VK Virus
Il virus VK rappresenta una nuova minaccia web, mascherato da popolare social network VK. I suoi metodi per infettare le vittime variano, dipende dagli hacker’ strategie e condizioni locali della macchina. In questa guida completa alla rimozione, forniremo alle vittime istruzioni dettagliate per ripristinare in modo efficace le loro macchine compromesse

Riepilogo del virus VK
| Nome | VK Virus |
| Tipo | Reindirizzare, Adware, Dominio dannoso |
| Tempo di rimozione | Meno di 15 verbale |
| Strumento di rimozione |
Verifica se il tuo sistema è stato interessato da malware
Scarica
Strumento di rimozione malware
|
VK Virus – Come ho ricevuto E
Il virus VK, parte di una famiglia di minacce basate sul web, inganna le vittime apparendo affiliato al popolare VK (VKontakte) rete sociale. Nella realtà, questi file virus non hanno alcuna affiliazione; sfruttano la base utenti globale della rete, poiché gli utenti scaricano e interagiscono facilmente con qualsiasi software o sito percepito relativo alla rete.
Gli hacker utilizzano vari metodi per diffondere campioni di virus VK, con pagine dannose che imitano il contenuto della rete che sono una scelta comune. Queste pagine sono spesso ospitate su nomi di dominio che assomigliano al sito autentico e possono presentare certificati di sicurezza autofirmati o rubati.
Gli utenti possono anche ricevere collegamenti infetti tramite phishing campagne, in genere tramite messaggi di posta elettronica e portali di reindirizzamento falsi. Queste campagne si mascherano da messaggi legittimi provenienti dal social network.
Il Virus VK può anche essere integrato in vari vettori payload di cui ci sono due tipi principali:
- documenti dannosi - I criminali possono creare documenti attraverso tutti i tipi popolari che includeranno gli script di infezione rilevanti. Questo comprende fogli di calcolo, presentazioni, database e file di testo.
- installazione di applicazioni - Gli hacker possono anche creare pacchetti di installazione del software popolare che è comunemente acquisito dagli utenti finali.
Tutti i file eseguibili possono anche essere caricati a vari reti di condivisione file - il più popolare è BitTorrentt. E 'utilizzato per diffondere sia contenuti legittimi e pirata. In certe situazioni gli hacker possono anche utilizzare browser hijacker che fornirà gli script necessari - sono caricati i repository rilevanti dei browser Web più diffusi utilizzando false recensioni degli utenti e le credenziali per sviluppatori.
VK Virus – Che cosa fa?
Il virus VK assume varie forme in base all'incontro della vittima, adattarsi alle condizioni locali. Tipicamente, inizia con la raccolta di informazioni, alla ricerca di dati che rivelano le vittime’ identità e profili hardware.
Il Prossimo, il "bypass di sicurezza".’ il modulo esegue la scansione e rimuove le applicazioni che possono bloccare il virus VK, come ad esempio programmi antivirus, firewall, e sistemi di rilevamento delle intrusioni.
La minaccia può anche alterare le opzioni di avvio, rendendo difficile seguire le guide per la rimozione manuale, insieme alla rimozione di file sensibili come backup e punti di ripristino.
INOLTRE, può modificare il registro di Windows, influendo sulle prestazioni del sistema, stabilità, e integrità dei dati.
Inoltre, il virus può fungere da meccanismo di consegna per altri tipi di malware, Comprese Trojan, minatori, reindirizzamenti, dirottatori, etc. La rimozione tempestiva è fondamentale per prevenire ulteriori complicazioni.
