Cosa è PC Zen? Cosa fa PC Zen fare? È PC Zen al sicuro? Puoi fidarti PC Zen? Zen PC è un virus?
Lo Zen PC Malware è un'arma pericolosa utilizzato contro gli utenti di computer in tutto il mondo. Infetta principalmente attraverso messaggi di posta elettronica di phishing. Il nostro articolo fornisce una panoramica del suo comportamento in base ai campioni raccolti e rapporti disponibili, Inoltre può essere utile nel tentativo di rimuovere il virus.

Sommario minaccia
| Nome | PC Zen |
| Tipo | Trojan |
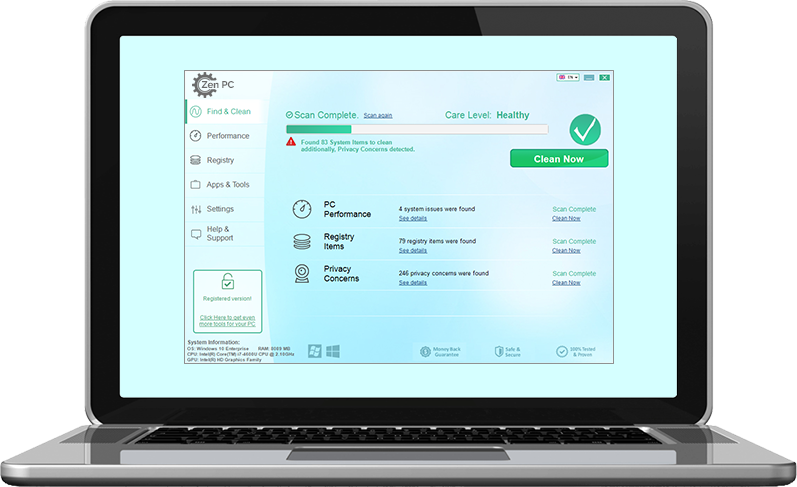
| breve descrizione | Lo Zen PC Malware è un programma di truffa che è stato progettato per infiltrarsi sistemi informatici. |
| Sintomi | Le vittime non possono verificarsi alcun sintomo apparente di infezione. |
| Metodo di distribuzione | messaggi di phishing, Installazioni freeware, pacchetti in bundle, Gli script e gli altri. |
| Detection Tool |
Verifica se il tuo sistema è stato interessato da malware
Scarica
Strumento di rimozione malware
|
| Esperienza utente | Iscriviti alla nostra Forum per discutere Zen PC. |

Zen PC Malware - metodi di distribuzione
Lo Zen PC è un'utility software truffa che viene distribuito contro gli utenti di computer a livello globale da un collettivo di hacking sconosciuta. Minacce come questo sono particolarmente popolari come si presenteranno come un software di sistema utile. Questo non significa che ogni applicazione chiamata Zen PC è dannoso per natura. E 'molto difficile determinare che è un vero e utile applicazione e che è il malware uno frodi.
Una delle principali strategie utilizzate per diffondere la Zen PC è di coordinare l'invio di i messaggi di posta elettronica di phishing e la creazione di i server degli hacker controllato che sono fatti al fine di manipolare le vittime. Essi saranno manipolati a credere che il contenuto proviene da un servizio ben noto o la società. Attraverso l'interazione con loro l'installazione virus inizierà. Di solito i siti dannosi ed e-mail provengono da siti che sono ospitati su nomi di dominio che suonano molto simili alle pagine iniziali legittimi dei servizi citati. Essi possono anche includere i certificati di protezione autofirmati o rubati.
I criminali possono guidare le infezioni inserendo codice malware varie portatori di file. I due tipi più popolari sono i seguenti:
- pacchetti di installazione - The Zen PC può essere inserito in un programma di installazione dell'applicazione senza che gli utenti lo sappia. I criminali in genere scelgono popolare software che viene spesso installato: utilità di sistema, strumenti di produttività e suite creatività. Non appena questi programmi di installazione vengono eseguiti i beneficiari non possono sapere che sono da installare malware al fianco di un'altra applicazione.
- Documenti Macro-Infected - Essi comprendono macro che porteranno alla infezione Zen PC. I documenti possono essere di tutti i formati più diffusi: presentazioni, file di testo, database e fogli di calcolo. Non appena vengono aperte dalle vittime verrà visualizzato un messaggio chiedendo loro di attivare il codice incorporato. Se questo è fatto verrà installato il virus. Spesso motivi diversi sono espressi in modo da invogliare gli utenti a fare in modo, il più popolare è il requisito per poter visualizzare correttamente i contenuti del file.
Tutti questi file possono essere caricati su diversi reti di condivisione file come BitTorrent dove si trova spesso pirata e dati legittimi. campagne di infezione più grandi possono essere effettuate inserendo il codice necessario a plugin Web dannosi - possono essere caricati repository rilevanti con finte recensioni degli utenti e una descrizione elaborata. Per passare attraverso lo sviluppatore controllare i criminali in grado di rubare le credenziali di autori di plugin o falso.

