This article has been created in order to help you by explaining to you how to remove the Instagram Scam which can be encountered via email messages.
This article has been created in order to help you by explaining to you how to remove the Instagram Scam which can be encountered via email messages.
Our Instagram scam guide reveals all popular social engineering tactics that are used on the popular network. We reveal some of the top trending schemes that can both extract sensitive information from the victims or hijack their money — both real currency and cryptocurrency. Continue reading to learn how to protect yourself.

Threat Summary
| Name | Scam on Instagram |
| Type | Scam |
| Short Description | The Instagram scams aim to access sensitive data, money or cryptocurrency assets by using complex social engineering tricks. |
| Symptoms | Profiles or messages that offer various lucrative proposals to the targets. |
| Distribution Method | Instagram and other related mobile apps . |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
User Experience | Join Our Forum to Discuss Scam on Instagram. |

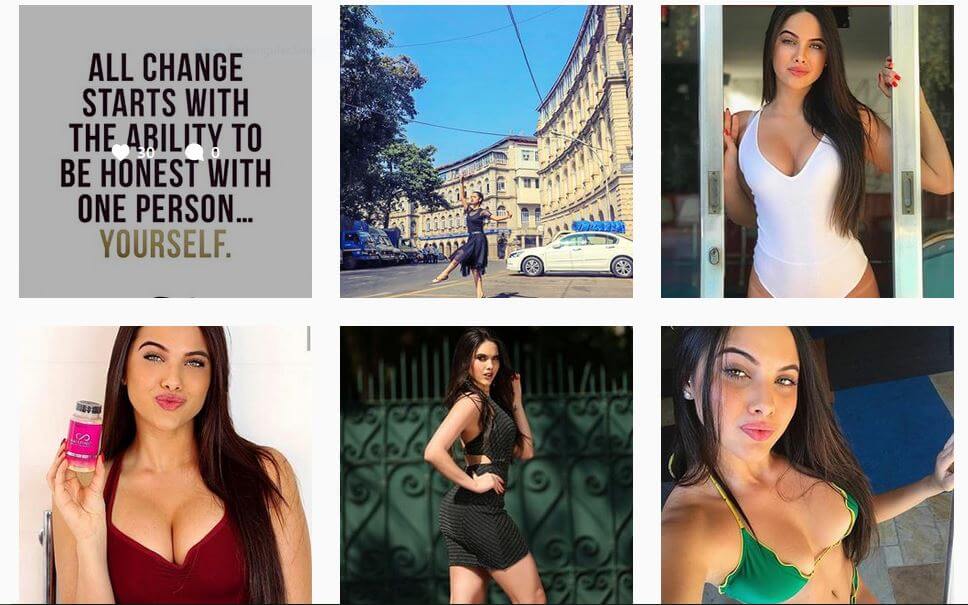
Instagram Scam #1 — The Modelling Job

A legitimate Instagram profile.
Credits to @stephanytattdevil
Instagram and other social media networks have created an entire new marketing platform that is heavily used by influencers and agencies to promote services and products. As a consequence social engineering scams proliferate across the platform. One of the most popular Instagram scams is known as the “Modelling Job” and it is mostly targeted to teenagers and college students. Hijacked profiles of models with many followers or fake copies usually message the targets and attempt to manipulate them by offering the job opportunities. The Instagram scammer profiles that are used by the criminals instruct the targets that they need to Skype either with them or their clients. The fake profiles can spam the recipients with many photos and videos as “proof” until they agree to do so. Once the Skype call is initiated the targets are manipulated into undressing while at the same time promising them that a lot of money is being sent to them. If the targets refuse to continue with this the scammers will blackmail them with threats of exposure.
WARNING!: The fake profiles can easily be confused with legitimate models!
This scam is especially dangerous as it includes several criminal elements: blackmail, sexual work and bullying. And while this is a common scheme in other social network platforms (especially on Facebook) in Instagram this has become one of the most common criminal activities. Partly one of the reasons why it is so successful is that the main target group is represented as the majority. The perpetrators of this scam can also easily scan their targets by assessing their emotional status through their posts and picking out the most likely victims in an easier way than other platforms.

Instagram Scam #2 — Donations Fund

This scam is taken from a classic phishing scheme that has its origins back to the first email scmas. Instagram scammers are sending users messages as strangers on the social network and ask them for donations. The reasons may be different:
- Rent & Bills
- Donations for a foundation
- Donations for medical interventions
- Food & Supplies
The scammers will request the target’s bank account in order to “transfer money”. A common strategy is to send fake checks for amounts over 500$ and ask for the the difference to be paid. However if this is done the fake check will bounce back and the victims will loose the funds and will be made to pay the associated bank fees. A dangerous fact that concerns this Instagram scam is that in connection with the scam operations a lot of private information is being requested.

Instagram Scam #3 — Cryptocurrency Theft

Cryptocurrency related scams are now becoming one of the most numerous blackmail tricks that are used by computer hackers today. The profiles send messages to the predefined targets and advertise the possibility of doubling their digital currency assets in 6 days by offering them “mining services” or “hacks”. All the targets need to do is send the hackers the coins “temporarily” or lend them the public-private key credentials to their wallets. In connection with this the Instagram scammer posts are usually shared on other social networks in order to boost the scam.
We have reviewed several examples using popular tags and found out that most of the scams are initiated through private messages (DMs). Details are provided to the targets with images and texts that are shown as “proof” of the fake successful enterprise.
This Instagram scam appears to primarily target beginner users that may not know that the promises cannot be completed in this manner. The hackers make use of the fact that a large part of the cryptocurrency communities are not actively moderated. This means that it can also infiltrate chat networks and messaging apps associated with the blockchain projects.

Instagram Scammer #4 — Purchase Offers
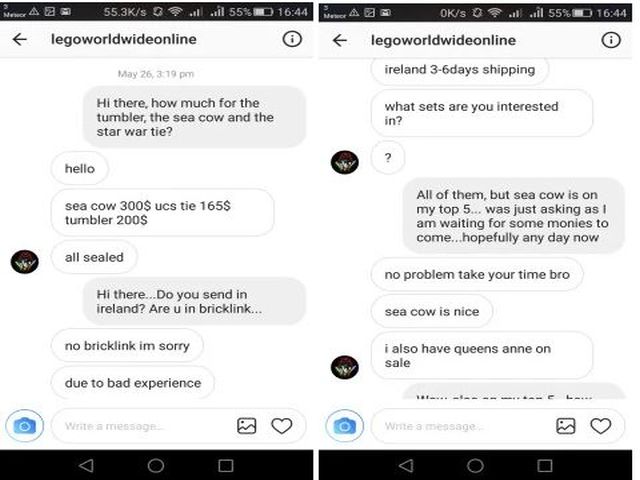
Advertising products for sale on Instagram is one of the preferred marketing tactics. However as much as it is used in legitimate sales and promotions the same tactics can be used for scams.
One such case was described on the Internet with an Instagram scammer profile that pretends to be the official LEGO store. A collector reached out to the criminals with the intention of buying sets from them and gives further details about the scam.
The profile has a name that reads just like an official profile of the company and follows accounts that are related both to the operations of LEGO and official fan pages. By interacting with various pages it has been able to gain a substantial amount of followers. The hackers behind the fake profiles have disabled user comments as a precaution — the victims can warn other users about the dangers in them.
The conversation with the seller reveals some concerning facts that can indicate that the seller is fake. One of the warning signs is the decline to use emails or any other form of communications besides Instagram. The payment is requested in advance via Western Union, respectively PayPal and other services that provide buyer’s protection are not accepted.

Instagram Scam #5 — Fake Escort Services
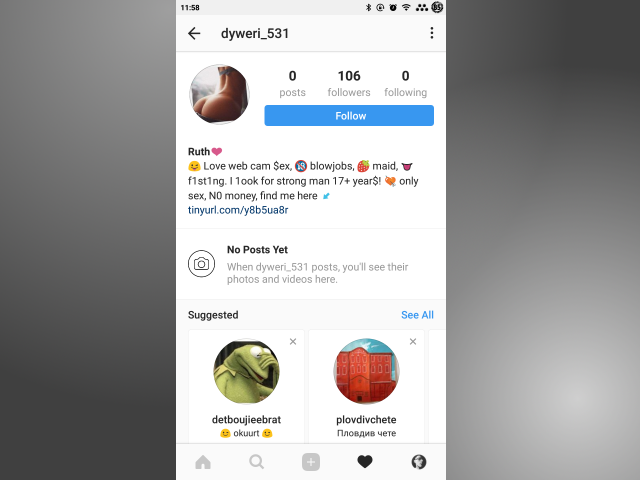
Instagram is a popular platform for meeting people and interacting with people with similar interests. Consequently it has also been used to post offers for escort or adult modeling work. One of the earliest scams that are identified in the platform are the fake escort posts and profiles. They are completely automated and usually have no posts and feature a one or two line profile description.
If they are followed or interacted with in any possible way they will send hyperlinks to fake adult sites that are described as cheap (or free) escort services or dating sites. Instead of posting photos with various tags the bots depend on another strategy — following users in an automated way. While this is among the most common scams on the social networks, users (especially newer to Instagram) can easily fall for this trap.

Instagram Scam #6 — Tinder Cross-Service Scam

A recent scam that has been revealed to be particularly active in the last few months. It facilitates the use of two of the most popular mobile apps — Tinder and Instagram. Fake profiles are created on both platforms used in combination to fool users into falling for their trap. The fake profile on the dating app is designed to look like an attractive webcam model. When a target users requests to contact her the hackers share proof that the shared visual content is not fake. This is one of the most complex scams as the criminals will need to provide high quality photos and possibly videos of attractive girls that cannot be found on the Internet along with professional profiles found on adult sites.
The profiles give details that they can meet in exchange for viewing a liveshow and voting for their performance. The targets are sent a link for a trial membership on an adult website. After the paid trial registration is complete the profile cannot be found on the platform.
This scam can be further customized for other similar scenarios such as the selling of adult content or personal items. It is possible that the photos and identities of the profiles are stolen as they appear to be completely legitimate.

Instagram Scam #7 — Phishing Tactics
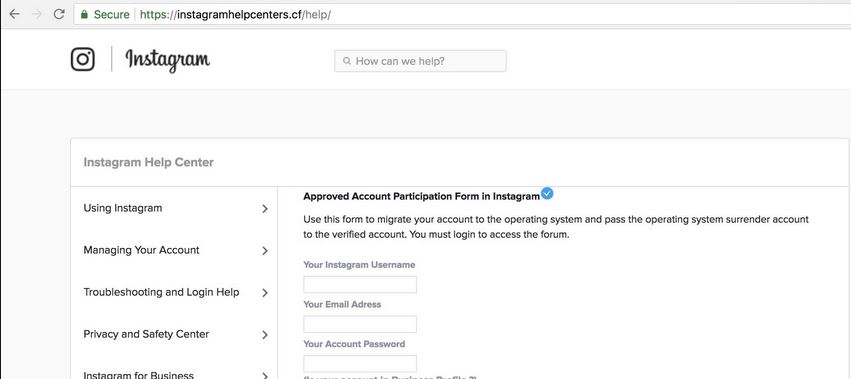
The computer criminals can use an alternative approach that is deemed effective in many cases. They set up pages that are reminiscent of setting pages, login prompts or other areas used by Instagram users. One of the newer examples of this practice is the spread of such pages on domains that may appear to the end users as used by the service.
The scams are assumed to be operated by experienced users as they have taken the web elements and web design layout from the service and implemented them in the phishing page. The captured sample pages in the security analysis reveal that these pages in particular contain hybrid content:
- Legitimate Content — The criminals include a help section that may hijack legitimate text and instructions from the official Instagram pages. They are laid out in a similar way to the actual company page which can confuse most users into interacting with the malicious elements.
- Phishing Content — In this particular scenario the hackers have embedded a login prompt into the phishing site. If entered the credentials will be sent automatically to the operators. As a result the criminals can take over control of the victim accounts.
The attack campaign utilizes an Instagram scam based around the concept of an account migration. The displayed text on the login prompt reads the following message:
Approved Account Participation Form in Instagram
Use this form to migrate your account to the operating system and pass the operating system surrender account to the verified account. You must login to access the forum.
This gives the users the assumption that the online service can allow them to migrate their accounts during an operating system reinstall. This is clearly a scam tactic as the social network is an online service that is not installed as a desktop application.
An additional measures is the inclusion of a Google Maps API which interacts with the stored cookies in the browsers. If the users are logged into their Google account they will see a profile photo of themselves. This trick is used in order to boost the purposed legitimacy.

