 CAPTHAs, or Completely Automated Public Turing test to tell Computers and Humans Apart, can be pretty annoying sometimes, but, in terms of online security, they are a necessary evil. Unfortunately, Google’s and Facebook’s CAPTCHA services have been broken down by three security researchers. Their work was recently presented during Black Hat Asia 2016.
CAPTHAs, or Completely Automated Public Turing test to tell Computers and Humans Apart, can be pretty annoying sometimes, but, in terms of online security, they are a necessary evil. Unfortunately, Google’s and Facebook’s CAPTCHA services have been broken down by three security researchers. Their work was recently presented during Black Hat Asia 2016.
Suphannee Sivakorn, Jason Polakis, and Angelos D. Keromytis managed to design an automated attack that can successfully break the CAPTCHA of Google and Facebook. In order to succeed, the expert trio applied various “tricks” to defeat the CAPTCHA services. They also used machine learning to figure out the right CAPTCHA answer. The precision they accomplished is at a higher level than previous attempts and studies.
The Defeat of ‘s and ‘s CAPTCHAs
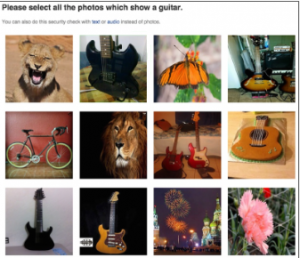
The researchers say that the reCaptcha service offered by Google, is the most widely used captcha service, and has been adopted by many popular websites for preventing automated bots from conducting nefarious activities.”
Google’s reCAPTCHA
They didn’t expect their experiment to be as successful as it turned out to be. While breaking down Google’s reCAPTCHA system, they recorded a success rate of 70.78 percent. As of the average CAPTCHA solving time, it was estimated at 19.2 seconds.
Facebook’s CAPTCHA system
The researchers got better results on Facebook’s CAPTCHA – a success rate of 83.5 percent on more than 200 CAPTCHAs. Why were they more successful with Facebook? The reason is quite simple and obvious – the social network uses images with a better resolution and displays objects from recognizable categories.
In comparison, Google’s images are with lower resolution, which are analogous to one another. This would make the automatic image classification more challenging.
Besides the technical part of attack on Google’s and Facebook’s CAPTCHAs, the researchers also took into consideration the financial needs to carry out such attacks. As it turns out, the automated attack is financially sounds – it would only cost cyber crooks $110 a day per IP address to break CAPTCHA codes.
What Did Facebook and Google Say?
Of course, the research team contacted Google and Facebook prior to going public with their discovery. Surprisingly, only Google responded and then took some measures to make their reCAPTCHA mechanism harder to break. Facebook hasn’t done anything to make their CAPTCHAs better yet.
This is what the team says:
We have disclosed a report with our findings and recommendations to Google, in an effort to assist them in making reCaptcha more robust to automated attacks. Following our disclosure, reCaptcha altered the safeguards and the risk analysis process to mitigate our large-scale token harvesting attacks. They also removed the solution flexibility and sample image from the image captcha for reducing the attack’s accuracy. We have also informed Facebook, but have not been notified of any changes. Overall, we hope that sharing our findings will help initiate the much-needed discussion between researchers and industry regarding the future of captchas.
Have a look at the original report.


