 As criptografias e infecções por ransomware criaram um caos que vale a pena 18 milhões de USD. Esses tipos de ataques vêm de cavalos de Tróia com scripts pré-programados que criptografam os arquivos do usuário principalmente nos algoritmos de criptografia AES e RSA. As infecções por ransomware tornaram-se um grave perigo para usuários inexperientes que geralmente abrem anexos de email sem pensar cuidadosamente em sua legitimidade. A ameaça em si pode ser removida com um programa anti-malware específico, Contudo, os arquivos criptografados permanecem. Este é um tutorial para ajudar os usuários a descriptografar dados criptografados do RSA. Os métodos abaixo foram recomendados por especialistas e foram testados várias vezes por usuários com um bom resultado. No entanto, isso não garante que funcione para você.
As criptografias e infecções por ransomware criaram um caos que vale a pena 18 milhões de USD. Esses tipos de ataques vêm de cavalos de Tróia com scripts pré-programados que criptografam os arquivos do usuário principalmente nos algoritmos de criptografia AES e RSA. As infecções por ransomware tornaram-se um grave perigo para usuários inexperientes que geralmente abrem anexos de email sem pensar cuidadosamente em sua legitimidade. A ameaça em si pode ser removida com um programa anti-malware específico, Contudo, os arquivos criptografados permanecem. Este é um tutorial para ajudar os usuários a descriptografar dados criptografados do RSA. Os métodos abaixo foram recomendados por especialistas e foram testados várias vezes por usuários com um bom resultado. No entanto, isso não garante que funcione para você.

O que é o algoritmo de criptografia RSA?
O algoritmo de criptografia RSA é um tipo de linguagem que, nesse caso, altera o código normal do arquivo com uma chave exclusiva. Esta chave pode ser descriptografada através de software especial, mas requer uma máquina poderosa, pois é um processo caro. O algoritmo RSA foi empregado pelos vírus de ransomware mais tradicionais que causaram devastações maciças em escala global. CryptoWall Variantes(2.0, 3.0), Bitcrypt e outros. Neste tutorial, mostramos a você um possível método de descriptografar seus arquivos e restaurá-los ao estado de trabalho anterior, caso você não tenha backup no sistema operacional (OS). Após o tutorial, fornecemos instruções sobre como habilitar o histórico de arquivos do Windows para que você possa fazer backup dos arquivos para que você possa se proteger de ataques futuros. Não se apresse e faça tudo, desde as etapas abaixo, e tudo ficará bem para você.

Manual de remoção de Ransomware
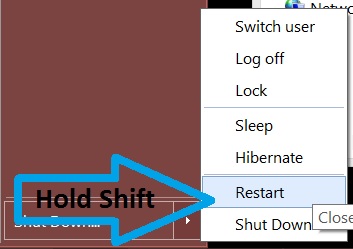
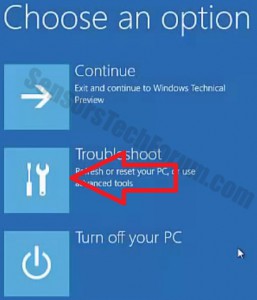
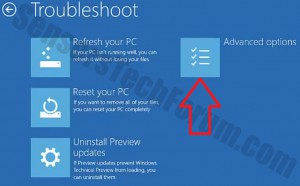
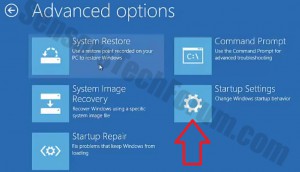
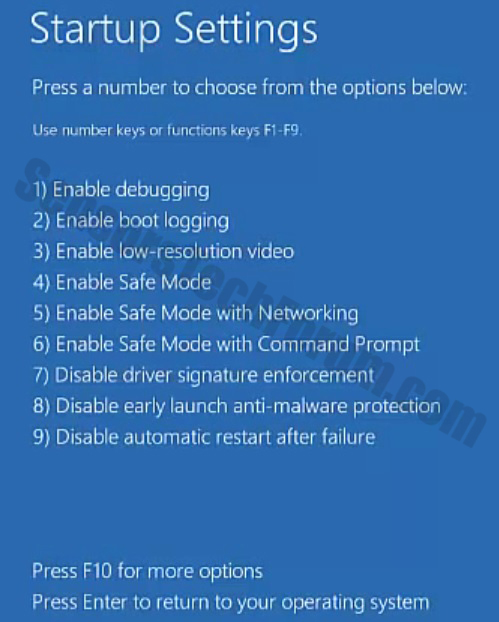
Antes de fazer isso, certifique-se de fazer backup de suas informações em um pendrive ou qualquer coisa dessa semelhança. Depois disso, certifique-se de baixar um software anti-malware respeitável que irá detectar algo fora do comum e ajudá-lo com a remoção da ameaça. Faça o download para um PC seguro, coloque-o no seu e inicialize o computador no Modo de Segurança on-line do Windows usando o seguinte manual:

Restauração de arquivos Ransomware
Para este tutorial em particular, nós usamos arquivos de extensão .bitcrypt, criptografado por ransomware, chamado Bitcrypt. Também usamos a versão Ubuntu 14.04 que nos ajudou a usar software especial apropriado para esta distribuição. Você pode obtê-lo na página de download do site deles e pode:
-Instale-o junto com o sistema operacional, inicializando uma unidade USB ativa.
