Remove 844-763-5838 Tech Support Scam
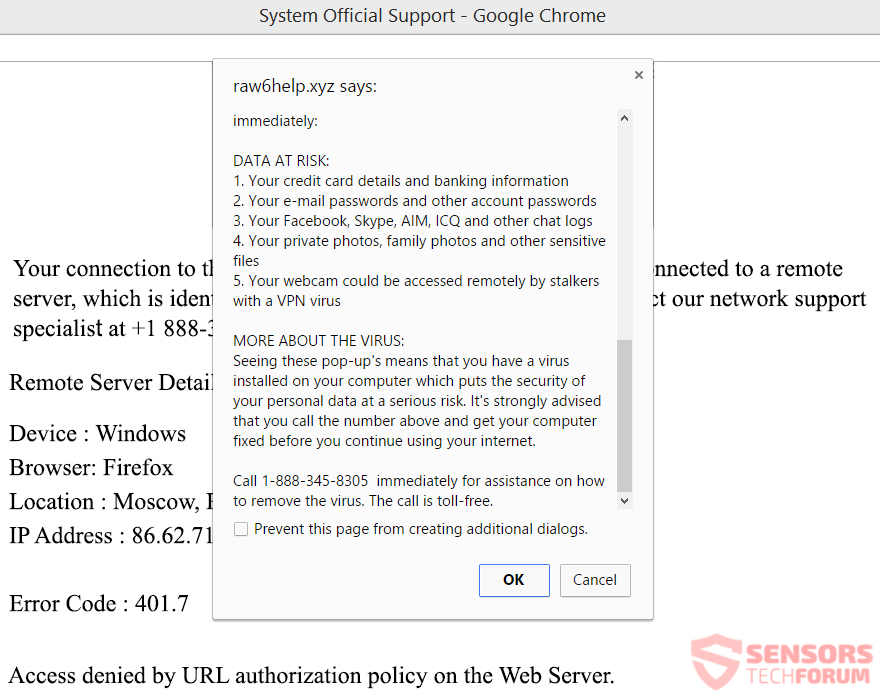
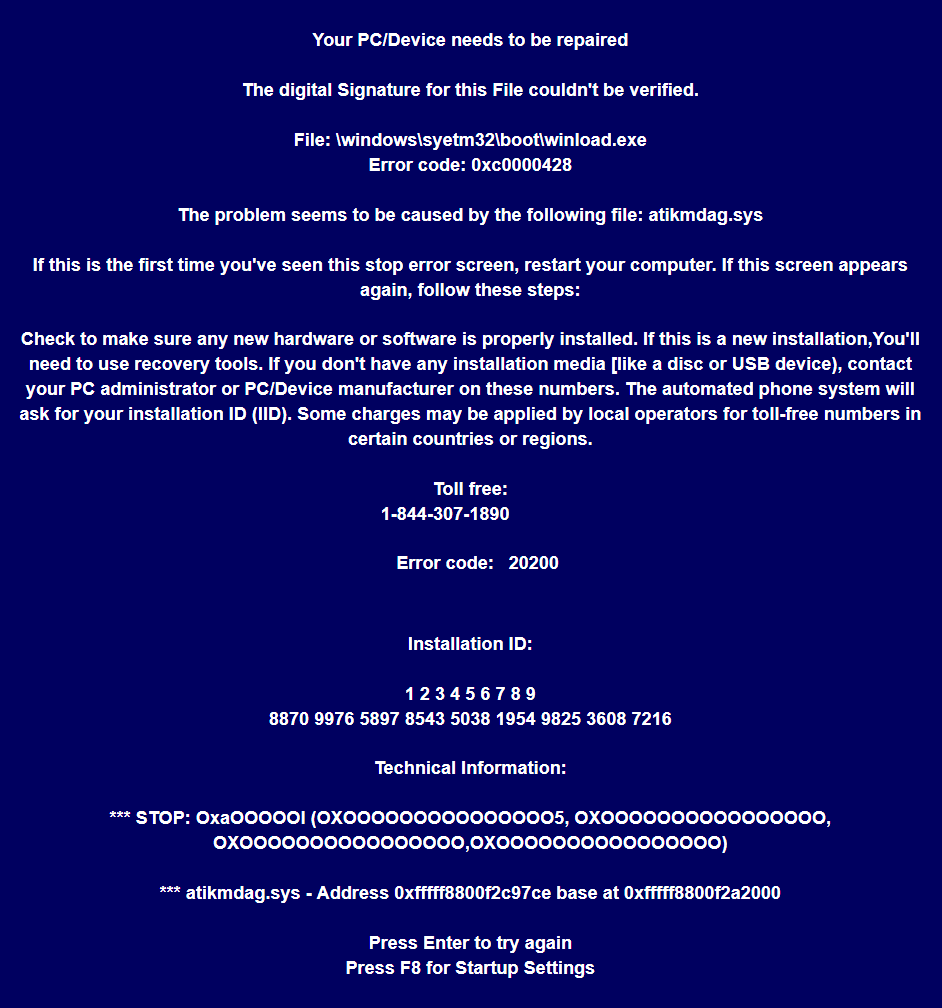
Tech support scams keep trying to use different tactics to work more efficiently. The latest such scam uses a Trojan horse which once launched, makes an executable file. That executable is named “WinInfos.exe”. Registry entries are created to make the…