Have you ever found yourself unexpectedly redirected to a different webpage while browsing on Safari, or bombarded with ads that seem to come from nowhere? If so, you might be facing the frustrating reality of the Safari Redirect Virus, a persistent issue plaguing many Mac users.
Affiliated services are often involved in these redirect campaigns, exposing users to fraudulent ad networks and deceptive online practices.
This article delves into the causes, symptoms, and, most importantly, solutions to combat this invasive malware, ensuring your Safari browsing experience remains seamless and secure. From recognizing early signs of infection to preventive measures and the dedicated use of security tools like SpyHunter for Mac, we’ll guide you through regaining control over your digital browsing space.
Safari Redirect Summary
| Name | Safari Redirect Virus |
| Type | Potentially Unwanted Program / Adware / Browser Hijacker |
| Short Description | Related to the presence of undesired program on your Mac. This program aims to heavily modify web browsers’ settings to display ads and redirect to suspicious pages. |
| Symptoms | Preferred web browser is configured to redirect you to unwanted pages. Slower Mac performance could be experienced as well. |
| Removal Time | Approximately 15 minutes for a full-system scan |
| Removal Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
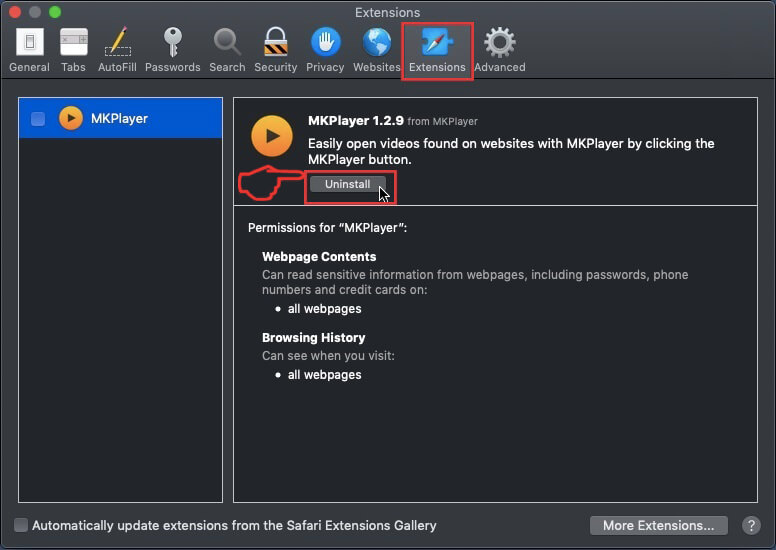
Removing Malicious Profiles and Extensions from Safari
The Safari Redirect Virus often infiltrates systems through malicious profiles or extensions added to Safari without your knowledge. To remove these:
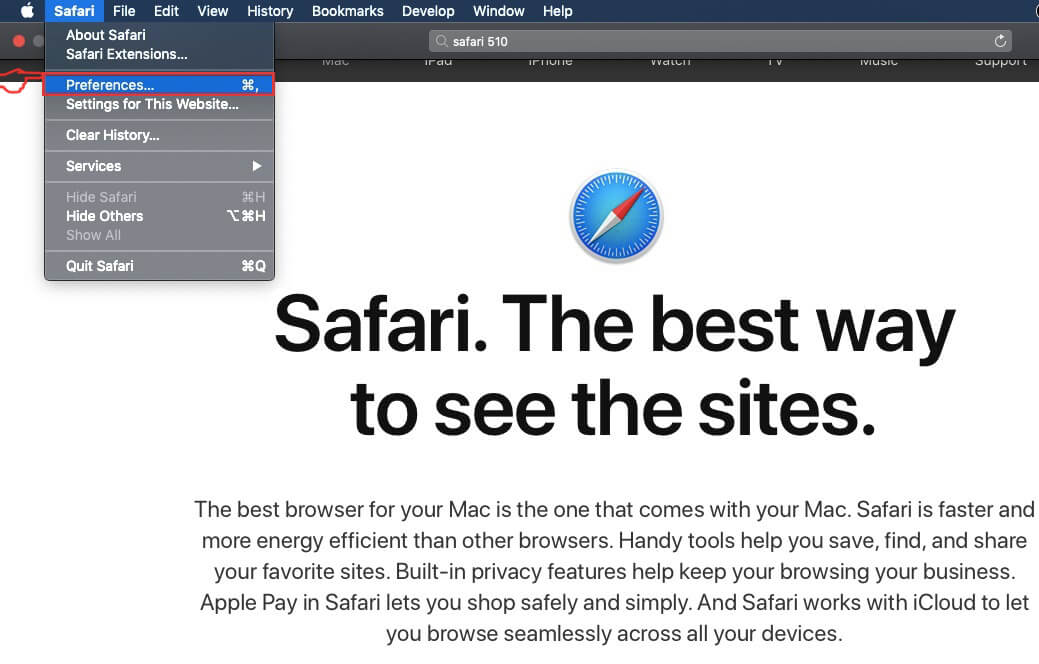
- Open Safari Preferences: Click Safari in the menu bar, then select ‘Preferences‘.
