The software is also known as DBAN and is oriented into those who want to completely wipe their hard drive, solid drive or any other drive on their computer completely so that it is as clean as the day it was first purchased. The program is very smart and works via Kernel (Linux) on live boot. We have decided to do a software review of Darik’s Boot and Nuke to illustrate the features of this software and how it can benefit users who want to take advantage of it.
The software is also known as DBAN and is oriented into those who want to completely wipe their hard drive, solid drive or any other drive on their computer completely so that it is as clean as the day it was first purchased. The program is very smart and works via Kernel (Linux) on live boot. We have decided to do a software review of Darik’s Boot and Nuke to illustrate the features of this software and how it can benefit users who want to take advantage of it.
App Profile
| Name | Darik’s Boot and Nuke |
| Type | Data Wiping Software |
| Developer | Blanco |
| Official Website | DBAN.org |
| Operating System | Any device which can boot it via BIOS or other firmware. |
| License Price | $14.95 with 100% Data Wipe and a Certificate Report. |
| Free Version | Yes, with no Certification of Wipe. |
| User Experience | Discuss Darik’s Boot and Nuke In Our Forum |
Darik’S Boot and Nuke – Technical Resume
As soon as we downloaded the 15.9MB ISO image, we have noticed its small size. This is extremely convenient because DBAN can fit on a wide range of different portable devices, such as old USB drives, CD’s, old Memory Cards, etc. This is very important because you have the choice on how to make it bootable. For example, if your laptop does not have a CD/DVD drive you may install and boot it via a USB drive which is particularly convenient
Besides this advantage, there are also other features that should be noted:
A variety of wiping standards.
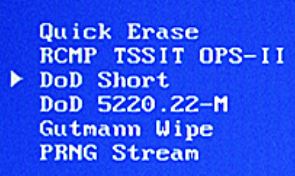
When DBAN boots you may notice that after you choose which drive you want to wipe completely, you will see a screen that offers several wiping options that are particularly effective:
One of those standards is the DoD(Department Of Defense)’s 5220-22 M, which uses a method that replaces the sector locations of your hard drive with different characters which may be completely random, after which verifies them. This is a very effective data wiping method, and it can fool even the most advanced data recovery software.
Another standard which is particularly interesting is the RCMP TSSIT OPS-II wipe method which has been reported to be used in a variety of file shredding programs and other software. What the method does is very similar to DoD’s method. However it performs several passes to make sure the information is gone for good:
→1: Writes a zero
2: Writes one
3: Writes a zero
4: Writes one
5: Writes a zero
6: Writes one
7: Writes a random character and verifies the write
Source: pcsupport.about.com
Another option to choose from is the Guttmann Wipe method, created by Peter Gutmann and Colin Plumb. This method is designed for ATA IDE and SATA because it takes advantage of conception for secure erasure support for ATA drives.
We particularly like the way PRNG Stream method operates since it uses a generator to replace data with random characters, similar to the data encryption principles.
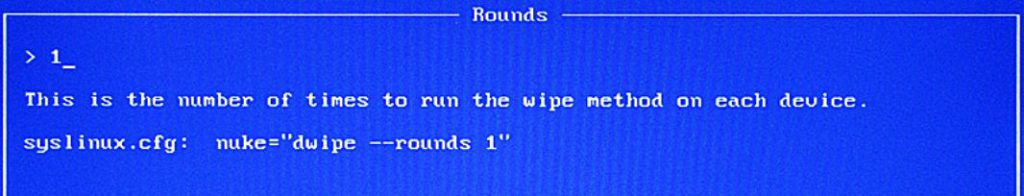
Wiping rounds.
This feature allows the user to set the number of passes he wants DBAN to perform to gain the maximum effectiveness of erasure. It is done via the command nuke=”dwipe – -rounds n” where “n” is the number of rounds but for easiness users can also set it from the menu:
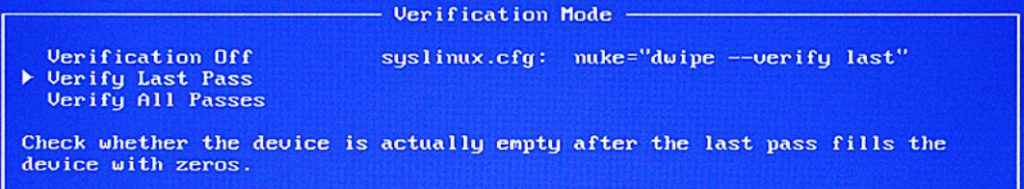
Verification Mode
This particular feature of the program is an important one because it performs a reverse check to verify whether or not the data has been wiped from the affected computer.

What We Like
We felt that certain features of this program distinguish it from others:
- Simplicity and Lightness.
- A choice between variety of wiping standards.
- Low in size.
- Explanation of the commands and meaning for each action.

What Is Missing
- We felt that several different aspects of this software could be improved.
- Added instructions for inexperienced users who download the program that explain how to make it bootable and use it effectively.
- Added bootable drive maker or image writer to disc to simplify the need to download and install such software in case the user does not have it.

Conclusion
 The bottom line for DBAN is that the program can help you if you are paranoid, want to sell your hard drive or even if you are running a PC repair business. However, we would recommend using the Certified version for businesses, because it has a guarantee of data removal, unlike the free license. Either way, we like this software because it is very simple and can get the job done for you without any hic-ups.
The bottom line for DBAN is that the program can help you if you are paranoid, want to sell your hard drive or even if you are running a PC repair business. However, we would recommend using the Certified version for businesses, because it has a guarantee of data removal, unlike the free license. Either way, we like this software because it is very simple and can get the job done for you without any hic-ups.