Aqui você vai encontrar pessoas como o ransomware cryptovirus BitPaymer haviam forçado em algumas partes do Alasca, EUA para voltar a usar máquinas de escrever. Isso se deve ao comprometimento dos sistemas de computador com o referido criptovírus e como tática de prevenção, para impedir que o malware se espalhe ainda mais. Mais que 200 vítimas foram atingidas com BitPaymer desde que saiu, embora a maioria deles tenha acontecido nas últimas semanas.
Origem do ataque cibernético BitPaymer no Alasca
Em 24 de julho, um vírus de computador atingiu o Área Metropolitana de Anchorage no Alasca, EUA e mais especificamente, a Matanuska-Susitna (Mat-Su) bairro. No início, apenas os servidores estavam sendo desconectados uns dos outros, mas logo telefones, e-mail e o acesso à Internet do Bairro Mat-Su seguido. Ontem, no dia 30 de julho, funcionários do município confirmaram que ainda estão recuperando a maioria de seus sistemas de TI que foram comprometidos. A infraestrutura ainda está sendo reconstruída lentamente.
Semana passada, A diretora de relações públicas Patty Sullivan afirmou:
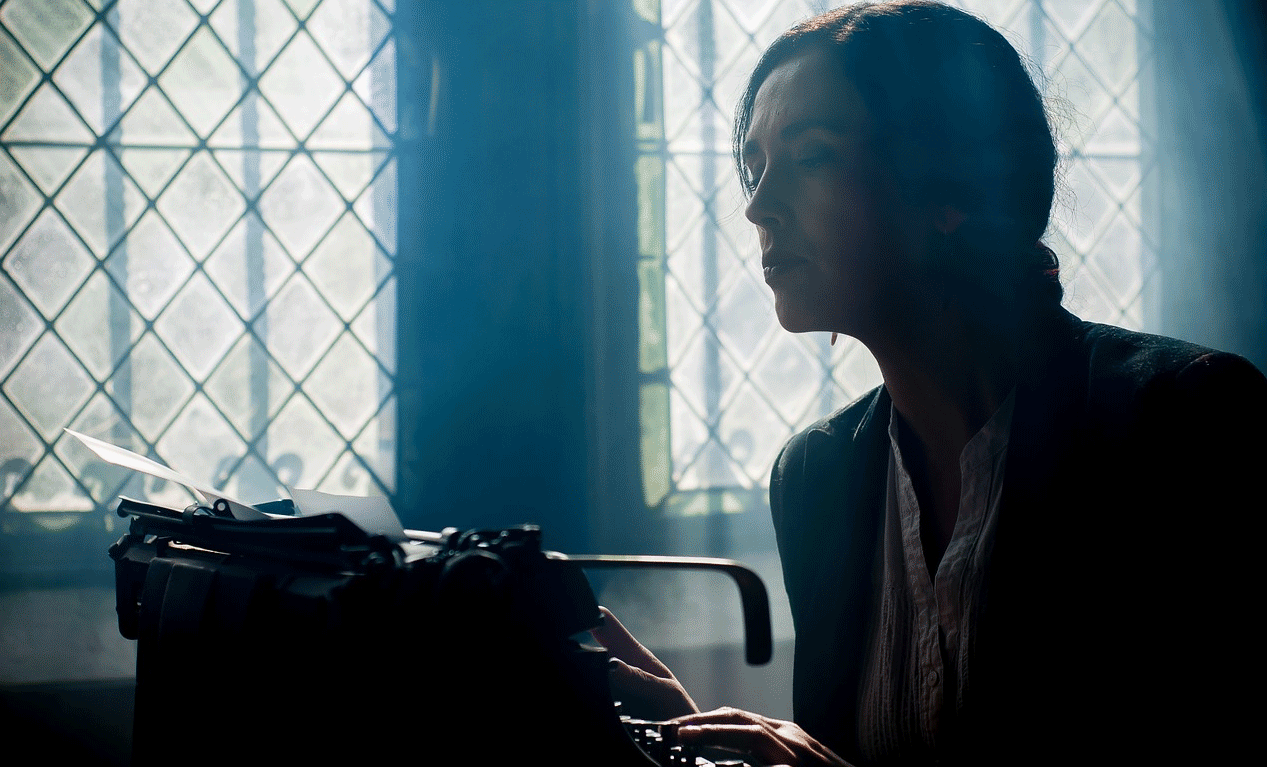
“Sem computadores e arquivos, Os funcionários do município agiram com desenvoltura… Eles re-alistaram máquinas de escrever de armários, e escrevi recibos à mão e listas de usuários de livros da biblioteca e taxas de aterros sanitários em alguns dos 73 edifícios diferentes.”