- Go to the Profiles section: If present, this can indicate unwanted configurations installed by malware.
- Remove any suspicious profiles: Select the questionable profile and press the ‘-‘ button to delete it.
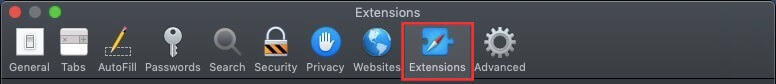
- Next, navigate to the Extensions tab to view all installed extensions.
- Identify and uninstall suspicious extensions by selecting them and clicking the ‘Uninstall’ button.
- Confirm the removal when prompted to clear your browser from potential threats.
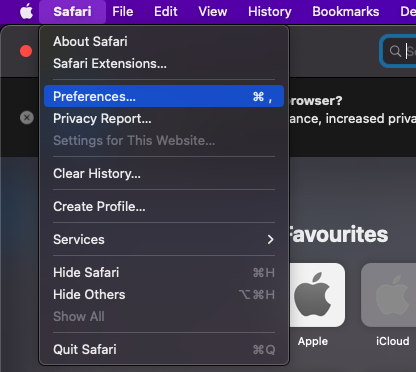
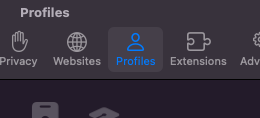
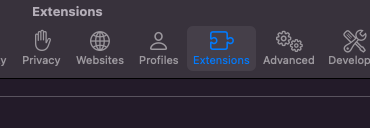
Removing unknown extensions and profiles is a crucial step in regaining control over your Safari browsing experience.
Securing Safari Settings and Preferences Post-Removal
After clearing malicious profiles and extensions, further secure your Safari settings to prevent future infections:
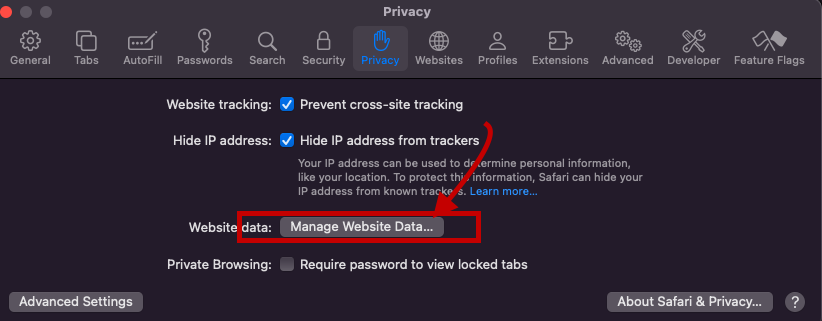
- Reset Safari: Go to ‘Safari’ > ‘Preferences’, select the ‘Privacy’ tab, and click ‘Manage Website Data’. From here, click ‘Remove All’ to delete stored website data that might contain harmful scripts.