Rimuovere VK virus dal computer
Per rimuovere VK Virus in modo efficace, seguire questi passaggi per individuare ed eliminare i file e gli oggetti nascosti. Per il rilevamento e la rimozione completi, consigliamo di utilizzare un software anti-malware avanzato. Identificherà ed eliminerà automaticamente tutti i file e gli oggetti relativi a VK Virus, garantendo la protezione futura del tuo computer.
- Windows
- Mac OS X
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
- Safari
- Internet Explorer
- Interrompi i popup push
Come rimuovere VK Virus da Windows.
Passo 1: Scansione per VK virus con lo strumento SpyHunter Anti-Malware



Passo 2: Avvia il PC in modalità provvisoria





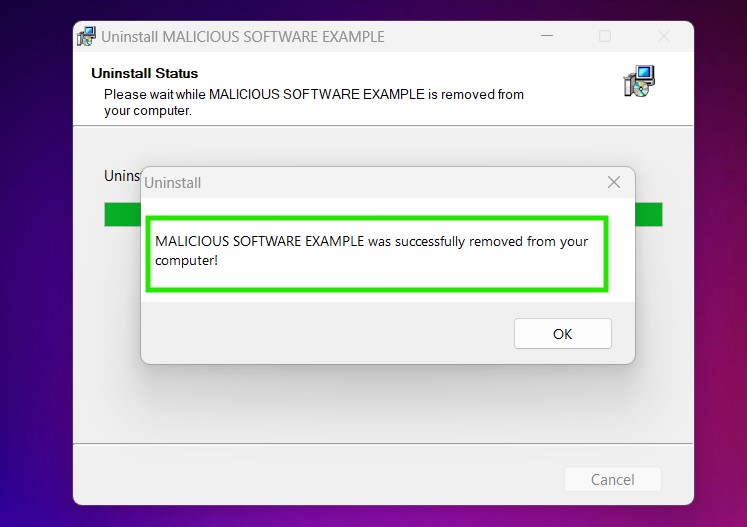
Passo 3: Disinstallare VK Virus e relativo software da Windows
Passaggi di disinstallazione per Windows 11
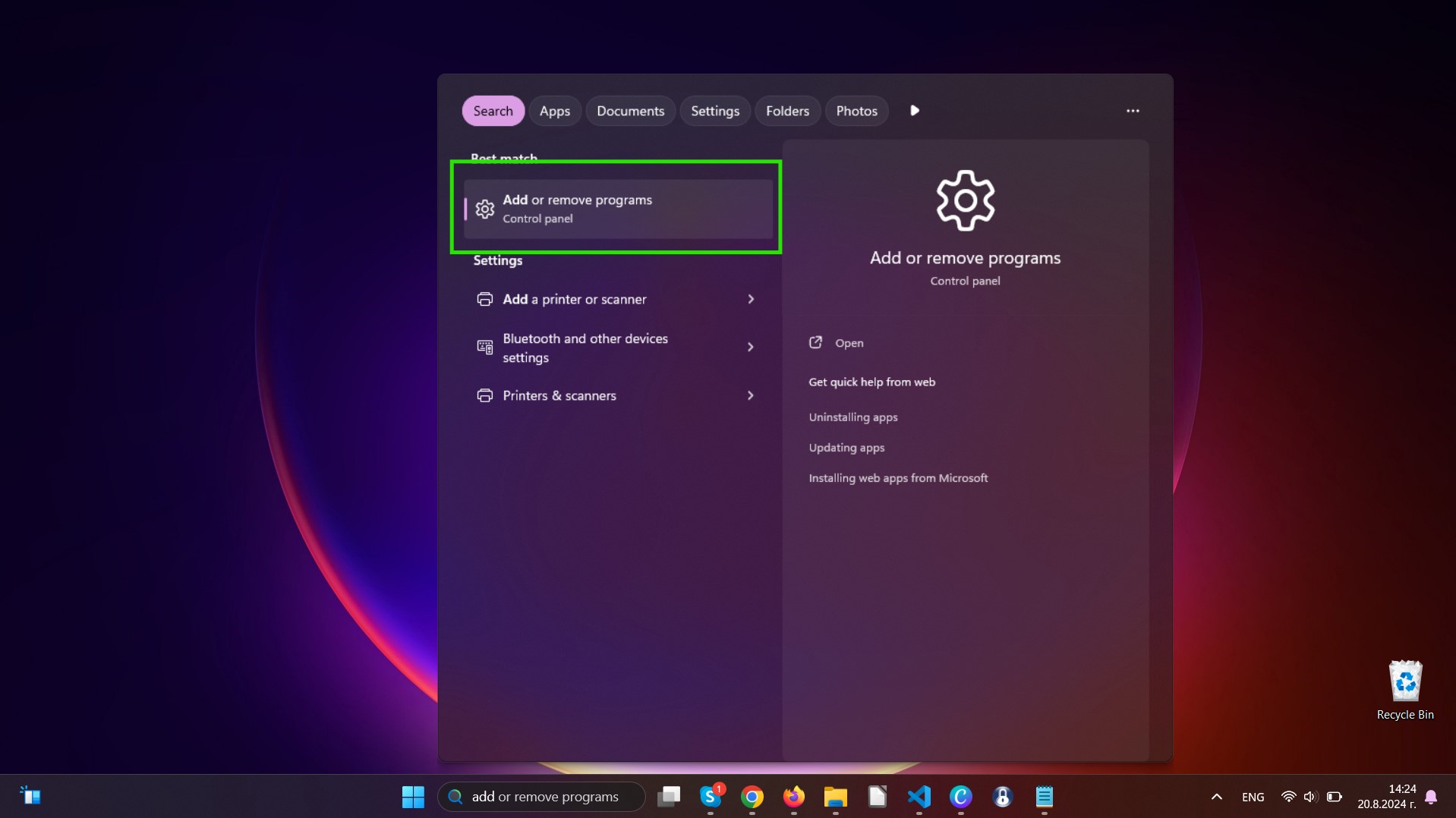
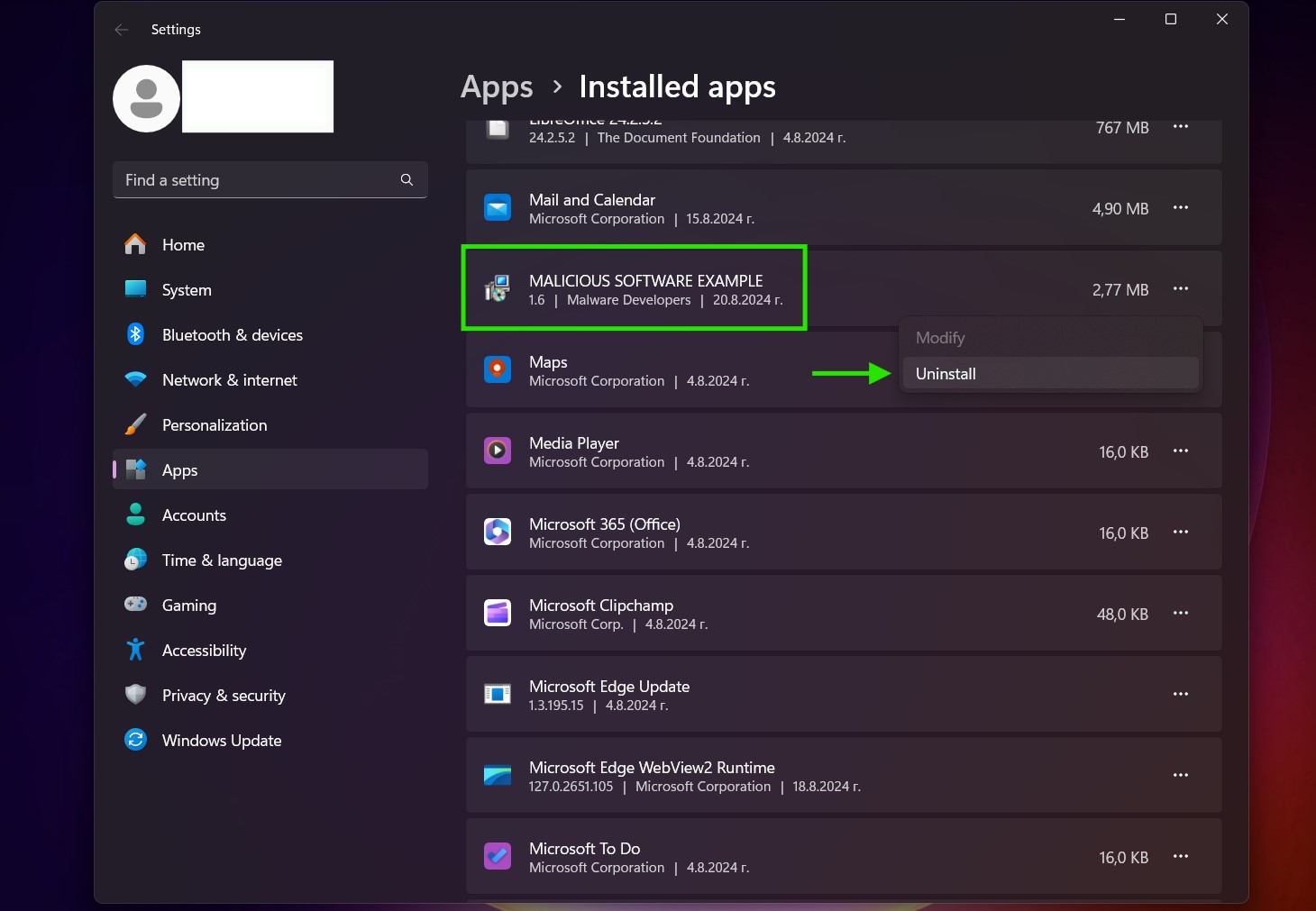
Passaggi di disinstallazione per Windows 10 e versioni precedenti
Ecco un metodo in pochi semplici passi che dovrebbero essere in grado di disinstallare maggior parte dei programmi. Non importa se si utilizza Windows 10, 8, 7, Vista o XP, quei passi otterrà il lavoro fatto. Trascinando il programma o la relativa cartella nel cestino può essere un molto cattiva decisione. Se lo fai, frammenti di programma vengono lasciati, e che possono portare al lavoro instabile del PC, errori con le associazioni di tipo file e altre attività spiacevoli. Il modo corretto per ottenere un programma dal computer è di disinstallarlo. Per fare questo:


 Seguire le istruzioni di cui sopra e vi disinstallare correttamente maggior parte dei programmi.
Seguire le istruzioni di cui sopra e vi disinstallare correttamente maggior parte dei programmi.
Passo 4: Pulisci tutti i registri, Created by VK Virus on Your PC.
I registri di solito mirati di macchine Windows sono i seguenti:
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion Run
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion Run
- HKEY_LOCAL_MACHINE Software Microsoft Windows CurrentVersion RunOnce
- HKEY_CURRENT_USER Software Microsoft Windows CurrentVersion RunOnce
È possibile accedere aprendo l'editor del registro di Windows e l'eliminazione di tutti i valori, creato da VK Virus lì. Questo può accadere seguendo la procedura sotto:


 Mancia: Per trovare un valore virus creato, è possibile fare clic destro su di esso e fare clic su "Modificare" per vedere quale file è impostato per funzionare. Se questa è la posizione file del virus, rimuovere il valore.
Mancia: Per trovare un valore virus creato, è possibile fare clic destro su di esso e fare clic su "Modificare" per vedere quale file è impostato per funzionare. Se questa è la posizione file del virus, rimuovere il valore.
Guida alla rimozione dei video per VK Virus (Windows).
Sbarazzati di VK Virus da Mac OS X.
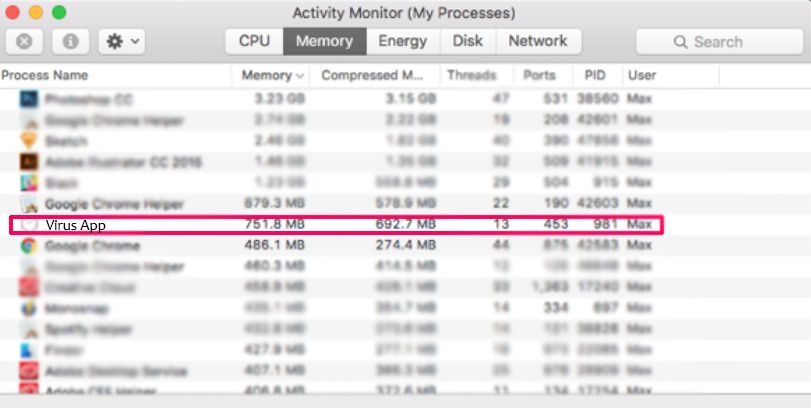
Passo 1: Disinstalla VK Virus e rimuovi file e oggetti correlati
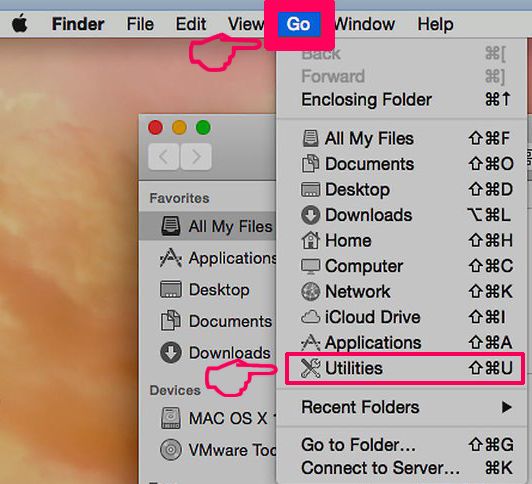
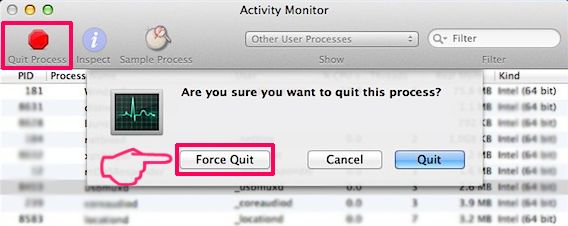
Il Mac ti mostrerà un elenco di elementi che si avvia automaticamente quando si accede. Cercare eventuali applicazioni sospette identici o simili a VK Virus. Controllare l'applicazione che si desidera interrompere l'esecuzione automatica e quindi selezionare sul Meno ("-") icona per nasconderlo.
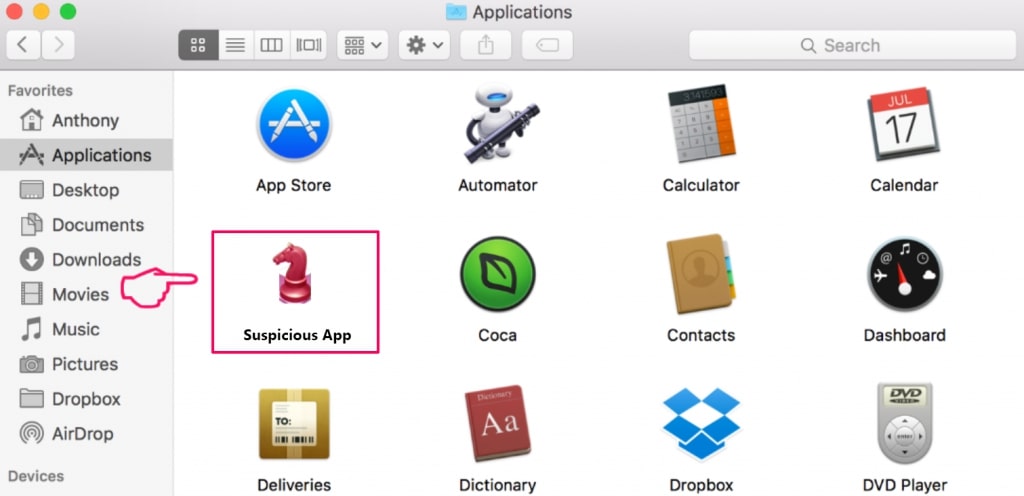
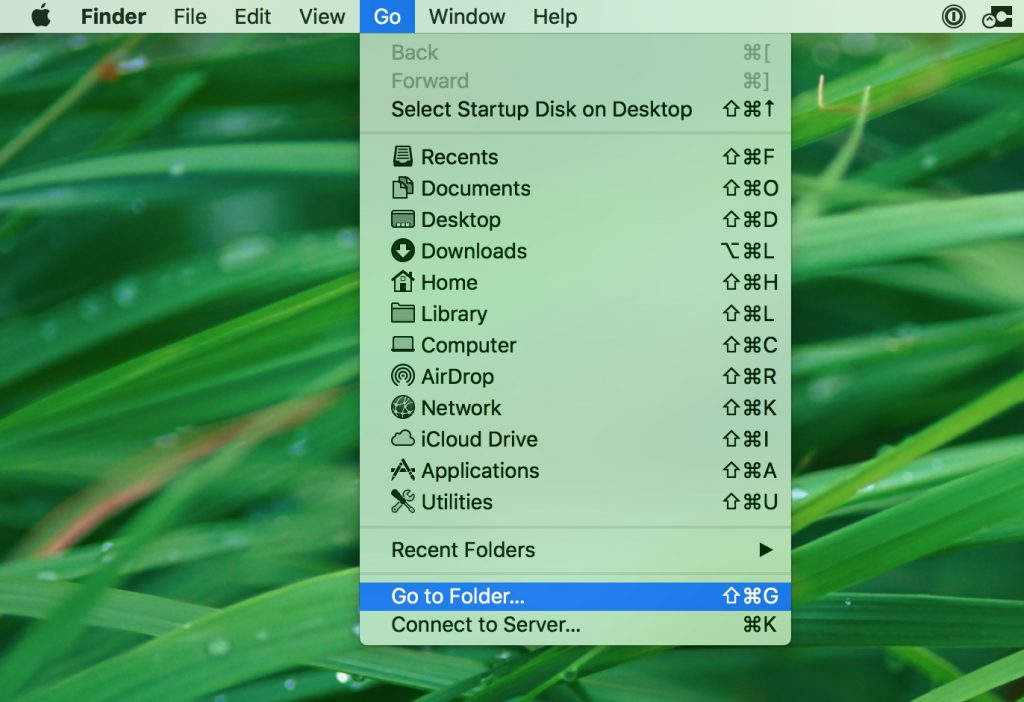
- Vai a mirino.
