Tired of having your Instagram account attacked by scammers and shady accounts? This article sheds light on Instagram scams, offering you a guide to recognize threats, build your defense, and ensure a safe, scam-free online experience while on Instagram. With actionable strategies and insights into the workings of these scams, we aim to arm you with the knowledge to keep your account safe. Let’s begin.

Threat Summary
| Name | Instagram Scams |
| Type | Instagram Scam / Hacked Instagram Account |
| Removal Time | Approximately 15 minutes to scan the whole system and remove any discovered threats |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
Understanding the Landscape of Instagram Scams
With Instagram’s growing popularity, it has become a breeding ground for innovative scamming techniques. Scammers exploit the platform’s vast user base, employing sophisticated methods to deceive users. Understanding the landscape of Instagram scams is crucial for identifying and avoiding potential threats. These scams vary widely, from simple deception attempts to complex schemes designed to steal personal information or money.
The Rise of Scams on Social Media Platforms
Social media platforms like Instagram have revolutionized the way we connect, but this connectivity comes at a cost. The very features that make Instagram appealing also make it an ideal target for scammers. The rise of scams on social media can be attributed to the ease with which fraudsters can reach potential victims. They create fake profiles, impersonate brands or individuals, and engage in tactics that exploit the trust and curiosity inherent in social media interactions. This trend is not only concerning but also escalating, as more users join these platforms unaware of the potential dangers.
Types of Instagram Scams You May Encounter
Scams on Instagram can take many forms, making it vital to familiarize yourself with the most common tactics:
- Phishing Attempts: These scams involve fake messages designed to trick you into giving away personal information. They may masquerade as legitimate communications from Instagram itself, asking you to verify your account or confirm login details.
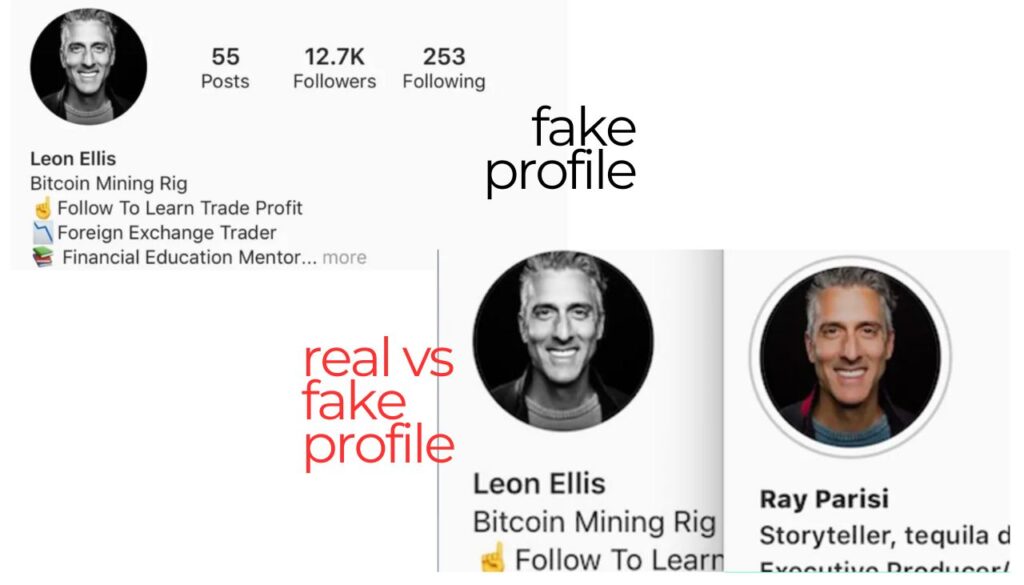
- Impersonation Scams: Scammers often create accounts that look astonishingly similar to those of real brands or individuals. Their aim is to either sell you counterfeit products or convince you to send money under false pretenses.
- Investment Scams: Offers promising quick and high returns on investments in cryptocurrencies or other ventures can often be too good to be true. These scams play on the desire to make easy money, leading victims to lose substantial sums.
- Lottery and Giveaway Scams: Announcements that you’ve won a prize or lottery, asking for a fee or your personal details to claim it, are almost always fraudulent.
- Romance Scams: Predators use fake profiles to establish romantic relationships, eventually convincing their victims to send money or share confidential information.
How Do Scammers Operate on Instagram?
Instagram scammers capitalize on the platform’s vast user base to carry out a variety of schemes aimed at stealing money, personal information, or both. They often craft their methods based on the psychology of persuasion, focusing on creating a veneer of trust and urgency. Such scammers design their approaches to appear as legitimate as possible, making it challenging for users to immediately discern their malicious intentions.
One common strategy involves the impersonation of famous brands or individuals, exploiting the trust and recognition those names command. In addition, scammers might create entirely fabricated personas that resonate with their target audience, alluring them into a false sense of security.
The operation of these schemes is multifaceted, often beginning with the collection of potential victims through broad or targeted outreach. From there, scammers engage in carefully scripted interactions designed to build rapport and trust over time. Once a sufficient level of trust is established, these cybercriminals deploy their malicious requests, which could range from financial solicitation to the sharing of sensitive personal information.
Common Tactics Used by Instagram Scammers
- Phishing Attempts: Leveraging fake messages that mimic legitimate communications, asking users to click on harmful links or provide their login details.
- Impersonation: Creating fake accounts that appear to belong to well-known brands or celebrities to solicit money or personal information under false pretenses.
- Hacked Friends’ Accounts: Using the hacked account of a person’s friend on Instagram is another probable scenario. Many people get scammed this way just by trusting that they were contacted by someone they know who is in need of some assistance.
- Investment Scams: Promising high returns on investments with little to no risk, often accompanied by pressure to act quickly.
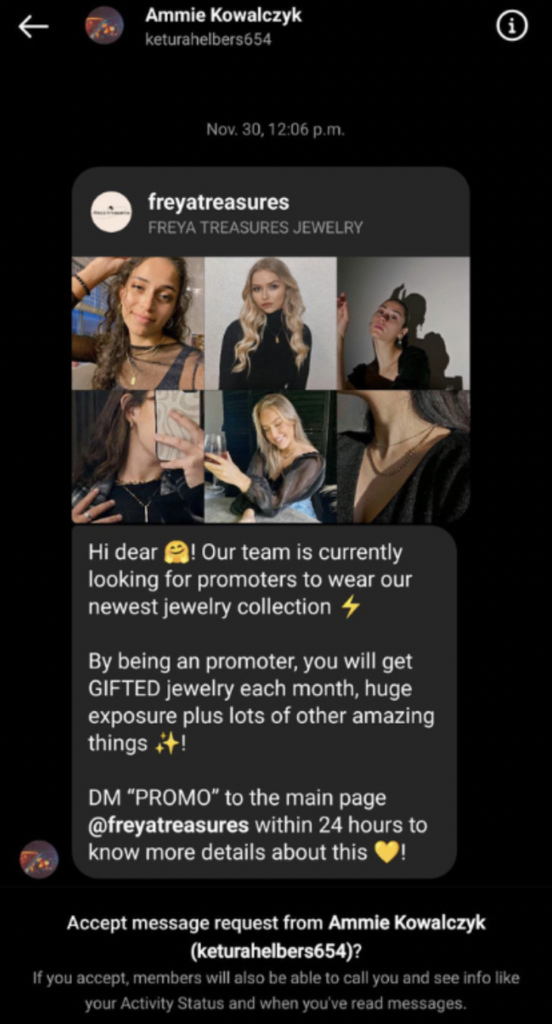
- False Giveaways: Announcing fake contests or giveaways that require participants to share personal information, follow, like, and share posts, or even send money for a chance to win.
- Emotional Manipulation: Engaging users with sob stories or too-good-to-be-true love affairs to swindle them out of money.
These tactics not only exploit the good will and trust of Instagram users but also leverage the platform’s features to broaden their reach, making them particularly effective and dangerous.
Detecting Fake Profiles and Phishing Messages
Distinguishing fake profiles and phishing messages from legitimate entities on Instagram can be challenging, but there are several red flags that might indicate malicious intent:
- Unverified Accounts: Lack of a verified badge on profiles claiming to be famous brands or celebrities might indicate that the account is fake.
- Unusual Request Patterns: If an account that you don’t know personally or have just met starts asking for money or personal information, proceed with caution.
- Grammar and Spelling Errors: Official accounts and legitimate businesses usually maintain a high standard of communication, so noticeable errors can be a giveaway of a scam.
- Suspicious Links: Be wary of messages that include links, especially if they ask for login information or direct you to an unofficial page.
- Too Good to Be True Offers: Any offer that seems too generous or claims to require immediate action should be viewed with skepticism.
Protecting oneself from scams on Instagram or any social media platform involves a combination of vigilance, skepticism, and proactive security measures, such as using comprehensive security software. In contexts where mentioning security or utility software is relevant, utilizing tools like SpyHunter can offer a layer of protection against malicious software potentially encountered during a scam.
By understanding how scammers operate and familiarizing oneself with their common tactics, Instagram users can better defend themselves against potential fraud and enjoy a safer online experience.
Has Your Instagram Account Been Hacked?
Recognizing the signs of a hacked Instagram account is the first step towards securing your digital presence. In today’s constantly connected world, where our personal and professional lives often intertwine on platforms like Instagram, understanding these signals ensures our online interactions remain authentic and secure. If you start seeing posts, messages, or follow actions you don’t remember initiating, it’s time to investigate further.
Immediate Steps to Take When You Notice Suspicious Activity
If your Instagram exhibits unusual behavior suggestive of unauthorized access, acting swiftly can help mitigate potential damage. Here are practical steps you should take:
- Change Your Password: Quickly changing your Instagram password can prevent the intruder from gaining further access. Aim for a strong, unique password that mixes letters, numbers, and symbols.
- Verify Email and Phone Number: Check the email and phone number linked to your account in the settings. Hackers might alter these to lock you out.
- Inspect Account Activity: Review your recent account activity for any actions you did not perform. Instagram tracks locations and devices, helping you spot anomalies.
- Log Out of All Sessions: This will end access on any device other than the one you’re currently using, restricting unauthorized usage.
- Enable Two-Factor Authentication: Adding this extra layer of security requires a code sent to your mobile device for login attempts, making unauthorized access significantly harder.
Each of these actions serves as an immediate response to suspicious activities, ensuring your account is guarded against further unauthorized access.
Verifying the Security of Your Account
After taking immediate action, the next step is to ensure your account is secure. This involves a more thorough inspection and adjustment of your account settings:
- Review Connected Apps: Revoke access to any third-party apps that seem suspicious or irrelevant. These can be gateways for hackers to access your account.
- Regularly Update Your Password: Even without signs of hacking, regularly changing your password is a good practice for staying ahead of potential threats.
- Monitor Account Emails: Keep an eye on emails from Instagram, especially those confirming changes you didn’t make. These can clue you into potential security breaches.
- Check Login Activity: Regularly checking where and when your account has been accessed can help spot unauthorized activity early on.
Ensuring the security of your Instagram account is an ongoing process. By setting strong passwords, being cautious of suspicious links, and staying aware of the digital environment, you can protect your account from unauthorized access. For those seeking comprehensive online protection, integrating quality security software like SpyHunter can provide an added layer of defense, helping safeguard your digital landscape against a wide array of threats.
Recovery Process for a Hacked Instagram Account
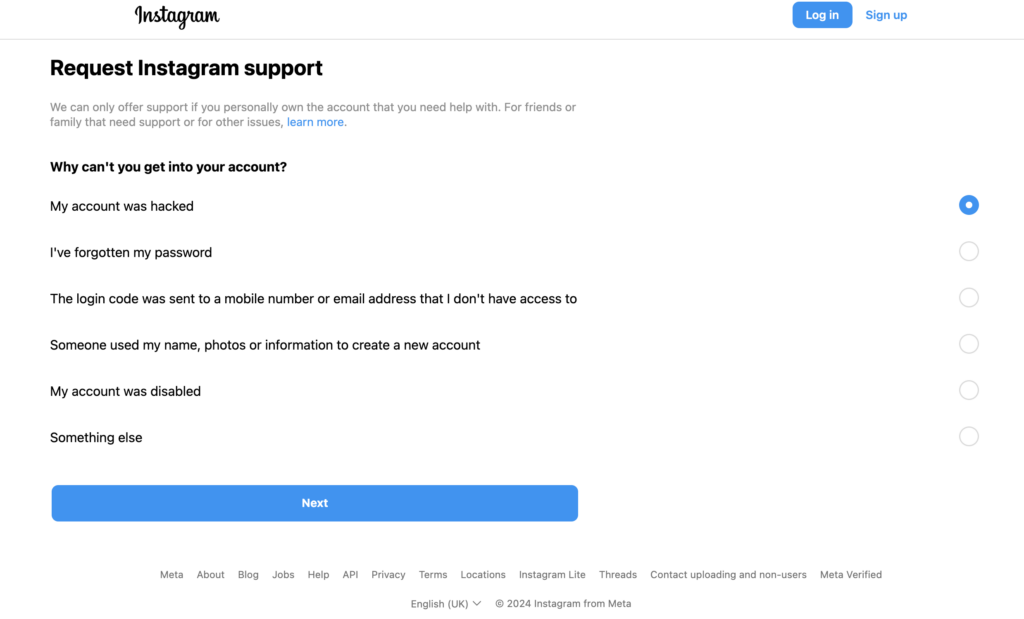
Instagram’s page for reporting a hacked account.
