A intensidade de ataques maliciosos que aplicaram kits de exploração (EK) aumentou nos últimos dois anos. De fato, dando uma olhada no terceiro trimestre de 2015, notará de imediato que a exploração de kits de exploração aumentou aparentemente. Como muitos pesquisadores apontaram, a queda do infame Blackhole EK em outubro 2013 trouxe outros kits de exploração à luz.
Exploit Kits Threat Landscape
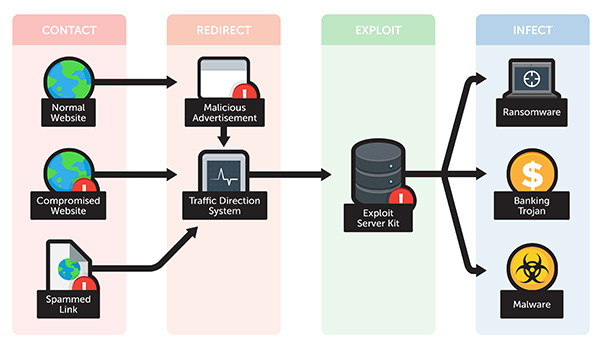
Os kits de exploração são normalmente usados em operações maliciosas conhecidas como downloads drive-by. Assim que esse download ocorrer, o usuário é redirecionado para o site de um invasor que hospeda um EK.
O crescimento em intensidade e eficácia dos ataques EK se deve à criação bem-sucedida de infraestrutura DNS criminosa. Este último saltou para 75% no último trimestre de 2015, em comparação com o terceiro trimestre de 2014. As estatísticas fazem parte de uma vasta pesquisa de Infoblox.
Por que devemos nos importar? Os kits de exploração são malware que representam ataques automatizados e devem ser uma grande preocupação para geeks de segurança e usuários. Os kits de exploração são definitivamente criados por criminosos cibernéticos com habilidades sofisticadas. Eles podem ser descritos como pacotes para entrega de uma determinada carga útil (por exemplo ransomware) que estão à venda ou aluguel. A forma como os diferentes tipos de software malicioso estão sendo distribuídos em fóruns clandestinos (malwares-as-a-service) é bastante alarmante. Praticamente, qualquer cibercriminoso, mesmo aqueles com pouco conhecimento técnico, pode ir atrás de indivíduos, empresas e organizações públicas.
A maior parte da atividade EK é rastreada até quatro peças de exploit bem conhecidas:
- Angler Exploit Kit;
- Magnitude EK;
- Neutrino EK;
- Nuclear EK.
Os quatro foram usados em 96% de todas as atividades do kit de exploração nos últimos três meses de 2015.
Angler Exploit Kit
A pesquisa indica que o Angler apareceu pela primeira vez no horizonte do malware no final de 2013. Desde a sua primeira aparição, Angler cresceu em popularidade e maldade. É considerado um dos kits de exploração mais agressivos que foge da detecção com sucesso e tem vários componentes. É com certeza uma das ferramentas de exploração mais prevalentes lá fora. Por exemplo, pesquisadores da Sophos relataram um grande número de páginas de destino infectadas com o Angler na primavera de 2015.
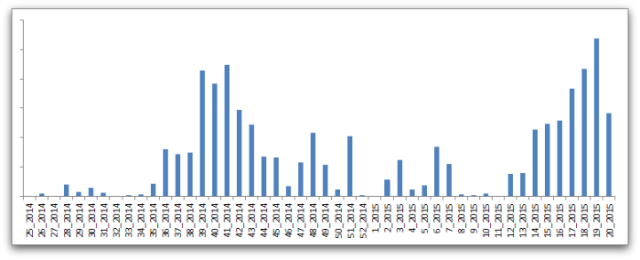
Aqui está um gráfico que representa a atividade do Angler nos últimos anos:
Leia mais sobre o Angler EK:
Explorar:HTML / Axpergle.N - Componente Angler Exploit Kit
Centenas de domínios GoDaddy expostos ao pescador
Magnitude EK
O pacote de exploit magnitude tornou-se famoso em outubro 2013 quando foi aplicado em um ataque a visitantes do PHP.net. Tipicamente, os visitantes foram redirecionados para o kit com a ajuda de um arquivo JavaScript comprometido. Mais tarde, Magnitude ganhou as manchetes mais uma vez quando se tornou público que foi usado em um ataque de malvertising ao Yahoo. Os criminosos compraram espaço publicitário no Yahoo e, em seguida, usaram os anúncios para vincular os visitantes a domínios maliciosos que hospedam o Magnitude. O kit é conhecido por explorar vulnerabilidades em Java e Flash.
