A nova tática de hackers perigoso foi identificado como o ataque de phishing ZeroFont que é responsável por infecções causadas pelo Gabinete 365 manipulação. Isso é feito usando táticas de engenharia social que manipulam os usuários para interagir com documentos anexados contendo fontes de tamanho zero. Essa técnica provou ser bem-sucedida e está sendo aproveitada em um ataque contínuo contra alvos em todo o mundo.
Ataque de phishing ZeroFont aproveita o Office 365 contra usuários
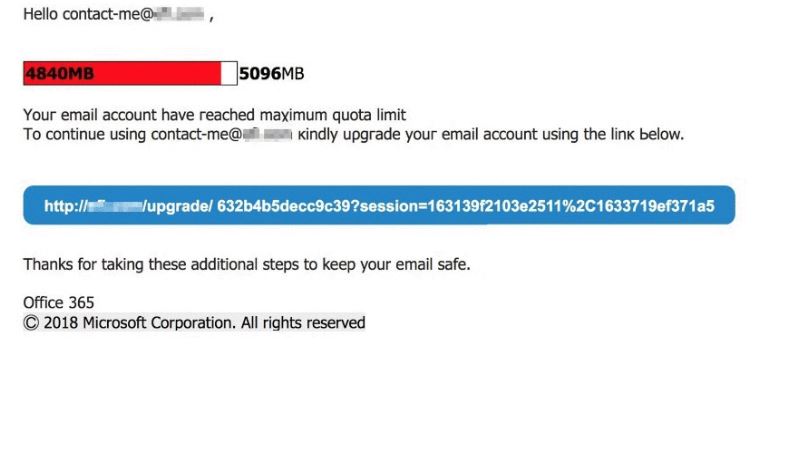
Os pesquisadores de segurança que revelaram informações sobre o ataque de phishing ZeroFont mostraram que o principal método de entrega são mensagens diretas que conseguiram enganar vários filtros anti-SPAM. Os destinatários recebem mensagens de e-mail que parecem notificações legítimas de serviços populares. Os hackers usam texto e gráficos tirados e projetam os e-mails usando os mesmos métodos. O ataque de phishing é marcado como único, pois usa um maneira inteiramente nova de enganar as pessoas para interagir com os elementos perigosos. Segundo os pesquisadores, uma das principais características é o uso do Office 365 como o serviço de nuvem. As etapas a seguir são feitas pelos operadores de hackers por trás da campanha:
- Os criminosos procuram orquestrar a campanha contra o Office 365 usuários de e-mail. Eles podem perfilá-los usando informações coletadas ou trabalhar em conjunto com grupos que possuem suas informações pessoais para criar mensagens personalizadas.
- As mensagens são enviadas para o Office 365 servidores e contornar os algoritmos da Microsoft usando um bypass de processamento de linguagem natural.
- Os usuários recebem mensagens em sua caixa de entrada que aparecem como notificações de segurança padrão.
O fato mais preocupante é que os hackers conseguiram descobrir uma maneira de contornar os filtros de SPAM da Microsoft. Isso é feito emulando os elementos de design de mensagens legítimas reais, como as marcas d'água, avisos de direitos autorais e etc. As mensagens são construídas para que possam se correlacionar com o remetente e os destinatários, bem como se encaixam em contextos que podem apresentar um problema real de cliente ou serviço. As amostras capturadas parecem personificar 365 notificações de limite de cota.
A razão pela qual os ataques são chamados “ZeroFont” é devido a uma nova técnica que utiliza conteúdo de fonte de tamanho zero. Cadeias de texto aleatórias são inseridas nas mensagens e programadas com um tamanho de fonte 0, isso é interpretado pelos servidores de e-mail e pelas interfaces gráficas do usuário da maneira correta. Essas strings de texto não são visíveis para os usuários. Ao mesmo tempo, o algoritmo lê o texto oculto e o sinaliza como conteúdo seguro que é entregue aos destinatários.
Consequências do ataque de phishing ZeroFont: Além do escritório 365
O ataque de phishing ZeroFont representa a mais recente abordagem inovadora que os hackers estão adotando para entregar mensagens falsificadas aos seus alvos prescritos. Uma fraqueza foi encontrada no algoritmo da Microsoft que lida com o processamento de linguagem natural por meio da modificação do tamanho da fonte de letras aleatórias. Divulgações públicas sobre essas vulnerabilidades de alto impacto são postadas por pesquisadores de segurança depois que a empresa aborda o problema.
O uso desta técnica pode ser direcionado a outros serviços de hospedagem de e-mail e software em nuvem. Os grupos criminosos podem usá-lo para ações maliciosas, como as seguintes:
- Implantação de Ransomware — Os hackers podem enviar vírus através de e-mails anexando-os diretamente como arquivos ou hiperlinkando-os no conteúdo do corpo.
- Malware Redirect — Essas mensagens de e-mail podem ser usadas para redirecionar as vítimas para sites controlados por hackers.
- Mensagens de SPAM — Superando as empresas de filtros de SPAM associadas, hackers e outras partes interessadas podem entregar mensagens personalizadas e não personalizadas para fins publicitários.
Neste ponto, não há informações sobre o número de arquivos afetados nem os hackers que estão aproveitando o ataque de phishing ZeroFont.