- Adjust Security Settings: Still in Preferences, enhance your security by enabling fraudulent site warnings under the ‘Security’ tab and ensuring JavaScript is only enabled for trusted websites in the ‘Websites’ tab.
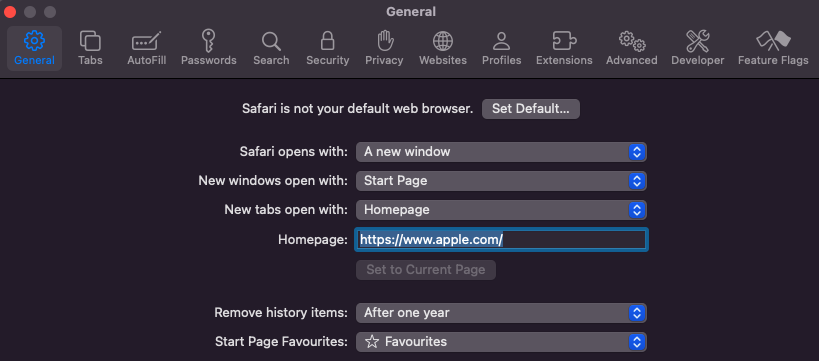
- Review Homepage and Search Engine Settings: In the ‘General’ tab, verify that your homepage hasn’t been altered. Similarly, check the ‘Search’ tab to ensure your preferred search engine is selected.
By meticulously following these steps and regularly checking for unauthorized changes, you can effectively shield your Safari browser from redirect viruses and other malicious software.
Remember, keeping your Mac and Safari updated, along with being cautious about the extensions you install, are key practices in maintaining a secure browsing environment. For those looking for an added layer of protection, SpyHunter for Mac offers comprehensive defense mechanisms against various malware types, including Safari redirect viruses.
Understanding Safari Redirect Virus: What You Need to Know
The Safari Redirect Virus, often a thorn in the side for Mac users, is more than just an annoyance. This malware category encompasses various forms of unwanted software designed to hijack your browser. By changing settings without permission, it takes control of the Safari browser and can lead to issues like constant redirects, unwelcome ads, and even privacy breaches. At its core, the Safari Redirect Virus aims to profit from these disruptions, whether through ad revenue or data collection. Recognizing its symptoms and understanding its operation is the first step in reclaiming your digital space.
Exploring the Nature of Safari Redirect Virus on Mac
This type of virus is commonly linked with browser hijackers, a subset of potentially unwanted applications (PUAs) that meddle with browser settings. Once infiltrated, these hijackers can alter the default search engine, homepage, and new tab page, redirecting users to specific URLs. While these changes might seem minor, they significantly disrupt the browsing experience. Browser hijackers commonly target well-known browsers like Safari, Chrome, and Firefox, making no Mac user completely immune. These applications not only interrupt online navigation but also monitor internet activity, collecting data that ranges from search queries to sensitive information, which could be shared with or sold to third parties.
How Does a Mac Become Infected with Safari Redirect Virus?
How does such disruptive software find its way onto your Mac? The paths are surprisingly mundane, highlighting the need for vigilance even during routine online activities. Here are three primary methods of infiltration:
- Deceptive Pop-up Ads: Clicking on a dubious pop-up ad can unintentionally trigger the download of a browser hijacker.
- Free Software Installers (Bundling): Often, PUAs come packaged with free applications. Without a careful review of the installation steps, users may unknowingly consent to install additional unwanted software.
- Fake Flash Player Installers: These have long been a notorious method for spreading various types of malware, including browser hijackers.
- Torrent File Downloads: Downloading software or media from unreliable sources can also serve as a conduit for unwanted applications.
Awareness and caution in these areas can help prevent the majority of Safari Redirect Virus infections. Employing trusted security solutions like SpyHunter for Mac can offer another layer of protection by detecting and removing any unwelcome applications before they can cause harm. Prompt action and smart browsing habits are crucial in maintaining a secure and enjoyable online experience.
