscalização.
About the GANDCRAB 5.0.1 Pesquisa
O conteúdo que publicamos em SensorsTechForum.com, this GANDCRAB 5.0.1 guia de como fazer a remoção incluído, é o resultado de uma extensa pesquisa, trabalho árduo e a dedicação de nossa equipe para ajudá-lo a remover o malware específico e restaurar seus arquivos criptografados.
Como conduzimos a pesquisa sobre este ransomware?
Nossa pesquisa é baseada em uma investigação independente. Estamos em contato com pesquisadores de segurança independentes, e como tal, recebemos atualizações diárias sobre as definições de malware e ransomware mais recentes.
além disso, the research behind the GANDCRAB 5.0.1 ameaça de ransomware é apoiada com VirusTotal e a projeto NoMoreRansom.
Para entender melhor a ameaça do ransomware, por favor, consulte os seguintes artigos que fornecem detalhes conhecedores.
Como um site dedicado a fornecer instruções gratuitas de remoção de ransomware e malware desde 2014, A recomendação do SensorsTechForum é preste atenção apenas a fontes confiáveis.
Como reconhecer fontes confiáveis:
- Sempre verifique "Sobre nós" página da web.
- Perfil do criador do conteúdo.
- Certifique-se de que pessoas reais estejam por trás do site e não nomes e perfis falsos.
- Verifique o Facebook, Perfis pessoais no LinkedIn e no Twitter.