Zen PC Malware - Descrizione dettagliata
A seconda delle condizioni locali e le istruzioni di hacker l'applicazione può funzionare in un modo completamente diverso da altre minacce simili. Nella maggior parte dei casi queste minacce malware assumeranno la forma di un programma di utilità di sistema utile. Ciò significa che, a seconda dei casi i criminali possono rendere il look come strumento come completamente funzionante. Tuttavia, non appena viene eseguito si può lanciare una varietà di moduli maligni pericolosi tra cui le seguenti:
- furto di informazioni - Una delle strategie più utilizzate è quello di cercare informazioni che possono esporre le vittime, cercando per archi nella memoria ed i contenuti del disco rigido in grado di rivelare i dati come il nome di una persona, indirizzo, numero di telefono e ecc. Questo può essere usato ulteriormente per scopi dannosi e crimini come il furto di identità. Questo particolare modulo può anche essere usato per generare un profilo completo del computer infetto. Queste informazioni possono essere utilizzate per generare un ID univoco per ogni host compromessi.
- Applicazioni di sicurezza di rimozione - L'intelligenza guadagnato sui computer può essere utilizzato per identificare se ci sono le applicazioni di sicurezza in esecuzione che possono bloccare la corretta esecuzione della minaccia. L'elenco dei più popolari includono i seguenti: minacce anti-virus, firewall, host di macchine virtuali, ambienti sandbox ed eseguire il debug.
- Installazione Persistent - La minaccia dannoso Zen PC può essere impostato per avviare automaticamente non appena le vittime alimentano il proprio computer. Questo passaggio può anche disabilitare l'accesso alle opzioni di avvio di recupero. Questo è molto importante in quanto la maggior parte delle guide di rimozione manuale dipendono da loro per tentare il recupero di malware.
- Windows modifica del Registro di sistema - Il motore principale può essere utilizzato per commettere modifiche al registro di Windows modificando i valori già esistenti o la creazione di nuovi relativi al malware Zen PC. Le conseguenze di queste azioni possono portare a problemi quando si accede a determinate funzioni app e di sistema, la perdita di dati e le frequenti errori imprevisti.
- rimozione dei dati - Il motore del malware può essere programmato per ook per i file sensibili che devono essere rimossi. Di solito questi sono importanti dati di sistema che sono importanti per il corretto funzionamento del sistema operativo. Gli esempi includono il sistema punti di ripristino, copie di volume ombra e backup.
- Ulteriori malware Infezioni - Le infezioni fatte con le versioni maligni dell'app Zen PC possono essere utilizzati come condotti per altri virus.
Cosa c'è di pericoloso in questo particolare software è che entrambe le imita un'utility di sistema del mondo reale e può essere utilizzato in vari tipi di attacchi degli hacker. Può essere installato da altri virus o può essere utilizzato come uno strumento complesso progettato per distribuire altro malware. Una scelta popolare è quello di lanciare un modulo Trojan che collegherà le macchine infette al server degli hacker controllato prestabilito che permette ai criminali di prendere il controllo delle macchine in qualsiasi momento, rubare i loro dati ed effettuare le minacce più pericolose.

