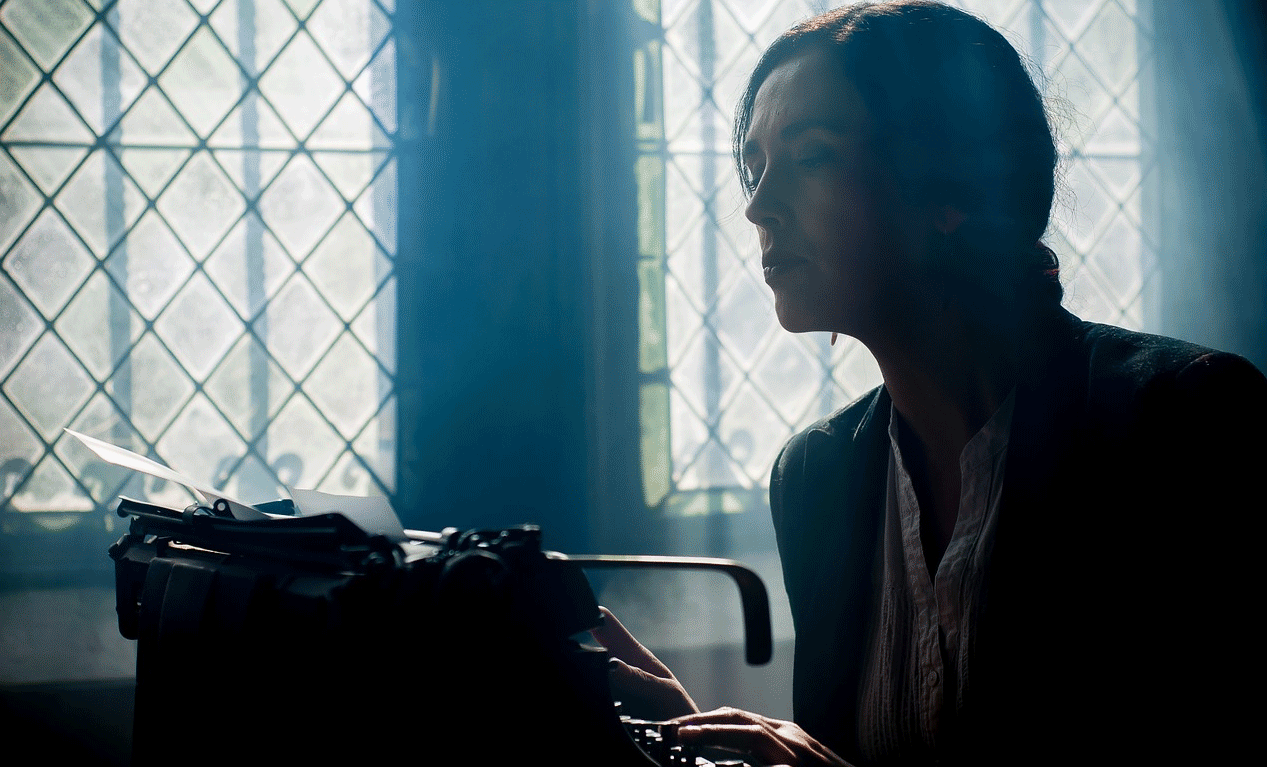
Here you will find out how the BitPaymer ransomware cryptovirus had forced people in some parts of Alaska, USA to go back to using typewriters. That is due to the computer systems getting compromised with said cryptovirus and as a prevention tactic, in order to stop the malware from spreading further. More than 200 victims had been struck with BitPaymer since it has come out, although most of them have happened within the last few weeks.
Origin of the BitPaymer Cyberattack in Alaska
On July 24th, a computer virus has hit the Anchorage Metropolitan Area in Alaska, USA and more specifically, the Matanuska-Susitna (Mat-Su) borough. At first only servers were being disconnected from each other, but soon phones, e-mail and the Internet access of the Mat-Su borough followed. Yesterday, on the 30th of July, borough officials have confirmed that they are still recovering most of their IT systems that have been compromised. The infrastructure is still slowly being rebuilt.
Last week, Public Affairs Director Patty Sullivan stated:
“Without computers and files, Borough employees acted resourcefully… They re-enlisted typewriters from closets, and wrote by hand receipts and lists of library book patrons and landfill fees at some of the 73 different buildings.”
The IT Director of Matanuska-Susitna borough Eric Wyatt met with FBI agents last week to isolate and identify the virus and gather intelligence that could help the FBI in identifying the cybercriminals behind the threat and proceed with their prosecution.
Wyatt said the following regarding the virus:
“A multi-pronged, multi-vectored attack… not a single virus but multiple aspects of viruses together including trojan horse, Cryptolocker, time bomb, and dead man’s switch. This is a very insidious, very well-organized attack… it’s not a kid in his mom’s basement.”
Yesterday, a PDF report was published with the IT Director identifying the cryptovirus as the BitPaymer Ransomware.
In the report, Eric Wyatt shared the following:
“This attack appears to have been lying dormant and/or undiscovered within our network since as early as May 3rd”
The anti-virus software had started detecting the trojan part of the BitPaymer ransomware from July 17th.
Repercussions After Tampering With BitPaymer
Passwords were changed forcefully by IT higher-ups, a few days later, to re-gain some access and admin privileges to systems. Trying to delete parts of the virus with a manually-made script had triggered the Crypto Locker component of the malware package. Eric Wyatt added:
“This trigger may have been automated, a Dead Man’s Switch, or there may have been a person manually monitoring activity and executed their Command and Control (C2) to launch the attack.”
The result was devastating as close as 500 Mat-Su desktop workstations and 120 out of 150 Mat-Su servers’ encryption followed. The network had been brought offline by Wyatt, the FBI had been notified promptly and the rebuilding operation had been set in motion. Luckily, some backups had remained unaffected and partial data has been successfully recovered since.
Wyatt also revealed that the city of Valdez, Alaska had also experienced a similar attack, which looks like to be a BitPaymer infection as well. On July 28, Valdez city officials confirmed in an official Facebook statement that they are dealing with a computer virus.
Around 650 desktop computers and servers located on the Matanuska-Susitna network seem to be compromised by the cryptovirus and are said to be wiped and reinstalled. From last week, including a busy weekend, 110 employee workstation PCs have been cleaned and deemed ready for work with the help of 20 different agencies and vendors from the private sector. The reconstruction of the Mat-Su governmental IT infrastructure is still in the works, as for a start the phone server has been rebuilt at Sunday night.
Payment card data was considered safe due to it being stored by third-party providers instead of on servers of the Mat-Su Borough. Interestingly enough, the borough’s door lock card swipe system had been encrypted, but still working and the official Matanuska-Susitna website was not compromised. The Facebook page of Mat-Su served as an information outlet to the public, keeping people up-to-date with news surrounding the incident and current recovery progress.
Alaska should be able to recover its IT systems to normal within the next few days or weeks, considering more residual components or infected systems are found.