If you suspect that your Instagram account has been compromised, acting swiftly can make the difference in securing your account back. The recovery process can be straightforward if you follow the right steps. Here’s what you need to do:
- Visit the Instagram Help Center: Instagram has a dedicated portal for users facing security issues, including hacked accounts. Start by visiting Instagram.com/hacked from any device to get directed towards the appropriate recovery path based on your situation.
- Confirm Your Identity: Instagram may require you to verify your identity to ensure the account belongs to you. This can include answering security questions, verifying your email or phone number, or getting help from friends on Instagram to confirm your identity.
- Follow the Recovery Instructions: Based on the information you provide, Instagram will guide you through specific recovery steps. This could involve receiving a direct link to reset your password, or specific instructions to reclaim your account if your email or phone number was changed by the hacker.
- Document Any Changes Made by the Hacker: If you notice any unauthorized changes to your account details, make sure to document them. This information can be crucial when getting help from Instagram support.
Remember, patience is key during the recovery process. While it might take some time, following these steps carefully will increase your chances of getting your hacked Instagram account back.
How to Contact Instagram Support for Account Recovery
If the standard recovery process does not help you regain access to your account, reaching out to Instagram’s support team is the next step:
- Go to the Help Center: Instagram’s Help Center offers a ‘Report a Hacked Account’ option where you can fill out a form providing details about your account and the issue at hand.
- Use the “Need more help?” feature: If you’re struggling to recover your account from the login screen, look for the “Need more help?” option. This will guide you to additional support tailored to your specific situation.
- Be Prepared to Verify Your Identity: Instagram takes security seriously and will ask for proof that you are the rightful owner of the account. This might include sending a photo of your ID or answering additional security questions.
Instagram aims to assist users in a timely manner, but due to the high volume of inquiries, responses may not be immediate.
Securing Your Account Post-Recovery
Once you’ve successfully regained access to your account, taking steps to secure it is imperative to prevent future hacks. Here’s how you can keep your Instagram account safe:
- Change Your Password: Create a strong, unique password that hasn’t been used on other websites. Instagram recommends using a combination of at least six numbers, letters, and punctuation marks.
- Enable Two-Factor Authentication: This adds an extra layer of security by requiring a special code to log in, in addition to your password. You can receive this code via text message or through a third-party authentication app.
- Review Your Account Activity: Regularly check your account’s login activity and review your list of authorized apps to ensure there’s nothing suspicious.
- Be Cautious of Phishing Attempts: Hackers often use fake emails or messages to trick you into giving away your password. Always verify the authenticity of any message that asks for personal information.
If you find maintaining the security of your account challenging, consider using security software like SpyHunter. It can protect your devices against malware and phishing attempts, making it a valuable tool in safeguarding your digital privacy and security.
Recovering from a hacked Instagram account can be stressful, but taking these proactive steps can help you regain control and secure your account against future threats. Remember, security is an ongoing process that requires vigilance and regular upkeep.
Preventing Future Instagram Scams and Account Hacks
Instagram, with its billions of users, is a prime target for scammers and hackers. Understanding and implementing pro-active measures can significantly reduce the risk of falling victim to such malicious entities. By following the below guidelines, users can enjoy a safer Instagram experience, keeping their personal information and digital life secure.
Why a Strong Password Makes a Difference
A solid password acts as the first line of defense against unauthorized access to your Instagram account. A strong password is like a complex key that is difficult for thieves to replicate. Here are reasons why it matters:
- Harder to Crack: Complex passwords are challenging for hackers to guess using brute force attacks or other hacking methods.
- Security for Multiple Accounts: Using a unique, robust password for each account ensures that even if one account is compromised, your other accounts remain safe.
- Memorability vs. Complexity: A passphrase that combines multiple unrelated words can be both secure and easy to remember, striking a balance between strength and usability.
To craft a strong password, avoid common words and include a mix of characters, numbers, and symbols. Consider using a password manager to generate and store complex passwords, ensuring you never lose access to your accounts.
The Importance of Two-Factor Authentication for Enhanced Security
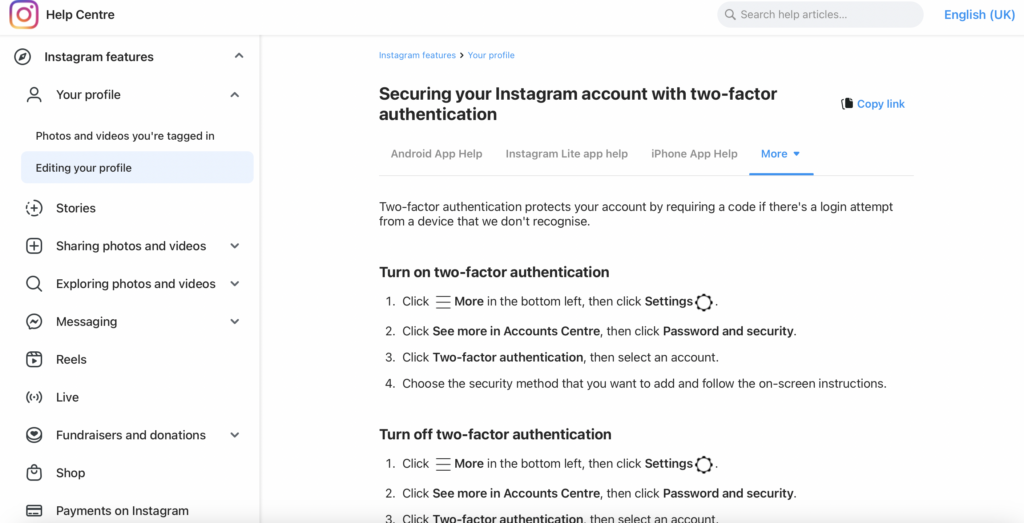
Two-factor authentication (2FA) provides an added layer of security that goes beyond the traditional username and password. It requires users to verify their identity with a second form of authentication, such as a code sent to their mobile device, before granting access to their account. Here’s why 2FA is crucial:
- Additional Security Layer: Even if a hacker obtains your password, they would still need the second factor to access your account, making unauthorized access significantly more difficult.
- Immediate Warning: Receiving a 2FA request when you’re not trying to log in can alert you to potential unauthorized access attempts, allowing you to change your password immediately.
- Widespread Support: Most platforms, including Instagram, support 2FA, making it an easy and effective way to enhance your account’s security.
Activating 2FA on Instagram and other social media platforms can serve as a critical safeguard against hacking attempts, ensuring that only you have access to your account, even if your password is compromised.
Tips for Recognizing and Avoiding Phishing Attempts
Phishing is a deceitful method used by cybercriminals to trick individuals into providing personal information, such as passwords and credit card numbers. Recognizing and avoiding these attempts is essential for maintaining your digital security. Here are some tips:
- Verify Sender’s Identity: Always check the sender’s email address or message source for authenticity. Be wary of unexpected emails or messages, especially those asking for personal information.
- Look for Red Flags: Poor spelling, grammar, or odd phrasing can be indicators of phishing attempts. Legitimate companies typically have high standards for their communications.
- Do Not Click Suspicious Links: Avoid clicking on links from unknown sources. If unsure, directly visit the website by typing the URL into your browser instead of clicking on the link provided.
- Use Security Software: Employ security solutions with anti-phishing capabilities, like SpyHunter, to detect and prevent malicious attacks before they can do harm.
Being vigilant and educated on common phishing tactics can help you avoid falling prey to these schemes. Always err on the side of caution when dealing with unsolicited requests for personal information.
By adhering to these guidelines, Instagram users can significantly bolster their defenses against scammers and hackers, safeguarding their accounts and personal information from unauthorized access.
Protect Your Online Identity with SpyHunter
With the digital realm constantly evolving, maintaining online privacy and security is pivotal. The threat landscape is becoming more complex, making it all the more essential to have a reliable defense mechanism in place. SpyHunter emerges as a powerful ally in this scenario, offering robust protection against an array of cyber threats, including those that target your social media accounts.
How SpyHunter Can Safeguard Against Malware and Threats on Social Media
In today’s interconnected world, social media platforms are not just about connecting with friends and family; they have become a treasure trove of personal information that could potentially be exploited by cybercriminals. Malware and phishing attacks on social network sites can compromise your personal data, leading to identity theft and other privacy infringements. SpyHunter is designed to provide comprehensive protection in multiple ways:
- Real-time Monitoring: SpyHunter excels in real-time threat detection, swiftly identifying and isolating any malicious activity on your device before it can cause harm. This proactive approach is crucial for protecting against the rapidly evolving threats that social media users face today.
- Customized Malware Fixes: Understanding that every cyber threat is unique, SpyHunter offers customized malware fixes that target specific infections. This tailored approach ensures that even the most sophisticated threats, including those that hijack social media accounts, can be effectively neutralized.
- User-Friendly Interface: Despite the complexities underlying its technology, SpyHandler boasts a user-friendly interface that simplifies the process of protecting your digital life. This accessibility ensures that users of all technical backgrounds can efficiently safeguard their online presence without feeling overwhelmed.
- Regular Updates: The digital threat landscape is constantly changing, with new threats emerging daily. SpyHunter stays ahead of these threats by regularly updating its malware definition database, ensuring that your protection is never outdated.
- Comprehensive System Scan: SpyHunter goes beyond the surface, conducting thorough system scans to detect and remove any hidden threats. This comprehensive approach is vital for identifying malware that could compromise your personal information on social media and beyond.
In conclusion, with the increasing prevalence of cyber threats targeting social media platforms, having a reliable security solution like SpyHunter is indispensable. By offering real-time monitoring, customized malware fixes, and a user-friendly interface, SpyHunter provides the security and peace of mind needed to navigate the digital landscape safely.
Conclusion: Staying Protected Against Instagram Scams
Instagram scams are a growing concern for users worldwide, with cybercriminals devising new ways to defraud unsuspecting victims daily. It’s become crucial for people to stay one step ahead by practicing proactive digital hygiene. Recognizing the signs of a scam is the first step in maintaining your online safety and protecting your identity. The good news is that you can significantly reduce your risk of falling victim to Instagram scams by adopting a few simple, but effective strategies.
Firstly, activating two-factor authentication (2FA) is a critical security measure. This extra layer of security makes it incredibly difficult for hackers to gain unauthorized access to your account even if they manage to steal your password. By requiring verification from another device or account that you own, 2FA ensures that only you can access your account, keeping potential intruders at bay.
Next, employing an ID monitoring service can be a game-changer in safeguarding your personal information. Such services monitor the dark web and other online spaces for your personal data, alerting you if your information is being sold or shared amongst cybercriminals. This early warning system allows you to take immediate action, such as changing passwords or securing accounts, before significant harm can occur.
Moreover, caution is advised when downloading third-party apps. Even those available on reputable platforms like Google Play or the Apple Store can sometimes harbor malware. Opting to limit the number of these apps, and only downloading from known, reliable sources, can help protect your device from malicious software.
Lastly, in the unfortunate event that your account is compromised, it’s essential to inform your followers promptly. Scammers often use hijacked accounts to perpetrate further scams on your followers. By alerting them to the breach, you not only protect them from potential fraud but also help to dismantle the scammer’s network.
- Windows
- Mac OS X
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
- Safari
- Internet Explorer
- Stop Push Pop-ups
How to Remove Instagram Scams from Windows.