Identifying the Presence of Safari Redirect Virus on Your Mac
When your Mac starts behaving oddly with Safari at the center of these quirks, it might be time to consider the possibility of a Safari Redirect Virus. This virus cleverly disguises its presence, making it crucial for users to spot the early warning signs.
Top Signs That Your Safari Browser Is Infected
Realizing your Safari browser is under the grip of malware can be alarming. Here are clear indicators that your Mac might be affected:
- Unexpected Changes: Your browser’s homepage or search engine switches to something you didn’t set up, and attempts to revert these changes are futile.
- Increased Ad Activity: An uptick in pop-ups, banners, and other ad formats clutter your browsing space, often unrelated to the sites you’re visiting.
- Sluggish Performance: Safari begins to lag, with web pages taking longer to load or failing to load entirely, hindering your browsing experience.
- Relentless Pop-Ups: Continuous pop-up ads, some flashing phony warnings about your Mac’s security, are a telltale sign.
- Locked Settings: You might find yourself unable to change certain browser settings, suggesting that unwanted software is dictating these configurations.
Encountering one or more of these issues could point towards an infection, nudging you towards immediate action to restore Safari’s health and your peace of mind.
Consequences of Ignoring Safari Redirect Malware
Dismissing the signs of Safari redirect malware can lead to dire outcomes for you and your Mac. The ramifications of oversight extend beyond mere inconvenience:
- Compromised Privacy: As browser hijackers gather your browsing data, including search histories and site visits, your privacy hangs in the balance. Worse yet, sensitive information might fall into the wrong hands.
- Decreased Security: The Safari Redirect Virus can serve as a gateway for more malicious software, exposing your system to a variety of threats and vulnerabilities.
- Disrupted Browsing: The onslaught of ads and redirects can transform your Safari experience into a frustrating one, with legitimate content being left behind due to the influx of ads.
- Potential Financial Loss: Accidental clicks on deceptive ads or redirects might lead to scams or phishing sites, risking financial loss or identity theft.
Inadequate attention to these warning signs not only jeopardizes your online security but can also have tangible, harmful effects on your everyday digital life. Addressing the issue promptly can avert these risks, ensuring your browsing experience remains both safe and enjoyable.
Detailed Guide to Manually Remove Safari Redirect Virus
Encountering the Safari Redirect Virus can significantly hamper your online experience, leading to unsolicited advertisements and potentially dangerous website redirects. This guide is tailored to help you manually eliminate these issues from your Mac, ensuring a safer and more enjoyable browsing experience.
Initial Steps to Take Before Removing the Virus
Before diving into the virus removal process, confirm the existence of the problem. Symptoms include unexpected redirects, pop-up ads, or changes to your homepage or search engine without your consent. Once confirmed, prepare your Mac by updating the operating system and Safari browser, ensuring all security patches are applied. Additionally, back up important data to prevent any loss during the cleanup process.