Rimuovere Zen PC Malware
Se si desidera rimuovere il Zen PC Malware software indesiderato dal computer si consiglia di utilizzare un software specifico anti-malware. Con un tale un programma anti-malware, il computer rimarrà con una protezione migliore e rimanere in buona salute prestazioni-saggio in futuro.
Preparazione prima di rimuovere Zen PC.
Prima di avviare il processo di rimozione effettiva, si consiglia di effettuare le seguenti operazioni di preparazione.
- Assicurarsi di avere le istruzioni sempre aperta e di fronte ai vostri occhi.
- Fare un backup di tutti i file, anche se potrebbero essere danneggiati. È necessario eseguire il backup dei dati con una soluzione di backup su cloud e assicurare i vostri file contro qualsiasi tipo di perdita, anche dalle più gravi minacce.
- Siate pazienti in quanto ciò potrebbe richiedere un po '.
- Cerca malware
- Correggi i registri
- Rimuovere i file dei virus
Passo 1: Scansione per Zen PC con SpyHunter Anti-Malware Strumento



Passo 2: Pulire eventuali registri, creato da Zen PC sul computer.
I registri di solito mirati di macchine Windows sono i seguenti:
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion Run
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion Run
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion RunOnce
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion RunOnce
È possibile accedere aprendo l'editor del registro di Windows e l'eliminazione di tutti i valori, creato da Zen un PC. Questo può accadere seguendo la procedura sotto:


 Mancia: Per trovare un valore virus creato, è possibile fare clic destro su di esso e fare clic su "Modificare" per vedere quale file è impostato per funzionare. Se questa è la posizione file del virus, rimuovere il valore.
Mancia: Per trovare un valore virus creato, è possibile fare clic destro su di esso e fare clic su "Modificare" per vedere quale file è impostato per funzionare. Se questa è la posizione file del virus, rimuovere il valore.Passo 3: Find virus files created by Zen PC on your PC.
1.Per Windows 8, 8.1 e 10.
Per i sistemi operativi Windows più recenti
1: Sulla vostra stampa della tastiera + R e scrivi explorer.exe nel Correre casella di testo e quindi fare clic sul Ok pulsante.

2: Clicca su PC dalla barra di accesso rapido. Questo è di solito una icona con un monitor e il suo nome è o "Il mio computer", "Il mio PC" o "Questo PC" o quello che hanno chiamato.

3: Passa alla casella di ricerca in alto a destra sullo schermo del tuo PC e digita "FileExtension:" e dopo di che digitare l'estensione del file. Se siete alla ricerca di eseguibili dannosi, Un esempio può essere "FileExtension:exe". Dopo aver fatto che, lasciare uno spazio e digitare il nome del file si ritiene che il malware si è creato. Ecco come si può essere visualizzato se è stato trovato il file:

NB. Consigliamo di attendere che la barra verde di caricamento nel box di navigazione si riempia nel caso il PC stia cercando il file e non lo abbia ancora trovato.
2.Per Windows XP, Vista, e 7.
Per i sistemi operativi Windows meno recenti
Nei vecchi sistemi operativi Windows l'approccio convenzionale dovrebbe essere quello efficace:
1: Clicca sul Menu iniziale icona (di solito sulla vostra in basso a sinistra) e quindi scegliere il Ricerca preferenza.

2: Una volta visualizzata la finestra di ricerca, scegliere Altre opzioni avanzate da l'assistente di ricerca. Un altro modo è cliccando su Tutti i file e le cartelle.