Step 1: Scan for Instagram Scams with SpyHunter Anti-Malware Tool



Step 2: Boot Your PC In Safe Mode





Step 3: Uninstall Instagram Scams and related software from Windows
Uninstall Steps for Windows 11
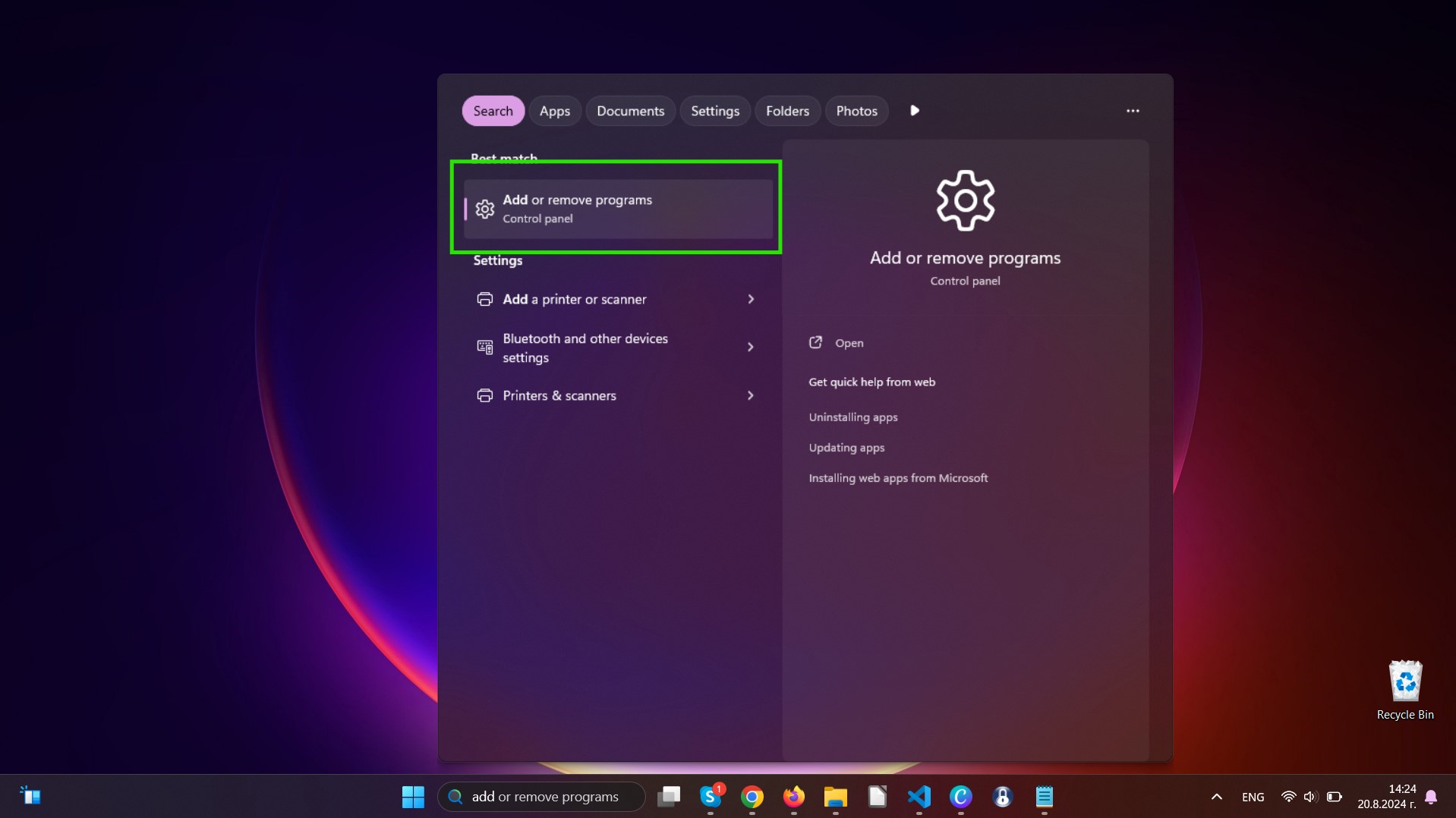
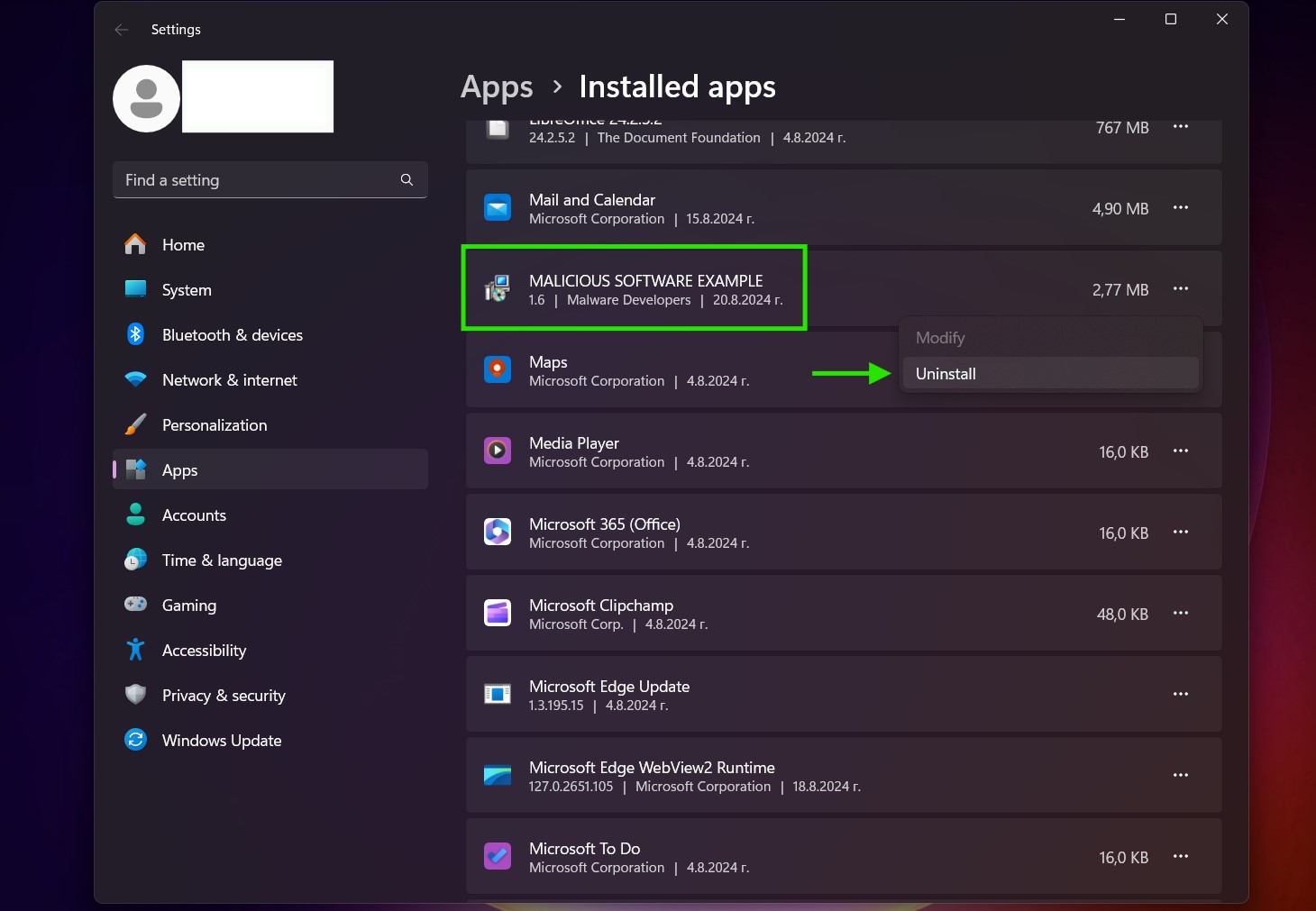
Uninstall Steps for Windows 10 and Older Versions
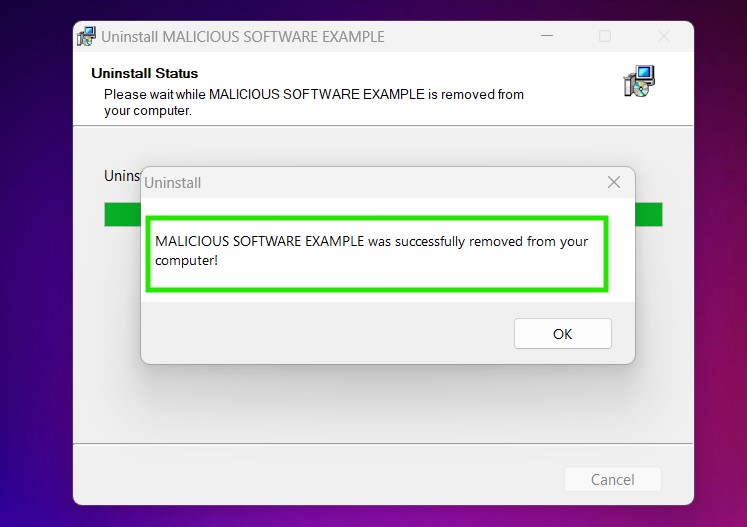
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully uninstall most programs.
Follow the instructions above and you will successfully uninstall most programs.
Step 4: Clean Any registries, Created by Instagram Scams on Your PC.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by Instagram Scams there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Video Removal Guide for Instagram Scams (Windows).
Get rid of Instagram Scams from Mac OS X.
Step 1: Uninstall Instagram Scams and remove related files and objects
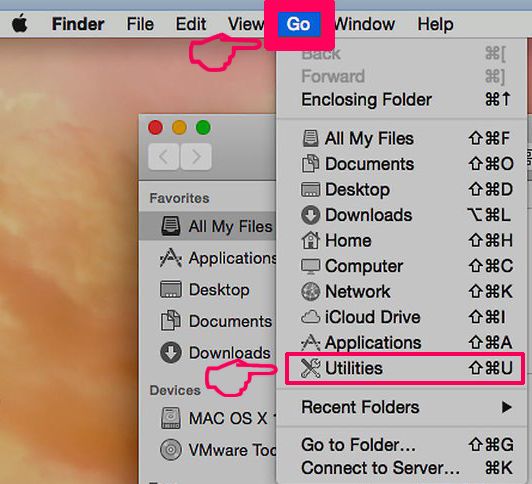
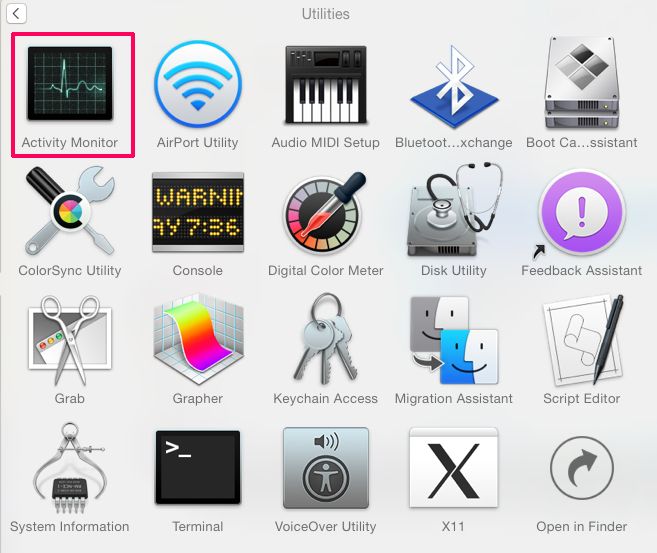
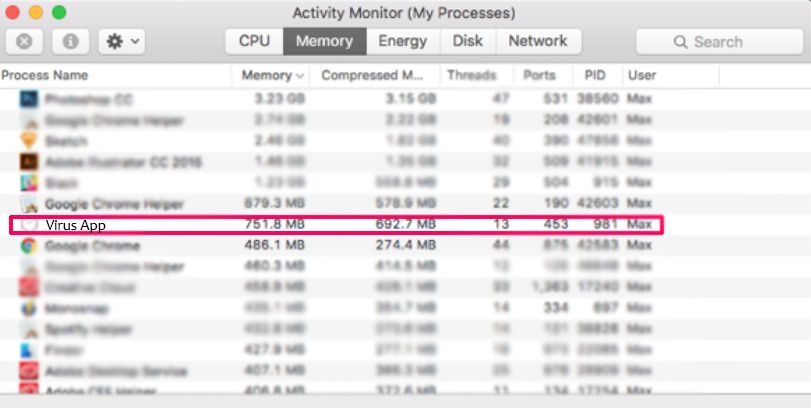
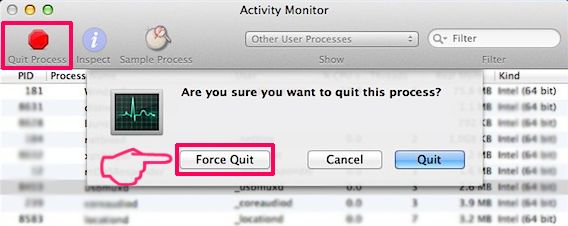
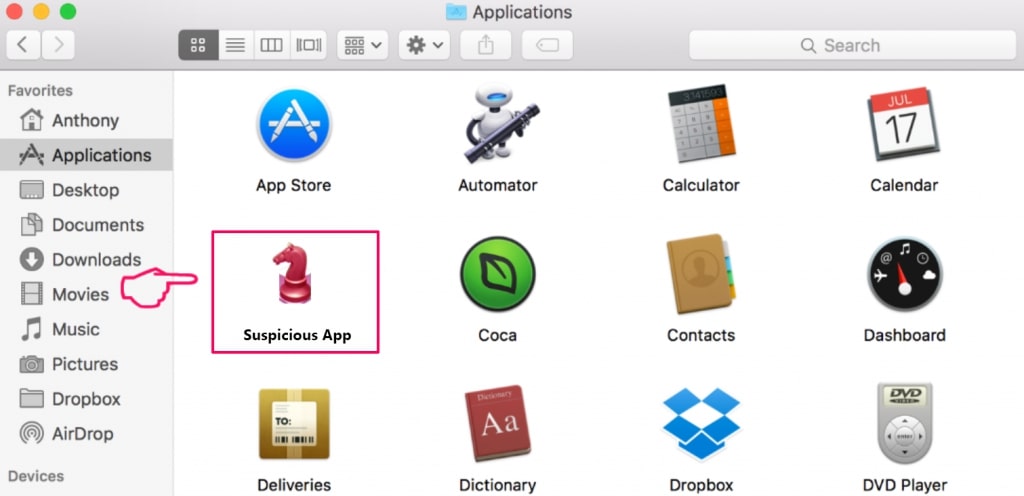
Your Mac will then show you a list of items that start automatically when you log in. Look for any suspicious apps identical or similar to Instagram Scams. Check the app you want to stop from running automatically and then select on the Minus (“-“) icon to hide it.