Instagram Scam #8 — Instagram Bank Scam
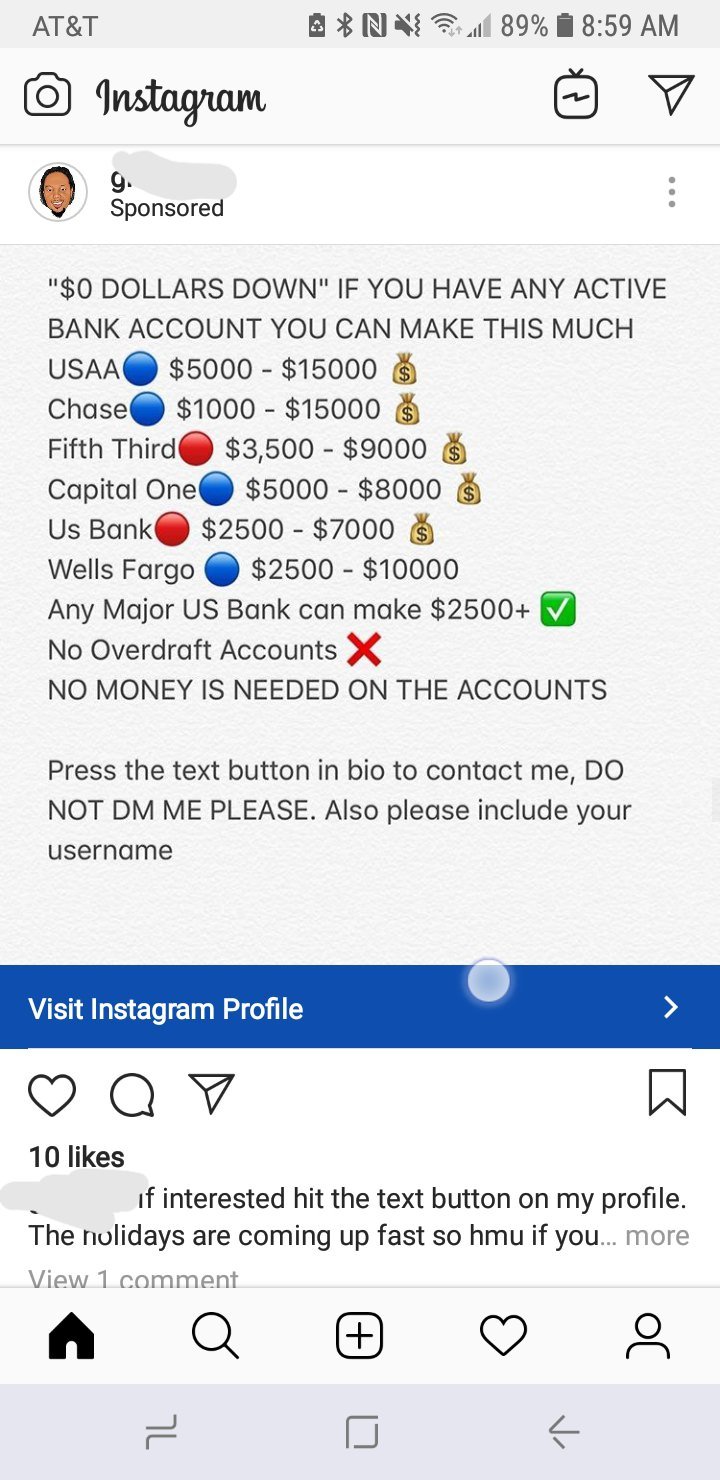
We have received several reports of a popular phishing tactic that makes use of sponsored messages — these are ad-based scams that are directly shown on the timelines when the users open up the application. The serious issue here is that Instagram have allowed the messages to be distributed without checking them for any apparent risks.
There are two possible hypotheses behind the appearance of the scam messages:
- Deliberate Distribution of Scam Messages — The users that have paid for the ads intentionally target Instagram users with the scam.
- Hacked Accounts — The other hypothesis is that the criminals are spreading the message through compromised accounts of ad agencies and users that have paid for promoted content.
The Instagram scam message itself will show a message that appears to come from an employee or partner of a financial institution. The users are coerced into contacting them through a text link. It is usually a shortened link that leads to a fake login screen or a scam landing page. Depending on the exact configuration the attackers will attempt to manipulate the victims into revealing various account credentials or to download virus software.

Instagram Scam #9 — Purchase Offers

Another popular scam is the one associated with clothing sales. Many merchants have set up their own shops and sell various items — from well-known brands to Chinese knock-offs. At this point the scam can take place. There are several popular options:
- Fake Brand Clothing — Selling counterfeit goods by pretending to be the official marketplace or an authorized reseller. They may use similar sounding profile names, design elements and content.
- Price Scams — The users will be displayed offers of clothing for a price that seems attractive. However the seller has ordered it for a substantially lower price and as a result the victims will be scammed for paying a high price for a cheap or knock-off item.
- Scam Items — In this particular case the victims will make a purchase and will not receive the bought item. Contacting the profile will not help as the accounts may be either disabled or hacked in the meantime.

Instagram Scams #10 — High-Profile & Influencers Accounts Theft
With the rise of marketing agencies and influencer accounts several scams surrounding them. Hijacking of such accounts is very dangerous as the criminals can take over control of such accounts and manipulate their messages. This can have a profound impact on both the image of the hacked victim, the brands and services that they are promoting and on the followers. The rise of branded-content scams shows that such activities do happen and that all profiles are potential targets.
The main idea behind them is to lure the influencers and marketing agencies into thinking that the scammers are legitimate brands. They will create fake ones or impersonate others in sending out phishing links.
All major elements that build up the profile of a “legitimate” Instagram profile are crafted by the hacker operators: the profile name, description and uploaded content. The target users will be contacted through direct messages with offers that simulate the way legitimate profiles do.
The sent phishing links will present login pages or surveys that will request account credentials to “validate” or correctly open a certain file or procedure. If such are entered they will be instantly transferred to the hackers who will steal the accounts.

Instagram Scam #11 — Scam Web Address Profiles
Some of the hacking groups that are behind the majority of Instagram scams have shifted into launching a slightly different campaign. Their new approach is to create profiles that do not use usernames or first and last name combinations. Instead they focus on assigning their names with the addresses of legitimate and well-known services or companies. By using this approach they add one malicious element that is used in combination with the posts and content.
The detected combinations include the following scenarios:
- All caps full address profiles.
- Lowercase addresses or shortened urls as the profile name.
- Addresses with slight spelling modifications.

Instagram Hacks — Future Development

While Instagram remains one of the most popular platforms for sharing multimedia posts the primary reason for choosing it is another. Instagram can connect to many Internet services and software. Combined with the fact that all posts can be tagged with publicly available tags a simple post can reach thousands of users in the matter of seconds. The application already comes preinstalled on many mobile devices and this further drives its popularity.
It is very easy for the criminal users to create fake profiles of well-known brands, companies or even people and create SPAM messages that can be artificially boosted using automated means. Criminal collectives (hacker groups) have started to post scams as soon as the service became popular and this has lead to the introduction of such powerful scams that are both damaging to the users and the spoofed targets at the same time. As Instagram matures and adds newer functionality so the possibilities of creating newer and more complex scams.

Remove Instagram Scam from Your Computer
In order to make sure that the Instagram Scam scam is fully gone from your computer, we recommend that you follow the removal instructions underneath this article. They have been divided in manual and automatic removal manuals so that they can help you delete this threat based on your malware removal experience. If manual removal is not exactly something that you feel confident in doing, recommendations are to remove this malware or check if it has your infected your computer automatically by downloading and scanning your computer via an advanced anti-malware program. Such software will effectively make sure that your PC is fully secured and you passwords and data remain safe in the future.
- Windows
- Mac OS X
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
- Safari
- Internet Explorer
- Stop Push Pop-ups
How to Remove Scam on Instagram from Windows.
Step 1: Scan for Scam on Instagram with SpyHunter Anti-Malware Tool