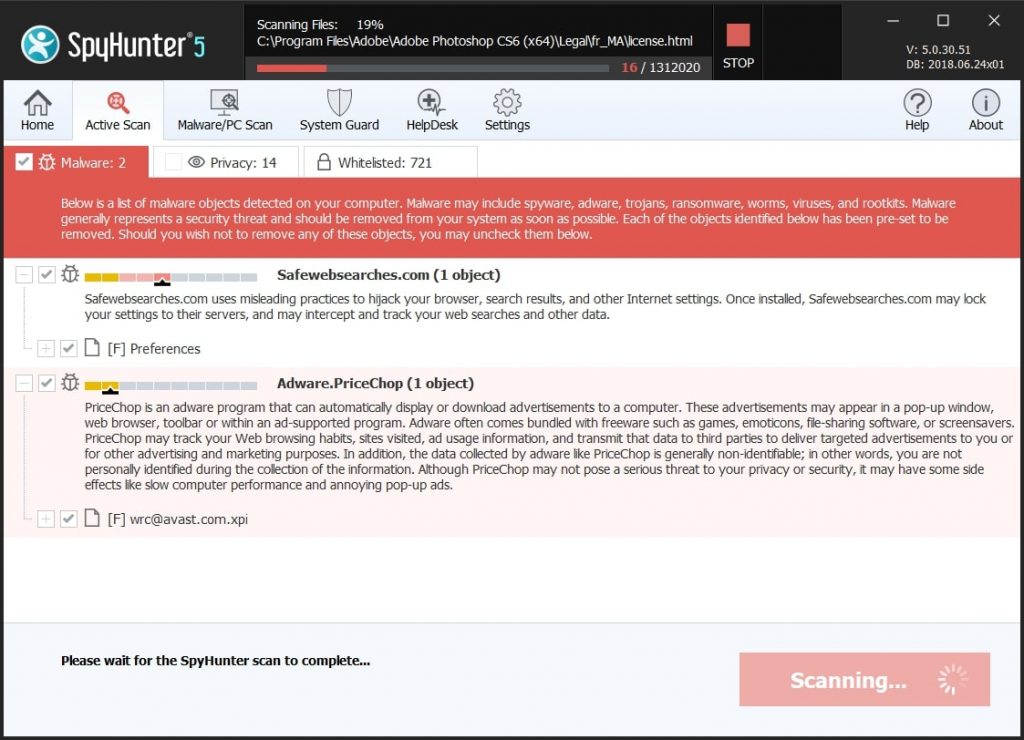
Utilizing SpyHunter for Thorough Removal of Safari Redirect Virus
Removing the Safari Redirect Virus from your Mac can be a tricky process. This is where SpyHunter for Mac steps in, providing a streamlined and efficient method for identifying and eliminating these unwanted intrusions. Designed specifically to cater to the macOS environment, SpyHunter simplifies the eradication of the virus, ensuring your system is safeguarded against future threats.
Why Choose SpyHunter for Mac to Combat Safari Redirect Virus?
Choosing SpyHunter for Mac comes with several benefits, making it a superior choice for combating the Safari Redirect Virus.
One of the most significant advantages is its tailored design for macOS, ensuring compatibility and efficiency. Unlike other generic software, SpyHunter offers comprehensive scanning capabilities that delve deep into your system to identify even the most elusive threats. Furthermore, its user-friendly interface makes virus removal accessible for users of all technical skill levels. Whether you’re dealing with severe malware infections or minor nuisances, SpyHunter provides a reliable defense mechanism for your digital life.
Installing SpyHunter: A Simple Guide for Effective Removal
Installing SpyHunter on your Mac is a straightforward process designed to get you up and running with minimal fuss. Here’s a quick guide:
- Begin by downloading SpyHunter for Mac from the official site to ensure you have the latest version.
- Open the downloaded file, which typically resides in your Downloads folder, and follow the on-screen instructions. These steps guide you through the installation process, requiring minimal input.
- Once installed, launch SpyHunter and select the option for a full system scan. This comprehensive scan is crucial for detecting the Safari Redirect Virus alongside any other hidden threats.
- After the scan, SpyHunter will display a list of detected threats. Follow the prompts to remove them, which includes the Safari Redirect Virus. This step is crucial for cleaning your system and restoring your browser’s security.
- For ongoing protection, consider setting SpyHunter to run regular scans automatically. This proactive approach helps keep your device safe from future infections without requiring manual intervention.
By following these steps, you can seamlessly install and utilize SpyHunter to protect your Mac from the Safari Redirect Virus, ensuring a safer browsing experience. Remember, regular scans are a key component of maintaining your system’s health and security.
Preventive Measures to Safeguard Your Mac Against Future Attacks
To protect your Mac from future cybersecurity threats, including malware that targets Safari, adopting preventive measures is crucial. These steps not only secure your system but also enhance your browsing experience, making it safer and more reliable. By staying proactive, you can significantly mitigate the risk of encountering malicious software and ensure your data remains secure.