3: Dopo di che tipo il nome del file che si sta cercando e fare clic sul pulsante di ricerca. Questo potrebbe richiedere un certo tempo dopo il quale verranno visualizzati i risultati. Se avete trovato il file dannoso, è possibile copiare o aprire la sua posizione da pulsante destro del mouse su di essa.
Ora si dovrebbe essere in grado di scoprire qualsiasi file in Windows, purché sia sul disco rigido e non è nascosto via software speciale.
Domande frequenti sul PC Zen
What Does Zen PC Trojan Do?
The Zen PC Trojan è un programma informatico dannoso progettato per disturbare, danno, o ottenere un accesso non autorizzato ad un sistema informatico. Può essere utilizzato per rubare dati sensibili, ottenere il controllo di un sistema, o avviare altre attività dannose.
I trojan possono rubare le password?
Sì, Trojan, come Zen PC, può rubare le password. Questi programmi dannosi sono progettati per ottenere l'accesso al computer di un utente, spiare le vittime e rubare informazioni sensibili come dati bancari e password.
Can Zen PC Trojan Hide Itself?
Sì, può. Un Trojan può utilizzare varie tecniche per mascherarsi, compresi i rootkit, crittografia, e offuscazione, per nascondersi dagli scanner di sicurezza ed eludere il rilevamento.
È possibile rimuovere un Trojan tramite il ripristino delle impostazioni di fabbrica?
Sì, un Trojan può essere rimosso ripristinando le impostazioni di fabbrica del dispositivo. Questo perché ripristinerà il dispositivo al suo stato originale, eliminando qualsiasi software dannoso che potrebbe essere stato installato. Tieni presente che esistono trojan più sofisticati che lasciano backdoor e infettano nuovamente anche dopo un ripristino delle impostazioni di fabbrica.
Can Zen PC Trojan Infect WiFi?
Sì, è possibile che un trojan infetti le reti WiFi. Quando un utente si connette alla rete infetta, il Trojan può diffondersi ad altri dispositivi connessi e può accedere a informazioni sensibili sulla rete.
I trojan possono essere eliminati?
Sì, I trojan possono essere eliminati. Ciò viene in genere eseguito eseguendo un potente programma antivirus o antimalware progettato per rilevare e rimuovere file dannosi. In alcuni casi, potrebbe anche essere necessaria la cancellazione manuale del Trojan.
I trojan possono rubare i file?
Sì, I trojan possono rubare file se sono installati su un computer. Questo viene fatto consentendo al autore di malware o utente per ottenere l'accesso al computer e quindi rubare i file memorizzati su di esso.
Quale anti-malware può rimuovere i trojan?
Programmi anti-malware come SpyHunter sono in grado di scansionare e rimuovere i trojan dal tuo computer. È importante mantenere aggiornato il tuo anti-malware e scansionare regolarmente il tuo sistema alla ricerca di software dannoso.
I trojan possono infettare USB?
Sì, I trojan possono infettare USB dispositivi. Trojan USB in genere si diffondono tramite file dannosi scaricati da Internet o condivisi tramite e-mail, consentendo all'hacker di accedere ai dati riservati di un utente.
Informazioni sulla ricerca Zen PC
I contenuti che pubblichiamo su SensorsTechForum.com, questa guida alla rimozione di Zen PC inclusa, è il risultato di ricerche approfondite, il duro lavoro e la dedizione del nostro team per aiutarti a rimuovere il problema specifico del trojan.
Come abbiamo condotto la ricerca su Zen PC?
Si prega di notare che la nostra ricerca si basa su un'indagine indipendente. Siamo in contatto con ricercatori di sicurezza indipendenti, grazie al quale riceviamo aggiornamenti quotidiani sulle ultime definizioni di malware, compresi i vari tipi di trojan (porta sul retro, downloader, Infostealer, riscatto, eccetera)
Inoltre, the research behind the Zen PC threat is backed with VirusTotal.
Per comprendere meglio la minaccia rappresentata dai trojan, si prega di fare riferimento ai seguenti articoli che forniscono dettagli informati.