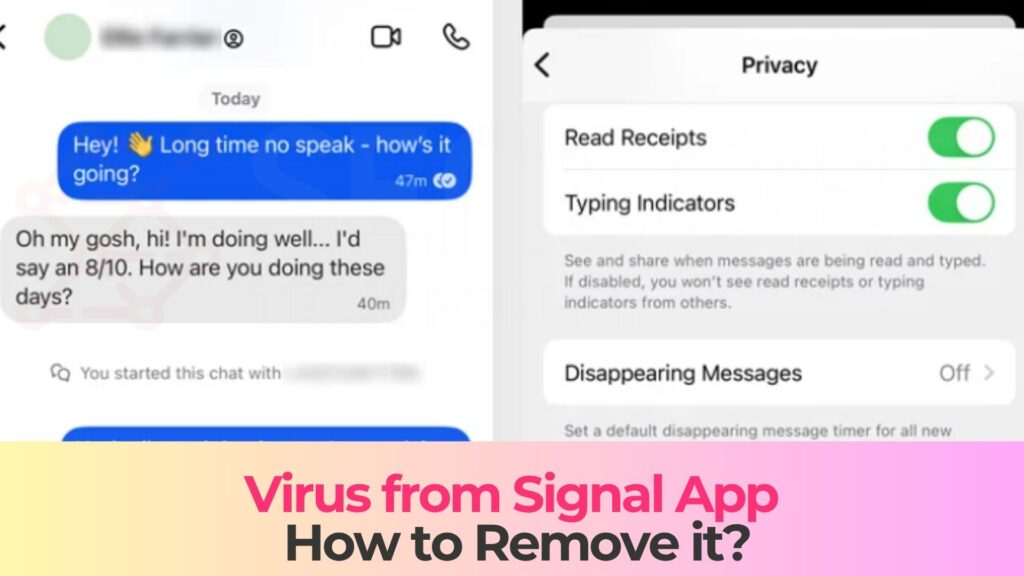
Virus from Signal App – How to Remove It
What is Virus from Signal App – How to Remove It Cybersecurity threats continue to evolve, and even trusted messaging platforms like Signal can be exploited by cybercriminals. If you suspect a virus from Signal App has affected your device,…


![Lumma Malware [Stealer] – Removal Guide [Fix] lumma malware stealer removal guide](https://cdn.sensorstechforum.com/wp-content/uploads/2026/04/lumma-malware-stealer-removal-guide-fix-1024x576.jpg)
![Rabbit Virus Malware – Removal Guide [Fix]](https://cdn.sensorstechforum.com/wp-content/uploads/2026/04/rabbit-virus-how-to-remove-it-1024x576.jpg)
![Riskware.Koala.AGen Malware – How to Remove It [Fix] riskware.koala,agen](https://cdn.sensorstechforum.com/wp-content/uploads/2026/03/Riskware.Koala_.AGen-virus-removal-guide-1024x576.jpg)
![Msedge.vg Virus – How to Remove It [Working] msedge.vg virus removal guide](https://cdn.sensorstechforum.com/wp-content/uploads/2026/03/msedge-vg-virus-removal-guide-1024x576.jpg)
![Virus.Obfuscator.AAO Malware – How to Remove It [Fix] Virus.Obfuscator.AAO Malware - How to Remove It [Fix]](https://cdn.sensorstechforum.com/wp-content/uploads/2026/03/Virus.Obfuscator-aao-1024x576.jpg)
![Verification Steps Malware – How to Remove it [Fix] Verification Steps Malware - How to Remove it [Fix]](https://cdn.sensorstechforum.com/wp-content/uploads/2026/03/complete-verification-steps-malware-removal-1024x576.jpg)
![HackTool:BAT/AutoKMS – Removal Instructions [Guide] HackTool:BAT/AutoKMS - Removal Instructions [Guide]](https://cdn.sensorstechforum.com/wp-content/uploads/2026/03/HackTool-BAT-AutoKMS-Removal-Instructions-Guide-1024x576.jpg)

![Renpy.infostealer Pop-ups Virus – Removal Steps [Fix] Renpy.infostealer Pop-ups Virus - Removal Steps [Fix]](https://cdn.sensorstechforum.com/wp-content/uploads/2026/03/Renpy-infostealer-virus-1024x576.jpg)
![Trojan.HTML/Phish – How to Remove It [Fix] trojan.html/phish virus](https://cdn.sensorstechforum.com/wp-content/uploads/2026/03/Trojan-HTML-Phish-1024x576.jpg)
![Osprivacy.exe Coin Miner Virus – Removal Steps [Fix] osprivacy.exe virus remvoal guide](https://cdn.sensorstechforum.com/wp-content/uploads/2026/03/Osprivacy-exe-virus-remvoal-guide-1024x576.jpg)
![CrossPatch Malware – Removal Guide [Fix] CrossPatch Malware](https://cdn.sensorstechforum.com/wp-content/uploads/2026/03/crosspatch-virus-removal-guide-1024x576.jpg)
![TinyTask777setup.exe Virus – How to Remove It [Fix] tinytask77setup.exe virus removal guide](https://cdn.sensorstechforum.com/wp-content/uploads/2026/03/tinytask777setup-exe-virus-removal-guide-1024x576.jpg)

![ProfluxeflowAiRC Virus – How to Remove It [Fix Guide] ProfluxeflowAiRC-virus-ads-removal-guide](https://cdn.sensorstechforum.com/wp-content/uploads/2026/03/ProfluxeflowAiRC-virus-ads-removal-guide-1024x576.jpg)
![Contebrew Virus – How to Remove It [Fix] contebrew virus removal guide](https://cdn.sensorstechforum.com/wp-content/uploads/2026/02/Contebrew-virus-removal-guide-1024x576.jpg)