Essential Habits to Keep Your Mac and Safari Secure
Developing a set of core practices is pivotal in safeguarding your Mac and Safari browser against potential attacks. Here are essential habits you should integrate into your daily online routine:
- Regular Updates: Keep your macOS and Safari browser up to date. Each update often includes important security patches that protect against new threats.
- Cautious Downloading: Only download apps and software from reputable sources. The Mac App Store and verified developers are your safest bets.
- Smart Browsing: Avoid visiting suspicious websites or clicking on ads that seem too good to be true. These can be gateways to malware.
- Use Security Software: Install a reliable antivirus solution, like SpyHunter for Mac, which can detect and eliminate various types of malware tailored for macOS.
- Backup Frequently: Regularly back up your important files. In the event of an attack, you won’t lose your valuable data.
By adhering to these habits, you can greatly enhance the security of your Mac and Safari browser, making it more difficult for cyber threats to infiltrate your system.
Configuring Safari’s Security Settings for Optimal Protection
Adjusting Safari’s built-in security settings can further shield you from malicious websites and downloads. Here’s how you can configure Safari for better protection:
- Fraudulent Sites Warning: Ensure Safari’s ‘Warn when visiting a fraudulent website’ option is enabled to get alerts about suspicious websites.
- Privacy Browsing: Use Private Browsing modes when conducting sensitive activities to avoid saving your browsing history or receiving cookies.
- Manage Extensions Wisely: Regularly review your installed Safari extensions. Uninstall those that are unnecessary or that you no longer trust.
- Block Pop-ups: Enabling Safari’s pop-up blocker can prevent annoying and potentially harmful ads from disrupting your browsing experience.
While no single measure can provide complete protection, combining these settings with safe browsing habits and robust security software like SpyHunter creates a strong defense line against various online threats, keeping your Safari experience pleasant and secure.
When to Seek Professional Help with Safari Redirect Virus Removal
Dealing with a Safari redirect virus can sometimes transcend simple DIY fixes, signaling the need for professional assistance. Recognizing the point at which to transition from a self-help approach to seeking expert aid is crucial for the swift and effective resolution of the issue. If you find that the virus persists even after following manual removal instructions, or if the malware removal process negatively affects your computer’s performance, it’s time to consider professional help. Additionally, users who are not comfortable performing detailed technical steps on their systems should opt for expert assistance from the start to avoid potential missteps that could further complicate the situation.
Understanding the Limitations of Manual Removal Methods
While manual removal techniques offer a hands-on approach to dealing with the Safari redirect virus, they come with limitations. These methods often require a certain level of technical proficiency and confidence in navigating system settings and files. In some cases, the malware might be deeply embedded within your system, beyond the reach of standard manual removal efforts. Moreover, manual removal processes might not always address the root cause of the malware, leading to future infections. It’s essential to evaluate your comfort level and the complexity of the infection before deciding to tackle it yourself.
Finding Reliable Technical Support for Complex Infections
Locating dependable technical assistance is paramount when facing tricky malware infections that are resistant to simple removal methods.
Start by consulting the support services of reputable cybersecurity firms, as they often have experience dealing with a wide range of malware threats, including the Safari redirect virus.
Opting for a specialized tool like SpyHunter ensures that you have ongoing support and a robust defense mechanism against future threats. Remember, choosing a reliable source for malware removal not only helps in effectively eliminating the virus but also safeguards your system against subsequent attacks. In the quest to maintain a secure digital experience, turning to established cybersecurity professionals can provide peace of mind and optimal outcomes.
Conclusion: Ensuring Your Mac Remains Secure and Free of Safari Redirect Virus
Maintaining a secure and smooth browsing experience on your Mac, especially when using Safari, requires proactive measures to fend off malware like the Safari Redirect Virus.
This nuisance not only hampers your online navigation with unwanted ads and redirects but also poses a threat to your privacy and security. Let’s simplify the approach to keeping your Safari browser clean, efficient, and free from malicious intrusions.
