 variante di ransomware, noto con il nome REKTLocker è stato segnalato per usare l'estensione del file .rekt e l'algoritmo di crittografia RSA-2048 a cifrare i dati degli utenti. Il virus cambia quindi la carta da parati con le richieste di riscatto, volendo la somma di 1 BTC come un payoff di riscatto. Gli utenti che sono diventati vittime sfortunate di questo malware sono vivamente consigliati dagli esperti di NON pagare alcun riscatto e di combattere questo malware isolandolo e rimuovendolo e cercando di ripristinare i file stessi. Ti consigliamo di leggere attentamente questo articolo per ulteriori informazioni sul ransomware REKTLocker e su come ripristinare i tuoi file e rimuoverlo dal tuo sistema.
variante di ransomware, noto con il nome REKTLocker è stato segnalato per usare l'estensione del file .rekt e l'algoritmo di crittografia RSA-2048 a cifrare i dati degli utenti. Il virus cambia quindi la carta da parati con le richieste di riscatto, volendo la somma di 1 BTC come un payoff di riscatto. Gli utenti che sono diventati vittime sfortunate di questo malware sono vivamente consigliati dagli esperti di NON pagare alcun riscatto e di combattere questo malware isolandolo e rimuovendolo e cercando di ripristinare i file stessi. Ti consigliamo di leggere attentamente questo articolo per ulteriori informazioni sul ransomware REKTLocker e su come ripristinare i tuoi file e rimuoverlo dal tuo sistema.

Sommario minaccia
| Nome |
REKTLocker |
| Tipo | ransomware Virus |
| breve descrizione | REKTLocker crittografa i file dei sistemi che infetta, chiede 1 BTC come un payoff di riscatto. |
| Sintomi | I file sono crittografati e non sono più accessibili con un'estensione file .rekt aggiunta e un file Readme.txt eliminato. |
| Metodo di distribuzione | Via URL dannosi, allegati di posta elettronica dannosi o altre forme di spam in linea. |
| Detection Tool |
Verifica se il tuo sistema è stato interessato da malware
Scarica
Strumento di rimozione malware
|
| Esperienza utente | Iscriviti alla nostra forum per Discuti REKTLocker Ransomware. |
| Strumento di recupero dati | Windows Data Recovery da Stellar Phoenix Avviso! Questo prodotto esegue la scansione settori di unità per recuperare i file persi e non può recuperare 100% dei file crittografati, ma solo pochi di essi, a seconda della situazione e se non è stato riformattato l'unità. |

REKTLocker - Metodi di distribuzione
Simile a altri ransomware, diffondere e infettare le vittime mentre sono ignare, REKTLocker può utilizzare una serie di strumenti che potrebbero aiutarlo a raggiungere i suoi obiettivi:
- obfuscators malware.
- file JavaScript.
- Exploit Kit.
- bots spam o servizi di spamming.
- Inserzionisti di terze parti e servizi PUP supportati da pubblicità.
Questi strumenti possono essere utilizzati per far scorrere il malware sotto forma di collegamenti Web dannosi o allegati dannosi. I collegamenti Web possono sembrare legittimi quando vengono scansionati alla ricerca di malware, ma possono causare reindirizzamenti del browser agli URL di infezione effettivi che potrebbero iniettare uno script dannoso e rilasciare il payload in modo drive-by.
allegati dannosi, tuttavia, può contenere un kit di exploit o essere in un .js, .exe, .dll o .tmp che possono causare l'infezione. Questi vengono inviati principalmente come allegati di posta elettronica che di solito assomigliano a documenti di Adobe Reader o Microsoft Office.

