malwares idade não desaparece, como é evidente pelas recentes revivals de casos antigos. Ontem nós escrevemos sobre a distribuição renovada do bem conhecido Backdoor.Nital e Gh0st RAT. Este artigo é dedicado a outro velho pedaço de malware do tipo verme - QakBot - que existe desde 2009. Pesquisadores ligados recentes bloqueios do Microsoft Active Directory para QakBot.
Active Directory, servidor de diretório da Microsoft, é projetado para permitir que os administradores de redes de controle de um único local. Não é difícil imaginar o estresse bloqueios do Active Directory pode trazer sobre admins.

Resumo ameaça
| Nome | Qakbot |
| Tipo | worm de computador, Banking Trojan, informações Stealer |
| Pequena descrição | Um worm espalha através de compartilhamentos de rede e unidades de mídia removível. O worm pode baixar mais malware, roubar informação sensível, ou abra um backdoor no sistema comprometido. É também um Trojan bancário. |
| Os sintomas | Em sua última operação, as vítimas são bloqueadas nas contas do Active Directory. |
| distribuição Método | Unidades de mídia removível, redes |
| Ferramenta de detecção |
Veja se o seu sistema foi afetado por malware
Baixar
Remoção de Malware Ferramenta
|
Experiência de usuário | Participe do nosso Fórum discutir o QakBot. |

Visão geral técnica do QakBot
pouco colocá, QakBot é um worm que se espalha através de compartilhamentos de rede e unidades de mídia removíveis. O worm pode baixar mais malware, roubar informação sensível, ou abra um backdoor no sistema comprometido. Alguns anos atrás, os pesquisadores descobriram que o QakBot tem até recursos de rootkit que ocultam sua presença no sistema e o tornam mais furtivo.
Quanto aos danos mais recentes associados ao QakBot - os bloqueios do Active Directory - ocorreram na semana passada e são a primeira vez para o malware.
De acordo com pesquisadores no X-Force da IBM, os usuários afetados não conseguiram acessar os endpoints, servidores da empresa e ativos de rede em domínios afetados.
Distribuição QakBot
Há apenas alguns dias, apareceu uma postagem no Reddit indicando sobre o estado renovado do malware. De acordo com o usuário do Reddit que iniciou a discussão, um distrito escolar foi "totalmente afetado" por sua última variante.
o 2017 variante tem se espalhado com a ajuda de um conta-gotas que espera cerca de 15 minutos para executar. Isso é feito para diminuir a chance de detecção de sandboxes ou mecanismos antivírus. O conta-gotas então abre um executável, injeta um arquivo DLL, substituindo o arquivo original. Finalmente, o dropper baixa o QakBot.
Como já mencionado, o malware sempre teve recursos semelhantes aos de worms, representados por sua capacidade de se auto-replicar por meio de unidades compartilhadas e mídia removível. Em suas últimas campanhas, o malware está usando redes para se propagar, bloqueio de usuários de suas contas. A propagação é baseada no ciclo de credenciais de usuário e domínio, pesquisadores dizem.
Para fazê-lo, o malware combina logins com várias técnicas de adivinhação de senha, como adivinhar senhas usando palavras em um dicionário. “Sob certas configurações de domínio, o ataque de dicionário do malware para acessar as máquinas alvo pode resultar em várias tentativas de autenticação com falha, que eventualmente desencadeia um bloqueio de conta,”Os pesquisadores explicaram em uma postagem do blog.
QakBot - um worm e um cavalo de Troia bancário
QakBot também é conhecido por atingir empresas. O que o torna um verdadeiro pesadelo é que é parte de um verme, Trojan bancário:
QakBot é modular, malware multithread cujos vários componentes implementam roubo de credencial de banco online, um recurso de backdoor, Proxy SOCKS, extensas capacidades anti-pesquisa e a habilidade de subverter antivírus (DE) Ferramentas. Além de suas técnicas de evasão, dado privilégios de administrador, A variante atual do QakBot pode desabilitar o software de segurança em execução no endpoint.
Além de tudo o mais, QakBot continua a ser capaz de escapar da detecção e é muito persistente. As reinicializações do sistema não funcionam bem como as tentativas de remoção com a chave de execução do Registro e tarefas agendadas. O malware ainda carregará após cada reinicialização do sistema. Quanto à tarefa agendada em schtasks.exe - fará com que o malware seja executado em intervalos programados.
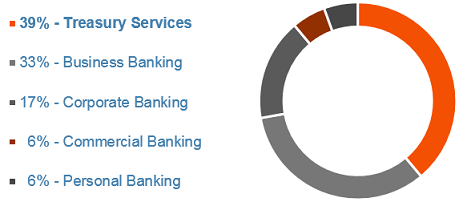
Resumindo, QakBot é um worm, um Trojan bancário e um ladrão de informações. Curiosamente, é “também o primeiro Trojan que foi projetado para atingir exclusivamente o setor de banco comercial, uma vocação que se manteve fiel ao longo dos últimos oito anos ”. Estes são os setores afetados pelo malware perigoso:

Mitigação e proteção QakBot
Como o QakBot visa principalmente bancos e empresas, vítimas em potencial devem usar soluções de detecção de malware adaptáveis com recursos em tempo real. A primeira coisa, Contudo, é consciência de cibersegurança, pesquisadores dizem. “Os usuários podem se proteger e proteger suas organizações praticando a higiene da navegação, desativando anúncios online, filtrar a execução de macros em arquivos que vêm por e-mail e observar outras práticas recomendadas de segurança”.
Para mitigar a atividade QakBot na rede, os usuários devem assegurar que as contas de domínio sejam configuradas com o mínimo de privilégios necessários para realizar tarefas de trabalho
As organizações são aconselhadas a criar uma conta de administrador de domínio aleatória para fins de segurança e, em seguida, certifique-se de que ela se reporta diretamente ao sistema de gerenciamento de informações e eventos de segurança (SIEM) quando há uma tentativa de usá-lo.
E finalmente, as organizações devem evitar comunicações de estação de trabalho para estação de trabalho sempre que possível "possível forçar o malware fora das trincheiras e em áreas onde os sistemas de detecção central irão detectá-lo rapidamente”, pesquisadores concluem.
digitalizador Spy Hunter só irá detectar a ameaça. Se você quiser a ameaça de ser removido automaticamente, você precisa comprar a versão completa da ferramenta anti-malware.Saiba Mais Sobre SpyHunter Anti-Malware Ferramenta / Como desinstalar o SpyHunter