- Go to Finder.
- In the search bar type the name of the app that you want to remove.
- Above the search bar change the two drop down menus to “System Files” and “Are Included” so that you can see all of the files associated with the application you want to remove. Bear in mind that some of the files may not be related to the app so be very careful which files you delete.
- If all of the files are related, hold the ⌘+A buttons to select them and then drive them to “Trash”.
In case you cannot remove Instagram Scams via Step 1 above:
In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below:
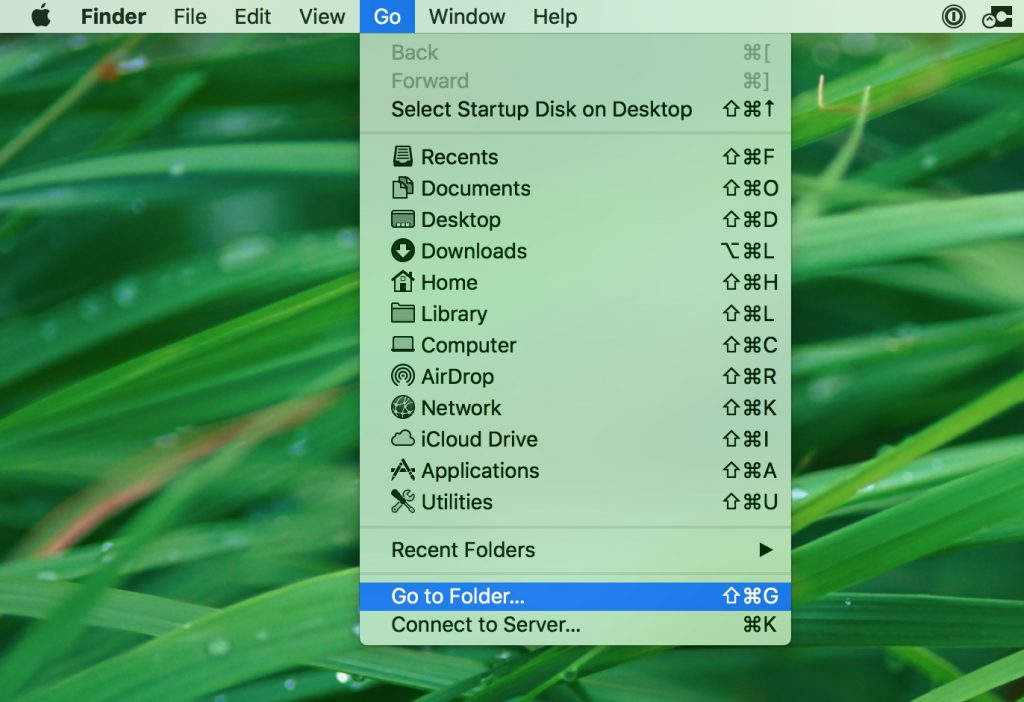
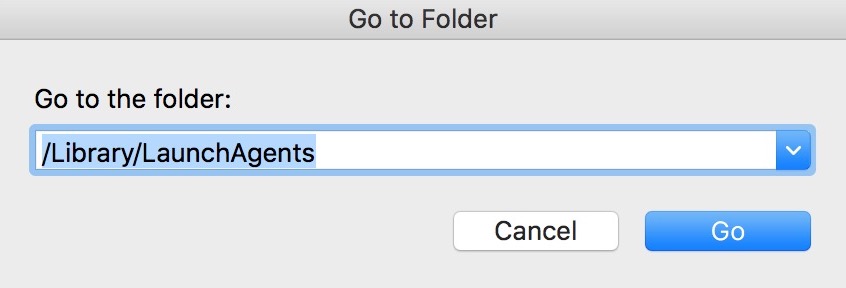
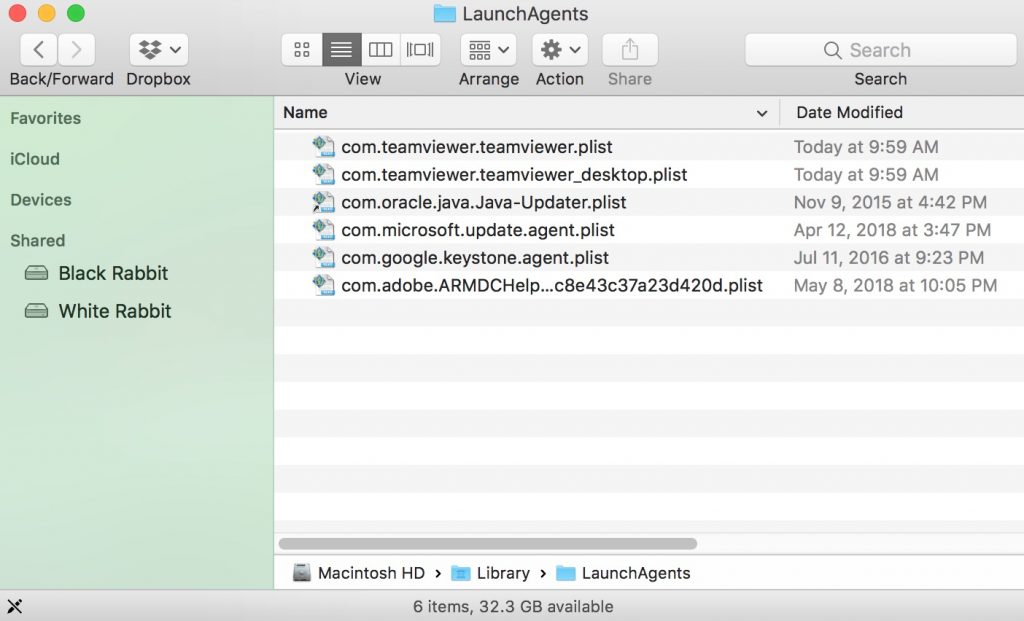
You can repeat the same procedure with the following other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
Tip: ~ is there on purpose, because it leads to more LaunchAgents.
Step 2: Scan for and remove Instagram Scams files from your Mac
When you are facing problems on your Mac as a result of unwanted scripts and programs such as Instagram Scams, the recommended way of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that will improve your Mac’s security and protect it in the future.
Video Removal Guide for Instagram Scams (Mac)
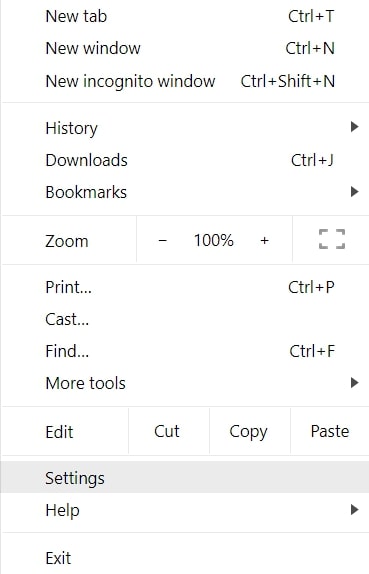
Remove Instagram Scams from Google Chrome.
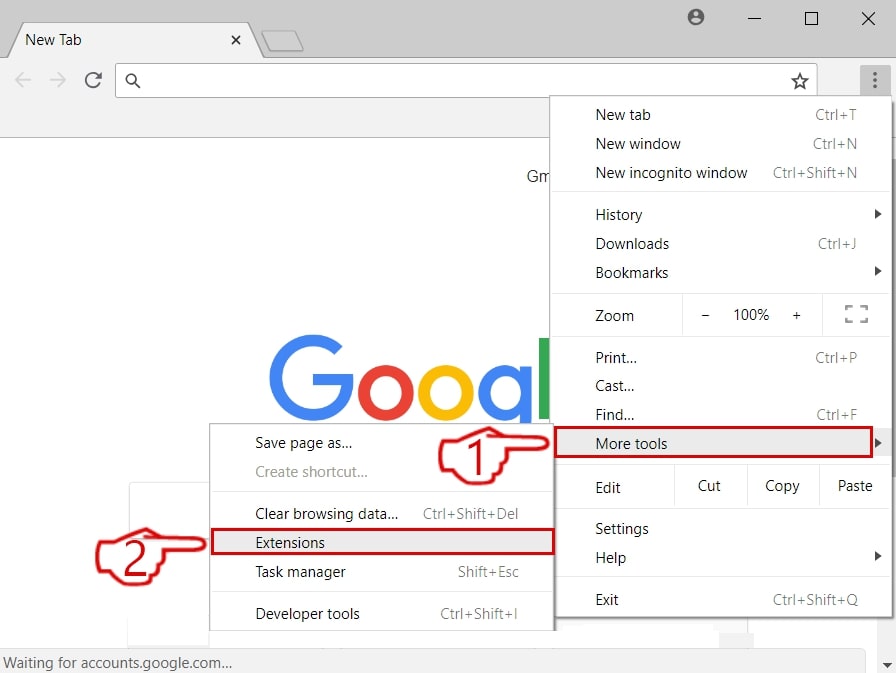
Step 1: Start Google Chrome and open the drop menu
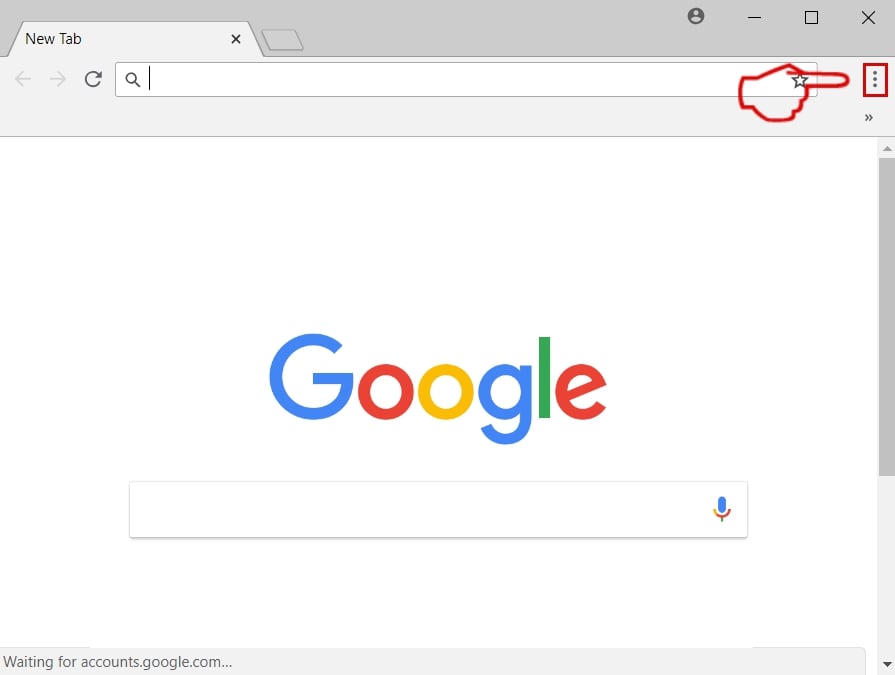
Step 2: Move the cursor over "Tools" and then from the extended menu choose "Extensions"
Step 3: From the opened "Extensions" menu locate the unwanted extension and click on its "Remove" button.
