
The fourth edition of the well-known Tianfu Cup hacking content took place during the weekend of October 17 and 17 in Chengdu. The competition was won by Kunlun Lab, a Chinese cybersecurity company. Kunlun Lab’s team got the monetary award of $654,500. Nearly all listed targets were successfully “pwned.”
The Tianfu Cup is similar to Pwn2Own, as it gives white hats the ability to break into the latest devices and systems via original approaches and techniques. The hacking contest hosts three simultaneous tournaments dedicated to vulnerability demonstration, device cracking, and compromising operating systems. The device cracking tournament offers the largest monetary awards to teams that have three five-minute attempts to crack a device.
Who got pwned during Tianfu Cup 2021?
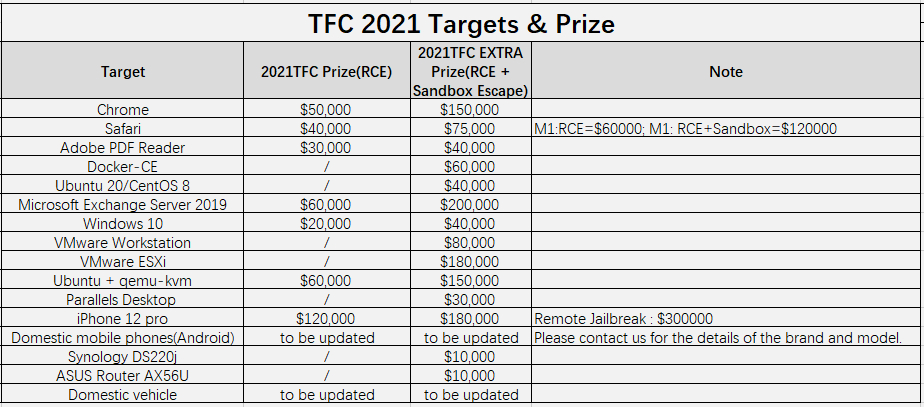
This year’s edition “targeted” Chrome running on Windows 10 21H1, Safari running on a Macbook Pro, Docker-CE installed on a server running Ubuntu Server 20.04, Linux operating system Ubuntu 20 and CentOS 8 installed on a Lenovo L14 system, Microsoft Exchange Server 2019, Windows 10, VMware Workstation and ESXi, Parallels Desktop, iPhone 13 Pro, Synology DS220j network-attached-storage device, and a ASUS Router AX56U.
Almost all targets were successfully hacked this year, with the exception of Synology DS220j NAS, Xiaomi Mi 11 smartphone, and an undisclosed Chinese electric vehicle, for which no participant even indicated to attempt an exploit.
Windows 10, on the other hand, was hacked 5 times. Here’s the list of the rest of the companies (compiled by TheRecord) that got pwned, some of which multiple times:
Adobe PDF Reader – 4 times
Ubuntu 20 – 4 times
Parallels VM – 3 times
iOS 15 – 3 times
Apple Safari – 2 times
Google Chrome – 2 times
ASUS AX56U router – 2 times
Docker CE – 1 time
VMWare ESXi – 1 time
VMWare Workstation – 1 time
qemu VM – 1 time
Microsoft Exchange – 1 time
Tianfu Cup 2020
It is noteworthy that an exploit against iOS showcased in the 2020 edition was used in an actual cyber-espionage campaign, carried out by the Beijing regime against its Uyghur population.
Last year’s edition was won by the team called “360 Enterprise Security and Government and (ESG) Vulnerability Research Institute,” from the respected Qihoo 360 company. The team received nearly two-thirds of the entire prize budget or $744,500 out of $1,210,000. Second and third place were given to the AntFinancial Lightyear Security Lab and security researcher Pang.