-Instale-o em uma unidade virtual (Recomendado).
Aqui temos breves tutoriais para ambos:
Instalação do Ubuntu na sua máquina:
Passo 1: Obtenha uma unidade flash USB com mais de 2 GB de espaço.
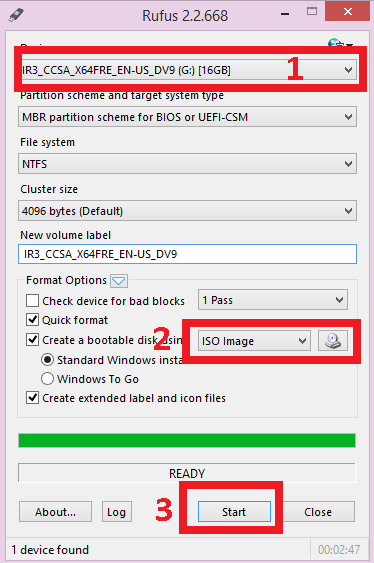
Passo 2: Faça o download do software gratuito, chamado Rufus e instale-o no seu Windows.
Etapa 3: Configure o Rufus escolhendo NTFS como um sistema e selecionando a unidade USB como a ser criada como um USB inicializável. Depois disso, inicialize a imagem do Linux a partir do seguinte botão:
Certifique-se de localizá-lo e selecione-o de onde você o baixou.
Passo 4: Depois que a unidade flash estiver pronta, reinicie o computador, e deve executar a instalação do Ubuntu. Se isso não acontecer, você deve ir ao menu do BIOS pressionando a tecla de atalho do BIOS na inicialização do seu PC (Geralmente é F1) e, a partir daí, selecione a primeira opção de inicialização como a unidade inicializável USB ou CD / DVD, caso você tenha queimado o Ubuntu em tal.
Instalação do Ubuntu no seu disco virtual
Para esta instalação, você precisa baixar o VMware Workstation de seus página de download ou qualquer outro programa de Gerenciamento de Unidade Virtual. Depois de instalado, você deve:
Passo 1: Crie uma nova unidade virtual.
Passo 2: Defina o tamanho da unidade. Verifique se você tem um mínimo de 20 gigabytes de espaço livre para o Ubuntu no seu computador. Escolha também "Executar como uma única unidade".
Degrau 3: Selecione a imagem ISO. Para esta opção, você deve saber onde é.
Degrau 4: Depois disso, jogue a Máquina Virtual e ela será instalada automaticamente.
descriptografia arquivo
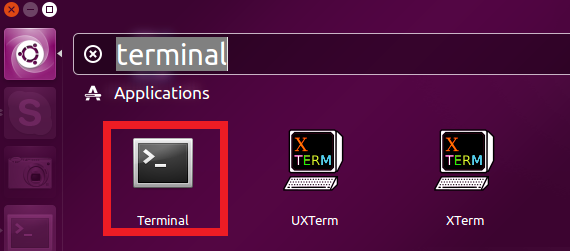
Depois de ter o Ubuntu ou qualquer outra distribuição Linux no seu computador, abra o terminal fazendo o seguinte:
Atualize seu Linux e instale uma versão maior que o Python 3.2 digitando o seguinte no terminal:
→sudo apt-get update
sudo apt-get install python3.2
Além disso, se o seu Linux não tiver sqlite3 módulo, instale-o digitando:
→sudo apt-get install sqlite3 libsqlite3-dev
sudo gem instala o sqlite3-ruby
Agora, depois de instalar o Python, precisamos baixar um script criado por 2014 Defesa da Airbus e segurança cibernética espacial. Para fazer isso, clique neste ligação. Faça o download do arquivo em sua ‘Página inicial’ pasta depois que você perguntar onde salvá-lo. Mantenha isso como decrypt.py, caso não seja salvo neste formato.
