O botnet Asprox ainda está esperando seu pico durante a temporada de férias
Se você encontrar uma mensagem de confirmação de entrega em sua caixa de entrada de e-mail atualmente, tenha cuidado, pois foi enviado de uma fonte legítima. Especialmente se você não está esperando nenhuma entrega. Muitos golpistas estão usando a temporada de férias para espalhar mensagens, contendo malware e outro software malicioso.
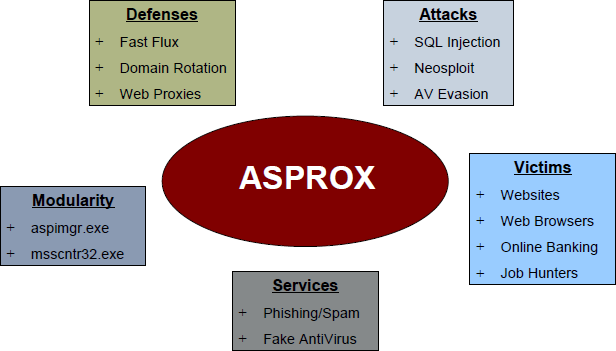
O que o botnet Asprox faz
Os e-mails sobre entregas são os mais comuns durante o período de festas, e é exatamente com isso que os criadores do Asprox Botnet contam. O que os bandidos estão usando como isca são os nomes de importantes varejistas dos EUA. Eles estão colocando-os no assunto das mensagens, para que as vítimas suspeitem menos de um possível golpe ao abri-los e clicar nos links que a mensagem contém. Os links contêm trojans que entram no seu computador e o contaminam com malware projetado para enganar a máquina, procure e roube credenciais, contas bancárias e outras informações pessoais dos usuários. A campanha em andamento no momento usa nomes de grandes marcas como Home Depot, CostCo, Alvo, Walmart, etc.
Asprox também cumpre um módulo de digitalização, procurando sites hackeados ou vulneráveis, contaminando aqueles com malware também, para que se espalhe para uma gama maior de usuários. As vítimas que os visitam também são objeto dos Trojans.
De acordo com uma publicação na postagem do blog Malcovery, a campanha do botnet Asprox espalha duas variantes do malware. Um dos cavalos de Tróia está sendo enviado como um anexo de uma mensagem de e-mail e o outro como um link, levando a um site comprometido. Analisando ambos, pesquisadores descobriram que as duas versões do Asprox estão localizadas em dois servidores de comando e controle separados (C&C) e que um deles é realmente mais velho que o outro.
Cuidado com as mensagens de entrega de e-mail
Embora as mensagens de e-mail que os usuários recebem pareçam ser de empresas grandes e legítimas, eles devem ter muito cuidado antes de abrir links de tais. Uma das principais dicas nessas mensagens é que o remetente e o nome do varejista no assunto parecem ser totalmente diferentes. Os usuários podem receber uma mensagem, por exemplo, com assunto “Walmart” e o nome de domínio do remetente para conter “CostCo”, etc.
Proteção
Como é apenas o início da temporada de férias, os pesquisadores acham que o botnet Asprox ainda não atingiu seu pico. Os cibercriminosos sabem disso e tentarão usar todo o seu potencial.
Os usuários são aconselhados a ter extremo cuidado com o envio e entrega de mensagens e a não abrir links diretamente do corpo dos e-mails. Se eles gostariam de abrir tal, é altamente recomendável digitá-lo manualmente em uma guia separada de seu navegador.
Eles também devem saber para evitar abrir anexos de tais, especialmente se eles não estiverem esperando nenhuma entrega recente. Comparar o assunto da mensagem e o domínio do e-mail do remetente também é essencial para reconhecer e-mails maliciosos.