- Nella barra di ricerca digitare il nome della app che si desidera rimuovere.
- Al di sopra della barra di ricerca cambiare i due menu a tendina per "File di sistema" e "Sono inclusi" in modo che è possibile vedere tutti i file associati con l'applicazione che si desidera rimuovere. Tenete a mente che alcuni dei file non possono essere correlati al app in modo da essere molto attenti che i file si elimina.
- Se tutti i file sono correlati, tenere il ⌘ + A per selezionare loro e poi li di auto "Trash".
Nel caso in cui non è possibile rimuovere VK Virus tramite Passo 1 sopra:
Nel caso in cui non è possibile trovare i file dei virus e gli oggetti nelle applicazioni o altri luoghi che abbiamo sopra riportati, si può cercare manualmente per loro nelle Biblioteche del Mac. Ma prima di fare questo, si prega di leggere il disclaimer qui sotto:
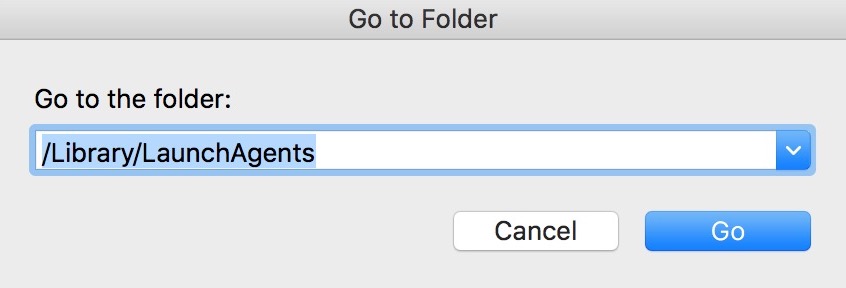
Puoi ripetere la stessa procedura con il seguente altro Biblioteca directory:
→ ~ / Library / LaunchAgents
/Library / LaunchDaemons
Mancia: ~ è lì apposta, perché porta a più LaunchAgents.
Passo 2: Scansiona e rimuovi i file VK Virus dal tuo Mac
Quando si trovano ad affrontare problemi sul vostro Mac come un risultato di script indesiderati e programmi come VK Virus, il modo consigliato di eliminare la minaccia è quello di utilizzare un programma anti-malware. SpyHunter per Mac offre funzionalità di sicurezza avanzate insieme ad altri moduli che miglioreranno la sicurezza del tuo Mac e la proteggeranno in futuro.
Guida alla rimozione dei video per VK Virus (Mac)
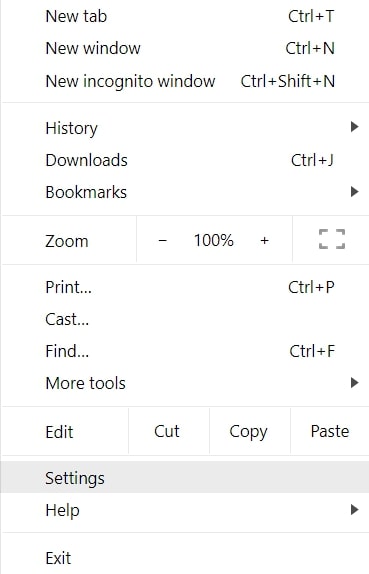
Rimuovi VK Virus da Google Chrome.
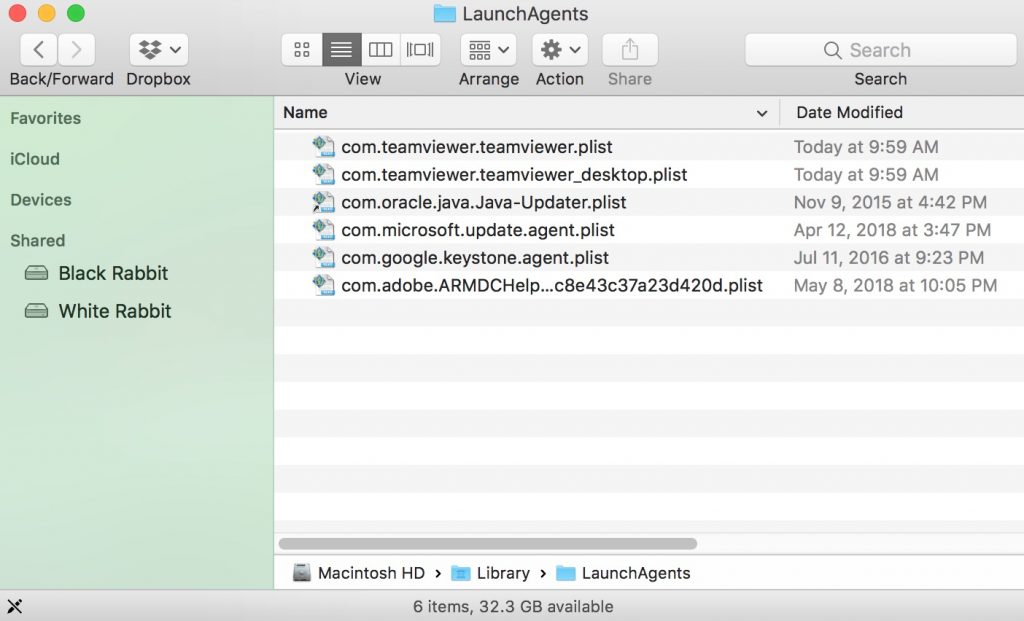
Passo 1: Avvia Google Chrome e apri il menu a discesa
Passo 2: Spostare il cursore sopra "Strumenti" e poi dal menu esteso scegliere "Estensioni"
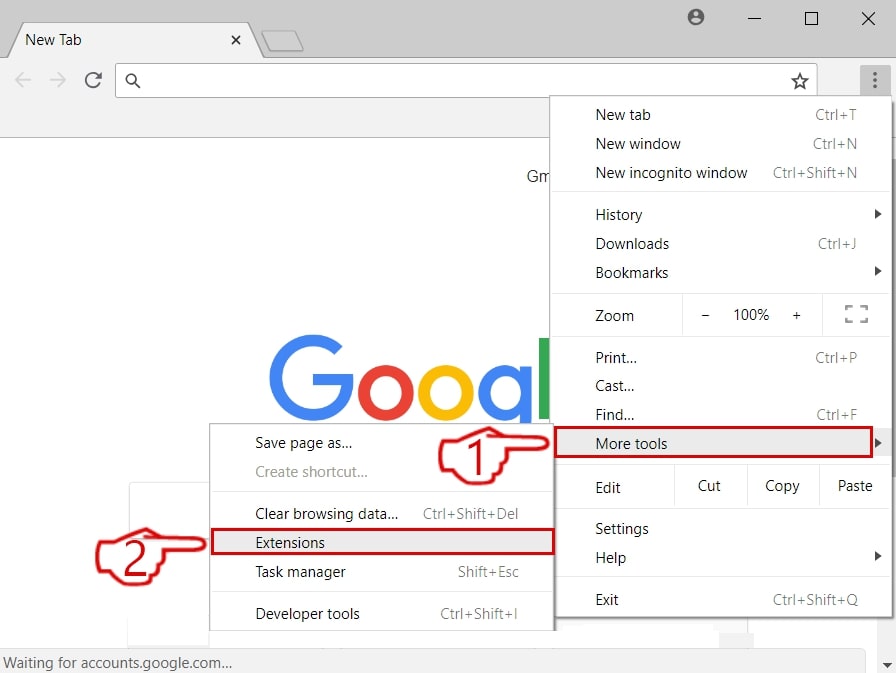
Passo 3: Dal aperto "Estensioni" menu di individuare l'estensione indesiderata e fare clic sul suo "Rimuovere" pulsante.
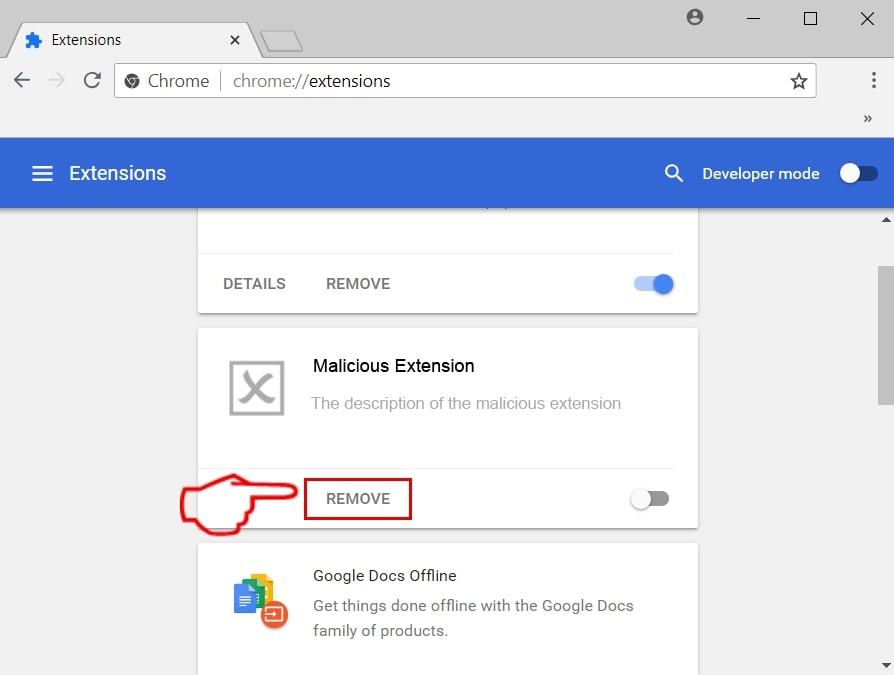
Passo 4: Dopo l'estensione viene rimossa, riavviare Google Chrome chiudendo dal rosso "X" pulsante in alto a destra e iniziare di nuovo.