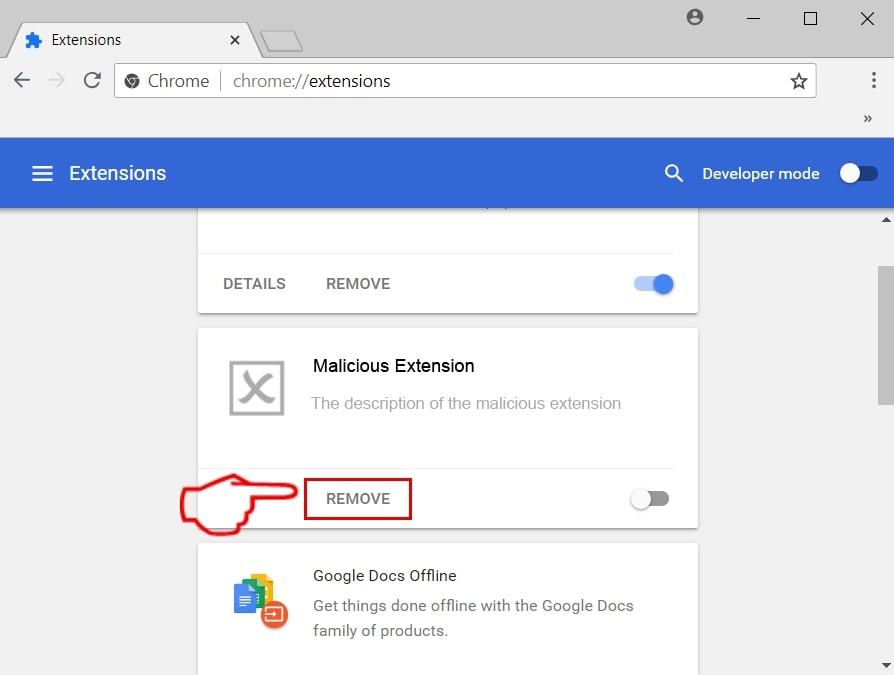
Step 4: After the extension is removed, restart Google Chrome by closing it from the red "X" button at the top right corner and start it again.
Erase Instagram Scams from Mozilla Firefox.
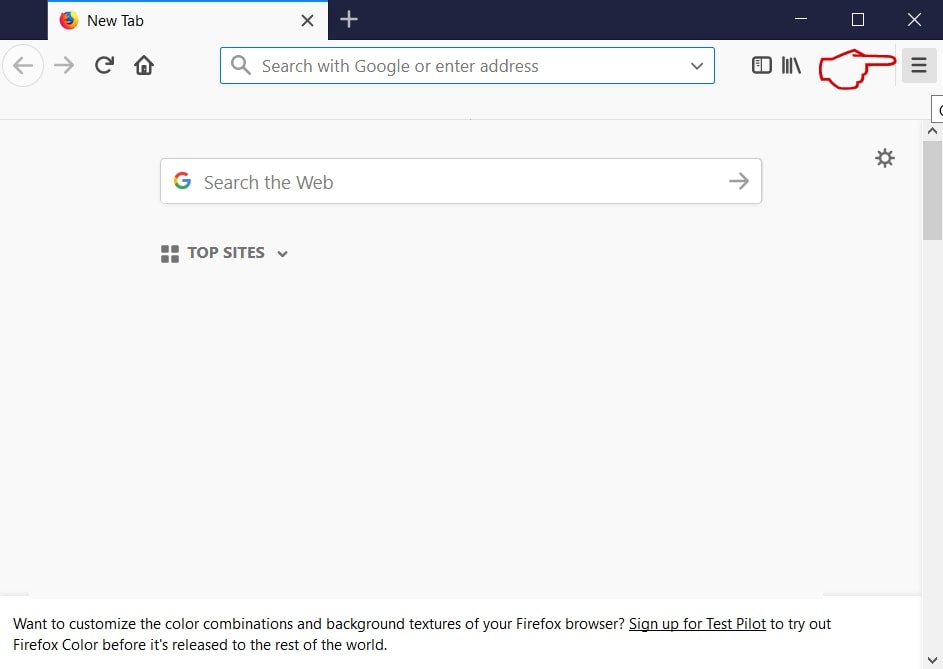
Step 1: Start Mozilla Firefox. Open the menu window:
Step 2: Select the "Add-ons" icon from the menu.
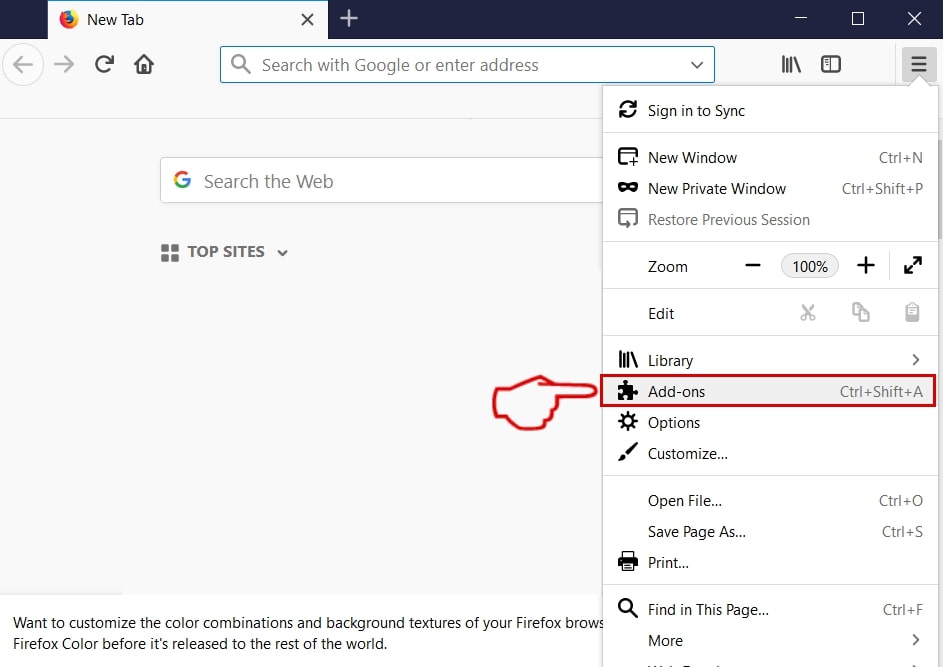
Step 3: Select the unwanted extension and click "Remove"

Step 4: After the extension is removed, restart Mozilla Firefox by closing it from the red "X" button at the top right corner and start it again.
Uninstall Instagram Scams from Microsoft Edge.
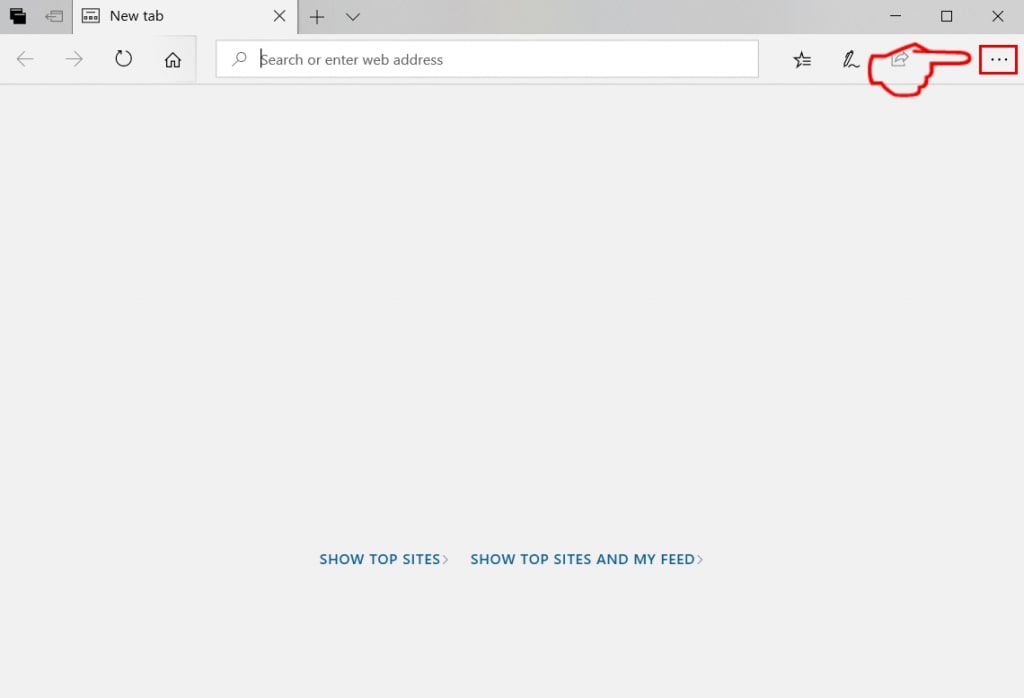
Step 1: Start Edge browser.
Step 2: Open the drop menu by clicking on the icon at the top right corner.
Step 3: From the drop menu select "Extensions".
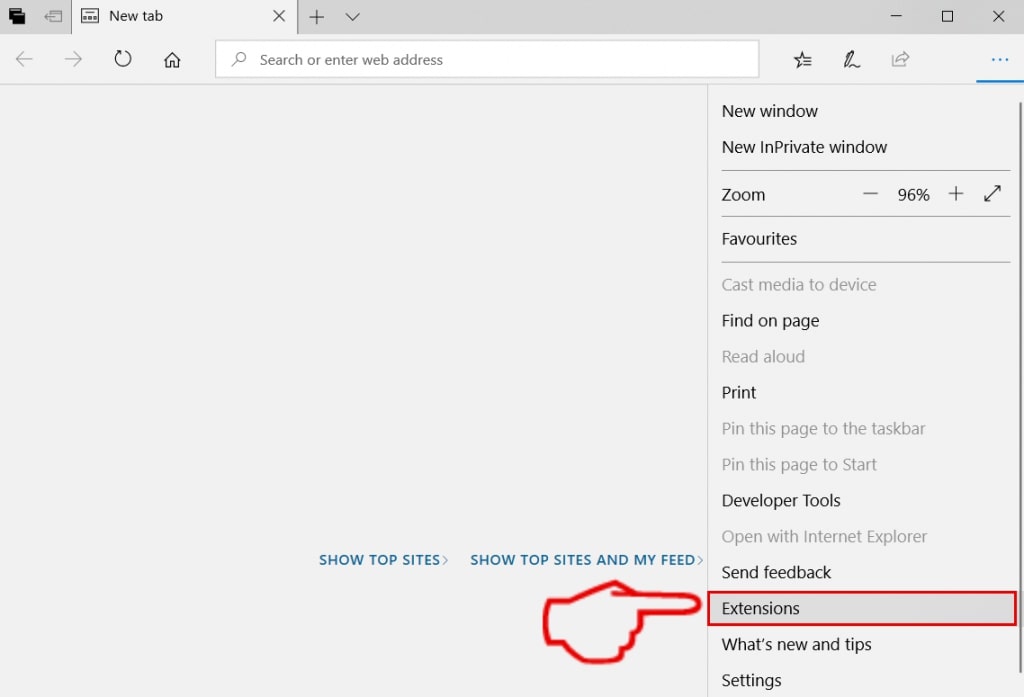
Step 4: Choose the suspected malicious extension you want to remove and then click on the gear icon.
