O botnet Necurs está sendo usado em uma nova campanha de ataque que concentra bancos em todo o mundo. Os relatórios de segurança mais recentes indicam que os invasores utilizam arquivos .PUB, que são documentos do Microsoft Publisher. Leia nosso artigo para saber mais sobre os incidentes.
Necurs Botnet usa arquivos .Pub para se infiltrar em bancos
Recebemos um relatório de segurança de uma nova campanha de infecção global utilizando o botnet Necurs. Os ataques em larga escala são contra bancos e usuários bancários com táticas avançadas de infiltração. Até agora temos informações sobre o ataque global que aconteceu em agosto 15 (ontem). Espera-se que o Necurs possa ser usado em futuros ataques quando os criminosos avaliarem quanto dano eles causaram durante o surto inicial.
O Necurs é especialmente adequado para este tipo de ataque, pois usa Algoritmos de Geração de Domínio (DGAs) e conexões diretas ponto a ponto, o que torna muito difícil o bloqueio pelos administradores de rede. Como tal, tem sido usado para espalhar a maioria dos ataques de ransomware Locky e Trojans como Dridex.
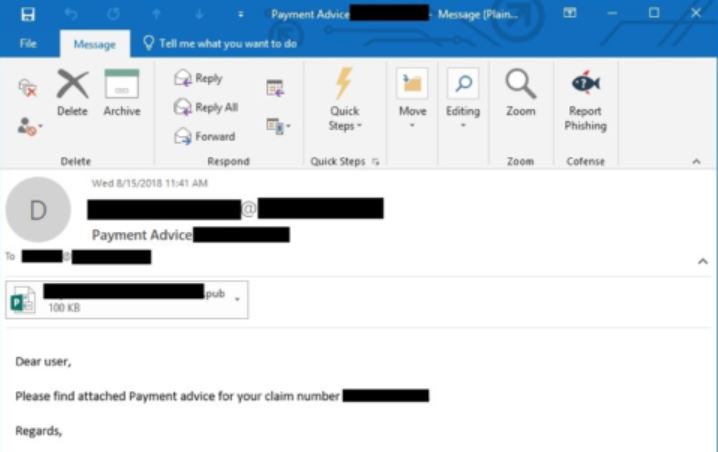
A última técnica usada por criminosos envolve phishing e-mails que envolvem o envio .BAR (Microsoft Publisher) arquivos. Os relatórios indicam um layout de mensagem típico, os destinatários receberão e-mails de endereços de origem indiana. Os assuntos podem incluir strings como “Solicitar BOI”, “Aviso de pagamento”, “Contratos” em combinação com caracteres alfanuméricos aleatórios. Se os usuários da vítima abrirem os arquivos infectados, uma série de macros maliciosas será ativada, baixando um malware de um site remoto. Em alguns casos, um prompt de notificação pode ser gerado, os usuários são aconselhados a não interagir com scripts recebidos por esses meios.
Assim que as macros forem iniciadas, o padrão de comportamento começará soltando um arquivo para a pasta onde o documento é salvo e um software de arquivamento também será entregue. Através do arquivo de conexão estabelecido, um arquivo protegido por senha é baixado e descompactado usando uma senha codificada. Os arquivos extraídos são renomeados como componentes do sistema e a infecção será iniciada por eles.
O objetivo final da infecção do Necurs Botnet é entregar um Trojan muito semelhante a um ataque anterior que utilizou .Arquivos IQY.
O Trojan usado no ataque aos arquivos .PUB é poderoso e personalizado contra bancos e usuários finais. Ele estabelece uma conexão segura constante entre o host infectado e um servidor controlado por hackers - isso efetivamente permite que os criminosos espionem as vítimas em tempo real, assumir o controle de suas máquinas e implantar outros vírus.
Muitas versões personalizadas incluem um módulo de colheita de dados que está configurado para sequestrar dois grupos de informações:
- Informação pessoal — Os dados coletados sobre os usuários podem ser usados para expor sua identidade. Isso é feito procurando por strings como seu nome, endereço, número de telefone, localização, interesses e senhas.
- campanha Metrics — Os hackers também são conhecidos por extrair informações que podem ser usadas para otimizar os ataques. Geralmente consistem em um relatório indicando os componentes de hardware instalados, opções definidas pelo usuário e determinados valores do sistema operacional.
Trojans como este também são conhecidos por alterações do Registro do Windows. Eles podem interromper a funcionalidade normal de aplicativos instalados pelo usuário e do sistema operacional como um todo. Algumas infecções podem ser detectadas por sintomas indiretos, como uma queda repentina no desempenho do sistema.
Os hackers podem instruir a carga perigosa para alterar o opções de inicialização — a ameaça pode ser configurada para iniciar automaticamente assim que o computador for iniciado. Ele também pode bloquear o acesso ao menu de recuperação de inicialização que renderiza muitas opções de remoção manual do usuário.
Analistas de segurança esperam que novas campanhas de ataque sejam lançadas em um curto período de tempo. Até esta data, não há informações sobre o hacker ou grupo criminoso por trás dos ataques em andamento.