First and foremost, regular checks on your Safari’s functionality can be a telltale sign of any lurking issues. Unusual browser behavior such as unexpected redirects, pop-up ads, or altered homepage settings usually signals an infection.
Act swiftly by scanning your system with a reliable security tool. In this line of thought, SpyHunter for Mac stands out by offering an effective remedy. A quick download and scan can identify and remove not only the Safari Redirect Virus but other potential threats from your Mac, reinstating a safer online environment.
Moreover, beyond just tackling immediate threats, cultivating secure online practices plays a crucial role. Ensure your OS and all applications, including Safari, are up to date, as these updates often include critical security patches. Also, be cautious about the websites you visit and the links you click. Phishing attempts and malicious sites are common culprits behind such malware.
Prevention, coupled with timely action, can significantly mitigate the chances of infection.
Integrating a robust solution like SpyHunter into your digital hygiene routine acts as both a shield and a remedy. This simple yet effective approach not only addresses current threats but also fortifies your Mac’s defenses against future ones.
By keeping your software updated and practicing cautious browsing, you can maintain a secure and satisfying online experience, ensuring your Safari remains a gateway to the vast resources of the internet, unmarred by malicious software.
In summary, securing your Mac against the Safari Redirect Virus involves a blend of vigilance, regular system checks, and the employment of effective security solutions like SpyHunter for Mac. Embrace these strategies to navigate the web confidently, knowing your digital space is safeguarded.
Steps to Prepare Before Removal:
Before starting to follow the steps below, be advised that you should first do the following preparations:
- Backup your files in case the worst happens.
- Make sure to have a device with these instructions on standy.
- Arm yourself with patience.
- 1. Scan for Mac Malware
- 2. Uninstall Risky Apps
- 3. Clean Your Browsers
Step 1: Scan for and remove Safari Redirect Virus files from your Mac
When you are facing problems on your Mac as a result of unwanted scripts and programs such as Safari Redirect Virus, the recommended way of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that will improve your Mac’s security and protect it in the future.
