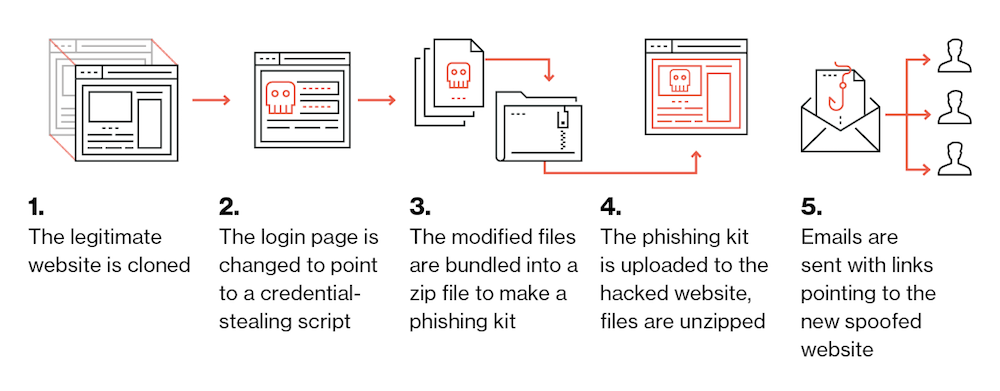
campanhas de phishing conduzir a maioria dos ataques maliciosos na natureza, e como se vê, cibercriminosos encontraram uma maneira eficiente de otimizar seu efeito. Um novo estudo revela que os invasores costumam reutilizar sites de phishing em vários hosts agrupando os recursos do site em um kit de phishing.
Os kits são então carregados para um host geralmente comprometido. Os arquivos do kit são extraídos, e e-mails de phishing são enviados para o novo site de phishing. O que é intrigante é que há casos em que os phishers deixam esses kits para trás, permitindo que os pesquisadores de segurança baixem e examinem-nos.
Pesquisadores Analisam 66,000 URLs e 7,800 Kits de Phishing
No relatório, Os pesquisadores de segurança do Duo examinaram 66,000 URLs e mais de 7,800 kits de phishing. Foi assim que eles encontraram dois kits que foram usados em mais de 30 anfitriões.
Outras descobertas incluem:
– Muitos kits de phishing foram projetados para contornar a detecção por meio do uso de arquivos .htacess e scripts PHP usados para bloquear conexões de empresas de inteligência de ameaças com base em recursos como os intervalos de endereço IP de origem, e o referenciador HTTP do cabeçalho do agente do usuário.
– Atacantes individuais de várias campanhas foram rastreados analisando cada kit de phishing para endereços de e-mail. Um ator cujo endereço de e-mail foi encontrado em mais de 115 kits de phishing únicos foram descobertos.
– Kits de phishing exclusivos em vários hosts foram rastreados. Muitos kits vistos em 30 diferentes hospedeiros foram encontrados, o que significa que os invasores lançaram várias campanhas de phishing usando o mesmo kit.
– Mais que 200 casos de kits de phishing backdoored foram divulgados. O que isto significa? Os autores do kit de phishing estão vendendo kits backdoored para outros invasores para que eles tenham acesso aos hosts comprometidos.
– Os kits de phishing estavam localizados principalmente em sites WordPress comprometidos, e em 16% dos casos, os kits foram encontrados em sites HTTPS.
– disse brevemente, a reutilização de kits de phishing melhora o ROI dessas campanhas, e também poupa os cibercriminosos do tempo de recriar vários ativos para cada nova campanha.
Para mais informações, pule para o Relatório completo.