Step 2: Boot Your PC In Safe Mode





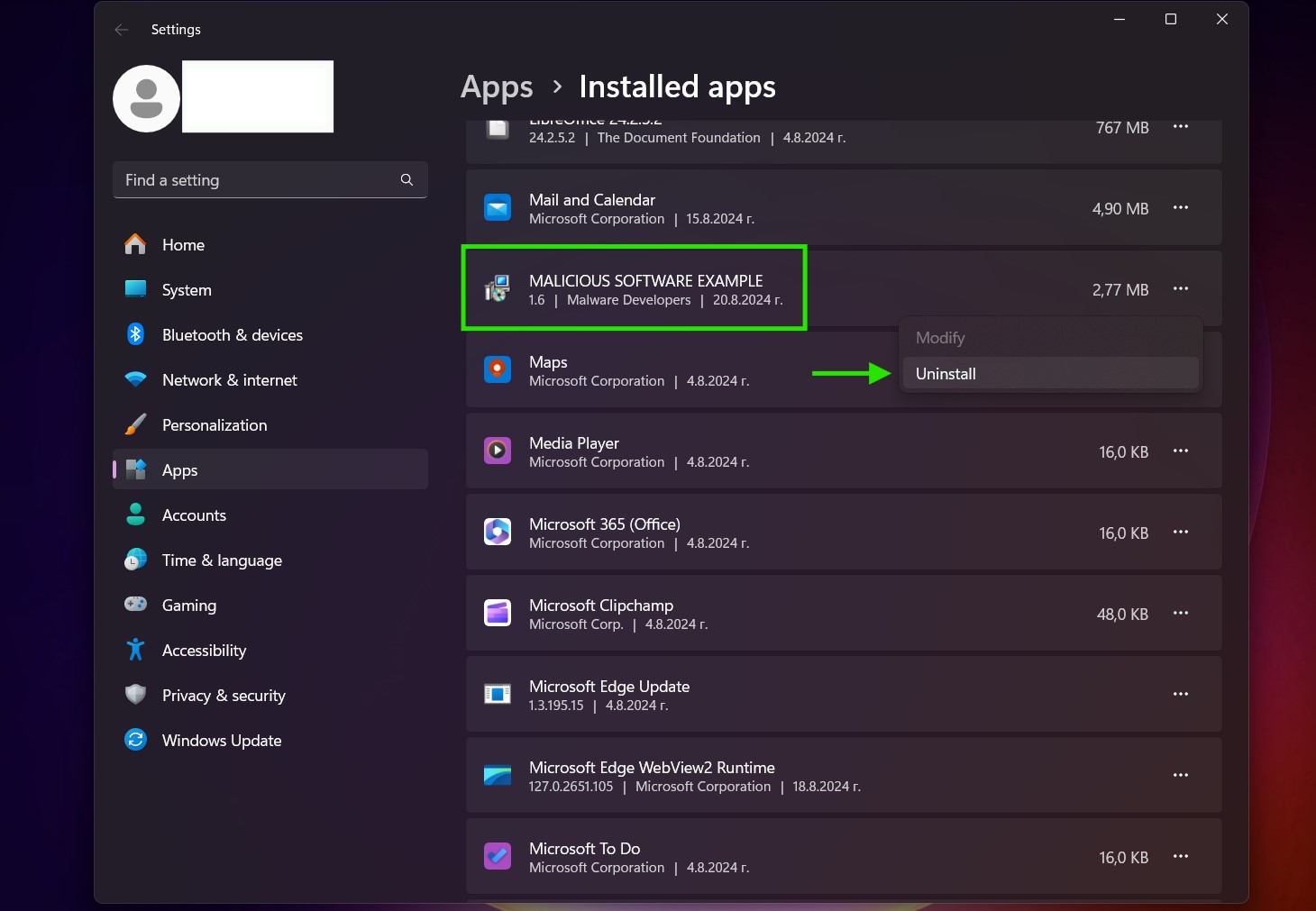
Step 3: Uninstall Scam on Instagram and related software from Windows
Uninstall Steps for Windows 11
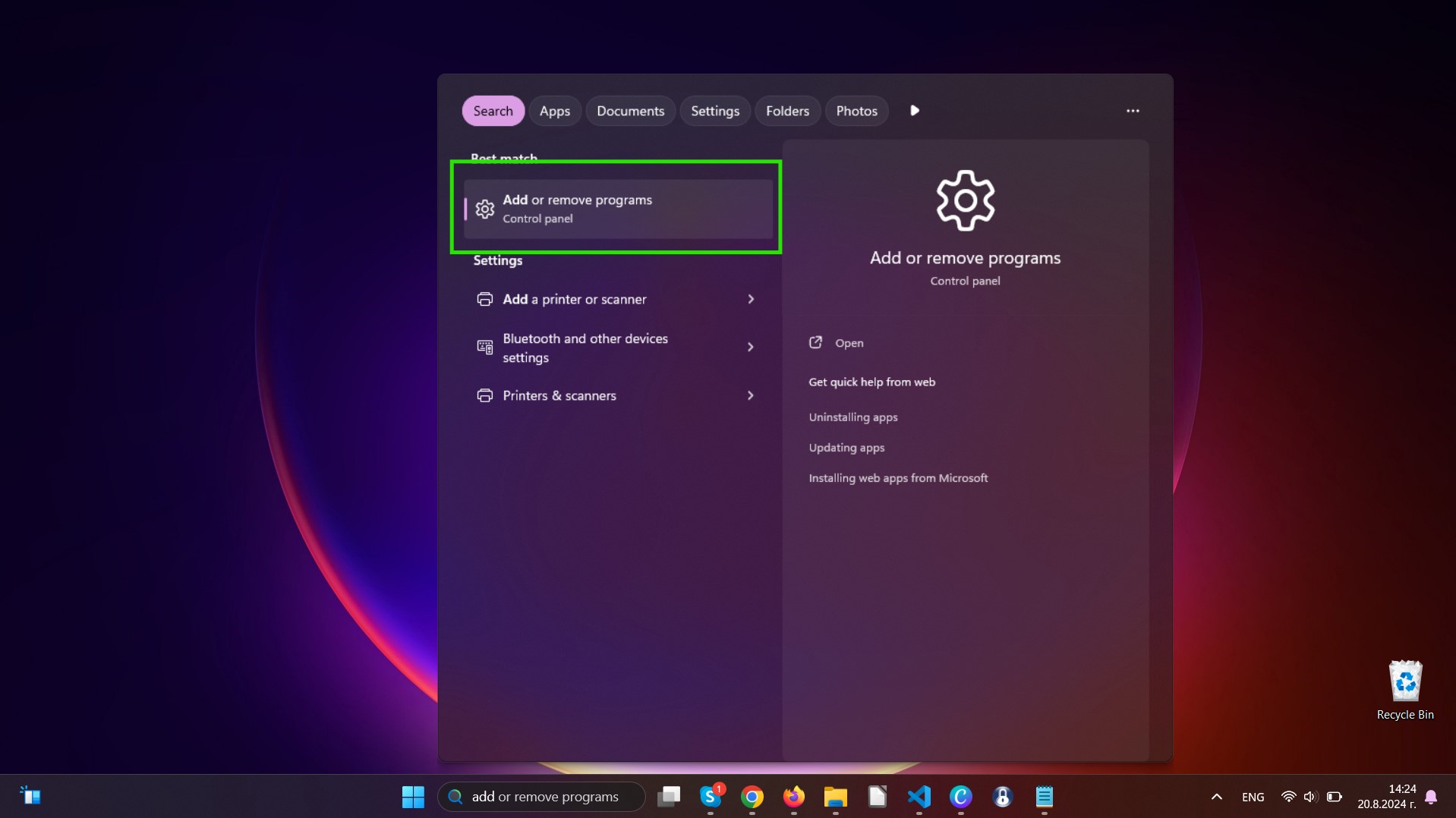
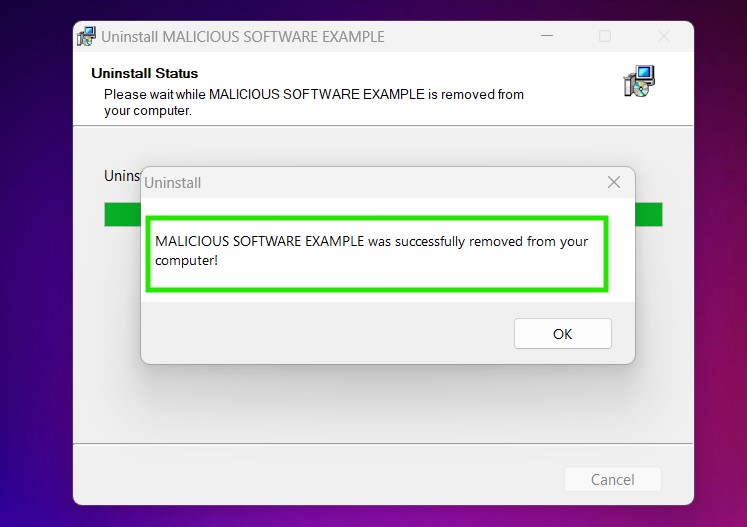
Uninstall Steps for Windows 10 and Older Versions
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully uninstall most programs.
Follow the instructions above and you will successfully uninstall most programs.
Step 4: Clean Any registries, Created by Scam on Instagram on Your PC.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by Scam on Instagram there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Video Removal Guide for Scam on Instagram (Windows).
Get rid of Scam on Instagram from Mac OS X.
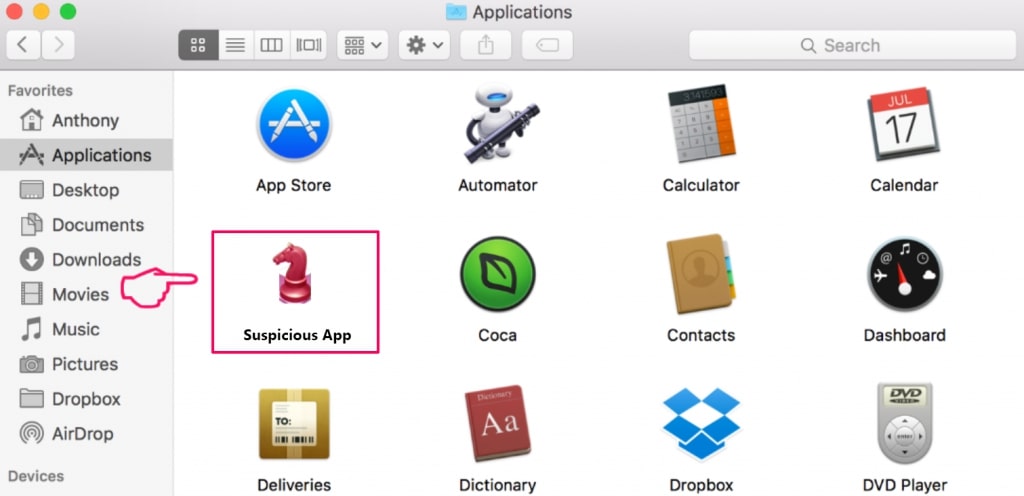
Step 1: Uninstall Scam on Instagram and remove related files and objects
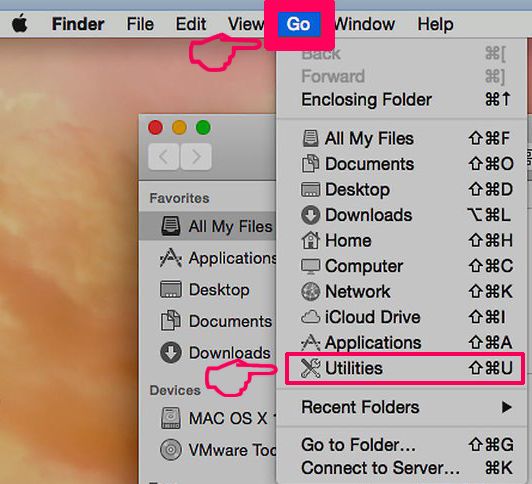
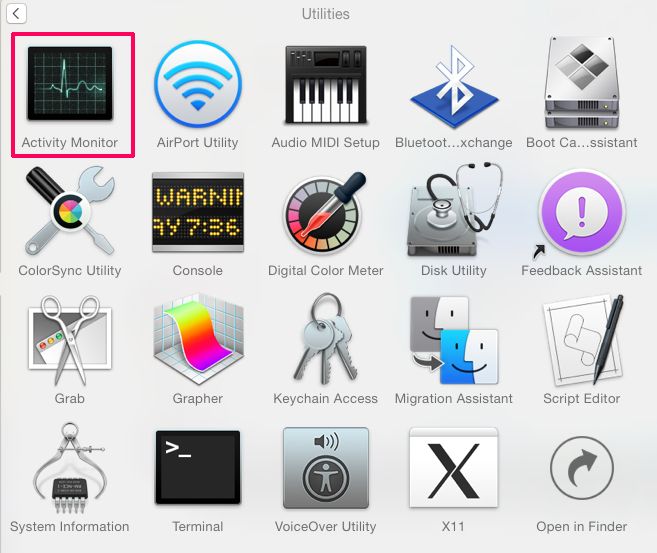
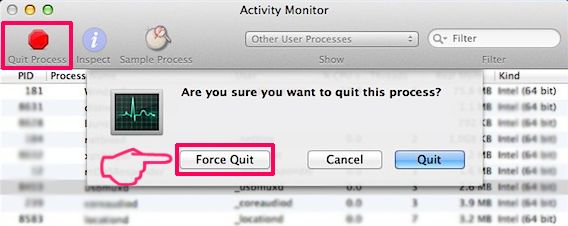
Your Mac will then show you a list of items that start automatically when you log in. Look for any suspicious apps identical or similar to Scam on Instagram. Check the app you want to stop from running automatically and then select on the Minus (“-“) icon to hide it.