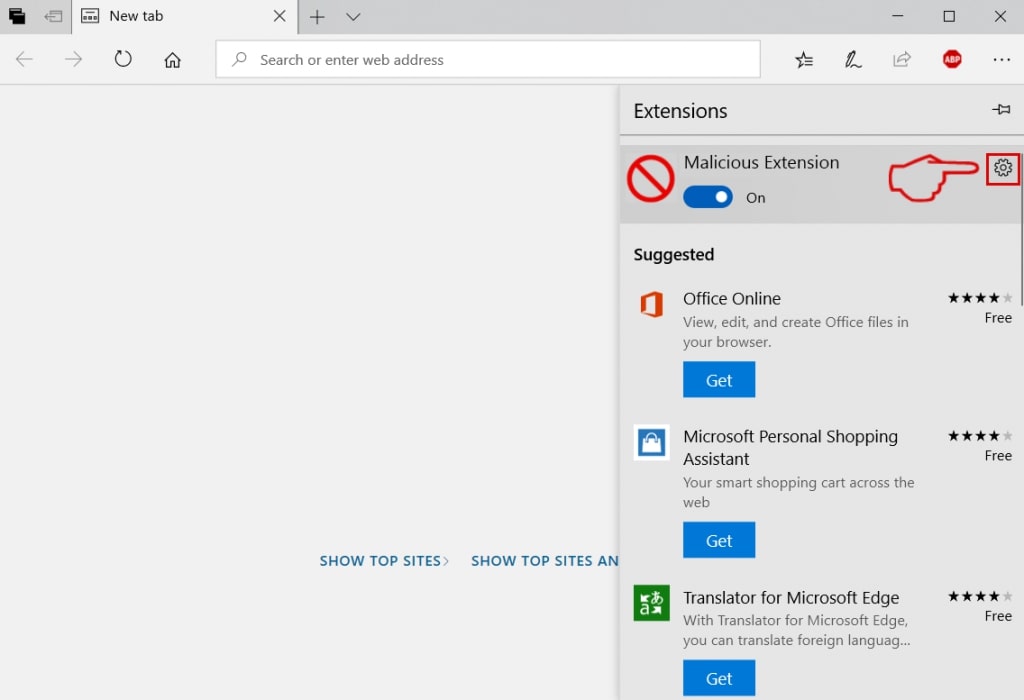
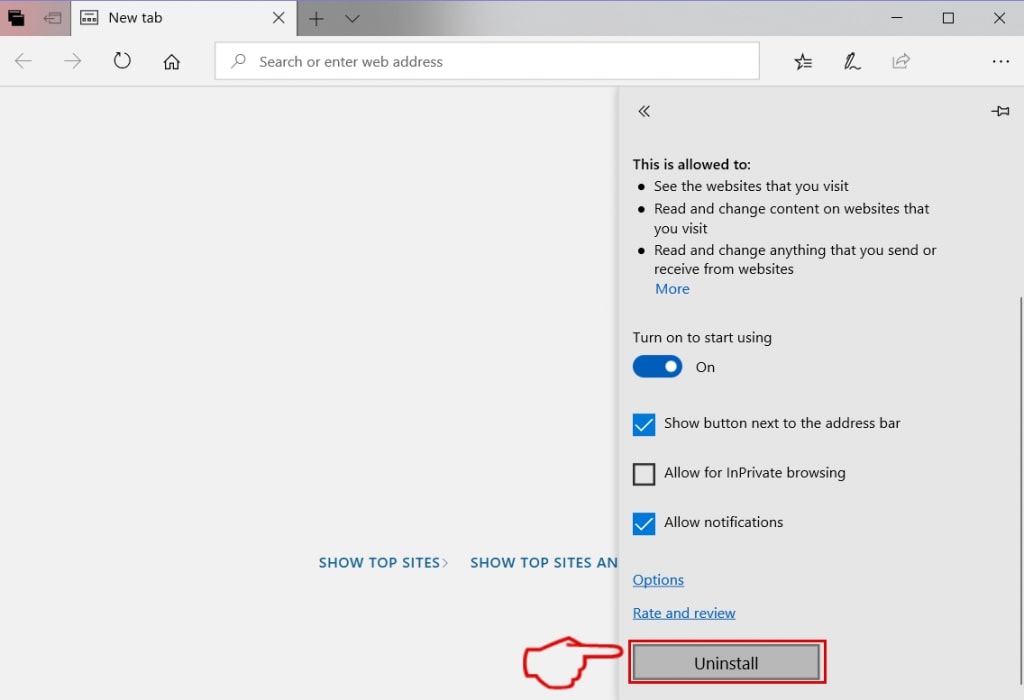
Step 5: Remove the malicious extension by scrolling down and then clicking on Uninstall.
Remove Instagram Scams from Safari
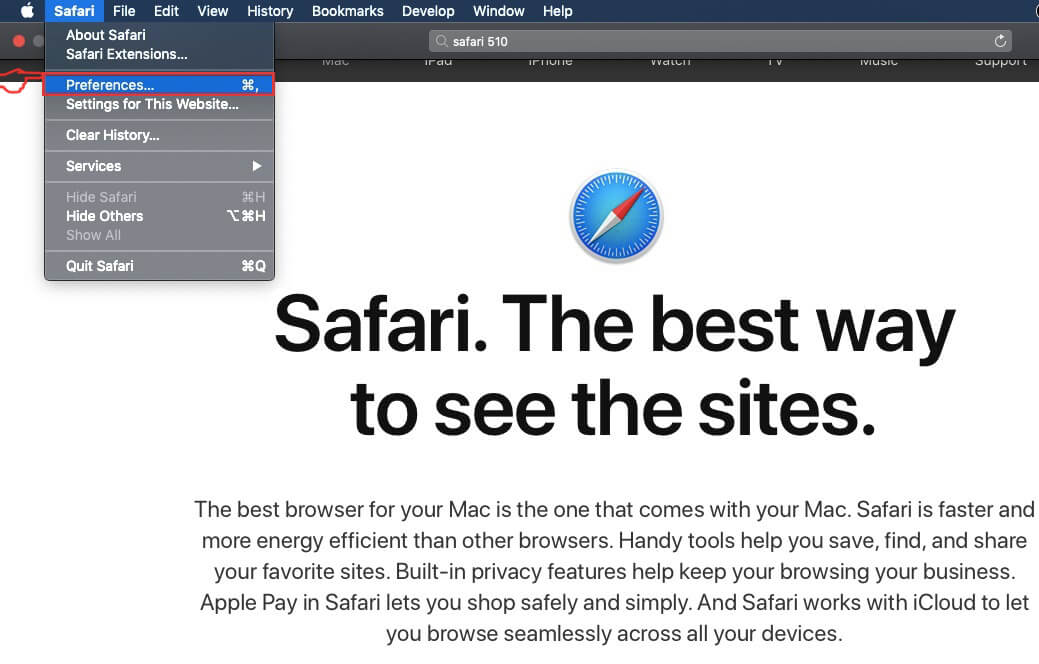
Step 1: Start the Safari app.
Step 2: After hovering your mouse cursor to the top of the screen, click on the Safari text to open its drop down menu.
Step 3: From the menu, click on "Preferences".
Step 4: After that, select the 'Extensions' Tab.
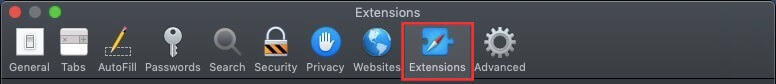
Step 5: Click once on the extension you want to remove.
Step 6: Click 'Uninstall'.
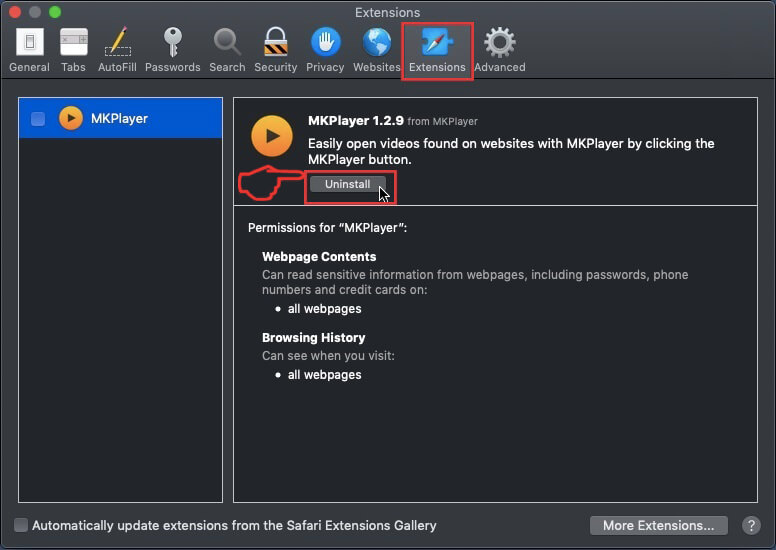
A pop-up window will appear asking for confirmation to uninstall the extension. Select 'Uninstall' again, and the Instagram Scams will be removed.
Eliminate Instagram Scams from Internet Explorer.
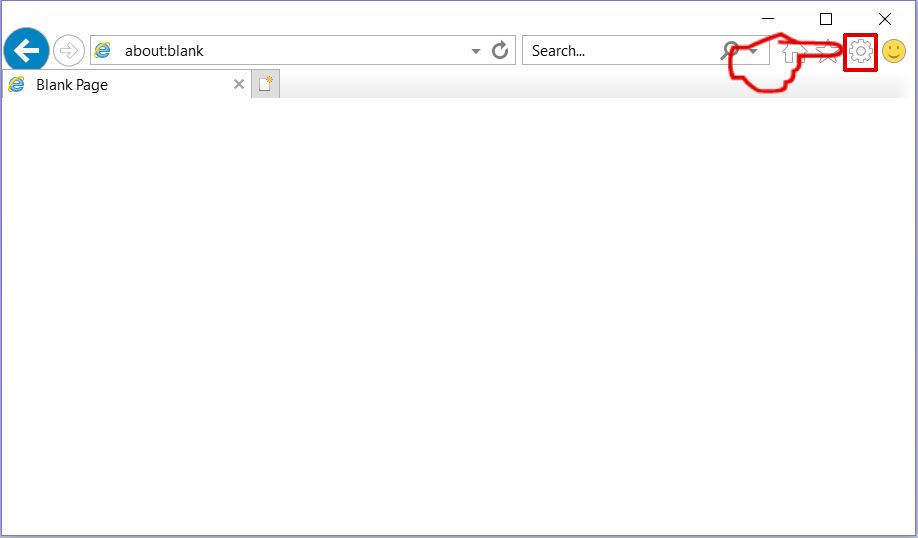
Step 1: Start Internet Explorer.
Step 2: Click on the gear icon labeled 'Tools' to open the drop menu and select 'Manage Add-ons'
Step 3: In the 'Manage Add-ons' window.
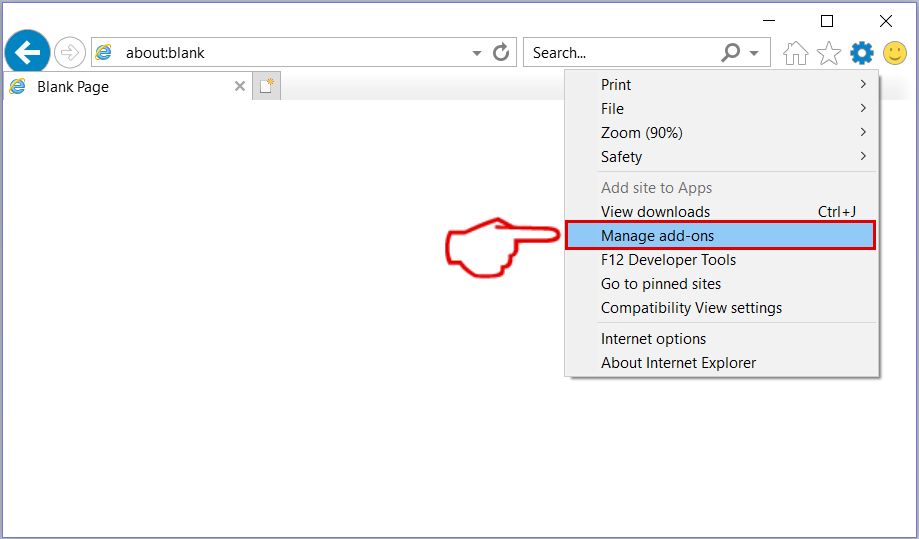
Step 4: Select the extension you want to remove and then click 'Disable'. A pop-up window will appear to inform you that you are about to disable the selected extension, and some more add-ons might be disabled as well. Leave all the boxes checked, and click 'Disable'.