o Diretor de TI do município de Matanuska-Susitna, Eric Wyatt encontrou-se com FBI agentes na semana passada para isolar e identificar o vírus e reunir informações que possam ajudar o FBI na identificação dos cibercriminosos por trás da ameaça e prosseguir com o processo.
Wyatt disse o seguinte sobre o vírus:
“Uma multifacetada, ataque multi-vetor... não um único vírus, mas vários aspectos de vírus juntos, incluindo cavalo de tróia, Cryptolocker, bomba relógio, e interruptor de homem morto. Isso é muito insidioso, ataque muito bem organizado... não é uma criança no porão de sua mãe.”
Ontem, uma relatório em PDF foi publicado com o Diretor de TI identificando o criptovírus como o BitPaymer Ransomware.
No relatório, Eric Wyatt compartilhou o seguinte:
“Este ataque parece estar adormecido e/ou não descoberto em nossa rede desde 3 de maio”
O software antivírus começou a detectar o troiano parte de BitPaymer ransomware a partir de 17 de julho.
Repercussões após adulteração do BitPaymer
senhas foram alterados com força pelos superiores de TI, alguns dias depois, para recuperar algum acesso e privilégios de administrador para sistemas. Tentando excluir partes do vírus com um script feito manualmente havia acionado o Componente do Crypto Locker do pacote de malware. Eric Wyatt adicionou:
“Esse gatilho pode ter sido automatizado, uma Interruptor do Homem Morto, ou pode ter havido uma pessoa monitorando manualmente a atividade e executado seu Comando e controle (C2) para lançar o ataque”.
O resultado foi devastador tão perto quanto 500 estações de trabalho Mat-Su e 120 fora de 150 Servidores Mat-Su' criptografia seguida. A rede foi desconectada por Wyatt, a FBI foi notificado prontamente e a operação de reconstrução foi iniciada. Felizmente, alguns backups permaneceu inalterado e os dados parciais foram recuperados com sucesso desde.
Wyatt também revelou que a cidade de Valdez, Alasca também sofreu um ataque semelhante, que parece ser um Infecção BitPaymer também. Em julho 28, Valdez autoridades da cidade confirmaram em um oficial Facebook declaração de que estão lidando com um vírus de computador.
Por aí 650 computadores desktop e servidores localizados na Matanuska-Susitna rede parece estar comprometida pelo criptovírus e diz-se que foi apagada e reinstalada. Da semana passada, incluindo um fim de semana agitado, 110 os PCs das estações de trabalho dos funcionários foram limpos e considerados prontos para o trabalho com a ajuda de 20 diferentes agências e fornecedores do setor privado. A reconstrução do Mat-Su infra-estrutura de TI governamental ainda está em obras, para começar, o servidor do telefone foi reconstruído no domingo à noite.
Dados do cartão de pagamento foi considerado seguro por ser armazenado por provedores de terceiros em vez de nos servidores do Mat-Su Borough. Interessantemente suficiente, o sistema de furto do cartão da fechadura da porta do município havia sido criptografado, mas ainda funcionando e o oficial Site Matanuska-Susitna não foi comprometido. A página do Facebook de Mat-Su serviu como um meio de informação para o público, manter as pessoas atualizadas com as notícias sobre o incidente e o progresso atual da recuperação.
Alasca deve ser capaz de recuperar o seu ISTO sistemas ao normal nos próximos dias ou semanas, considerando que mais componentes residuais ou sistemas infectados são encontrados.