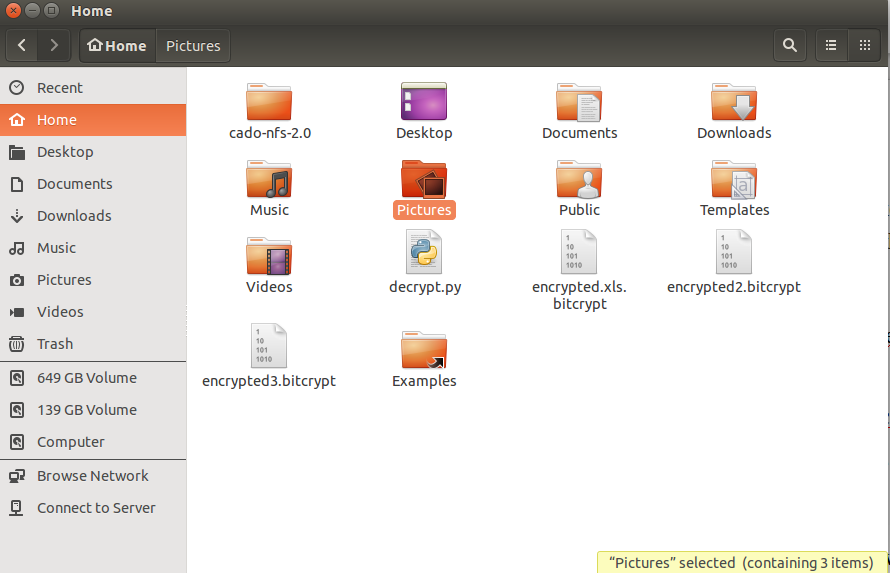
Agora que temos o Python e o script, é hora de descobrir a chave do arquivo criptografado .bytrcypt. Para fazer isso, mova seus arquivos criptografados da pasta pessoal usando o gerenciador de arquivos:
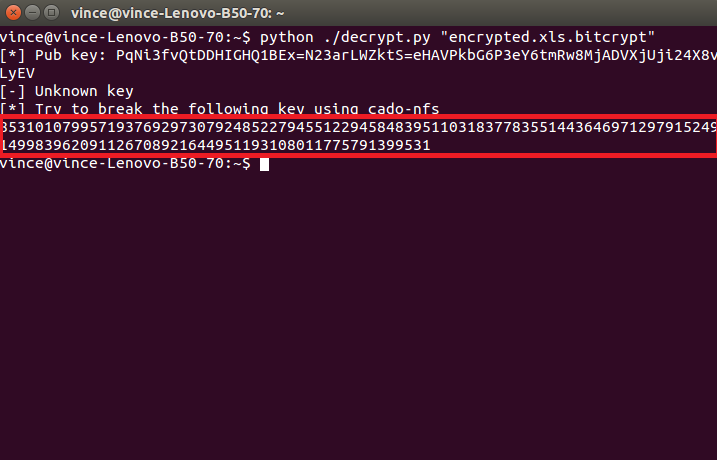
Depois de localizar todos os arquivos criptografados, juntamente com o arquivo “decrypt.py”, digite o seguinte no terminal para iniciar o script:
→python ./decrypt.py “Your_Encrypted_Document_Name_and_Format”
Isso mostrará um erro, e isso é totalmente normal, desde que você veja esse código:
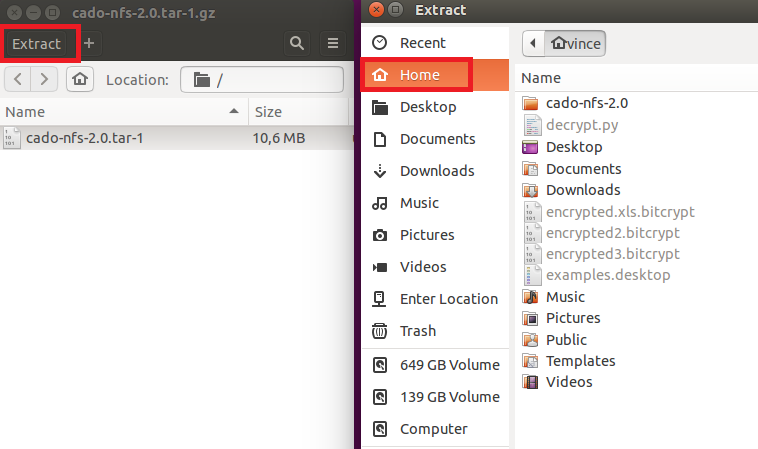
Este é o código RSA para este arquivo. Agora, precisamos decifrá-lo, e estamos no meio do caminho. Para fazer isso, baixe um programa chamado cado-nfs2.0.tar.gz do diretório página de download aqui. Recomendamos o 2.0 versão. Contudo, a versão mais recente também está em um bom nível.