- Go to Finder.
- In the search bar type the name of the app that you want to remove.
- Above the search bar change the two drop down menus to “System Files” and “Are Included” so that you can see all of the files associated with the application you want to remove. Bear in mind that some of the files may not be related to the app so be very careful which files you delete.
- If all of the files are related, hold the ⌘+A buttons to select them and then drive them to “Trash”.
In case you cannot remove Scam on Instagram via Step 1 above:
In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below:
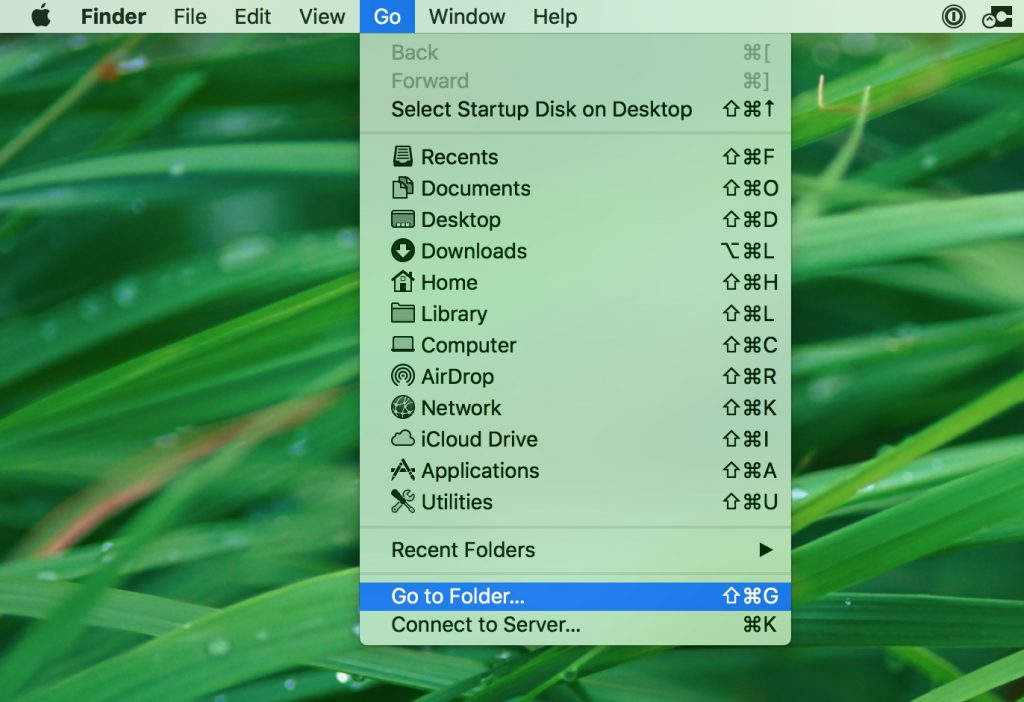
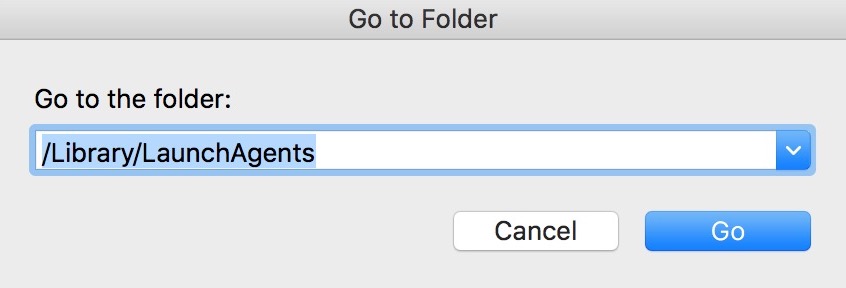
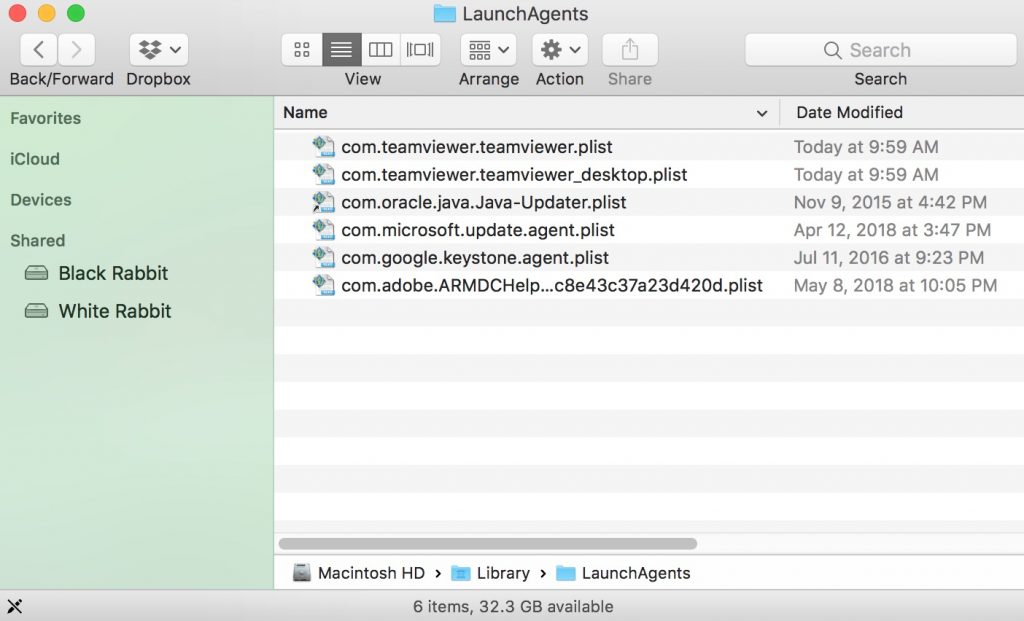
You can repeat the same procedure with the following other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
Tip: ~ is there on purpose, because it leads to more LaunchAgents.
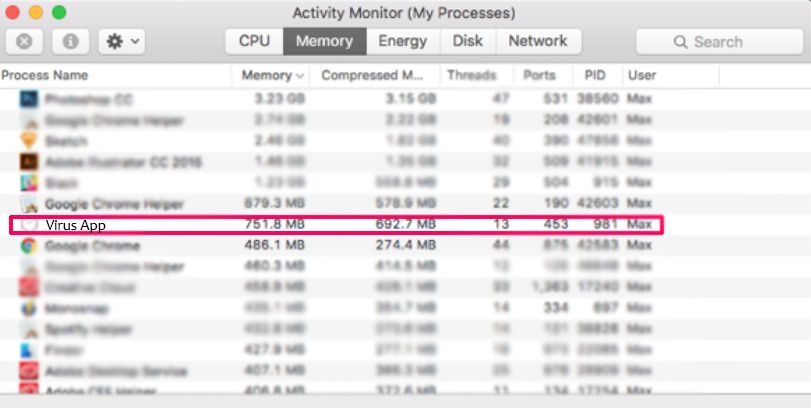
Step 2: Scan for and remove Scam on Instagram files from your Mac