Cancella VK Virus da Mozilla Firefox.
Passo 1: Avviare Mozilla Firefox. Aprire la finestra del menu:
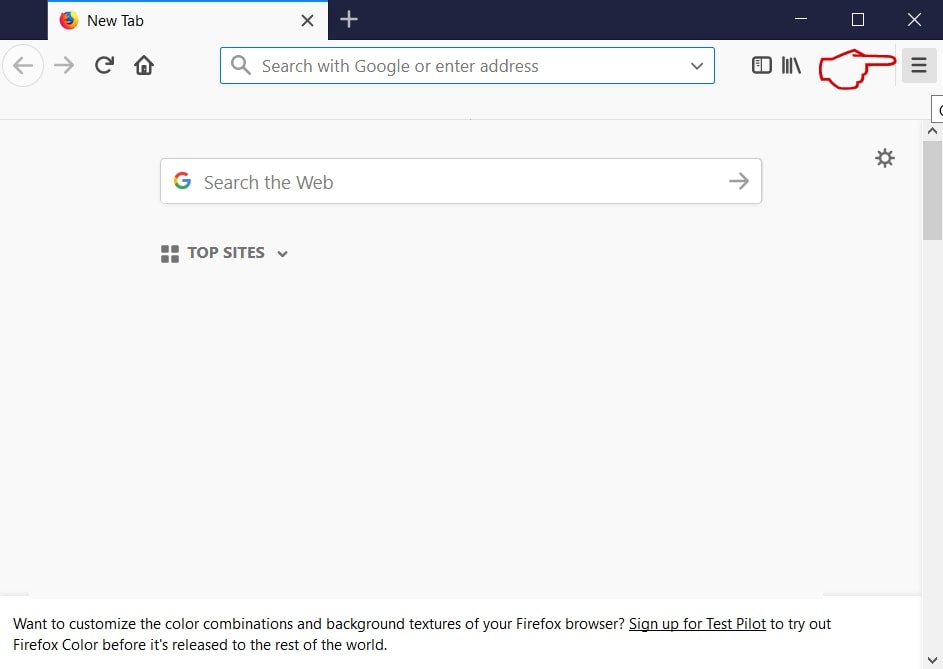
Passo 2: Selezionare il "Componenti aggiuntivi" icona dal menu.
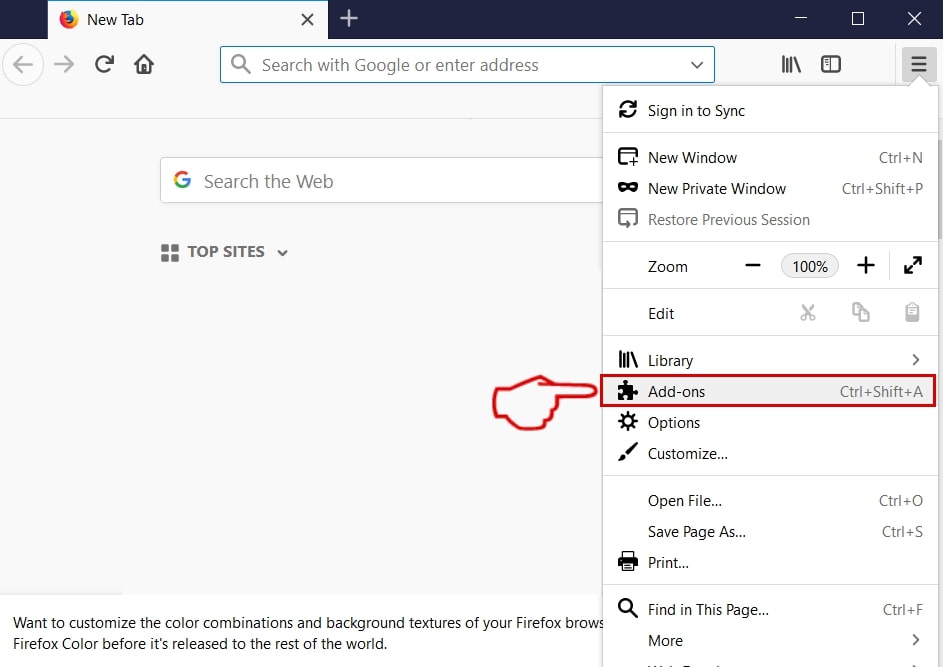
Passo 3: Selezionare l'estensione indesiderata e fare clic su "Rimuovere"

Passo 4: Dopo l'estensione viene rimossa, riavviare Mozilla Firefox chiudendo dal rosso "X" pulsante in alto a destra e iniziare di nuovo.
Disinstallare VK Virus da Microsoft Edge.
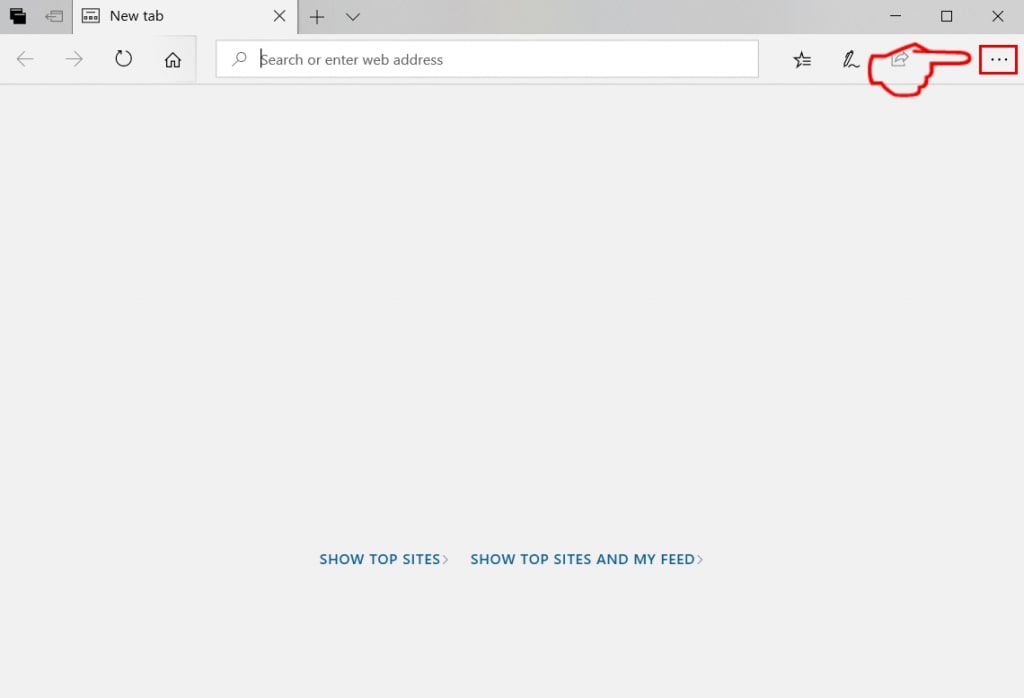
Passo 1: Avviare il browser Edge.
Passo 2: Apri il menu a tendina facendo clic sull'icona nell'angolo in alto a destra.
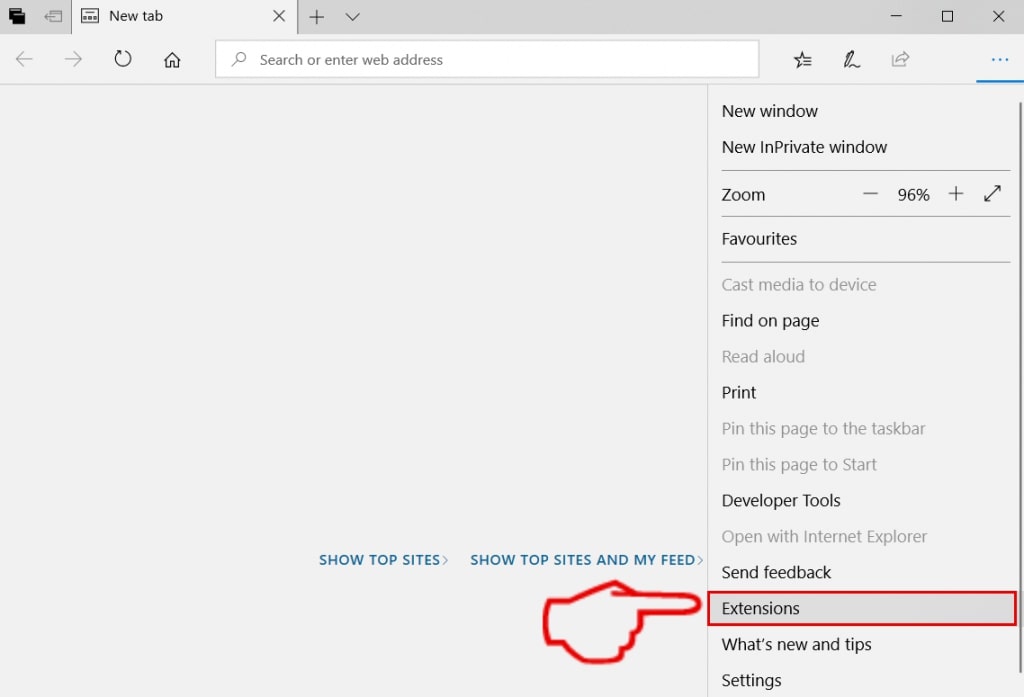
Passo 3: Dal menu a discesa selezionare "Estensioni".
