 This article is created to show you what are the most desired and effective hacking gadgets in 2020 and what makes them so special and sought after.
This article is created to show you what are the most desired and effective hacking gadgets in 2020 and what makes them so special and sought after.
SIDENOTE: This post was originally published in August 2017. But we gave it an update in January 2020.
The last few years have seen an Information Technology revolution. With rapid developments in both the hardware and software part of a machine, there has also been a progress in cyber-crime and hacking devices. The trend from small and separated cyber-criminals has shifted towards cyber-criminal organizations who rely on zero days, data leaks and many exploits to combine their powerful hacking tools in order to spread their malware. The development of cryptocurrencies which are difficult to track, such as BitCoin and Monero has resulted in many crooks using them to launder their money over the web and their increase in popularity has made them more accessible than ever. And now, with the rising of Internet of Things (IoT) the situation with hacking devices and tools becomes a whole new ball game. Here are the hacking gadgets which we believe are extremely well-engineered and can become the nightmare of any secure device, provided the right set of skills.
Disclaimer: SensorsTechForum is sharing this information for educational purpose only. Any use of prohibited hacking devices may result in the user facing the consequences of it.
iPhone, iPad GPS Spy Audio USB Cable (Lightning)
At initial glance, this hacking device looks like your typical Lightning USB port for mobile devices. However, it features a very well concealed SIM-card slot, combined with a GPS device and a real-time tracking via GPRS system. The way this hacking device operates is you have to insert your SIM card within the cable. Since this SIM card has, it’s own cell-phone number, you can call it every-time you want to see if the device is connected with it and listen-in on all the sound. However, since you may not know when the victim connects his/her mobile device so that you can call, the cable also offers a voice-activated Callback. This works fairly simple – when you text the code “1111” to the phone number of the SIM card connected to the cable, it will trigger this service. The service automatically detects if there is sound over 45 decibels and if there is, the SIM-card automatically dials your phone number, so that you can listen in. And more to it than that, you can also text “DW” to receive direct location of the phone and the cable connected to it via GPS.
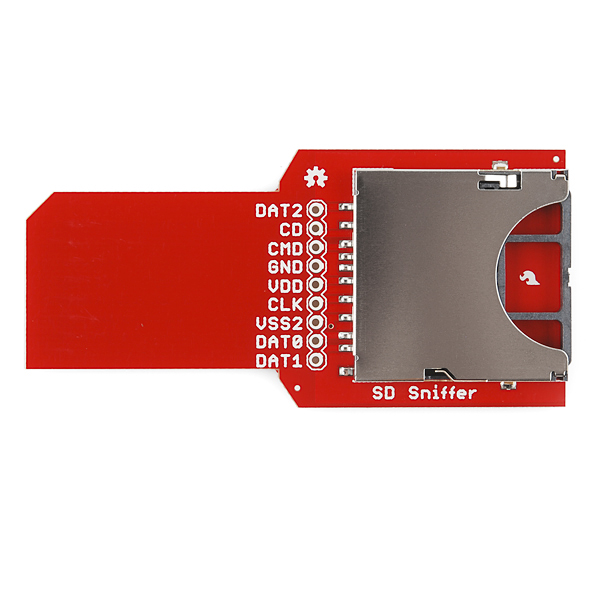
SD Sniffing Hacking Device
Created by SparkFun his extremely well-designed hacking device, looks small and rather simple, but it is created to extract important information from sophisticated devices, like logic analyzers and micro controllers. The way this SD sniffer works is that it monitors the SPI traffic, responsible for the packets, enabling it to capture crucial information which if not properly encrypted can result in the hacker obtaining credentials as well as system information from the targeted device. But this can work as long as the device has an SD socket in it with an SD card into this socket.
Wireless Password Cracker Antenna
This password cracker is probably not exactly one of the newer inventions, but it is still as effective and as used as it was when such hacking devices first appeared in public. Supporting the USB 2.0 standard, this hacking device works with WEP, WPA, WPA2, TKIP and even AES encryption. It has a wide compatibility for operating systems it works with as well. The hacking device can run on Linux, Windows versions from 2000 up until 8 and MacOS 10.5 and 10.5. Irreplaceable for wardriving brute forcing or any type of Wi-Fi attacking.