When you are facing problems on your Mac as a result of unwanted scripts and programs such as Scam on Instagram, the recommended way of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that will improve your Mac’s security and protect it in the future.
Video Removal Guide for Scam on Instagram (Mac)
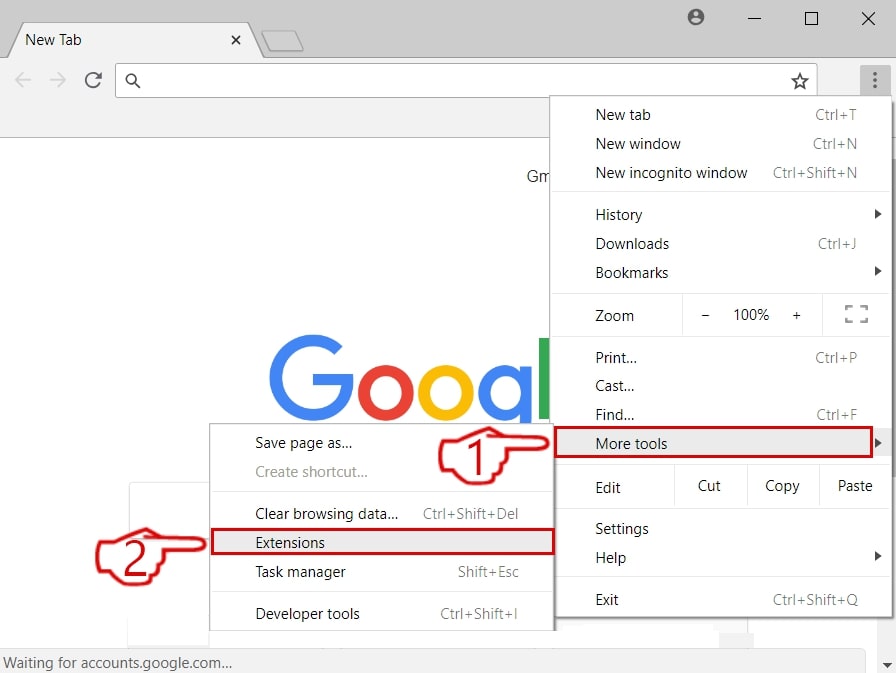
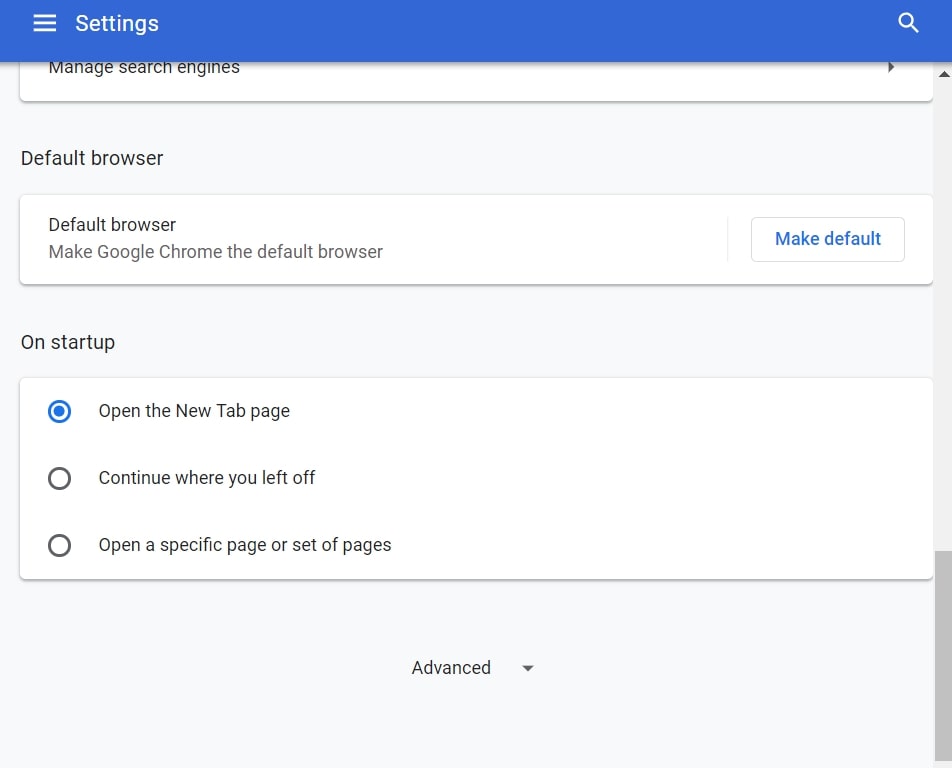
Remove Scam on Instagram from Google Chrome.
Step 1: Start Google Chrome and open the drop menu
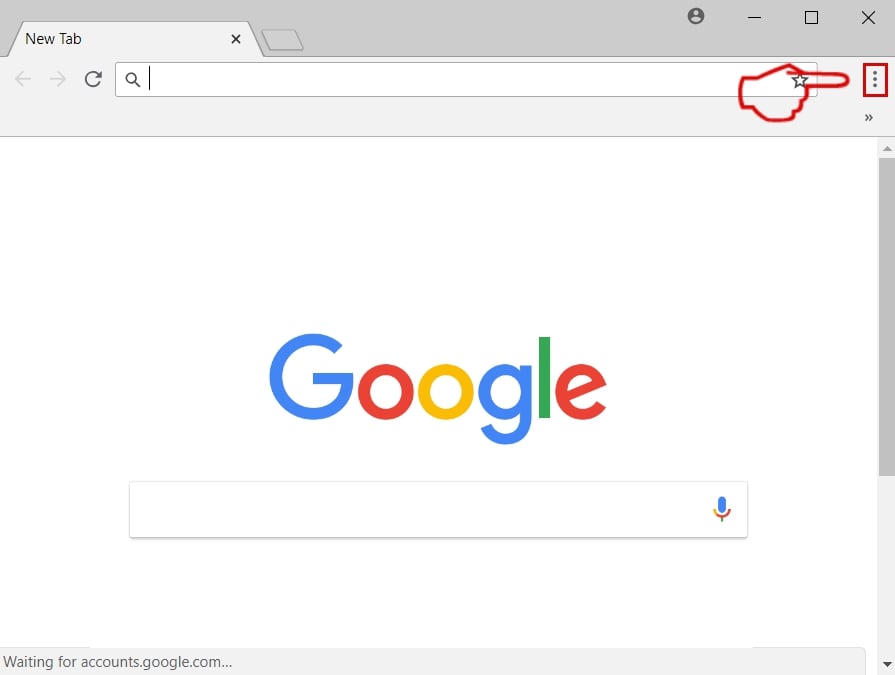
Step 2: Move the cursor over "Tools" and then from the extended menu choose "Extensions"
Step 3: From the opened "Extensions" menu locate the unwanted extension and click on its "Remove" button.
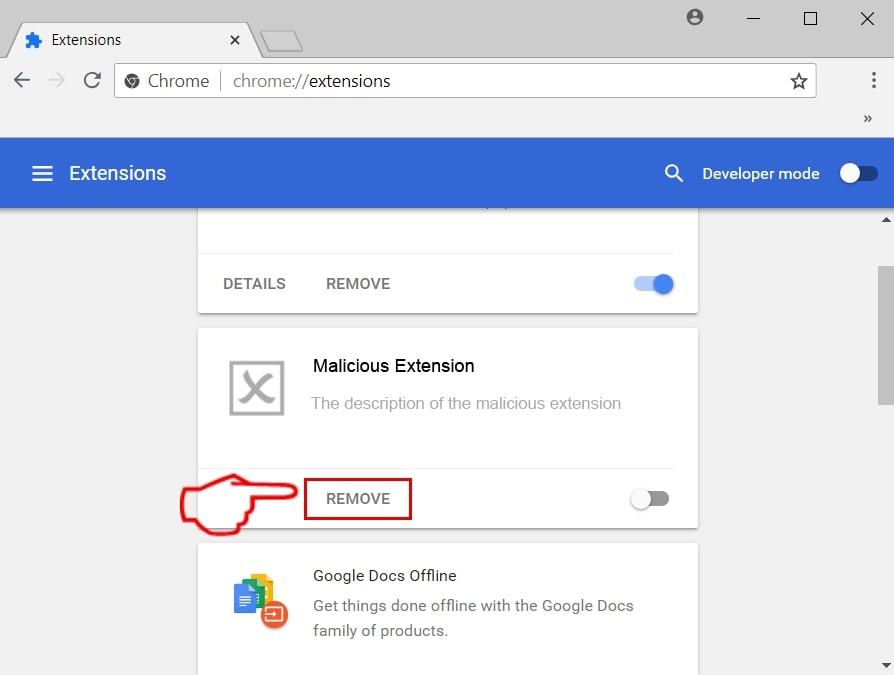
Step 4: After the extension is removed, restart Google Chrome by closing it from the red "X" button at the top right corner and start it again.
Erase Scam on Instagram from Mozilla Firefox.
Step 1: Start Mozilla Firefox. Open the menu window:
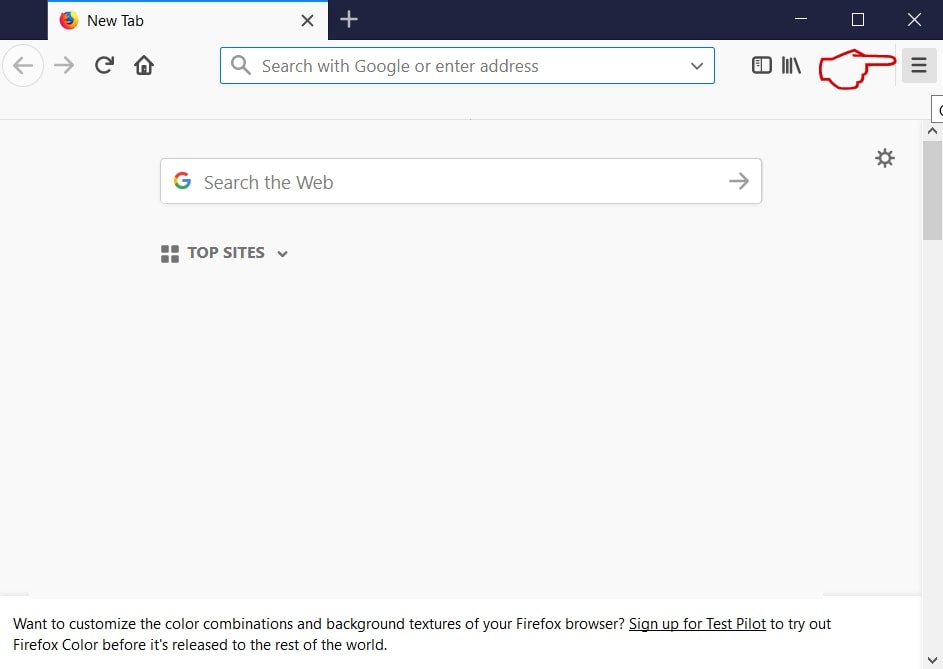
Step 2: Select the "Add-ons" icon from the menu.
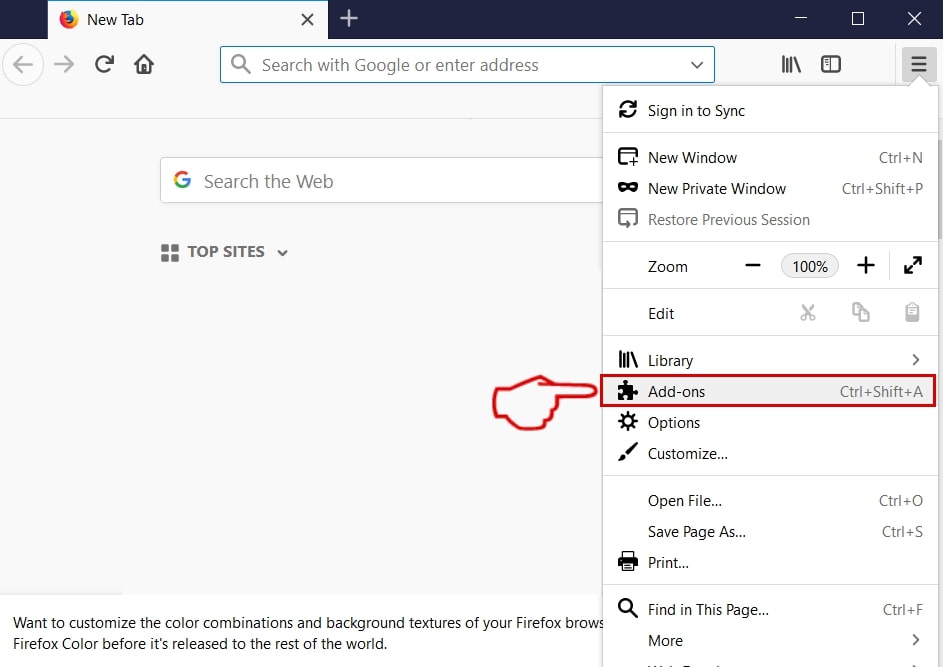
Step 3: Select the unwanted extension and click "Remove"