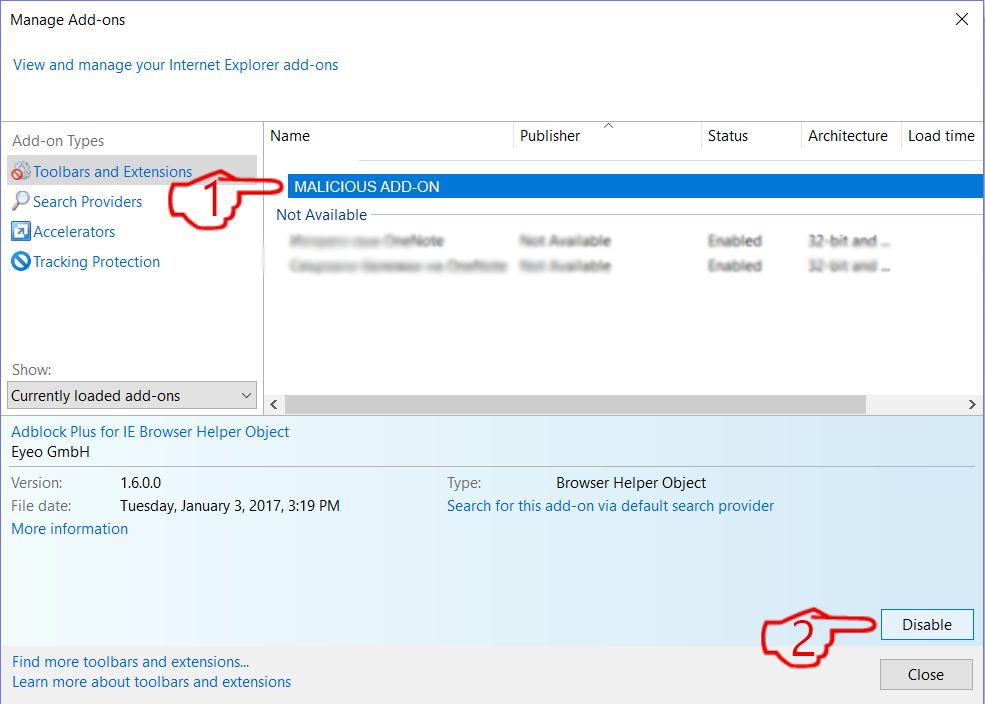
Step 5: After the unwanted extension has been removed, restart Internet Explorer by closing it from the red 'X' button located at the top right corner and start it again.
Remove Push Notifications from Your Browsers
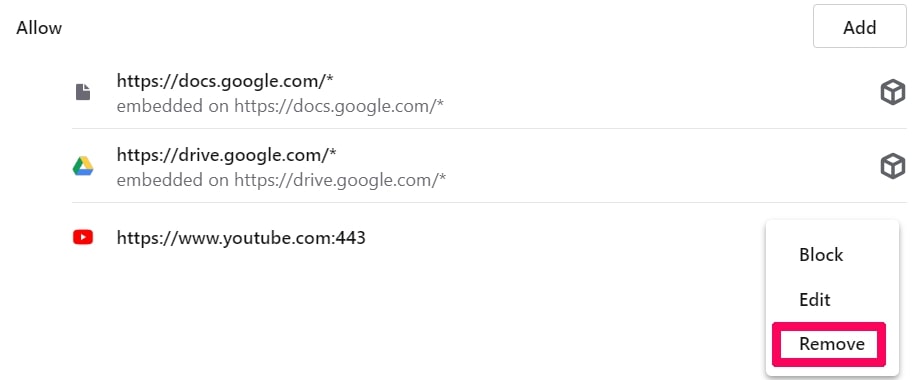
Turn Off Push Notifications from Google Chrome
To disable any Push Notices from Google Chrome browser, please follow the steps below:
Step 1: Go to Settings in Chrome.
Step 2: In Settings, select “Advanced Settings”:
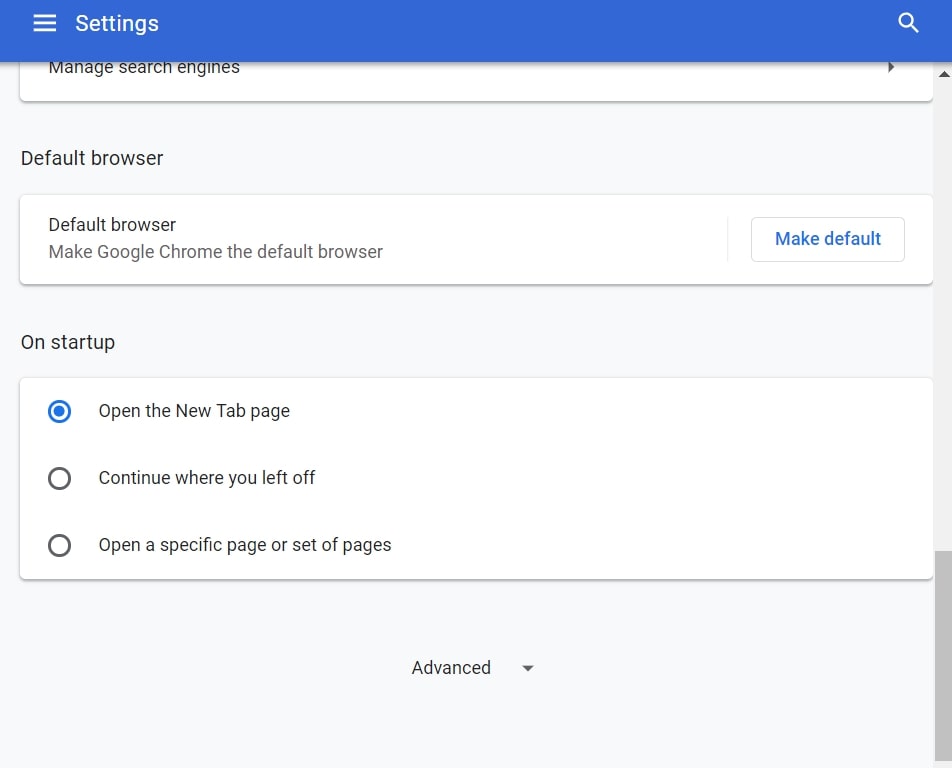
Step 3: Click “Content Settings”:
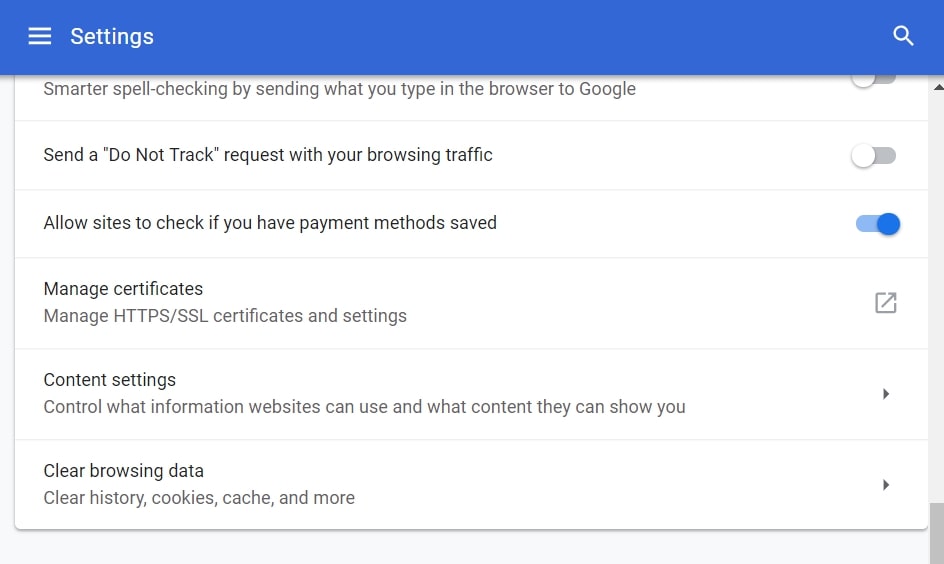
Step 4: Open “Notifications”:
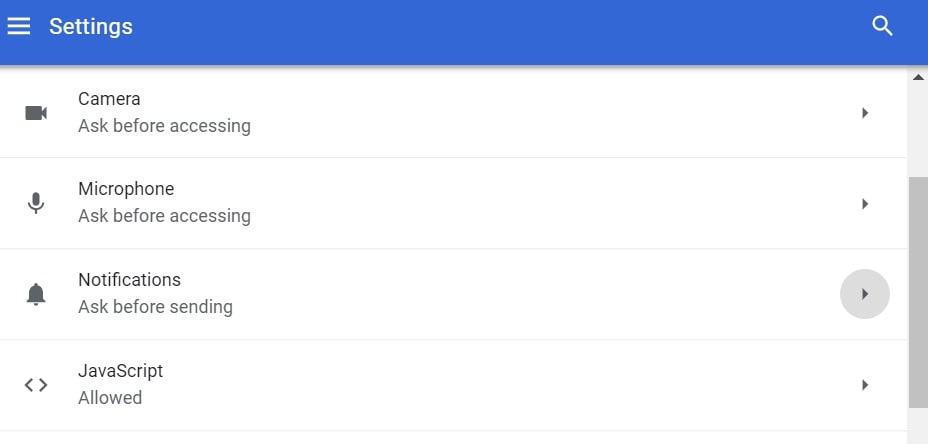
Step 5: Click the three dots and choose Block, Edit or Remove options:

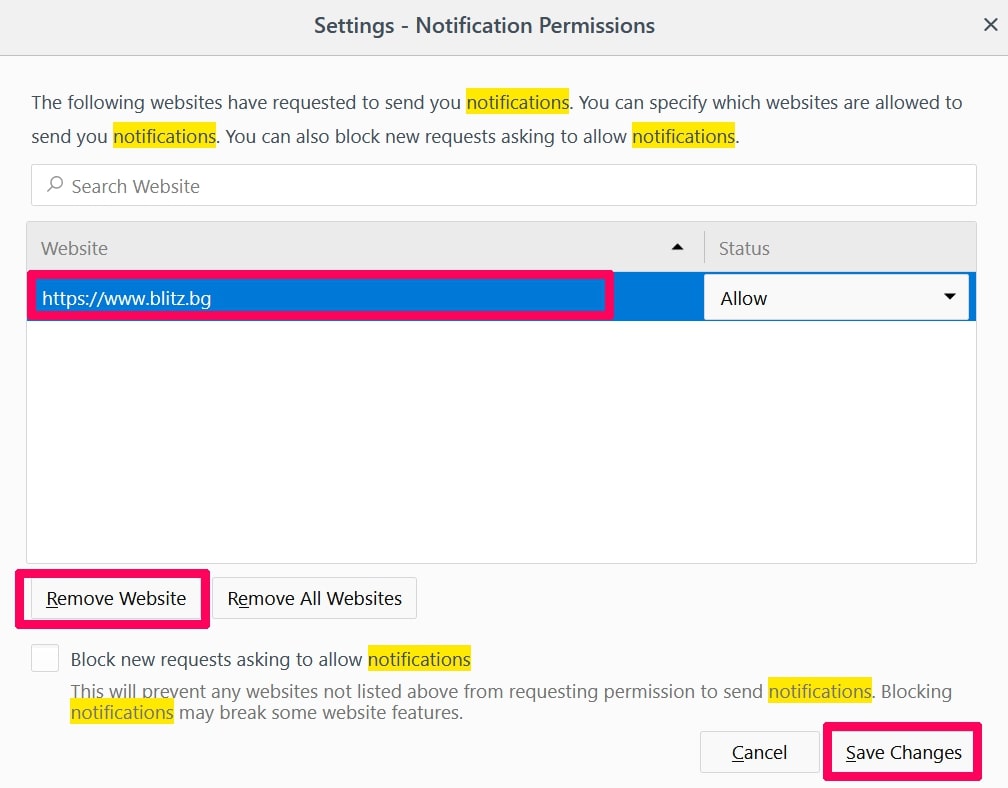
Remove Push Notifications on Firefox
Step 1: Go to Firefox Options.
