Uma nova mineiro Android chamado “HiddenMiner” foi descoberto por pesquisadores de segurança. É um malware perigoso, que tem o potencial de causar falha do dispositivo iminente.
Descoberta do Android Miner HiddenMiner
Uma equipe de especialistas em segurança descobriu um malware perigoso baseado em Android chamado HiddenMiner. De acordo com seu nome, é um perigoso minerador de criptomoedas que aproveita os recursos do sistema disponíveis para realizar cálculos complexos e gerar renda para os operadores criminosos. O que é distinto para ele é o fato de conter algoritmos de infecção avançada que pode contornar algumas das medidas de segurança que a plataforma Android oferece.
É entregue principalmente por meio de cargas úteis. Os hackers usam a conhecida estratégia de criar aplicativos de malware que são espalhados no repositório do Google Play. Os hackers tendem a criar aplicativos com credenciais de desenvolvedor falsas e análises de usuários que aparecem como aplicativos úteis. Normalmente, esse software também é enviado para vários sites de hackers, Redes P2P (como o BitTorrent) e repositórios de terceiros. No momento, alguns dos principais alvos são Índia e China.
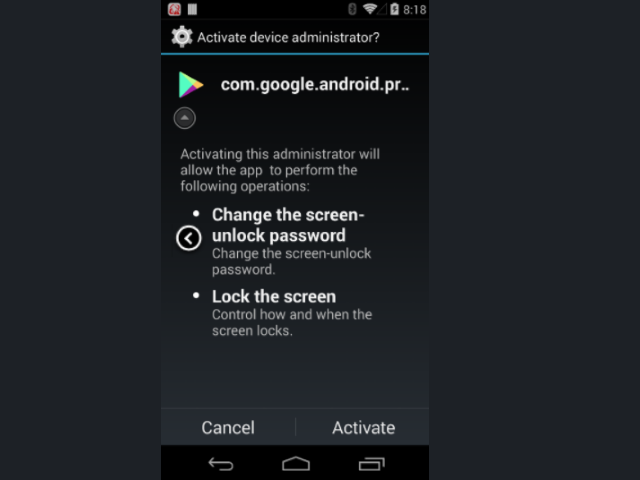
As amostras de malware adquiridas foram consideradas como o aplicativo de atualização legítimo do Google Play com o nome com.google.android.provider junto com o ícone relevante. Uma vez que o aplicativo é instalado no dispositivo Android da vítima, ele pedirá persistentemente aos usuários para ativá-lo como um “administrador do dispositivo” o que lhe concede muitas permissões. A notificação pede as seguintes permissões:
- Alterar a senha de desbloqueio da tela - Alterar a senha de desbloqueio de tela.
- Bloquear a tela - Controle como e quando a tela bloqueia.
Detalhes técnicos do HiddenMiner Android Miner
Uma vez que o malware tenha sido instalado nos dispositivos da vítima, ele inicia o minerador Monero integrado. O HiddenMiner usa a energia da CPU e os recursos de memória disponíveis para constantemente “meu” o criptomoeda Monero. É uma das alternativas mais populares ao Bitcoin e seus mineradores podem ser obtidos em várias formas - software, aplicativos móveis e scripts da web. O fato de o minerador estar profundamente integrado ao aplicativo e não fornecer controle da instância perigosa. Como resultado, os dispositivos podem superaquecer e fazer com que eles falhem.
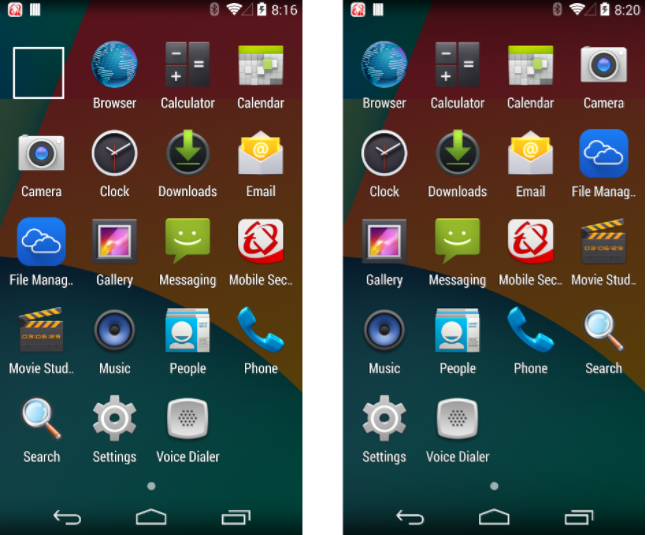
O que é mais interessante é o fato de que o malware HiddenMiner usa várias técnicas para se esconder do sistema Android e do software de segurança relevante. Uma das maneiras é esvaziar o rótulo do aplicativo e usar um ícone transparente após a instalação. Assim que o dispositivo tiver recebido as permissões relevantes, ele ocultará o aplicativo do inicializador, modificando as configurações de exibição do inicializador Android.
além do que, além do mais, tem embutido proteção discrição recursos que podem ignorar qualquer software de segurança instalado. O mecanismo de vírus procura assinaturas pertencentes a programas antivírus, emuladores, Máquina Virtual hosts ou ambientes sandbox. Depois de se infiltrar no sistema, não pode mais ser desinstalado, pois os hackers usaram uma técnica que bloqueia a tela do dispositivo se os usuários quiserem desativar seus privilégios. Este é um exploit encontrado no Android 7.0 (nogado) e versões posteriores.