REKTLocker - Ulteriori informazioni
Non appena REKTLocker è stato avviato sul computer dell'utente, potrebbe rilasciare i suoi file dannosi nelle seguenti cartelle:
- %AppData%
- %Temp%
- %Roaming%
- %Del posto%
- %SystemDrive%
- %Profilo di utente%
- %Finestre%
I file rilasciati da REKTLocker possono essere più di uno, e possono avere formati di file diversi a seconda di ciò per cui sono stati creati. Per esempio, se il ransomware rilascia un .BAT (file batch) è molto probabile che venga eliminato per eliminare i backup e le copie shadow del volume del computer, utilizzando il seguente comando amministrativo:
→ vssadmin eliminare ombre / all / quiet
Non appena ha rilasciato i file, il ransomware REKTLocker può creare valori di registro dannosi nelle seguenti chiavi di registro di Windows per il suo eseguibile che crittografa i file da eseguire all'avvio di Windows:
→ HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion Run
HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion Run
HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion RunOnce
HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion RunOnce
Dopo questo è stato fatto, REKTLocker potrebbe avviare il processo di crittografia. Il virus può utilizzare un algoritmo di crittografia RSA-2048 che genererà una chiave di decrittografia e la invierà ai criminali informatici 'C&C (Comando e Controllo) server dopo aver crittografato i file del seguente tipo:
- I file audio.
- Immagini e altri file di immagine.
- I file video.
- Banche dati.
- file di Photoshop.
- documenti di Microsoft Office.
- File web.
- Altri file associati a software ampiamente utilizzato.
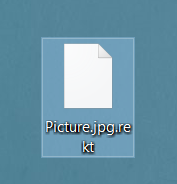
Dopo la cifratura è stata completata, REKTLocker ransomware modifica la struttura dei file rendendoli inaccessibili e assomigliando al seguente esempio:
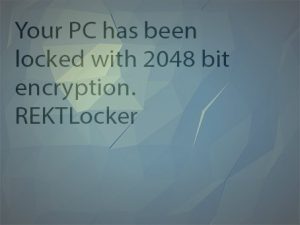
Dopo la crittografia, il ransomware REKTLocker aggiunge un file Readme.txt insieme a una foto che cambia come sfondo. Ecco cosa affermano entrambi:
"Il tuo PC è stato bloccato con 2048 bit encryption.
REKTLocker "
File Readme.txt:
"Il tuo computer è stato crittografato.
Inviare 1 BTC a 1NuLLtgCmigRb5mXeFgsGDFnVLypLC4a8Y oi tuoi file verranno crittografati in modo permanente.
Decryptor:
Le chiavi di altre persone non funzioneranno sul tuo computer.
Non pensare che il tuo antivirus ti salverà; non lo farà. "

REKTLocker Ransomware - Conclusione, Rimozione, e ripristino dei file
Come una linea di fondo, È molto probabile che REKTLocker sia stato acquistato come servizio (RAAS) online da un forum web profondo e dalle persone che lo stanno dietro, hanno inserito dell'umorismo storto, includendo l'estensione del file .rekt in esso, con un riferimento al cosiddetto “possesso” di videogiochi. Consigliamo di non rispettare le richieste di questi criminali informatici e di concentrarsi sull'affrontare la minaccia da soli. Per farlo, dovresti prima rimuovere REKTLocker ransomware e dopo questo, concentrati sul recupero dei tuoi file seguendo le istruzioni seguenti.
Per rimuovere REKTLocker, abbiamo progettato passaggi metodologicamente organizzati che ti aiuteranno a individuare e rimuovere manualmente i file purché tu abbia la conoscenza esatta di dove si trovano tutti i file. Per la massima efficacia, vi invitiamo a utilizzare un programma anti-malware avanzato, perché non solo rileverà e rimuoverà automaticamente REKTLocker e altri rischi per il tuo PC, ma lo proteggerà anche in futuro.
Nel caso tu sia interessato a ripristinare i tuoi file, assicurati di eseguire prima il backup dei dati crittografati e NON reinstallare Windows. Questo aiuterà i programmi come il software di recupero dati che suggeriamo di utilizzare nel passaggio “3. Ripristina i file crittografati da REKTLocker "per agire in modo più efficace e ripristinare almeno una piccola parte dei tuoi file. Mentre tenti di ripristinare i tuoi file, consigliamo vivamente di seguire questo articolo e i nostri aggiornamenti, poiché pubblicheremo immediatamente un aggiornamento non appena gli esperti di ricerca sul malware hanno rilasciato un decryptor gratuito per REKTLocker ransomware.
- Passo 1
- Passo 2
- Passo 3
- Passo 4
- Passo 5
Passo 1: Scansiona REKTLocker con lo strumento SpyHunter Anti-Malware