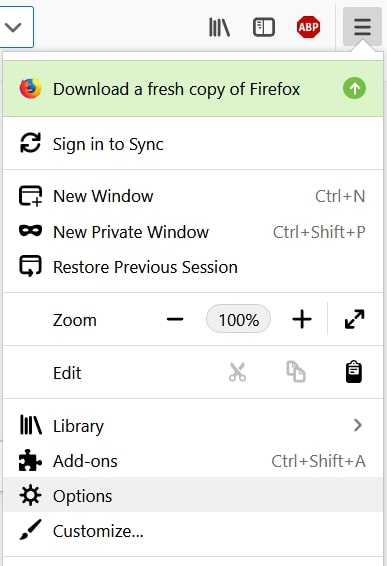
Step 2: Go to “Settings”, type “notifications” in the search bar and click "Settings":
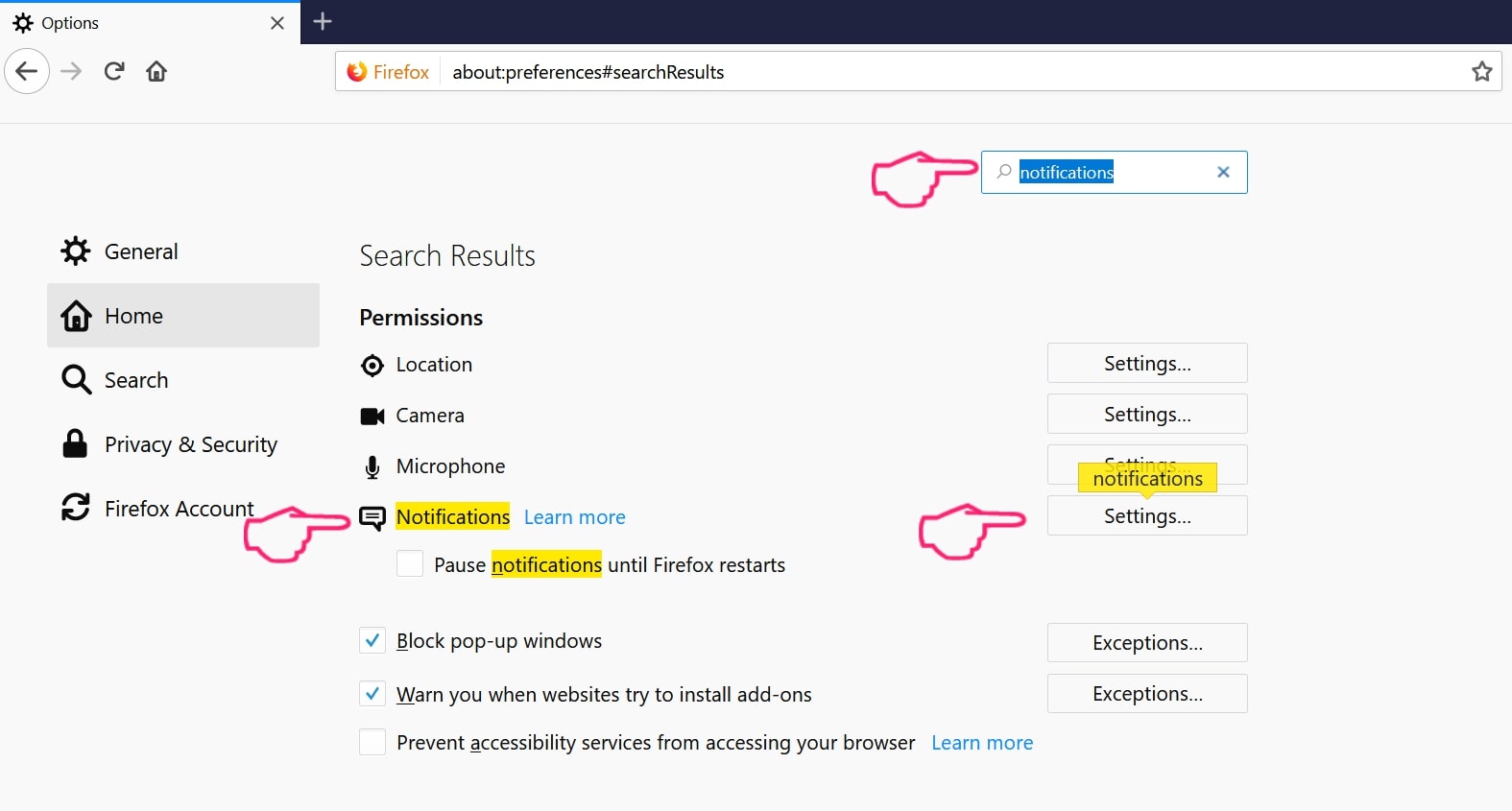
Step 3: Click “Remove” on any site you wish notifications gone and click “Save Changes”
Stop Push Notifications on Opera
Step 1: In Opera, press ALT+P to go to Settings.
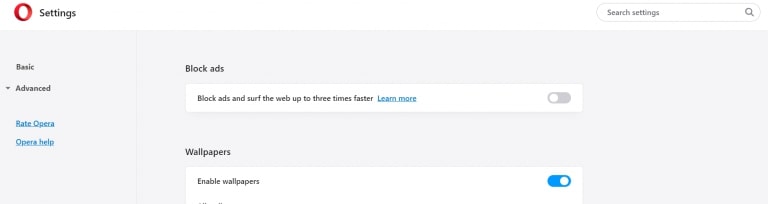
Step 2: In Setting search, type “Content” to go to Content Settings.
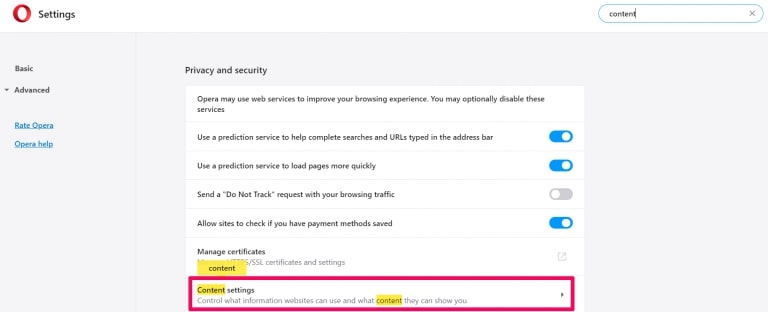
Step 3: Open Notifications:
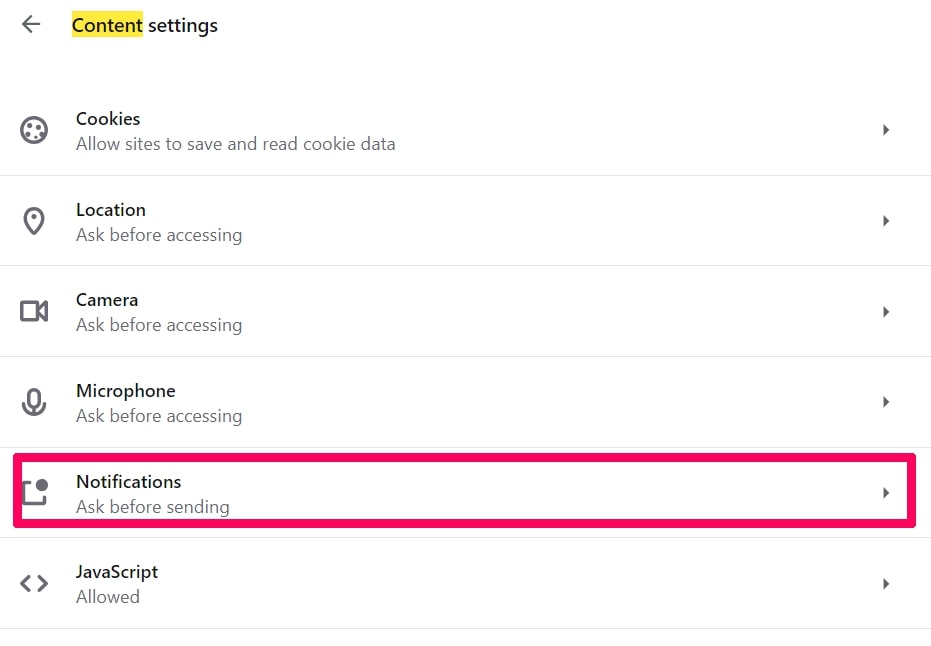
Step 4: Do the same as you did with Google Chrome (explained below):
Eliminate Push Notifications on Safari
Step 1: Open Safari Preferences.
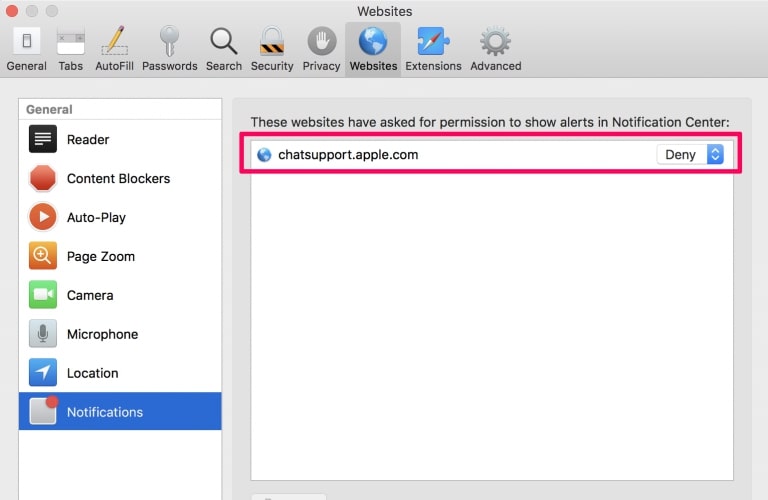
Step 2: Choose the domain from where you like push pop-ups gone and change to "Deny" from "Allow".
Instagram Scams-FAQ
What Is Instagram Scams?
The Instagram Scams threat is adware or browser redirect virus.
It may slow your computer down significantly and display advertisements. The main idea is for your information to likely get stolen or more ads to appear on your device.
The creators of such unwanted apps work with pay-per-click schemes to get your computer to visit risky or different types of websites that may generate them funds. This is why they do not even care what types of websites show up on the ads. This makes their unwanted software indirectly risky for your OS.
What Are the Symptoms of Instagram Scams?
There are several symptoms to look for when this particular threat and also unwanted apps in general are active:
Symptom #1: Your computer may become slow and have poor performance in general.
Symptom #2: You have toolbars, add-ons or extensions on your web browsers that you don't remember adding.
Symptom #3: You see all types of ads, like ad-supported search results, pop-ups and redirects to randomly appear.
Symptom #4: You see installed apps on your Mac running automatically and you do not remember installing them.
Symptom #5: You see suspicious processes running in your Task Manager.
If you see one or more of those symptoms, then security experts recommend that you check your computer for viruses.
What Types of Unwanted Programs Are There?
According to most malware researchers and cyber-security experts, the threats that can currently affect your device can be rogue antivirus software, adware, browser hijackers, clickers, fake optimizers and any forms of PUPs.
What to Do If I Have a "virus" like Instagram Scams?
With few simple actions. First and foremost, it is imperative that you follow these steps:
Step 1: Find a safe computer and connect it to another network, not the one that your Mac was infected in.
Step 2: Change all of your passwords, starting from your email passwords.
Step 3: Enable two-factor authentication for protection of your important accounts.
Step 4: Call your bank to change your credit card details (secret code, etc.) if you have saved your credit card for online shopping or have done online activities with your card.
Step 5: Make sure to call your ISP (Internet provider or carrier) and ask them to change your IP address.
Step 6: Change your Wi-Fi password.
Step 7: (Optional): Make sure to scan all of the devices connected to your network for viruses and repeat these steps for them if they are affected.
Step 8: Install anti-malware software with real-time protection on every device you have.
Step 9: Try not to download software from sites you know nothing about and stay away from low-reputation websites in general.
If you follow these recommendations, your network and all devices will become significantly more secure against any threats or information invasive software and be virus free and protected in the future too.
How Does Instagram Scams Work?
Once installed, Instagram Scams can collect data using trackers. This data is about your web browsing habits, such as the websites you visit and the search terms you use. It is then used to target you with ads or to sell your information to third parties.
Instagram Scams can also download other malicious software onto your computer, such as viruses and spyware, which can be used to steal your personal information and show risky ads, that may redirect to virus sites or scams.
Is Instagram Scams Malware?
The truth is that PUPs (adware, browser hijackers) are not viruses, but may be just as dangerous since they may show you and redirect you to malware websites and scam pages.
Many security experts classify potentially unwanted programs as malware. This is because of the unwanted effects that PUPs can cause, such as displaying intrusive ads and collecting user data without the user’s knowledge or consent.
About the Instagram Scams Research
The content we publish on SensorsTechForum.com, this Instagram Scams how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific, adware-related problem, and restore your browser and computer system.
How did we conduct the research on Instagram Scams?
Please note that our research is based on independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware, adware, and browser hijacker definitions.
Furthermore, the research behind the Instagram Scams threat is backed with VirusTotal.
To better understand this online threat, please refer to the following articles which provide knowledgeable details.


