The 21st century – we are living in volatile times and with the emerging of newer and newer technologies, we are reaching data transfer speeds and power which is beyond our imagination. However, with power comes responsibility, because we are using this technology to store our important files. We are talking about family photos, important memories, secret files, and other data on which we heavily depend. This is where malware writers see a great opportunity for money making, designing file encryption malware or lock screen type of software to extort users.
Why The Need to Protect Your Files from Viruses?
This is a very good question, because it is dependable on so many factors. To answer it properly we must split the two types of data storing users:
Type 1: The average home user
The average user usually keeps important data on his computer, but also most of the users with some experience like to use external drives, cloud or file encryption, it really depends on the importance of the data.
It is a common practice for most users not to store their data in a paranoid way, especially in home PCs, because they either lack the knowledge or the data is not that important for them. Such computers may store data such as family photos, school projects, student research papers and other data.
If the files are lost, the impact may vary from a headache to a ruined semester of a student. The malware attacks here are primarily via massive spam campaigns that are publicly visible, instead of individually targeted intrusions.
Type 2: The business user
This type is a bit more advanced. Here we have people who are solely focused on keeping data solely to their discretion or the discretion of the organization. These type of users usually do not use home networks to connect their business machines.
The usage of a professional anti-malware software which includes firewalls, proxies, VPNs and even protection hardware (VPN boxes, several layers of firewalls) gives additional layer of protection.
Not only this, but these users are also staying constantly educated on how to use the web safely and what is the latest development in malware. However, on the other hand, this is the best case scenario.
Often we see business users who disregard security practices and even if they do not disregard them, they often tend to make a mistake sooner or later and get infected with malware. A wise man once said that a large percentage of data compromising in companies is due to human error, for example someone may say a password if he or she is drunk on a party. This is why with business users we mostly see targeted attacks, instead of massive ones.
Since data protection is crucial for all types of users, we at SensorsTechForum have decided to conduct research based on a voting poll and a bit of experience to establish how users tend to protect their important data nowadays. We have decided to provide users with the following options:
- File encryption on the PC.
- External drive storage.
- Cloud backup or storage.
- The data being hidden on the computer.
- The data being stored on another partition.
- The data being backed up using a local backup of the PC.
- Other.
Here are the results of the voting poll by approximately 200 users:
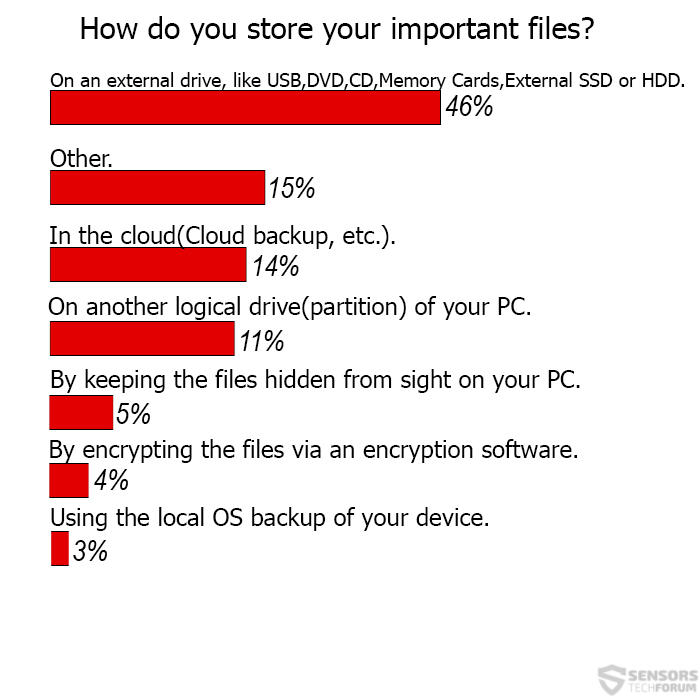
When we take a quick look, most users prefer to use simpler methods such as backing up their files online or using a USB flash stick or another external device to store their files. These methods are very suitable in some particular situations, but not all.
But we also see people who genuinely believe they are protected and store the data on their PC. We have managed to notice that almost nobody chooses to use the local OS backup provided by default, which is quite interesting.
The conclusion for the research is that people prefer simplicity when they are securing important files.
However, it is crucial to note that for different types of users, different file protection methods are appropriate. This is why we have decided to review all of them so that you can choose the appropriate one which will fit your needs.
What Are The Best Methods to Protect Your Files from Viruses?
Method 1: Keeping The Files On External Drives
This method is really “old school” and the word “old” from these two is a bit more appropriate. This is because of malware such as “USB Thief” being created specifically to steal information from computers and USB drives. Not only this, but such malware may make your flash drive a payload carrier, meaning that it can spread to other computers it has come across with.
Not only this, but advanced ransomware such as STOP/DJVU, Locky or TeslaCrypt variants may be configured to encrypt files that are located on other flash drives or partitions, which may be fatal if you insert your external drive in a ransomware-infected computer.