Ele fará o download de um arquivo .tar (.arquivos tar são muito semelhantes aos arquivos .rar ou .zip). Simplesmente abra-o e clique no botão Extrair na parte superior e escolha o ‘Início’ pasta. Deve ficar assim:
Após o, temos todos os arquivos extraídos no ‘Home’ pasta, precisamos compilar cado-nfs. Para fazer isso, abra outro terminal e digite:
→cd cado-nfs-2.0
faço
Depois que isso estiver definido, é hora de executar o cracker de chaves. Importante - esse processo pode levar de várias horas a dias para ser concluído. Para iniciar o processo, digite seu terminal cd cado-nfs:
→./factor.sh YOUR_UNIQUE_KEY_WHICH_IS_LETTERS_OR_NUMBERS_HERE -s 4 -t 6
Após a conclusão do processo, você deve ver o seguinte:
→informações:Fatoração Completa: CPU total / tempo real para tudo: hhhh / dddd
LongNumber1 LongNumber2
Depois de termos a chave descriptografada, precisamos inserir no script "decrypt.py". Faça isso abrindo decrypt.py em um editor de texto e localizando essa parte dele:
→known_keys = { muitos números longos }
Precisamos adicionar antes do segundo colchete (“}”) estas linhas:
A chave anterior, uma coluna, parênteses abertos, LongNumber1, Vírgula, LongNumber2, parênteses fechados. Deve ficar assim:
→A chave anterior:(LongNumber1, LongNumber2)
Esteja ciente de que você deve fazer isso apenas uma vez. Depois disso, é hora de decodificar os arquivos. Para fazer esse tipo:
→python ./decrypt.py “Your_Encrypted_Document.docx.bitcrypt”
A execução deste comando criará um arquivo chamado “Your_Encrypted_Document.docx.bitcrypt.CLEAR”
Apenas renomeie o arquivo removendo a extensão .clear e você estará pronto. Repita o processo para seus outros arquivos também. Mas lembre-se de que primeiro você deve descobrir as chaves iniciais para descriptografá-las. Você deve poder abri-los agora. Esperamos que isso funcione para você.

Conclusão
A melhor defesa contra ameaças de Ransomware é sempre o próprio usuário. É crucial saber quais arquivos você abre e se os locais desses arquivos são seguros ou não. No entanto, se você estiver em uma organização ou em algum lugar em que o computador esteja localizado em um ambiente público ou de trabalho, sempre abre a um ataque direto que é ainda mais perigoso. Um verdadeiro especialista dirá que o melhor computador é aquele que está desligado, porque pode ter as melhores defesas, mas quem comete os erros não é a máquina, é o homem. É por isso que você deve sempre manter conhecimento suficiente e criar um comportamento de uso do PC orientado à segurança.
digitalizador Spy Hunter só irá detectar a ameaça. Se você quiser a ameaça de ser removido automaticamente, você precisa comprar a versão completa da ferramenta anti-malware.Saiba Mais Sobre SpyHunter Anti-Malware Ferramenta / Como desinstalar o SpyHunter



Oi,
Eu tenho o mesmo problema. Meus arquivos também estão infectados pelo Cryptowall 3.0. E a extensão é ccc. Posso usar esse script python para descriptografar ? Existem outras soluções possíveis ?
muito thx a
Patrick