Step 4: After the extension is removed, restart Mozilla Firefox by closing it from the red "X" button at the top right corner and start it again.
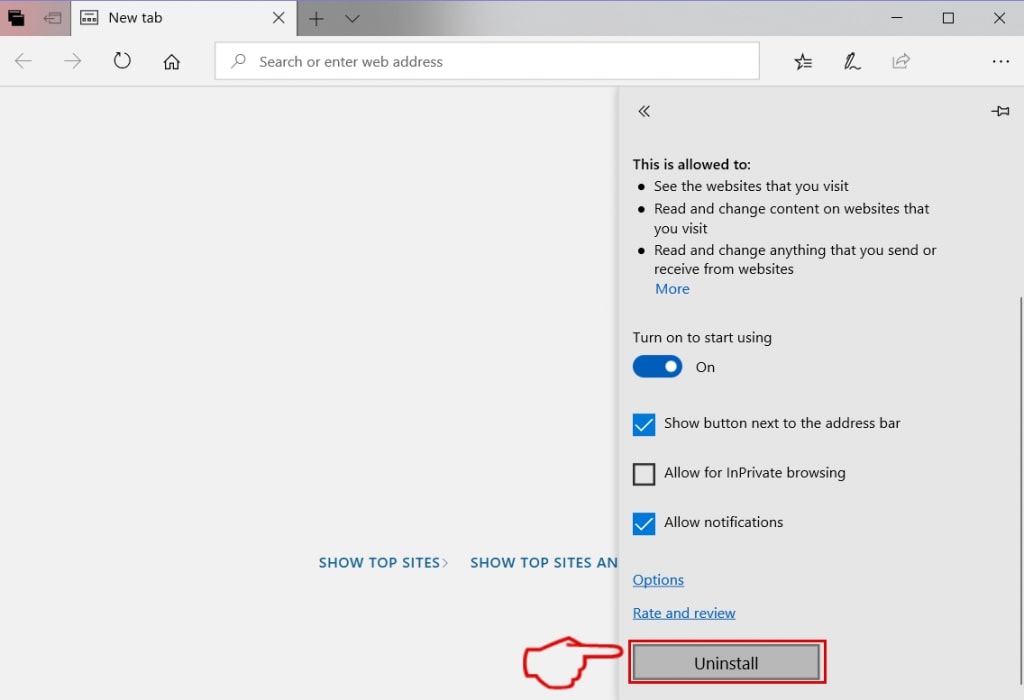
Uninstall Scam on Instagram from Microsoft Edge.
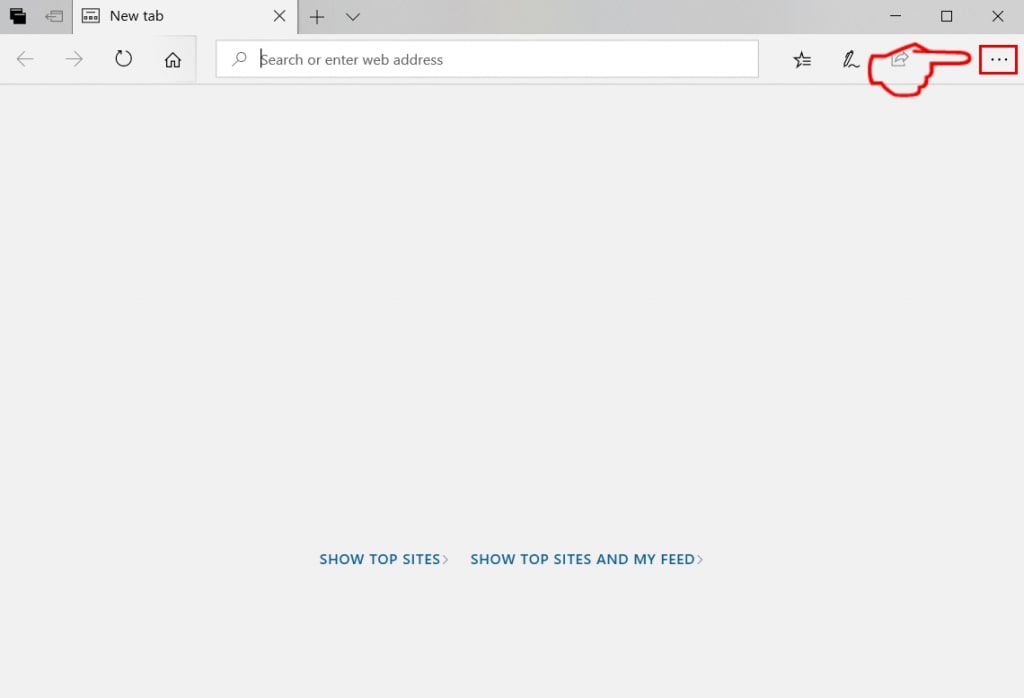
Step 1: Start Edge browser.
Step 2: Open the drop menu by clicking on the icon at the top right corner.
Step 3: From the drop menu select "Extensions".
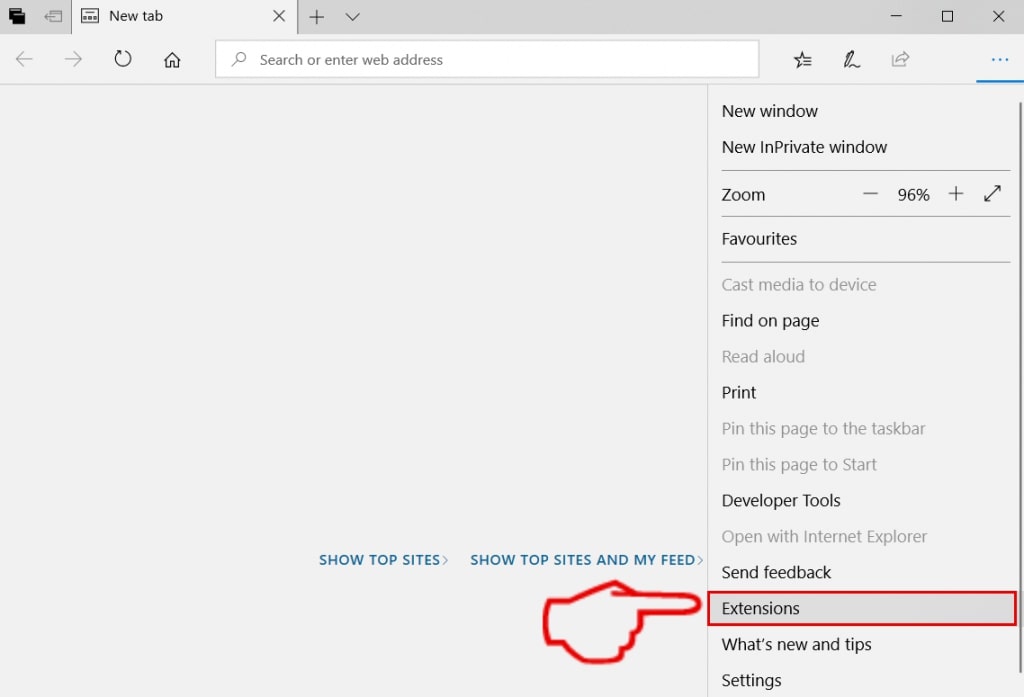
Step 4: Choose the suspected malicious extension you want to remove and then click on the gear icon.
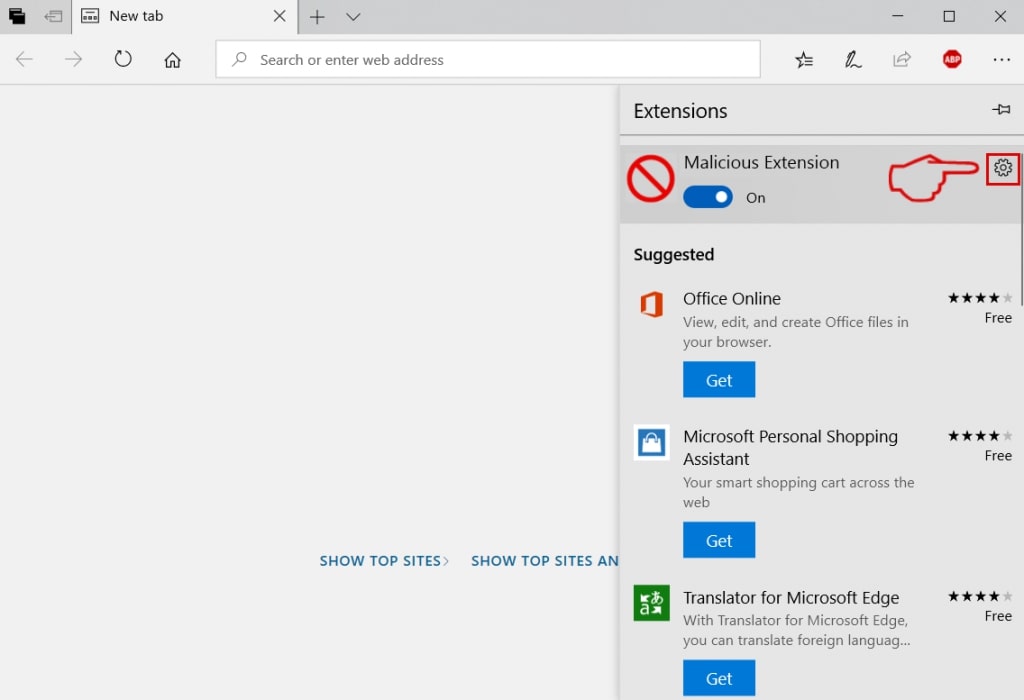
Step 5: Remove the malicious extension by scrolling down and then clicking on Uninstall.
Remove Scam on Instagram from Safari
Step 1: Start the Safari app.
Step 2: After hovering your mouse cursor to the top of the screen, click on the Safari text to open its drop down menu.
Step 3: From the menu, click on "Preferences".
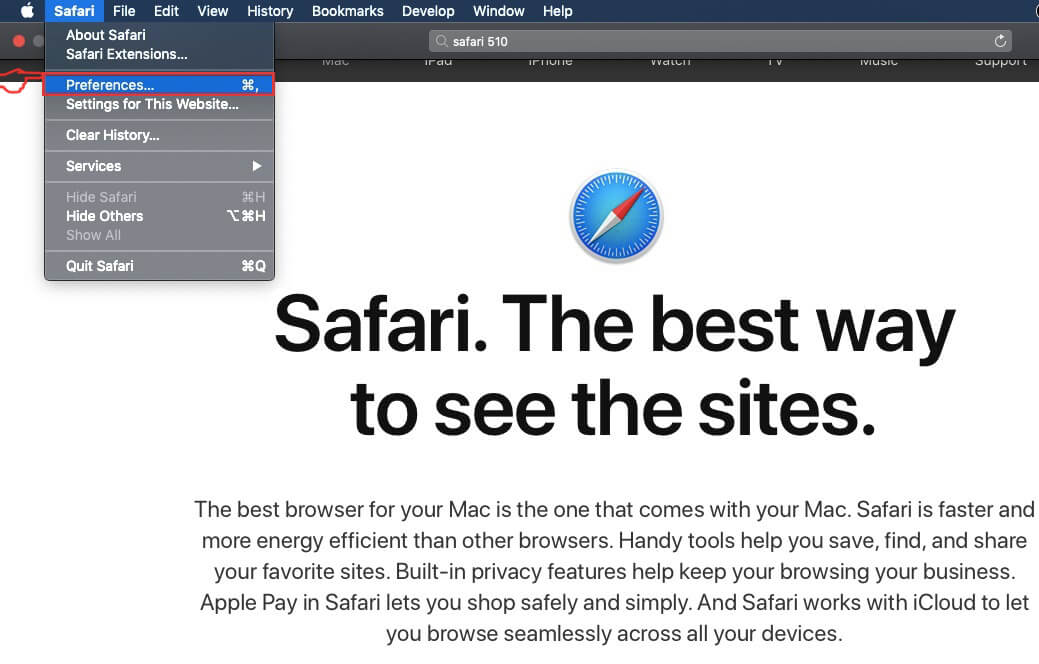
Step 4: After that, select the 'Extensions' Tab.
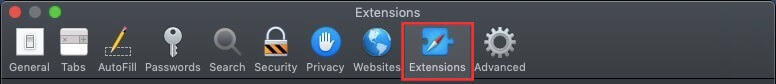
Step 5: Click once on the extension you want to remove.
Step 6: Click 'Uninstall'.
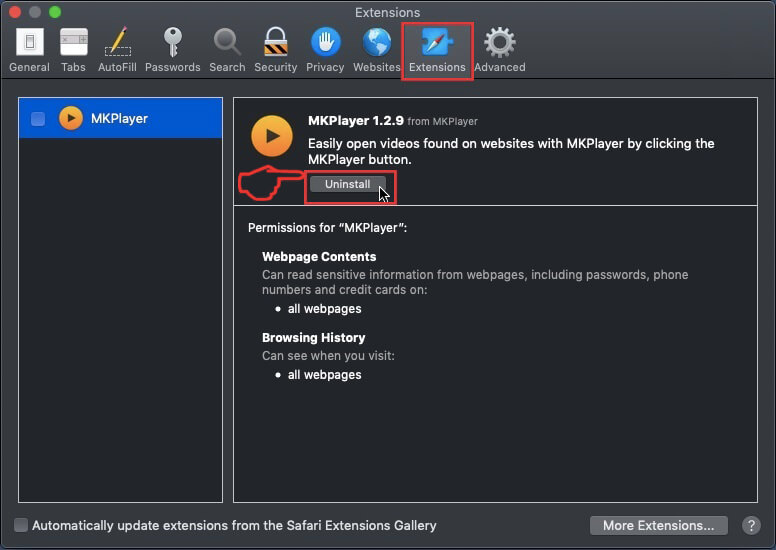
A pop-up window will appear asking for confirmation to uninstall the extension. Select 'Uninstall' again, and the Scam on Instagram will be removed.