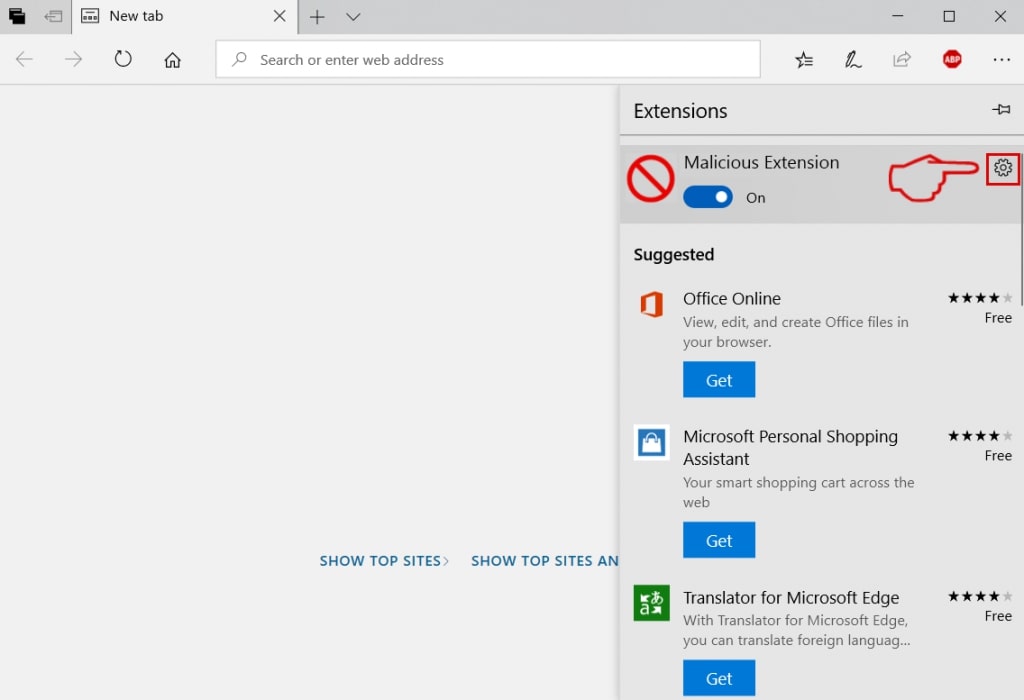
Passo 4: Scegli l'estensione dannosa sospetta che desideri rimuovere, quindi fai clic sull'icona a forma di ingranaggio.
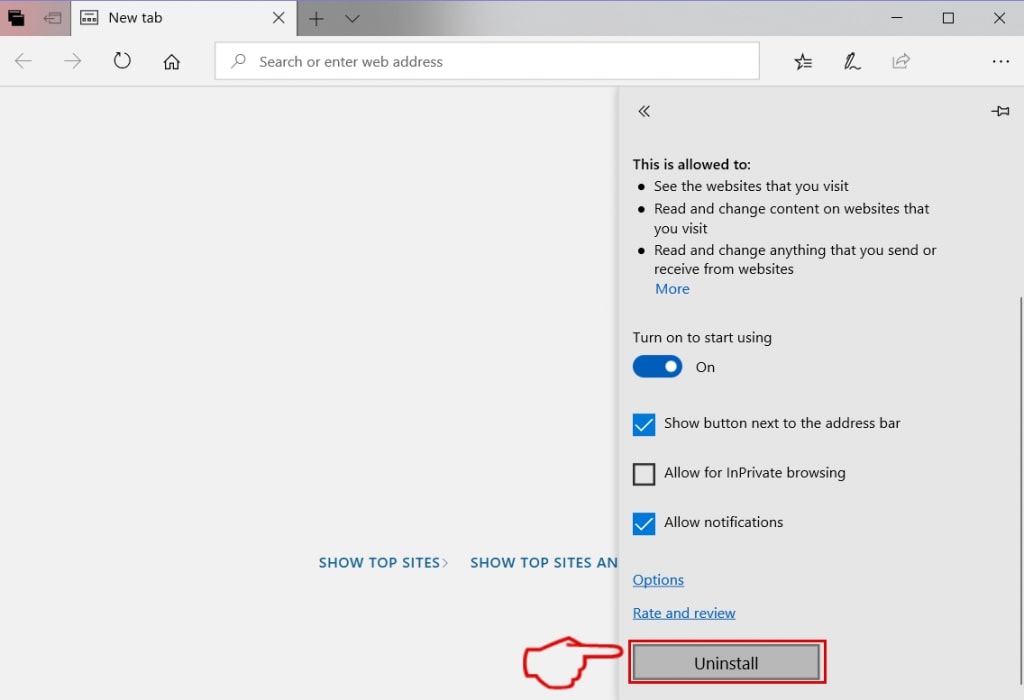
Passo 5: Rimuovere l'estensione dannosa scorrendo verso il basso e quindi facendo clic su Disinstalla.
Rimuovere VK Virus da Safari
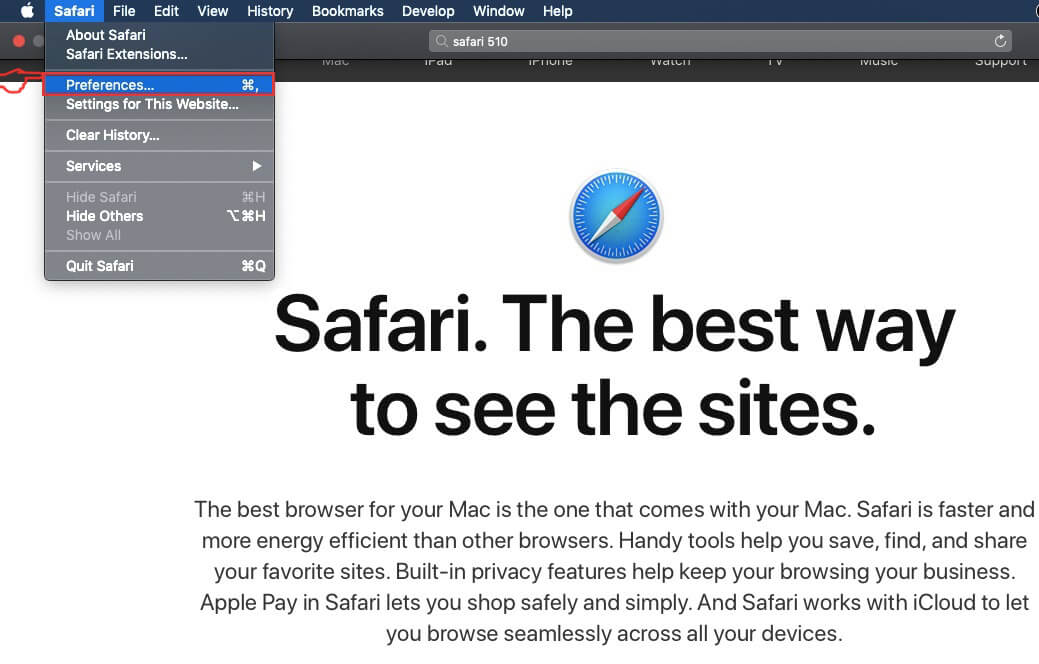
Passo 1: Avvia l'app Safari.
Passo 2: Dopo avere posizionato il cursore del mouse nella parte superiore dello schermo, fai clic sul testo di Safari per aprire il suo menu a discesa.
Passo 3: Dal menu, clicca su "Preferenze".
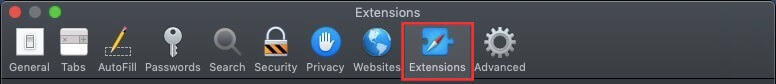
Passo 4: Dopo di che, seleziona la scheda "Estensioni".
Passo 5: Fare clic una volta sulla estensione che si desidera rimuovere.
Passo 6: Fare clic su "Disinstalla".
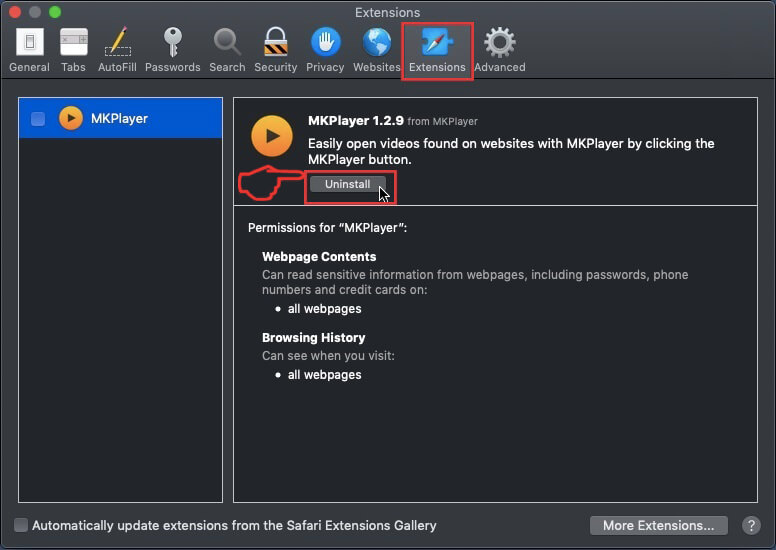
Una finestra pop-up che chiede conferma per disinstallare l'estensione. Selezionare 'Uninstall' di nuovo, e il virus VK sarà rimosso.
Elimina VK Virus da Internet Explorer.
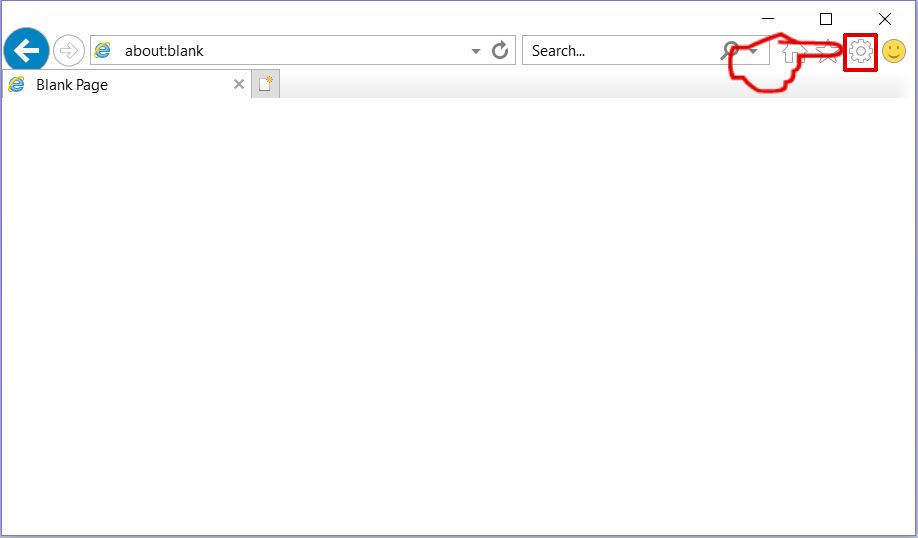
Passo 1: Avviare Internet Explorer.
