Have you ever encountered being redirected to Gggtrenks.com? If so, it’s essential to take quick action! Please read this guide to understand what steps to take to secure your device and valuable data.
What Is Gggtrenks.com?
The website Gggtrenks.com may raise some concerns, although it doesn’t appear to be malicious. This article aims to answer your questions about Gggtrenks.com and provide guidance on what to do if you come across it.
To assess Gggtrenks.com’s safety, we need to consider various factors, including its security, reputation, content quality, and user feedback.
– Details
| Name | |
| Symptoms | Our systems have detected multiple symptoms that may suggest that this website may be unsafe, such as concealing data from the user, lack of social media profiles and other details. |
| Detection Tool |
See If Your Device Has Been Compromised by : Download
Malware Removal Tool
|
[/su_table]
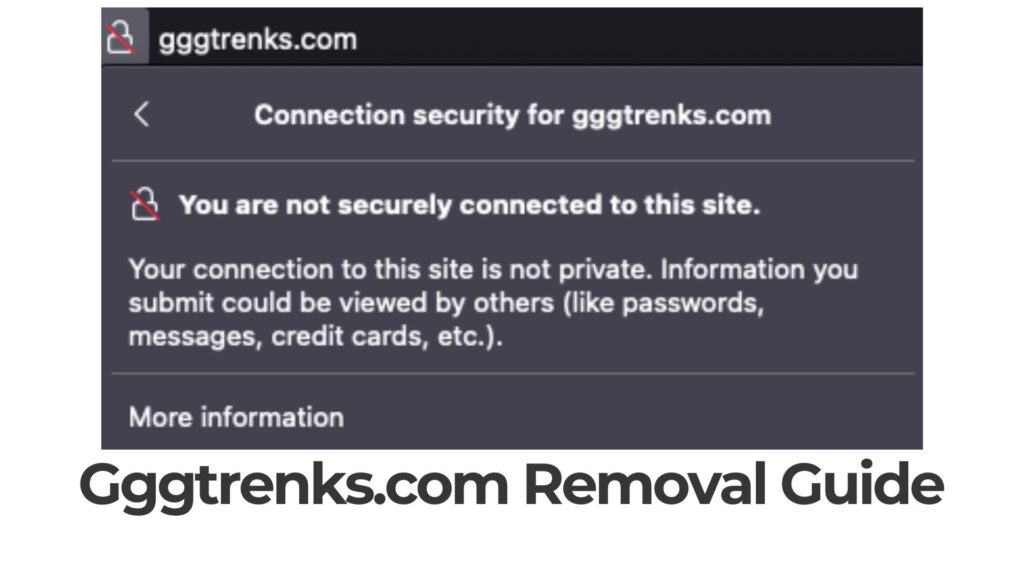
Gggtrenks.com Security
One clear sign of a questionable website is its security measures. Gggtrenks.com might lack essential security features like SSL encryption (HTTPS) or strong firewall protection, which can make it susceptible to data breaches and unauthorized access. This exposes users to potential risks, such as:
- Being redirected to risky third-party websites.
- Downloading torrents from unknown sources.
Gggtrenks.com may also use various cookies and tracking mechanisms to gather data about your online activities, including:
- Your IP and MAC addresses.
- Your mouse movements.
- Your browsing history.
- Your search queries.
- Your bookmarked websites.
- Websites you’ve visited.
- Your mouse clicks.
- Personal information you may have entered.
Is Gggtrenks.com Trustworthy?
If Gggtrenks.com lacks a good reputation or a substantial online presence, it’s wise to be cautious. These factors suggest a higher likelihood of suspicious behavior. If you suspect adware on your device, you may be at risk of redirection to sites like:
- Untrustworthy software download sites.
- Fraudulent survey websites.
- Phishing pages.
- Tech support scams.
- URLs containing virus-infected files or scripts.
- Websites hosting scams.
- Redirects to hazardous sites via pay-per-click routes.
This is often referred to as malvertising and comes with specific risks. Some of these risks include malware infections like Ransomware, Trojans, Rootkits, and other types of malware. Other problems associated with such sites include tech support scams and phishing.
Gggtrenks.com – Pros and Cons
Advantages:
- Currently not detected as malicious.
Disadvantages:
- No associated social media profiles.
- Difficulty finding patches or cracks.
- Possible redirects to unfamiliar websites.
- Potential use of third-party cookies for data collection.
- Risk of downloading harmful files that can lead to malware infections.
- Possibility of similar websites.
What Should You Do?
If you suspect that Gggtrenks.com has compromised your device in any way, our top recommendation is to scan your device for malware. Several methods are available, but for a fast and effective solution, consider using professional anti-malware software. Experts often recommend this software because it can automatically scan, detect, and remove hidden malware from your device.


