downLOadiTKeeP Removal Manual
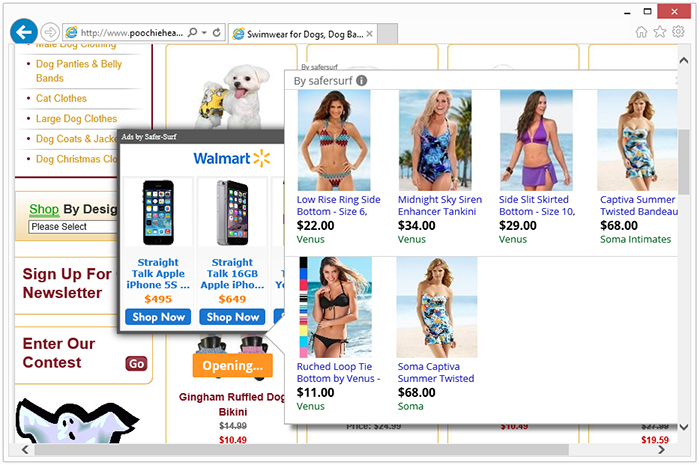
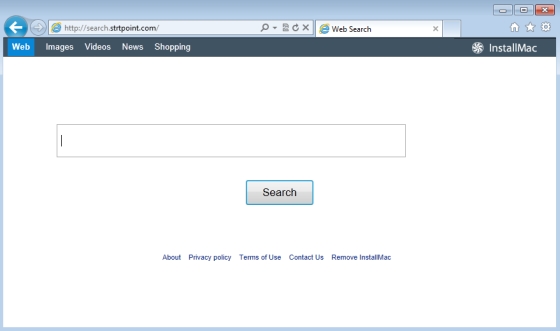
Created by InstalleRex-WebPick, downLOadiTKeeP (downloaDitkeep, DownloadItKeep) is an adware-laced program that alters the settings of your browser, so it would load different pop-ups and banner ads as you browse the Web. downLOadiTKeeP is a browser add-on and a BHO (browser…