Furthermore, there may also be other risks with external drives, such as the possibility of them breaking with time. This is why, extreme attention on care should be taken, such as changing the external drive to a newer one, so that the files may remain in good health.
As a bottom line, we would recommend using this method only if you are a home user and keep your system secure and most importantly if you are using the flash drive rarely, meaning that it is appropriate for old files, photos etc.
Method 2: Storing the Data In The Cloud
With crypto-viruses on the rise, cloud backup has sure gained a lot of popularity nowadays. This is because some users do not tend to have the time to deal with flash drives, securing their PCs by buying anti-malware tools and other headaches.
The other reason for preferring cloud backup is that some cloud backup programs offer unlimited data storage, and this is very suitable for people with a lot of terabytes at their disposal.
However, you have to know that cloud backup also conceals certain risks, for example, an Infostealer Trojan, may steal your username and password and gain access to your files, so this “security bottleneck” is something that you should consider if you are using cloud backup.
There is also a risk of a keylogger being executed in an obfuscated manner which steals your credentials by collecting keystrokes.
As a final word for storing data in the cloud, we would say that it is appropriate for home and business users as long as you have enough trust with your data to the company storing it on their servers.
Method 3: By Encrypting the Files On Your Device Yourself
Data encryption software that hides the files on your computer in plain sight is a very clever way to store them. In fact, most government agencies use this method of storing secret files on their servers.
To encrypt the data of their files they use encryption algorithms that are very strong and classified as a Suite B category for top secret files. However, there are risks with that as well, because first, no code is perfect and an encryption software often generates a unique decryption key for the files.
With sufficient access, these “encryptors” can be exploited and the keys discovered. There are also other risks with encryption software, for example, the encrypted files may damage over time and become impossible to decrypt with their key.
So it is important to use software that has a strong algorithm and can not only encrypt your files but also give you other options, like APO Encryption Standard Edition which uses AES-256 cipher.
The bottom line is that we recommend file encryption to users who store extremely important data that is for their eyes only.
Method 4: Using the Local OS Backup of Your Device
Compared to the above-mentioned methods, this method is way less secure, and this may be one of the reasons only 3% of the voters prefer it. Local backup can be made to look like a joke in front of malware, especially on Windows systems.
Imagine the following scenario: You click on a malicious URL, believing it is sent to you by a via a message and you experience the so-called drive-by infection after which your computer has ransomware that encrypts your files with a strong RSA encryption algorithm.
Will you use your backup to restore them? Of course. But most malware writers know of such possibility, and this is why to ensure themselves that your files may temporarily be their property, they execute the following administrative command in Windows Command Prompt which deletes your backup:
→ vssadmin delete shadows /for={DrivePartition} [/oldest | /all | /shadow={Identification of the shadow copies}] [/quiet]
And suddenly, you have to pay ransom money in BitCoin to unlock your files. Of course, you may salvage a small percentage of the data using data restoration programs, like Stellar Windows Data Recovery, or Android Data Recovery Pro for mobile devices but few recovered files are the best case scenario. So we would recommend you not to use your local backup for data keeping.
Method 5: By Keeping the Files Hidden from Sight
This is the oldest trick in the book, and it will not protect your files from malware and from people who know how to find hidden files on your computer.
If you are going to take advantage of this method, we advise using it to hide data that is not so important for you, but you do not wish other users on the computer to see it and if you are going to hide files this way, we recommend using scrambled names so that people cannot discover it via filtered search.
Either way, this method is an extremely bad idea in most cases, and we advise it to people who like to live dangerously. In case you are hiding your files on your PC, we advise using a reputable antivirus software to protect them, the very least.
Method 6: On Another Logical Drive(Partition)
This option also makes sense if the files are not that important for you. It will keep you safe from malware which may corrupt your OS and make you reinstall it.
However, its effectiveness is relatively the same as hiding the files on the drive, because physically they are in the same drive. You can, however, lock your Partition using your own OS’s protection. For Windows it can happen by following these administrative actions:
1. Right-click on Your Partition and then Choose “Turn On BitLocker”.
2. Mark “Use a Password”, type your password, click “Next” and You are Done.
How to Protect Your Files from Viruses – The Bottom Line
The bottom line is that no protection method is 100 percent secure. This is most likely the reason some users chose the “Other” voting option. Sometimes, it is good to use a combination of several different data storing methods to increase the security of the files.
We have often heard of experts talking about keeping the data in more than one copies on different drives, so that if the files are lost, they have an instant backup. We have also used a USB encryption software which directly locks the USB drive, denying all access to it and encrypts the files in it, like APO Encryption Standard for USB, for example.
Either way, it is important to include the human factor, because it is the most important one. This is why, whichever methods you may choose, we advise you to stay updated on how to protect your information.
And for the more paranoid users we recommend reading security blocks and asking around in forums. Because, with today’s ever-changing world the methods of data theft are always changing and with that, also should our behavior towards technology usage in that sense.