Passo 2: Fare clic sull'icona a forma di ingranaggio denominata "Strumenti" per aprire il menu a discesa e selezionare "Gestisci componenti aggiuntivi"
Passo 3: Nella finestra "Gestisci componenti aggiuntivi".
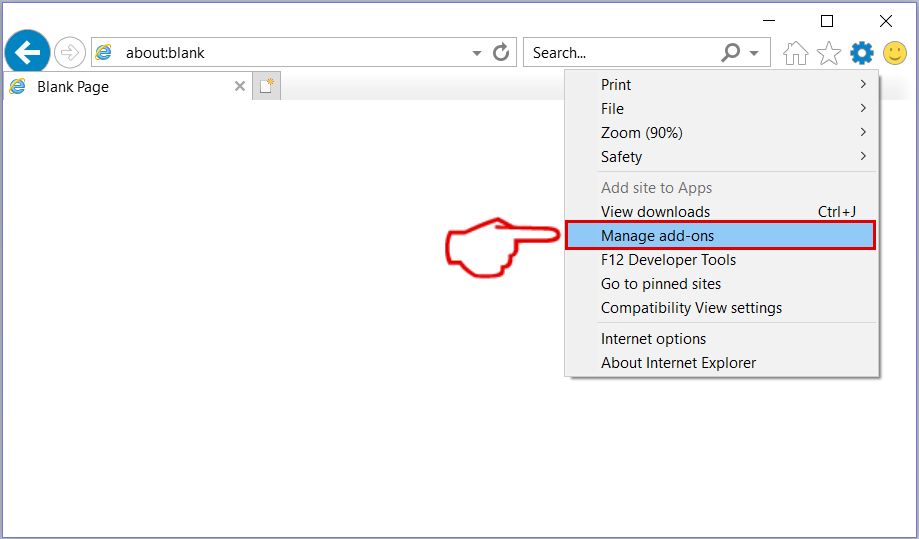
Passo 4: Seleziona l'estensione che desideri rimuovere, quindi fai clic su "Disabilita". Una finestra pop-up apparirà per informarvi che si sta per disattivare l'estensione selezionata, e alcuni altri componenti aggiuntivi potrebbero essere disattivate pure. Lasciare tutte le caselle selezionate, e fai clic su "Disabilita".
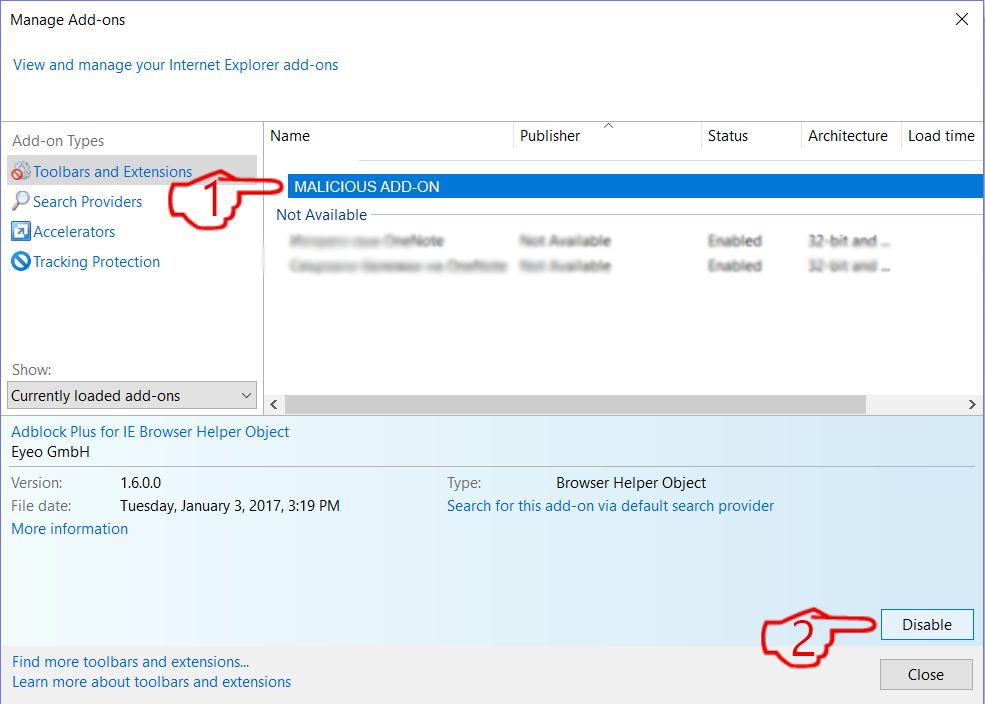
Passo 5: Dopo l'estensione indesiderato è stato rimosso, riavvia Internet Explorer chiudendolo dal pulsante rosso "X" situato nell'angolo in alto a destra e riavvialo.
Rimuovi le notifiche push dai tuoi browser
Disattiva le notifiche push da Google Chrome
Per disabilitare eventuali notifiche push dal browser Google Chrome, si prega di seguire i passi di seguito:
Passo 1: Vai a Impostazioni in Chrome.
Passo 2: In Impostazioni, selezionare “Impostazioni avanzate":
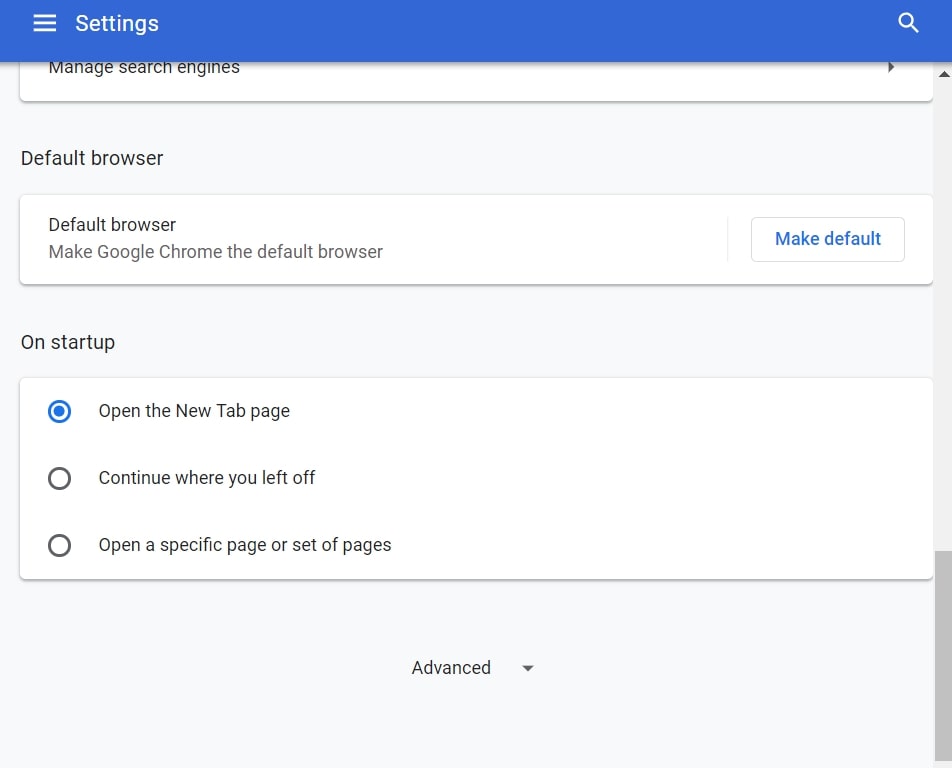
Passo 3: Fare clic su "Le impostazioni del contenuto":
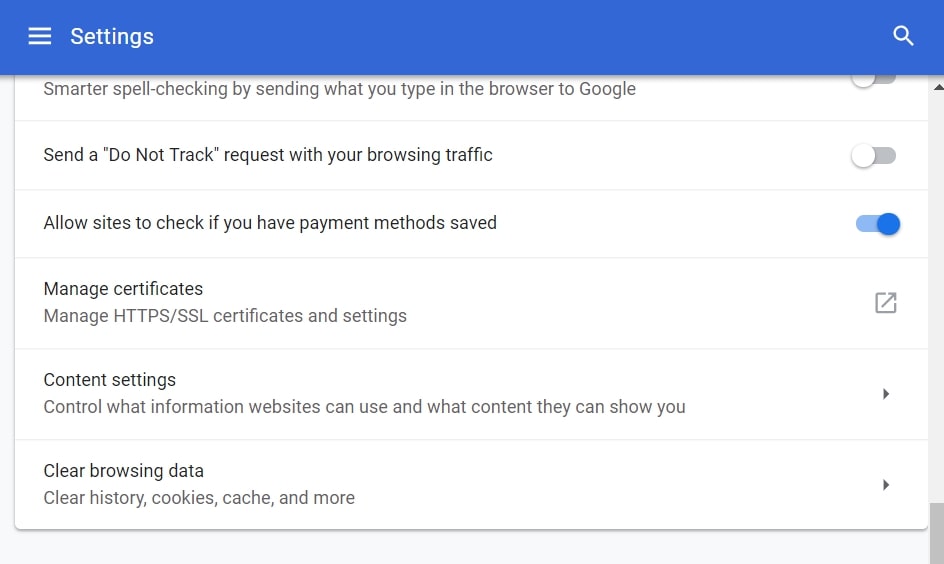
Passo 4: Aperto "notifiche":
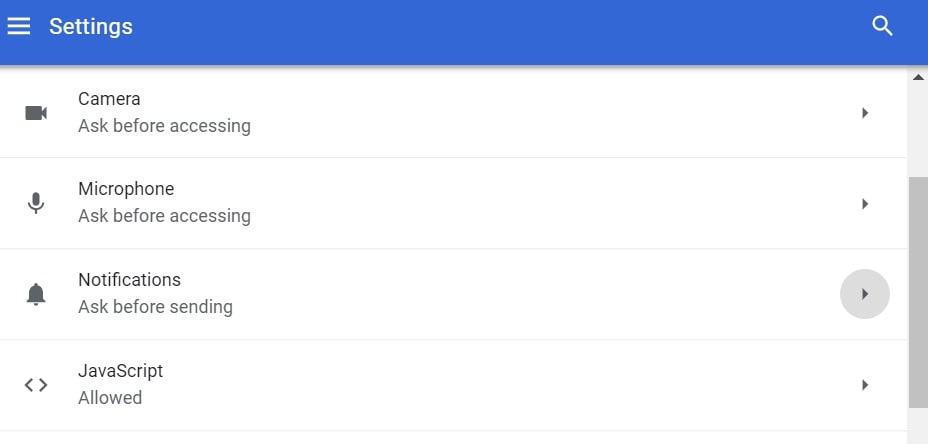
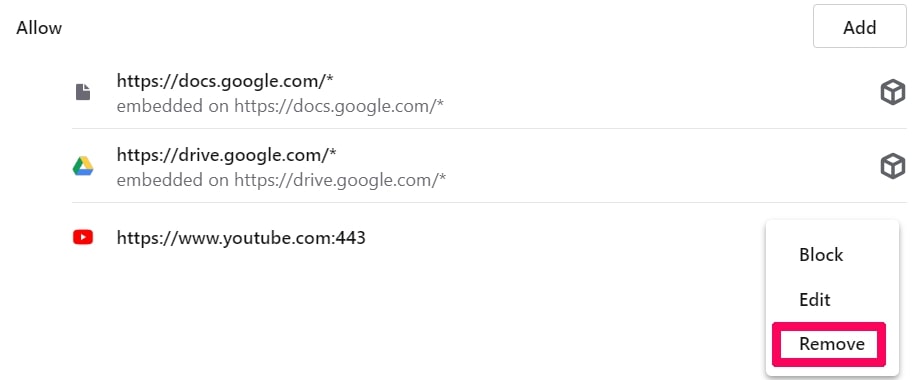
Passo 5: Fare clic sui tre punti e scegliere Blocca, Modificare o rimuovere le opzioni:

Rimuovere le notifiche push su Firefox
Passo 1: Vai a Opzioni di Firefox.
