Há uma crença de que os usuários de Mac não são suscetíveis a software malicioso. Bem, havia uma crença ... Uma vasta pesquisa sobre malware para Mac revela que 2015 tem sido o pior até agora em termos de segurança. O novo relatório sobre o assunto foi publicado recentemente pela empresa de segurança de TI Bit9 + Equipe de pesquisa de ameaça de negro de fumo.
Levou a equipe 10 semanas para coletar e analisar os dados, necessário para tal papel. Durante o período, os pesquisadores analisaram mais de 1,400 amostras exclusivas de malware OS X. A conclusão veio naturalmente - em 2015, o malware atual para Macs é bastante forte e devastador. Seu relatório é apelidado de ‘2015: O ano mais produtivo da história para o malware OS X '. Os esforços de pesquisa da equipe podem ter acabado de quebrar a ilusão de que os Macs são imunes a hacks em comparação com PCs que executam o sistema operacional Windows.
O que a pesquisa enfatiza?
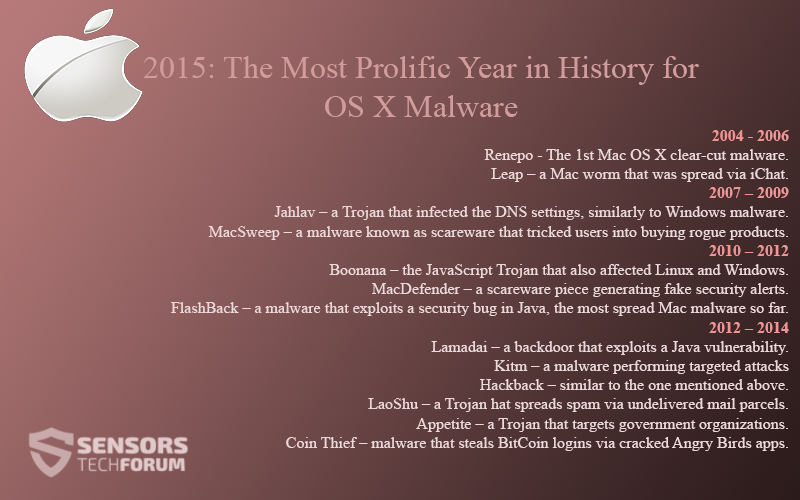
A equipe observou de perto as vulnerabilidades no OS X, e as peças de malware que tiraram proveito deles. Eles também coletaram amostras. Um bom exemplo aqui é o XcodeGhost. As ferramentas XcodeGhost implementam componentes maliciosos em aplicativos criados com Xcode. além disso, foi relatado recentemente que o OS X El Capitan - o décimo segundo grande lançamento do OS X, lançado em setembro - contém sérias falhas de segurança nos recursos do Gatekeeper e das Chaves. Para provar seu ponto, a equipe criou uma linha do tempo de malware para Mac, que se parece com isso:
2004 – 2006
- Renepo – O primeiro malware claro do Mac OS X.
- Leap - um worm Mac que foi espalhado pelo iChat.
2007 - 2009
- Jahlav - um Trojan que infectou as configurações de DNS, semelhante ao malware do Windows.
- MacSweep - um malware conhecido como scareware que induziu os usuários a comprar produtos nocivos.
2010 - 2012
- Boonana - o cavalo de Troia JavaScript que também afetou o Linux e o Windows.
- MacDefender - uma peça de scareware que gera alertas de segurança falsos.
- FlashBack - um malware que explora um bug de segurança em Java, o malware para Mac mais difundido até agora.
2012 - 2014
- Lamadai - um backdoor que explora uma vulnerabilidade Java.
- Kitm - um malware executando ataques direcionados.
- Hackback - semelhante ao mencionado acima.
- LaoShu - um chapéu de Tróia espalha spam por meio de pacotes de correio não entregues.
- Appetite - um Trojan que visa organizações governamentais.
- Coin Thief - malware que rouba logins do BitCoin por meio de aplicativos corrompidos do Angry Birds.
Como os pesquisadores explicam a aceitação do malware para Mac? Aqui está uma justificativa muito boa:
“Este aumento no malware para Mac OS X vem após vários anos de ganhos rápidos de participação de mercado do OS X, com 16.4 por cento do mercado agora executando o OS X, incluindo a expansão da implantação na empresa. Isso representa uma superfície de ataque crescente para dados confidenciais, Como 45 por cento das empresas agora oferecem Macs como uma opção para seus funcionários.”
Explicação do comportamento de malware do Mac
Como já dissemos, a análise foi baseada em mais de 1,400 amostras, fontes abertas, e compromissos de resposta a incidentes. Para avaliar as ameaças do Mac, os pesquisadores não podem usar ferramentas comuns de análise de malware do Windows. Para pular este obstáculo, o Bit9 + A equipe do Carbon usou uma série de ferramentas personalizadas e pré-construídas, como fs_usage, dtrace, e opensnoop.
Eles utilizaram as ferramentas e criaram máquinas especiais para análise dinâmica, que foram executados junto com a sandbox Carbon Black customizada. Graças a essas abordagens, a equipe identificou com sucesso ações comuns realizadas por malware do Mac, como criação de arquivos e comunicações de rede, observar o comando & infraestrutura de controle e artefatos que faziam parte da execução do malware.
O malware OS X utiliza recursos como LauchDaemons / LaunchAgents
Outros recursos aproveitados incluem itens de login e plug-ins de navegador. Outra descoberta que foi feita é que o malware Mac reside na "terra do usuário" e em mecanismos de persistência compatíveis, em vez de tentar residir em 'kernel-land' escrevendo extensões de kernel personalizadas.
Outra revelação curiosa feita pelos pesquisadores foi que a adaptação do malware Unix / Lunux para OS X não foi observada, não ao ponto que eles esperavam. Era lógico suspeitar de tais adaptações devido às raízes do OS X no FreeBSD. O malware estilo Unix trazido para o OS X não foi monitorado na análise de 10 semanas.
Ter um olhar para o todo Bit9 + Relatório de negro de fumo .