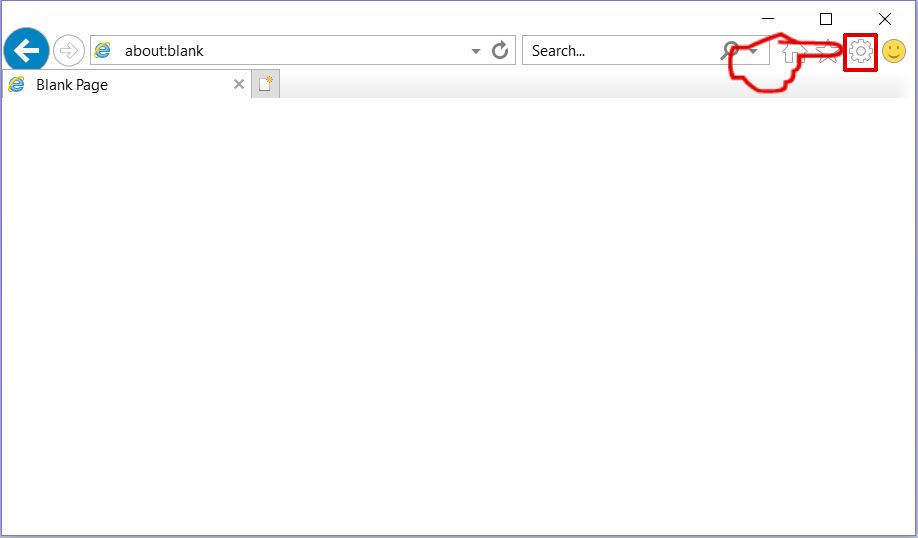
Eliminate Scam on Instagram from Internet Explorer.
Step 1: Start Internet Explorer.
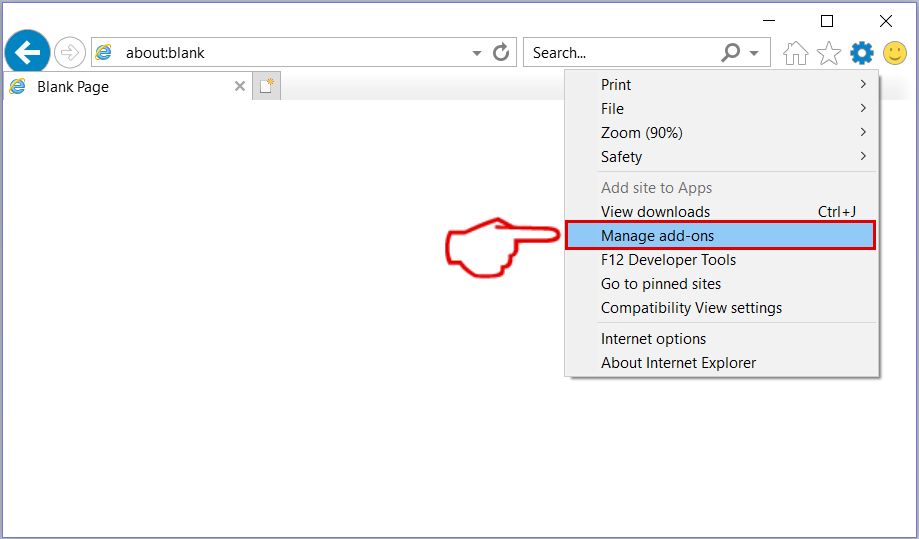
Step 2: Click on the gear icon labeled 'Tools' to open the drop menu and select 'Manage Add-ons'
Step 3: In the 'Manage Add-ons' window.
Step 4: Select the extension you want to remove and then click 'Disable'. A pop-up window will appear to inform you that you are about to disable the selected extension, and some more add-ons might be disabled as well. Leave all the boxes checked, and click 'Disable'.
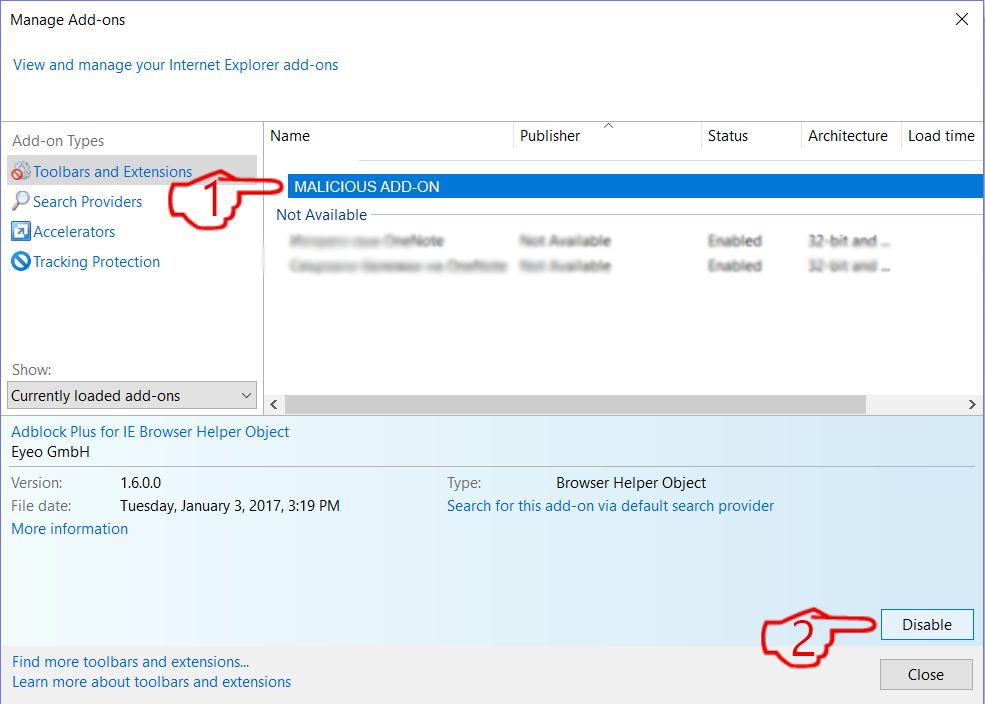
Step 5: After the unwanted extension has been removed, restart Internet Explorer by closing it from the red 'X' button located at the top right corner and start it again.
Remove Push Notifications from Your Browsers
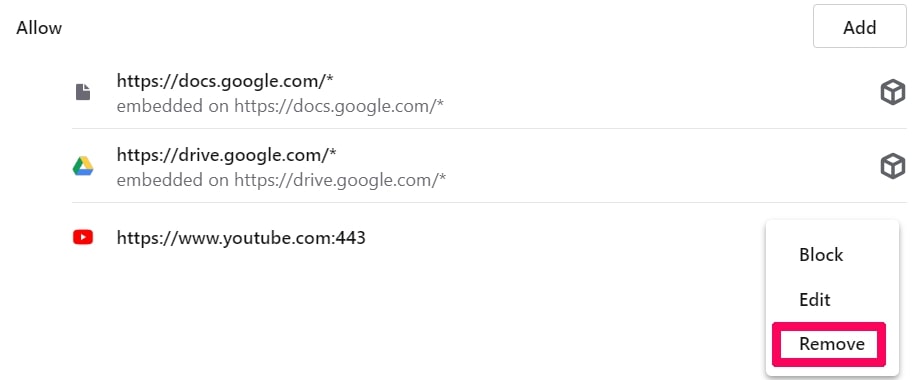
Turn Off Push Notifications from Google Chrome
To disable any Push Notices from Google Chrome browser, please follow the steps below:
Step 1: Go to Settings in Chrome.
Step 2: In Settings, select “Advanced Settings”:
Step 3: Click “Content Settings”:
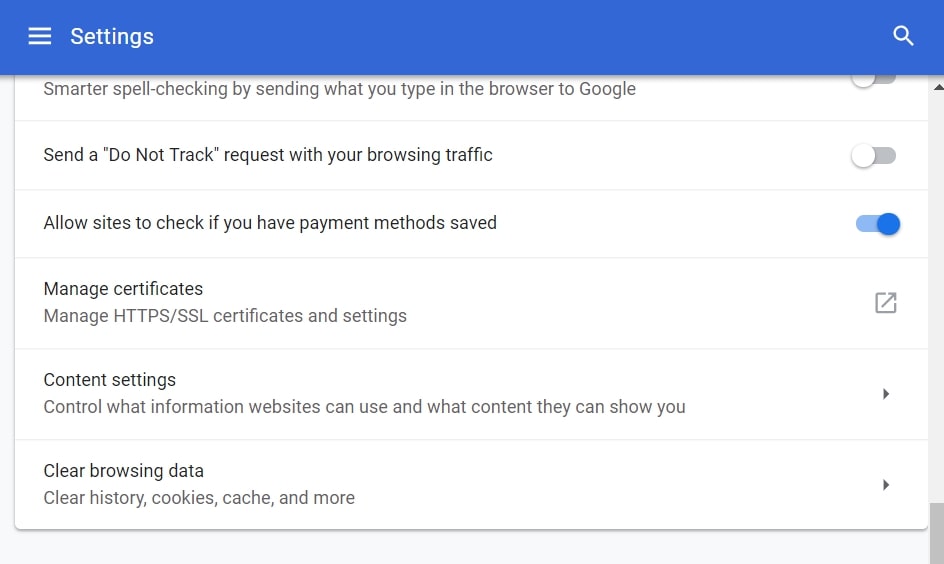
Step 4: Open “Notifications”:
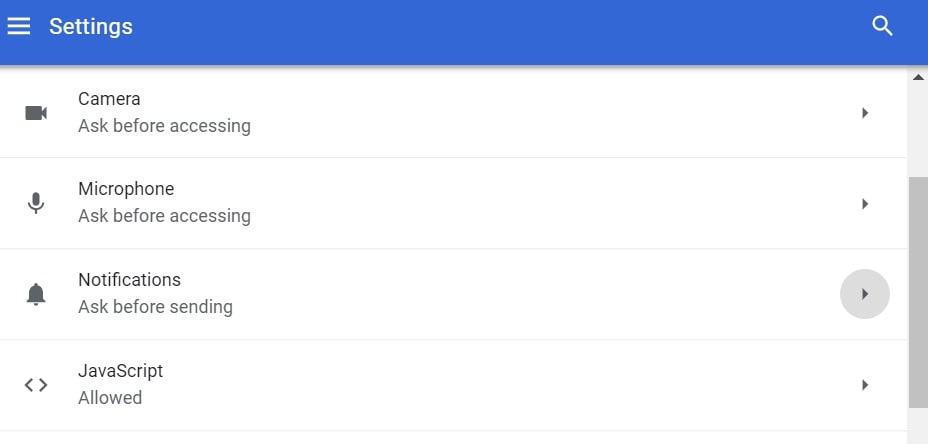
Step 5: Click the three dots and choose Block, Edit or Remove options:

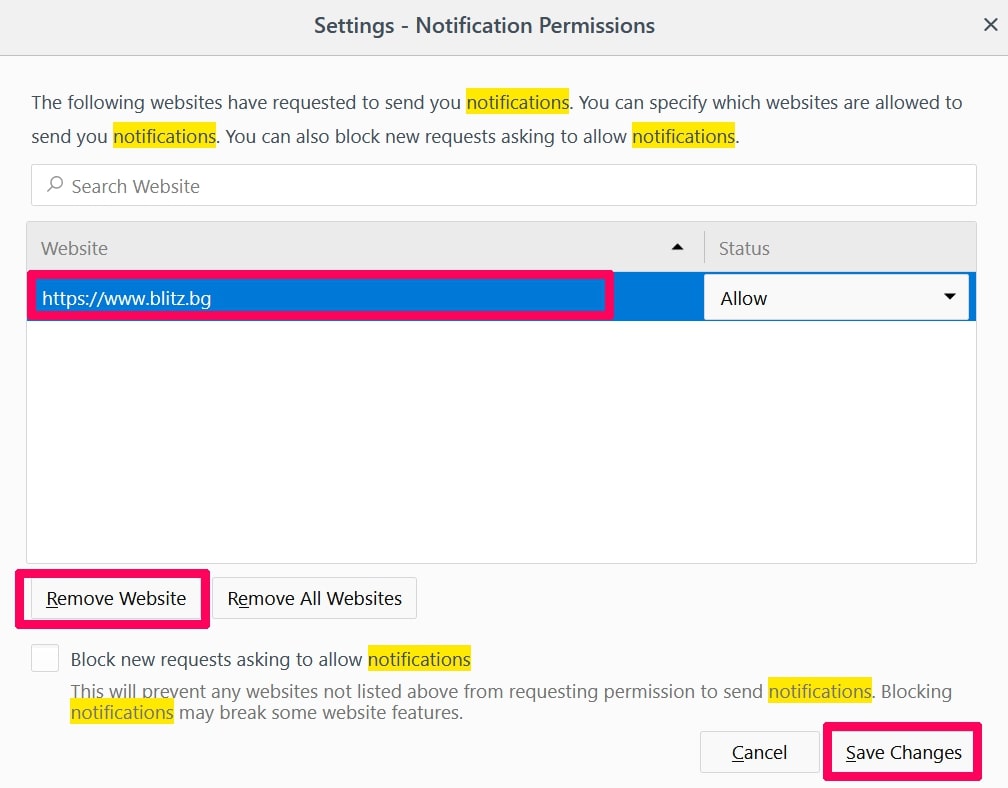
Remove Push Notifications on Firefox
Step 1: Go to Firefox Options.
Step 2: Go to “Settings”, type “notifications” in the search bar and click "Settings":
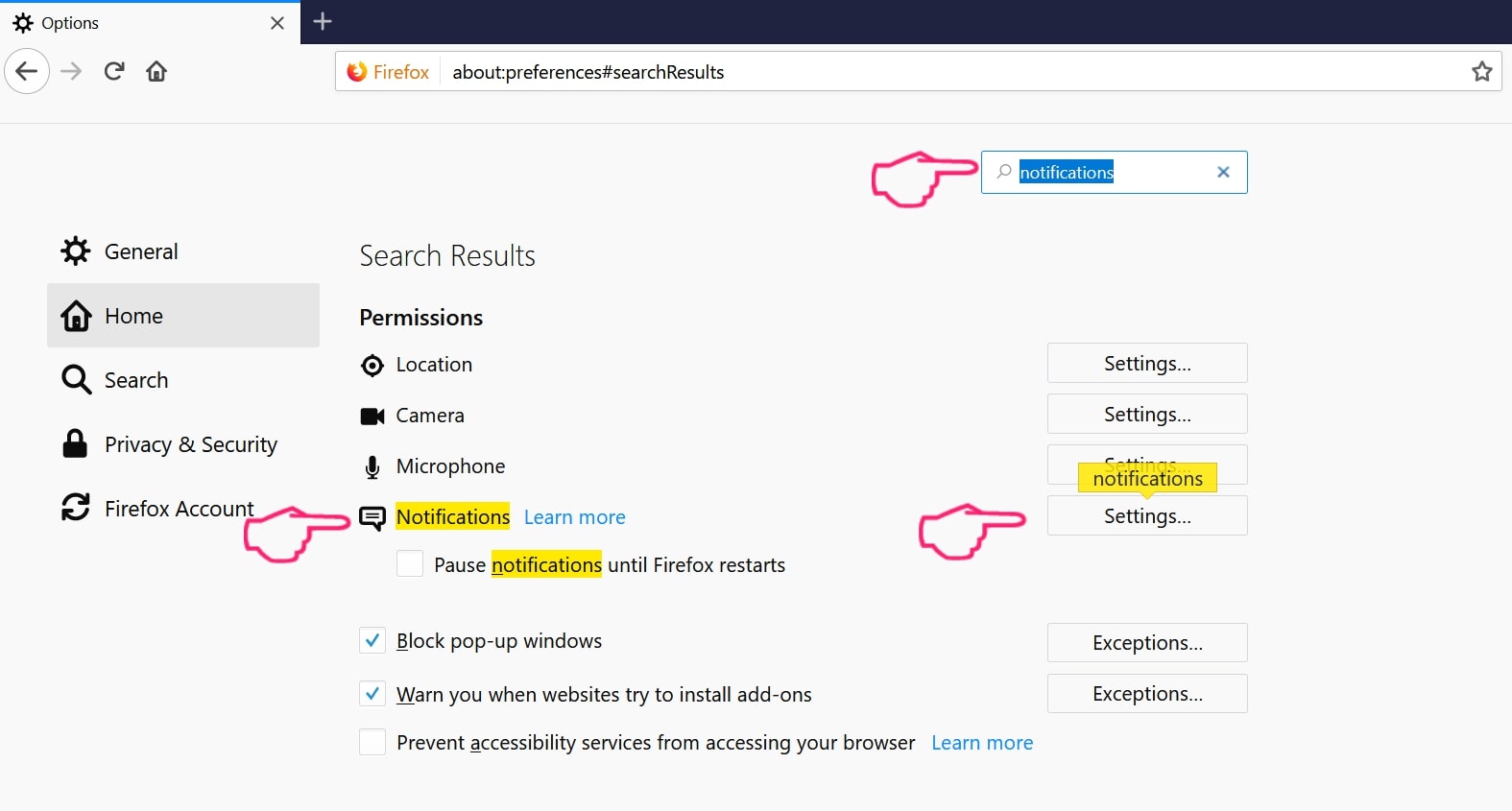
Step 3: Click “Remove” on any site you wish notifications gone and click “Save Changes”
Stop Push Notifications on Opera
Step 1: In Opera, press ALT+P to go to Settings.
Step 2: In Setting search, type “Content” to go to Content Settings.
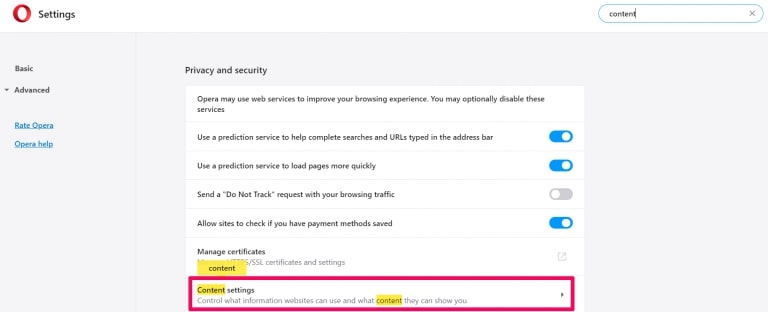
Step 3: Open Notifications:
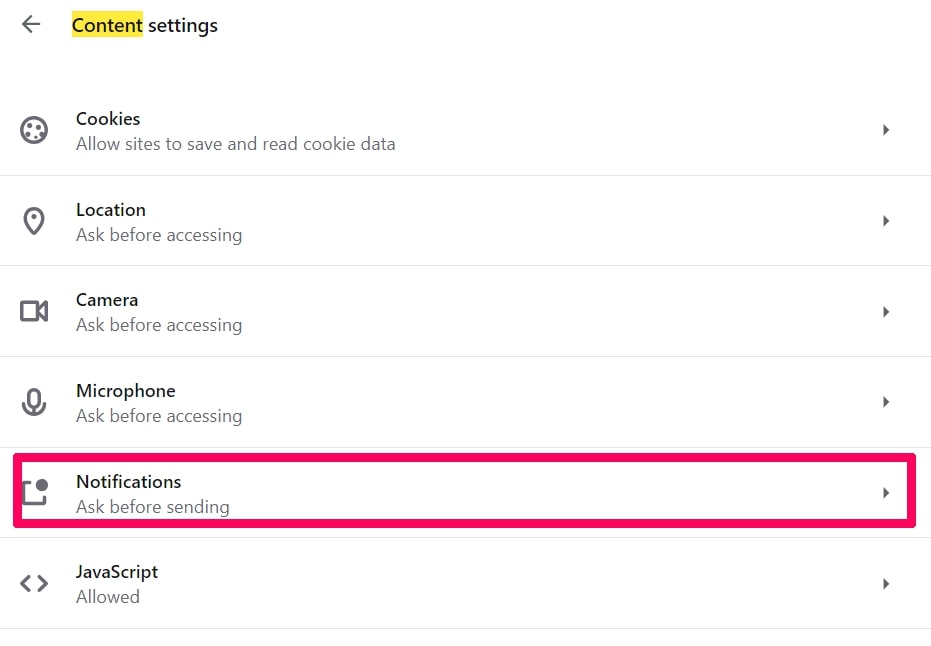
Step 4: Do the same as you did with Google Chrome (explained below):
Eliminate Push Notifications on Safari
Step 1: Open Safari Preferences.
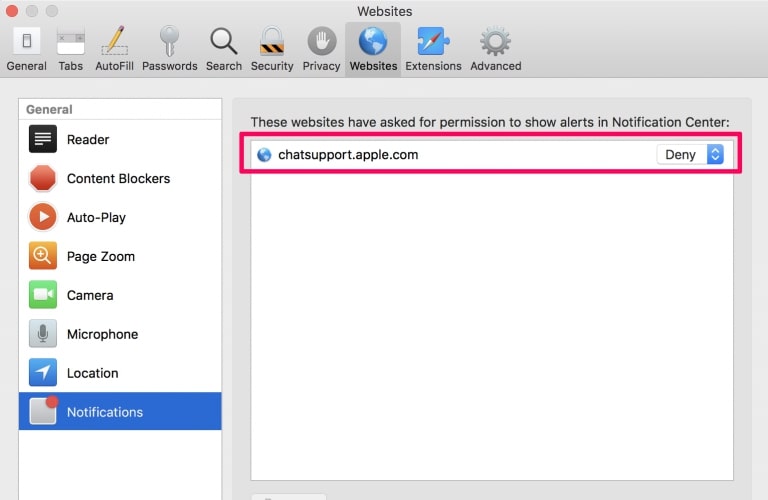
Step 2: Choose the domain from where you like push pop-ups gone and change to "Deny" from "Allow".
Scam on Instagram-FAQ
What Is Scam on Instagram?
The Scam on Instagram threat is adware or browser redirect virus.
It may slow your computer down significantly and display advertisements. The main idea is for your information to likely get stolen or more ads to appear on your device.
The creators of such unwanted apps work with pay-per-click schemes to get your computer to visit risky or different types of websites that may generate them funds. This is why they do not even care what types of websites show up on the ads. This makes their unwanted software indirectly risky for your OS.
What Are the Symptoms of Scam on Instagram?
There are several symptoms to look for when this particular threat and also unwanted apps in general are active:
Symptom #1: Your computer may become slow and have poor performance in general.
Symptom #2: You have toolbars, add-ons or extensions on your web browsers that you don't remember adding.
Symptom #3: You see all types of ads, like ad-supported search results, pop-ups and redirects to randomly appear.
Symptom #4: You see installed apps on your Mac running automatically and you do not remember installing them.
Symptom #5: You see suspicious processes running in your Task Manager.
If you see one or more of those symptoms, then security experts recommend that you check your computer for viruses.
What Types of Unwanted Programs Are There?
According to most malware researchers and cyber-security experts, the threats that can currently affect your device can be rogue antivirus software, adware, browser hijackers, clickers, fake optimizers and any forms of PUPs.
What to Do If I Have a "virus" like Scam on Instagram?
With few simple actions. First and foremost, it is imperative that you follow these steps:
Step 1: Find a safe computer and connect it to another network, not the one that your Mac was infected in.
Step 2: Change all of your passwords, starting from your email passwords.
Step 3: Enable two-factor authentication for protection of your important accounts.
Step 4: Call your bank to change your credit card details (secret code, etc.) if you have saved your credit card for online shopping or have done online activities with your card.
Step 5: Make sure to call your ISP (Internet provider or carrier) and ask them to change your IP address.
Step 6: Change your Wi-Fi password.
Step 7: (Optional): Make sure to scan all of the devices connected to your network for viruses and repeat these steps for them if they are affected.
Step 8: Install anti-malware software with real-time protection on every device you have.
Step 9: Try not to download software from sites you know nothing about and stay away from low-reputation websites in general.
If you follow these recommendations, your network and all devices will become significantly more secure against any threats or information invasive software and be virus free and protected in the future too.
How Does Scam on Instagram Work?
Once installed, Scam on Instagram can collect data using trackers. This data is about your web browsing habits, such as the websites you visit and the search terms you use. It is then used to target you with ads or to sell your information to third parties.
Scam on Instagram can also download other malicious software onto your computer, such as viruses and spyware, which can be used to steal your personal information and show risky ads, that may redirect to virus sites or scams.
Is Scam on Instagram Malware?
The truth is that PUPs (adware, browser hijackers) are not viruses, but may be just as dangerous since they may show you and redirect you to malware websites and scam pages.
Many security experts classify potentially unwanted programs as malware. This is because of the unwanted effects that PUPs can cause, such as displaying intrusive ads and collecting user data without the user’s knowledge or consent.
About the Scam on Instagram Research
The content we publish on SensorsTechForum.com, this Scam on Instagram how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific, adware-related problem, and restore your browser and computer system.
How did we conduct the research on Scam on Instagram?
Please note that our research is based on independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware, adware, and browser hijacker definitions.
Furthermore, the research behind the Scam on Instagram threat is backed with VirusTotal.
To better understand this online threat, please refer to the following articles which provide knowledgeable details.