Rimozione automatica ransomware - Videoguida
Passo 2: Uninstall REKTLocker and related malware from Windows
Ecco un metodo in pochi semplici passi che dovrebbero essere in grado di disinstallare maggior parte dei programmi. Non importa se si utilizza Windows 10, 8, 7, Vista o XP, quei passi otterrà il lavoro fatto. Trascinando il programma o la relativa cartella nel cestino può essere un molto cattiva decisione. Se lo fai, frammenti di programma vengono lasciati, e che possono portare al lavoro instabile del PC, errori con le associazioni di tipo file e altre attività spiacevoli. Il modo corretto per ottenere un programma dal computer è di disinstallarlo. Per fare questo:


 Segui le istruzioni sopra e cancellerai con successo la maggior parte dei programmi indesiderati e dannosi.
Segui le istruzioni sopra e cancellerai con successo la maggior parte dei programmi indesiderati e dannosi.
Passo 3: Pulire eventuali registri, creato da REKTLocker sul tuo computer.
I registri di solito mirati di macchine Windows sono i seguenti:
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion Run
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion Run
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion RunOnce
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion RunOnce
È possibile accedere aprendo l'editor del registro di Windows e l'eliminazione di tutti i valori, creato da REKTLocker lì. Questo può accadere seguendo la procedura sotto:


 Mancia: Per trovare un valore virus creato, è possibile fare clic destro su di esso e fare clic su "Modificare" per vedere quale file è impostato per funzionare. Se questa è la posizione file del virus, rimuovere il valore.
Mancia: Per trovare un valore virus creato, è possibile fare clic destro su di esso e fare clic su "Modificare" per vedere quale file è impostato per funzionare. Se questa è la posizione file del virus, rimuovere il valore.
Prima di cominciare "Passo 4", Per favore l'avvio in modalità normale, nel caso in cui siete attualmente in modalità provvisoria.
Questo vi permetterà di installare e uso SpyHunter 5 con successo.
Passo 4: Avvia il tuo PC in modalità provvisoria per isolare e rimuovere REKTLocker





Passo 5: Try to Restore Files Encrypted by REKTLocker.
Metodo 1: Utilizza STOP Decrypter di Emsisoft.
Non tutte le varianti di questo ransomware possono essere decifrati gratis, ma abbiamo aggiunto il decryptor utilizzato dai ricercatori che viene spesso aggiornato con le varianti che diventano poi decifrati. Si può cercare di decifrare i file utilizzando le istruzioni riportate di seguito, ma se non funzionano, poi purtroppo la vostra variante del virus ransomware non è decifrabile.
Seguire le istruzioni riportate di seguito per utilizzare il decrypter Emsisoft e decrittografare i file gratuitamente. Puoi scaricare lo strumento di decrittazione Emsisoft legata qui e quindi seguire i passaggi indicati di seguito:
1 Pulsante destro del mouse sulla Decrypter e cliccare su Esegui come amministratore come mostrato di seguito:

