 Quando uma série de ataques maliciosos estão ocorrendo, certifique-se de que botnets estejam envolvidos. Botnets são uma das ameaças cibernéticas mais perigosas, comprometer a rede e os computadores domésticos. Como você deve saber, um botnet é um grupo de máquinas comprometidas conectadas via Internet e se comunicando com outras máquinas. Botnets ilegais podem ser usados em várias operações maliciosas, como envio de spam, executar ataques DDoS, etc.
Quando uma série de ataques maliciosos estão ocorrendo, certifique-se de que botnets estejam envolvidos. Botnets são uma das ameaças cibernéticas mais perigosas, comprometer a rede e os computadores domésticos. Como você deve saber, um botnet é um grupo de máquinas comprometidas conectadas via Internet e se comunicando com outras máquinas. Botnets ilegais podem ser usados em várias operações maliciosas, como envio de spam, executar ataques DDoS, etc.
Seu computador é um zumbi?
Computadores zumbis nada mais são do que máquinas comuns situadas em residências e escritórios espalhados pelo mundo. Qualquer (desprotegido) computador pode se tornar parte de uma botnet. Os invasores só precisam se infiltrar no sistema de destino, geralmente através de um backdoor e solta malware nele. A instalação de botnets geralmente acontece por meio da exploração de vulnerabilidades em software existente. Às vezes, engenharia social (phishing, spear phishing) também pode ser incluído no cenário de ataque. A pior parte é que o dono do computador comprometido pode ficar sem saber das atividades do botnet por um período indefinido.
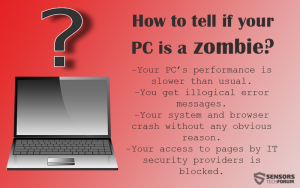
Como saber se seu PC foi transformado em um zumbi?
Se as seguintes ações continuarem acontecendo, seu computador pode fazer parte de um botnet:
- O desempenho da sua máquina está mais lento que o normal, não importa quantos aplicativos você tenha em execução. Isso pode ser porque o processador do seu computador pode ser explorado por hackers.
- Você recebe muitas mensagens de erro ilógicas.
- Seu sistema e navegador travam sem qualquer motivo óbvio.
- Seu acesso a páginas por provedores de segurança de TI está bloqueado.
- Há mensagens em sua pasta de e-mails enviados que não foram enviadas por você.
assim, quantos botnets existem?
É difícil atirar em um número exato. Contudo, fornecedores de segurança analisam periodicamente dados compilados. Alguns dos piores botnets que vimos ativos nos últimos dois anos são ZeroAccess, Conficker, Kraken, Simda, Asprox. Interessantemente suficiente, A Kaspersky Labs concluiu que aproximadamente 70% das vítimas de botnet DDoS estão localizadas em apenas dez países. Pelo menos é o que as estatísticas do segundo trimestre de 2015 tem mostrado. Os dois países mais visados são os Estados Unidos e a China, o que pode ser facilmente explicado pela hospedagem barata oferecida por eles. Não obstante, uma coisa é certa - nenhum país é seguro o suficiente para evitar ataques DDoS (Apesar de, por algumas razões, alguns territórios são preferidos a outros).
Qual é o botnet conhecido mais perigoso?
De acordo com pesquisa da empresa de segurança italiana FoxIT, Ponmocup ou Poncocup Hunter é um dos botnets mais antigos e bem sucedidos que ao longo do tempo infectou 15 milhões de computadores e fez milhões de dólares. Ponmocup é, Contudo, muitas vezes subestimado pelos fornecedores de AV e, portanto,, não chegou às manchetes com tanta frequência quanto outros botnets. O pico do Ponmocup foi em 2011 quando assumiu o controle 2.4 milhões de máquinas. No 2015, pesquisadores acreditam que pelo menos meio milhão de sistemas são vitimados pela botnet. Alguns especialistas referem-se ao botnet como 'um gigante escondido nas sombras'.
Ponmocup foi descoberto pela primeira vez em 2006. Naquela época, era conhecido como Vundo e Virtumonde. É sofisticado e subestimado – uma combinação que provou ser bastante bem-sucedida para seus autores, atualmente focado em um ganho financeiro puro.
Especialistas da FoxIT acreditam que as técnicas empregadas pelo Ponmocup sugerem que seus autores têm conhecimento acima da média do Windows e muitos anos de experiência em software malicioso. Os criminosos cibernéticos são suspeitos de serem de origem russa, com base na descoberta de que as instruções para afiliados são escritas em russo. Aparentemente o Ponmocup não infectaria países dos Estados soviéticos.
Os pesquisadores acreditam que a quantia exata de dinheiro que os operadores do Ponmocup ganharam não pode ser calculada com precisão. O que se sabe, porém, é que seus lucros se aproximam dos ganhos de um negócio multimilionário.. Bem, o cibercrime provou ser um campo de trabalho gratificante, não tem?
Leia mais sobre Roubar dinheiro online a maneira do crime cibernético
Como evitar que sua máquina se torne um zumbi?
Tendo em mente que as redes de bot são frequentemente implantadas para espalhar malware por várias máquinas simultaneamente, ter uma solução anti-malware poderosa parece ser uma necessidade.
Os cibercriminosos aplicam duas estratégias para invadir as máquinas das vítimas e transformá-las em zumbis:
- Instalação de malware através da exploração de vulnerabilidades de software ou do seqüestro de suas contas fracas. Saiba por que as senhas importam.
- Enganando você a instalar malware com a ajuda de técnicas de engenharia social.
Para melhorar sua segurança e evitar se tornar um zumbi, consulte as seguintes dicas de segurança:
- Instale software anti-spyware e antivírus. Um programa anti-spyware rastreia os componentes da espionagem e penetra profundamente no sistema. Um programa antivírus pesquisará o disco rígido e removerá os convidados indesejados. Além disso, tenha em mente que é importante usar um software que funcione em tempo real.
- Atualize seu software com freqüência, sistema operacional e navegadores.
- Use senhas fortes.
- Mantenha seu firewall ligado. Um firewall fornece proteção contra intrusos da Internet.
- Não use pen drives de origem desconhecida.
- Revise seus hábitos de navegação e download e aplique filtros anti-spam.

digitalizador Spy Hunter só irá detectar a ameaça. Se você quiser a ameaça de ser removido automaticamente, você precisa comprar a versão completa da ferramenta anti-malware.Saiba Mais Sobre SpyHunter Anti-Malware Ferramenta / Como desinstalar o SpyHunter
Referências:
Microsoft
Kaspersky
Software Enigma
O registro
FoxIT
ZoneAlarm