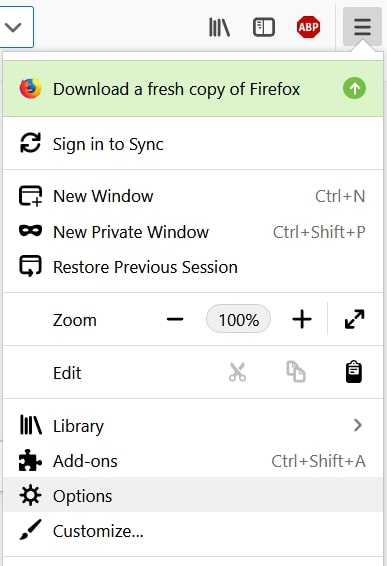
Passo 2: Vai alle impostazioni", digitare "notifiche" nella barra di ricerca e fare clic "Impostazioni":
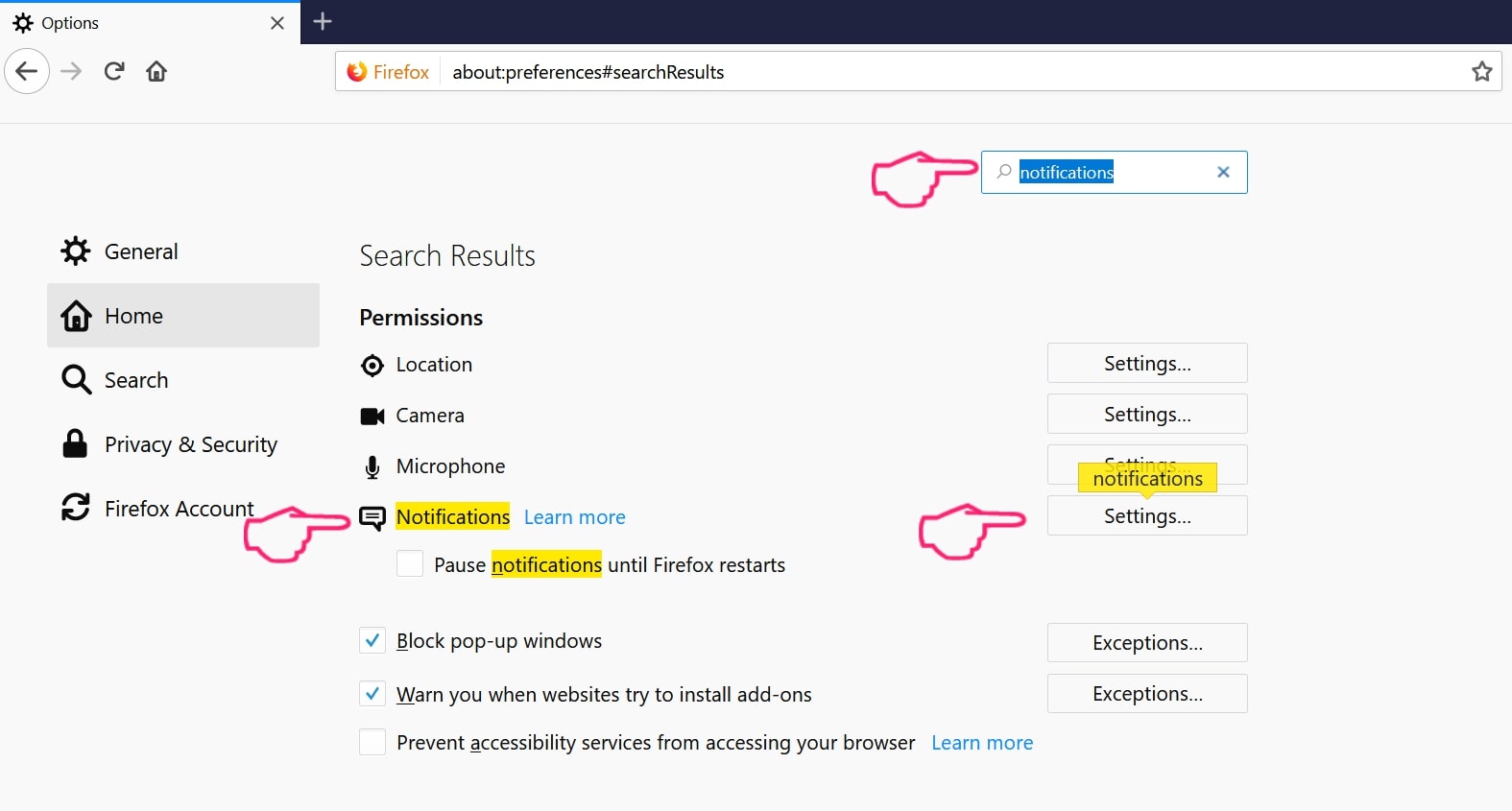
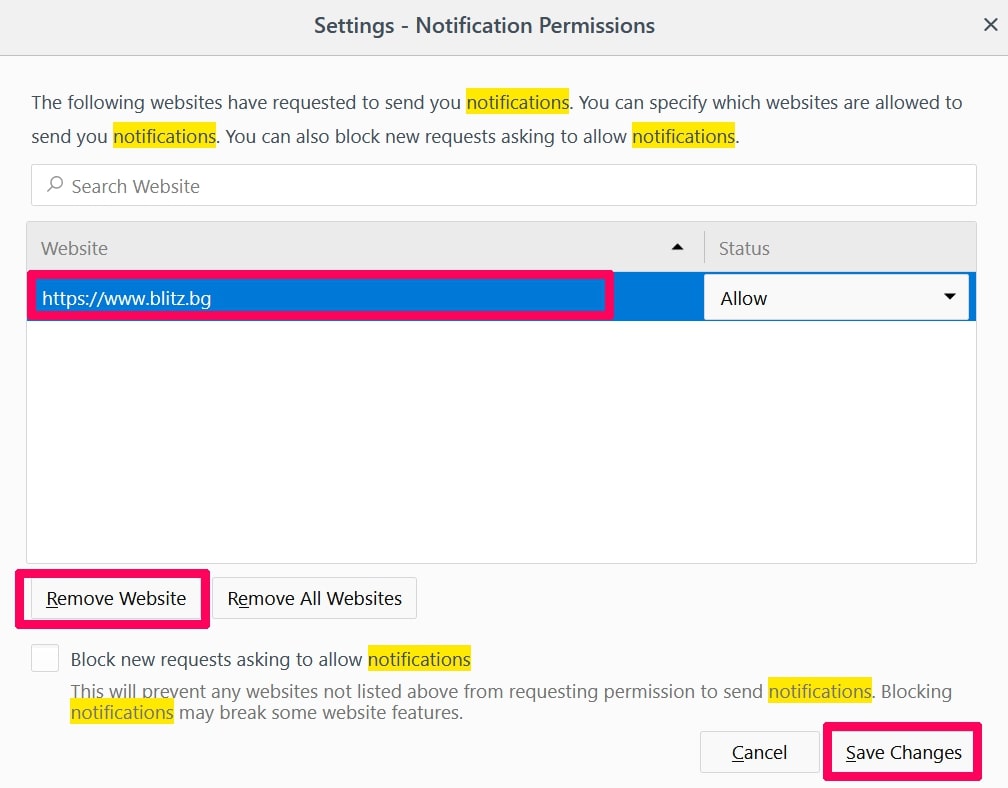
Passo 3: Fai clic su "Rimuovi" su qualsiasi sito in cui desideri che le notifiche vengano eliminate e fai clic su "Salva modifiche"
Interrompi le notifiche push su Opera
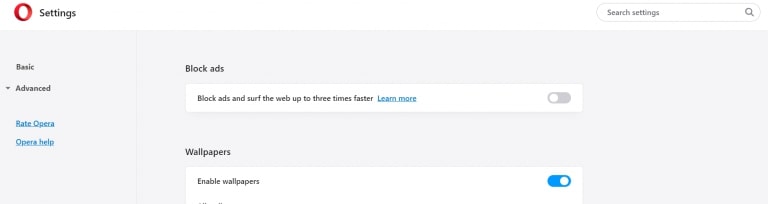
Passo 1: In Opera, stampa ALT + P per andare su Impostazioni.