2. D'accordo con i termini della licenza:

3. Clicca su "Aggiungi cartella" e poi aggiungere le cartelle in cui si desidera i file decriptati come mostrato sotto:

4. Clicca su "decrypt" e attendere che i file da decodificare.

Nota: Credito per il decryptor va a Emsisoft ricercatori che hanno fatto il passo avanti con questo virus.
Metodo 2: Utilizzare un software di recupero dati
Ransomware infections and REKTLocker aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. Questo è il motivo per cui abbiamo suggerito un metodo di recupero di dati che possono aiutare a andare in giro decrittazione diretta e cercare di ripristinare i file. Tenete a mente che questo metodo non può essere 100% efficace, ma può anche aiutare un po 'o molto in situazioni diverse.
Basta cliccare sul link e sui menu del sito in alto, scegliere Recupero dati - Procedura guidata di recupero dati per Windows o Mac (a seconda del tuo sistema operativo), e quindi scaricare ed eseguire lo strumento.
REKTLocker-FAQ
What is REKTLocker Ransomware?
REKTLocker is a ransomware infezione - il software dannoso che entra silenziosamente nel tuo computer e blocca l'accesso al computer stesso o crittografa i tuoi file.
Molti virus ransomware utilizzano sofisticati algoritmi di crittografia per rendere inaccessibili i tuoi file. L'obiettivo delle infezioni da ransomware è richiedere il pagamento di un riscatto per ottenere l'accesso ai file.
What Does REKTLocker Ransomware Do?
Il ransomware in generale è un software dannoso quello è progettato per bloccare l'accesso al tuo computer o ai tuoi file fino al pagamento del riscatto.
Anche i virus ransomware possono danneggiare il tuo sistema, corrompere i dati ed eliminare i file, con conseguente perdita permanente di file importanti.
How Does REKTLocker Infect?
Via several ways.REKTLocker Ransomware infects computers by being sent tramite e-mail di phishing, contenente allegato virus. Questo allegato è di solito mascherato come documento importante, come una fattura, documento bancario o anche un biglietto aereo e sembra molto convincente per gli utenti.
Another way you may become a victim of REKTLocker is if you scaricare un programma di installazione falso, crack o patch da un sito Web con bassa reputazione o se si fa clic sul collegamento di un virus. Molti utenti segnalano di avere un'infezione da ransomware scaricando torrent.
How to Open .REKTLocker files?
tu can't senza decrittatore. A questo punto, il .REKTLocker file sono criptato. Puoi aprirli solo dopo che sono stati decrittografati utilizzando una chiave di decrittografia specifica per il particolare algoritmo.
Cosa fare se un decryptor non funziona?
Niente panico, e eseguire il backup dei file. Se un decryptor non ha decifrato il tuo .REKTLocker file correttamente, quindi non disperare, perché questo virus è ancora nuovo.
Posso ripristinare ".REKTLocker" File?
Sì, a volte i file possono essere ripristinati. Ne abbiamo suggeriti diversi metodi di recupero file che potrebbe funzionare se si desidera ripristinare .REKTLocker file.
Questi metodi non sono in alcun modo 100% garantito che sarai in grado di recuperare i tuoi file. Ma se hai un backup, le tue possibilità di successo sono molto maggiori.
How To Get Rid of REKTLocker Virus?
Il modo più sicuro e più efficace per la rimozione di questa infezione da ransomware è l'uso a programma anti-malware professionale.
It will scan for and locate REKTLocker ransomware and then remove it without causing any additional harm to your important .REKTLocker files.
Posso segnalare il ransomware alle autorità?
Nel caso in cui il tuo computer sia stato infettato da un'infezione da ransomware, puoi segnalarlo ai dipartimenti di Polizia locale. Può aiutare le autorità di tutto il mondo a rintracciare e determinare gli autori del virus che ha infettato il tuo computer.
Sotto, abbiamo preparato un elenco con i siti web del governo, dove puoi presentare una segnalazione nel caso in cui sei vittima di un file criminalità informatica:
Autorità di sicurezza informatica, responsabile della gestione dei rapporti sugli attacchi ransomware in diverse regioni del mondo:
Germania - Portale ufficiale della polizia tedesca
stati Uniti - IC3 Internet Crime Complaint Center