Leia mais sobre Magnitude EK:
CryptoWall e Magnitude EK
Neutrino EK
Neutrino foi relatado recentemente para atacar sites usando a plataforma de comércio Magento do eBay. O Google bloqueou milhares de sites (mais que 8000) que foram associados ao ataque de Neutrino. Os pesquisadores alertam que os usuários que executam vulneráveis, versões não corrigidas do Flash podem se tornar vítimas ao serem infectadas com a carga maliciosa do Neutrino. As cargas úteis do ataque são provavelmente malware Andromeda e Gamarue.
Leia mais sobre malware relacionado a Neutrino:
Remover BKDR_KASIDET.FD a.k.a. Backdoor.Neutrino
Nuclear EK
O pacote nuclear é definido como um dos kits de exploração mais amplamente difundidos que apareceu pela primeira vez em 2009. O kit é bastante eficaz, ser capaz de realizar uma série de atividades maliciosas, como Flash, luz cinza, PDF, e explorações do Internet Explorer, para eliminar cargas de malware avançado e ransomware.
Leia mais sobre Nuclear EK:
Crowti Ransomware distribuído via EKs
Os kits de exploração podem trazer uma variedade de ameaças
Por causa de seu caráter multifacetado, EKs são frequentemente usados como um veículo para realizar ataques de dia zero e tirar proveito de vulnerabilidades de software. Eles também são frequentemente usados em operações de exfiltração de dados. Muitas empresas foram afetadas não apenas pelos EKs listados neste artigo, mas por muitos outros.
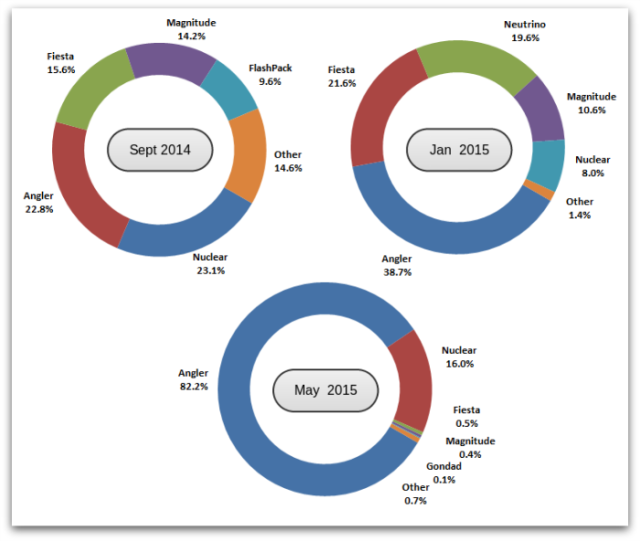
image Source: Sophos
Como se manter protegido contra Exploit Kits
O que todos devem ter em mente é que a maioria dos ataques EK são iniciados por meio de campanhas de e-mail de spam e sites comprometidos. Eles também podem ser incorporados em anúncios online. Milhões de usuários podem se tornar vítimas de EKs, crimeware e suas cargas maliciosas. A questão é como ficar protegido contra eles.
Estar protegido contra ataques de exploração definitivamente requer o conjunto certo de ferramentas e conhecimentos. Patches regulares são extremamente necessários, começar com. A proteção de endpoint com um gerenciamento de patch integrado é uma obrigação para as organizações. A boa notícia é que mesmo exploits projetados para evitar a detecção de AV podem ser anulados quando os sistemas visados são completamente corrigidos.