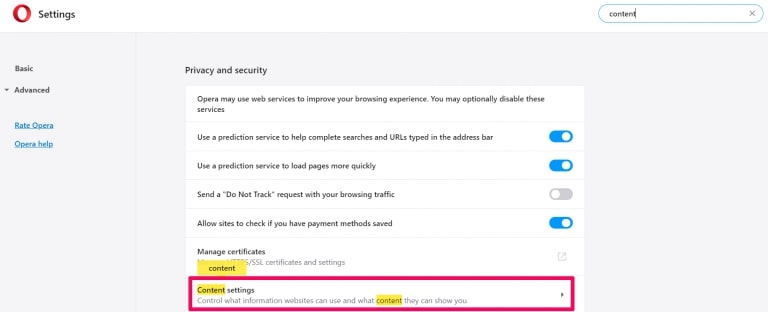
Passo 2: In Setting search, digitare "Contenuto" per accedere alle impostazioni del contenuto.
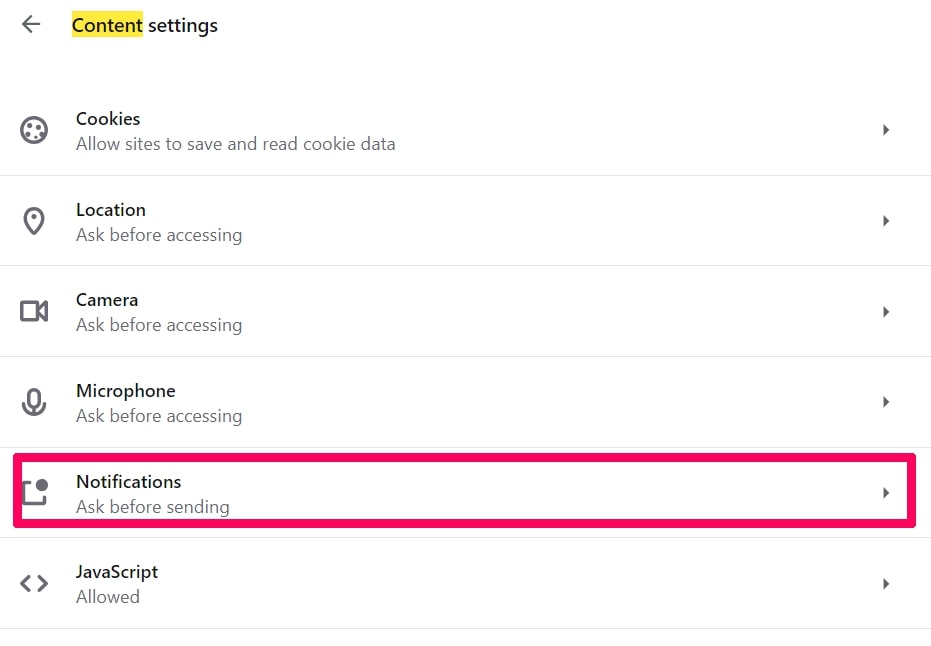
Passo 3: Notifiche aperte:
Passo 4: Fai lo stesso che hai fatto con Google Chrome (spiegato di seguito):
Elimina le notifiche push su Safari
Passo 1: Apri le preferenze di Safari.
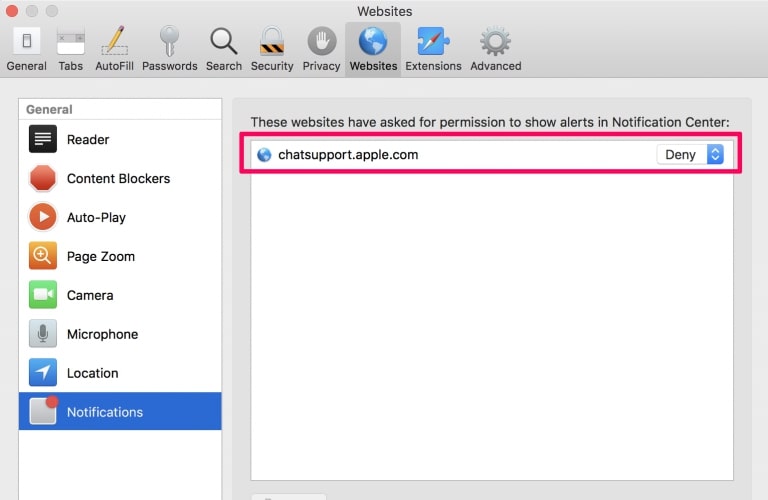
Passo 2: Scegli il dominio da cui ti piacciono i push pop-up e passa a "Negare" da parte di "permettere".
VK Virus-FAQ
What Is VK Virus?
La minaccia VK Virus è adware o virus redirect del browser.
Potrebbe rallentare notevolmente il computer e visualizzare annunci pubblicitari. L'idea principale è che le tue informazioni vengano probabilmente rubate o che più annunci vengano visualizzati sul tuo dispositivo.
I creatori di tali app indesiderate lavorano con schemi pay-per-click per fare in modo che il tuo computer visiti siti Web rischiosi o diversi tipi che potrebbero generare loro fondi. Questo è il motivo per cui non si preoccupano nemmeno dei tipi di siti Web visualizzati negli annunci. Questo rende il loro software indesiderato indirettamente rischioso per il tuo sistema operativo.
What Are the Symptoms of VK Virus?
Ci sono diversi sintomi da cercare quando questa particolare minaccia e anche le app indesiderate in generale sono attive:
Sintomo #1: Il tuo computer potrebbe rallentare e avere scarse prestazioni in generale.
Sintomo #2: Hai delle barre degli strumenti, componenti aggiuntivi o estensioni sui browser Web che non ricordi di aver aggiunto.
Sintomo #3: Vedi tutti i tipi di annunci, come i risultati di ricerca supportati da pubblicità, pop-up e reindirizzamenti per apparire casualmente.
Sintomo #4: Vedi le app installate sul tuo Mac in esecuzione automaticamente e non ricordi di averle installate.
Sintomo #5: Vedi processi sospetti in esecuzione nel tuo Task Manager.
Se vedi uno o più di questi sintomi, quindi gli esperti di sicurezza consigliano di controllare la presenza di virus nel computer.
Quali tipi di programmi indesiderati esistono?
Secondo la maggior parte dei ricercatori di malware ed esperti di sicurezza informatica, le minacce che attualmente possono colpire il tuo dispositivo possono essere software antivirus non autorizzato, adware, browser hijacker, clicker, ottimizzatori falsi e qualsiasi forma di PUP.
Cosa fare se ho un "virus" come VK Virus?
Con poche semplici azioni. Innanzitutto, è imperativo seguire questi passaggi:
Passo 1: Trova un computer sicuro e collegalo a un'altra rete, non quello in cui è stato infettato il tuo Mac.
Passo 2: Cambiare tutte le password, a partire dalle tue password e-mail.
Passo 3: consentire autenticazione a due fattori per la protezione dei tuoi account importanti.
Passo 4: Chiama la tua banca a modificare i dati della carta di credito (codice segreto, eccetera) se hai salvato la tua carta di credito per acquisti online o hai svolto attività online con la tua carta.
Passo 5: Assicurati che chiama il tuo ISP (Provider o operatore Internet) e chiedi loro di cambiare il tuo indirizzo IP.
Passo 6: Cambia il tuo Password Wi-Fi.
Passo 7: (Opzionale): Assicurati di scansionare tutti i dispositivi collegati alla tua rete alla ricerca di virus e ripeti questi passaggi per loro se sono interessati.
Passo 8: Installa anti-malware software con protezione in tempo reale su ogni dispositivo che hai.
Passo 9: Cerca di non scaricare software da siti di cui non sai nulla e stai alla larga siti web di bassa reputazione generalmente.
Se segui questi consigli, la tua rete e tutti i dispositivi diventeranno significativamente più sicuri contro qualsiasi minaccia o software invasivo delle informazioni e saranno privi di virus e protetti anche in futuro.
How Does VK Virus Work?
Una volta installato, VK Virus can raccogliere dati utilizzando tracker. Questi dati riguardano le tue abitudini di navigazione sul web, come i siti web che visiti e i termini di ricerca che utilizzi. Viene quindi utilizzato per indirizzarti con annunci pubblicitari o per vendere le tue informazioni a terzi.
VK Virus can also scaricare altro software dannoso sul tuo computer, come virus e spyware, che può essere utilizzato per rubare le tue informazioni personali e mostrare annunci rischiosi, che potrebbero reindirizzare a siti di virus o truffe.
Is VK Virus Malware?
La verità è che i PUP (adware, browser hijacker) non sono virus, ma potrebbe essere altrettanto pericoloso poiché potrebbero mostrarti e reindirizzarti a siti Web di malware e pagine di truffe.
Molti esperti di sicurezza classificano i programmi potenzialmente indesiderati come malware. Ciò è dovuto agli effetti indesiderati che i PUP possono causare, come la visualizzazione di annunci intrusivi e la raccolta di dati dell'utente senza la conoscenza o il consenso dell'utente.
Informazioni sulla ricerca sul virus VK
I contenuti che pubblichiamo su SensorsTechForum.com, questa guida alla rimozione di VK Virus inclusa, è il risultato di ricerche approfondite, duro lavoro e la dedizione del nostro team per aiutarti a rimuovere lo specifico, problema relativo all'adware, e ripristinare il browser e il sistema informatico.
Come abbiamo condotto la ricerca su VK Virus?
Si prega di notare che la nostra ricerca si basa su un'indagine indipendente. Siamo in contatto con ricercatori di sicurezza indipendenti, grazie al quale riceviamo aggiornamenti quotidiani sugli ultimi malware, adware, e definizioni di browser hijacker.
Inoltre, the research behind the VK Virus threat is backed with VirusTotal.
Per comprendere meglio questa minaccia online, si prega di fare riferimento ai seguenti articoli che forniscono dettagli informati.