Regno Unito - Polizia antifrode
Francia - Ministro degli Interni
Italia - Polizia Di Stato
Spagna - Polizia nazionale
Paesi Bassi - Forze dell'ordine
Polonia - Polizia
Portogallo - Polizia giudiziaria
Grecia - Unità per la criminalità informatica (Polizia ellenica)
India - Polizia di Mumbai - CyberCrime Investigation Cell
Australia - Australian High Tech Crime Center
È possibile rispondere ai rapporti in tempi diversi, a seconda delle autorità locali.
Puoi impedire al ransomware di crittografare i tuoi file?
Sì, puoi prevenire il ransomware. Il modo migliore per farlo è assicurarsi che il sistema del computer sia aggiornato con le ultime patch di sicurezza, utilizzare un programma anti-malware affidabile e firewall, eseguire frequentemente il backup dei file importanti, ed evitare di fare clic su link malevoli o il download di file sconosciuti.
Can REKTLocker Ransomware Steal Your Data?
Sì, nella maggior parte dei casi ransomware ruberà le tue informazioni. It is a form of malware that steals data from a user's computer, lo crittografa, e poi chiede un riscatto per decifrarlo.
In molti casi, il autori di malware o gli aggressori minacciano di eliminare i dati o pubblicalo online a meno che non venga pagato il riscatto.
Il ransomware può infettare il WiFi?
Sì, il ransomware può infettare le reti WiFi, poiché gli attori malintenzionati possono usarlo per ottenere il controllo della rete, rubare dati riservati, e bloccare gli utenti. Se un attacco ransomware ha successo, potrebbe portare alla perdita del servizio e/o dei dati, e in alcuni casi, perdite finanziarie.
Dovrei pagare ransomware?
No, non dovresti pagare gli estorsori di ransomware. Il loro pagamento incoraggia solo i criminali e non garantisce che i file oi dati verranno ripristinati. L'approccio migliore consiste nell'avere un backup sicuro dei dati importanti ed essere vigili sulla sicurezza in primo luogo.
What Happens If I Don't Pay Ransom?
If you don't pay the ransom, gli hacker potrebbero ancora avere accesso al tuo computer, dati, o file e potrebbe continuare a minacciare di esporli o eliminarli, o addirittura usarli per commettere crimini informatici. In alcuni casi, potrebbero persino continuare a richiedere pagamenti di riscatto aggiuntivi.
È possibile rilevare un attacco ransomware?
Sì, ransomware può essere rilevato. Software anti-malware e altri strumenti di sicurezza avanzati può rilevare il ransomware e avvisare l'utente quando è presente su una macchina.
È importante rimanere aggiornati sulle ultime misure di sicurezza e mantenere aggiornato il software di sicurezza per garantire che il ransomware possa essere rilevato e prevenuto.
I criminali ransomware vengono catturati?
Sì, i criminali ransomware vengono catturati. Le forze dell'ordine, come l'FBI, L'Interpol e altri sono riusciti a rintracciare e perseguire i criminali di ransomware negli Stati Uniti e in altri paesi. Mentre le minacce ransomware continuano ad aumentare, così fa l'attività di esecuzione.
About the REKTLocker Research
I contenuti che pubblichiamo su SensorsTechForum.com, this REKTLocker how-to removal guide included, è il risultato di ricerche approfondite, duro lavoro e la dedizione del nostro team per aiutarti a rimuovere il malware specifico e ripristinare i tuoi file crittografati.
Come abbiamo condotto la ricerca su questo ransomware??
La nostra ricerca si basa su un'indagine indipendente. Siamo in contatto con ricercatori di sicurezza indipendenti, e come tale, riceviamo aggiornamenti quotidiani sulle ultime definizioni di malware e ransomware.
Inoltre, the research behind the REKTLocker ransomware threat is backed with VirusTotal e la progetto NoMoreRansom.
Per comprendere meglio la minaccia ransomware, si prega di fare riferimento ai seguenti articoli che forniscono dettagli informati.
Come sito dedicato da allora a fornire istruzioni di rimozione gratuite per ransomware e malware 2014, La raccomandazione di SensorsTechForum è di prestare attenzione solo a fonti affidabili.
Come riconoscere fonti affidabili:
- Controlla sempre "Riguardo a noi" pagina web.
- Profilo del creatore di contenuti.
- Assicurati che dietro al sito ci siano persone reali e non nomi e profili falsi.
- Verifica Facebook, Profili personali di LinkedIn e Twitter.