AntMiner S4 BitCoin Mining Hacking Devices
If there is a hacking device that would best represent the revolution of cryptocurrencies, this is the AndMiner by BitMain. This hacking device has been used so much that there are factories mining BitCoin with It and similar hacking devices all over the Globe. The massive adoption of mining software for the CryptoCurrency BitCoin has resulted In a total surge of its price, and it’s massive adoption for a payment method, following many alternative crypto coins, like Ethereum, Ripple, and Litecoin. The hacking device itself is among the best sought after ones, because of its power (2000 giga hashes per second) for the price it is offered. And it’s simple configuration is just a bonus to it all – all you have to do is set up the mining pool information in the hacking device, add it’s own IP address and you can start making money out of thin air. Many BitCoin farms using such hacking devices are already making millions per month, especially countries with low electricity costs.
Keyllama USB Keylogger
Being classified as one of the most undetectable software out there, Keyllama USB Keylogger is one of the USB flash drives you do not want on your computer. It does not have any software which it requires to run, and it is activated immediately after it has been plugged in. The most interesting part of this hardware keylogger is that it can also be inserted into wireless keyboards as well.
RoadMASSter-3 Forensic Hard Drive Acquisition/Duplicator and Analysis
Appropriate for both law enforcement investigators and data thieves, the RoadMASSter-3 mobile duplicator is the best suitcase of goods you can have with you when you want to create a duplicate hard drive of a device you previously have obtained. It also works well if you want to make a reserve backup of large data from one big drive to another, making it possible to support large databases and networks. The hacking device is completely portable, has a large screen and a package of different programs that are used to unlock various hard drives and SSD drives. It also has support for various media files, hashing capabilities while on the move, powerful processor and works with FireWire, USB, IDE, SATA, SAS plus SCSI.
NooElec NESDR Mini 2 USB RTL-SDR Hacker Gadget
Working as an advanced antenna that can be configured to listen in to any radio frequency it connects to, the NooElec is the perfect radio sniffing tech if you want to be portable and always listening. Primarily used to scan for police frequencies and other custom radio frequencies. A Very sensitive tool which also has the support for ADS-B scanning, trunking satellite images, and other radio-frequency related activities.
Mengshen® Spy GSM USB Mouse
This interesting mouse has nothing to do with hacking the computer It has been connected to. The mouse is attached to an audio bug hacking device which can listen to anything surrounding it via an ordinary SIM card and a microphone connected to it. And it cannot be detected in any way, except if you disassemble the mouse because the tapping hacking device is not connected to the computer directly. The way that this neat little hacker gadget does its magic is very similar to the USB cable listening device – you dial the number, and the hacking device automatically starts the bugging procedure. What is beautiful is that the battery continues to work even after the computer is turned off for around 2 hours, depending on the state of the 4200mA battery.
The Drone Defender
Created by BATTELLE, this hacker gadget can be attached to any weapon system, serving as a drone disabling device from the ground. What is beautiful about the hacking device is that wile it weighs less than 5 kg, it can be used to disable a drone from a long distance without even damaging it. The way it works is that the antenna is linked to a brute force hacking gadget which attacks the drone’s radio programming protocols, resulting in total control of the drone, which can safely land it, without having to use any firearms or other weaponry to permanently phase it out. Here is how the attack looks:
https://gfycat.com/AromaticGlamorousAzurevase
https://gfycat.com/WeeInsignificantAcornbarnacle
The drone has already become popular among police forces, especially with the new no-fly drone laws introduced in the U.S. It’s development followed many similar hacking devices, using the same methods.
The Bottom Line
With the advancements in technology, hacking devices have also seen quite a development the past few years, and these hacking devices are the commercially available ones. Now imagine what we do not know about so far and what Is not yet publicly available…
As a bottom line, be advised to check this article, since SensorsTechForum may add more hacking devices in the future and also if you have any suggestions on other hacking devices, make sure to drop a comment!
Image Sources:
Amazon.com
www.tobem.com












I love the products it all great