Quick and Easy Mac Malware Video Removal Guide
Bonus Step: How to Make Your Mac Run Faster?
Mac machines maintain probably the fastest operating system out there. Still, Macs do become slow and sluggish sometimes. The video guide below examines all of the possible problems that may lead to your Mac being slower than usual as well as all of the steps that can help you to speed up your Mac.
Step 2: Uninstall Safari Redirect Virus and remove related files and objects
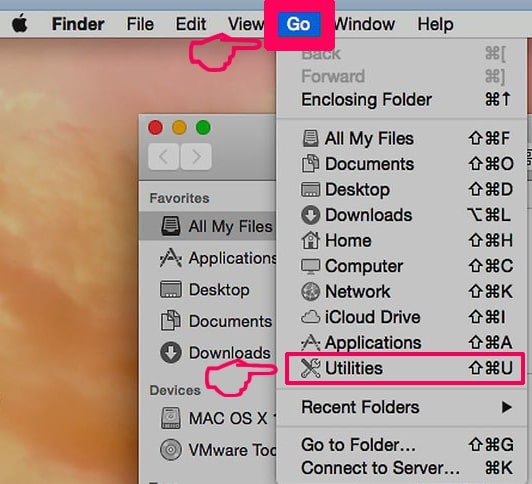
1. Hit the ⇧+⌘+U keys to open Utilities. Another way is to click on “Go” and then click “Utilities”, like the image below shows:
2. Find Activity Monitor and double-click it:

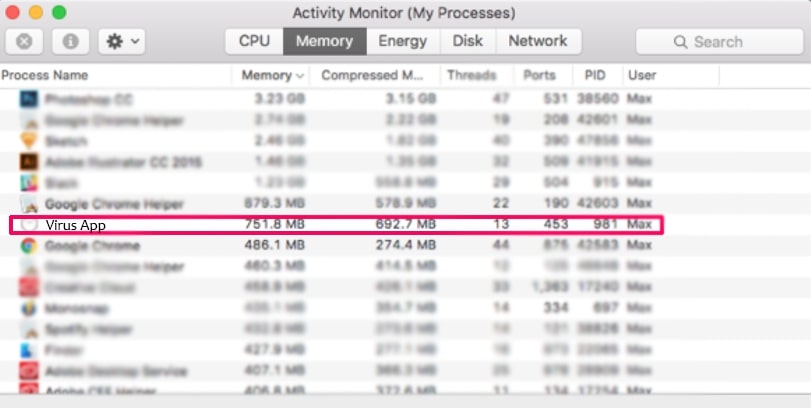
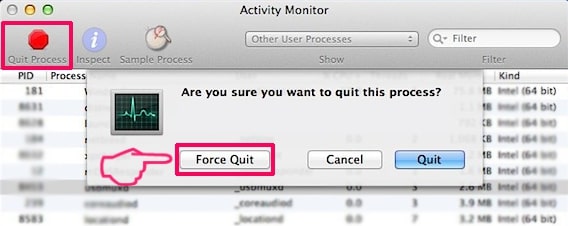
3. In the Activity Monitor look for any suspicious processes, belonging or related to Safari Redirect Virus:
4. Click on the "Go" button again, but this time select Applications. Another way is with the ⇧+⌘+A buttons.
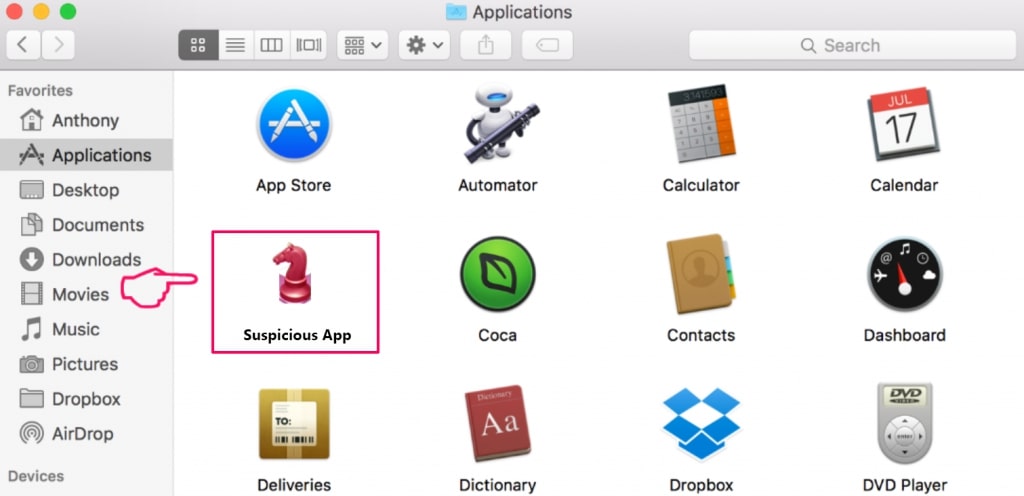
5. In the Applications menu, look for any suspicious app or an app with a name, similar or identical to Safari Redirect Virus. If you find it, right-click on the app and select “Move to Trash”.
6. Select Accounts, after which click on the Login Items preference. Your Mac will then show you a list of items that start automatically when you log in. Look for any suspicious apps identical or similar to Safari Redirect Virus. Check the app you want to stop from running automatically and then select on the Minus (“-“) icon to hide it.
7. Remove any leftover files that might be related to this threat manually by following the sub-steps below:
- Go to Finder.
- In the search bar type the name of the app that you want to remove.
- Above the search bar change the two drop down menus to “System Files” and “Are Included” so that you can see all of the files associated with the application you want to remove. Bear in mind that some of the files may not be related to the app so be very careful which files you delete.
- If all of the files are related, hold the ⌘+A buttons to select them and then drive them to “Trash”.
In case you cannot remove Safari Redirect Virus via Step 1 above:
In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below:
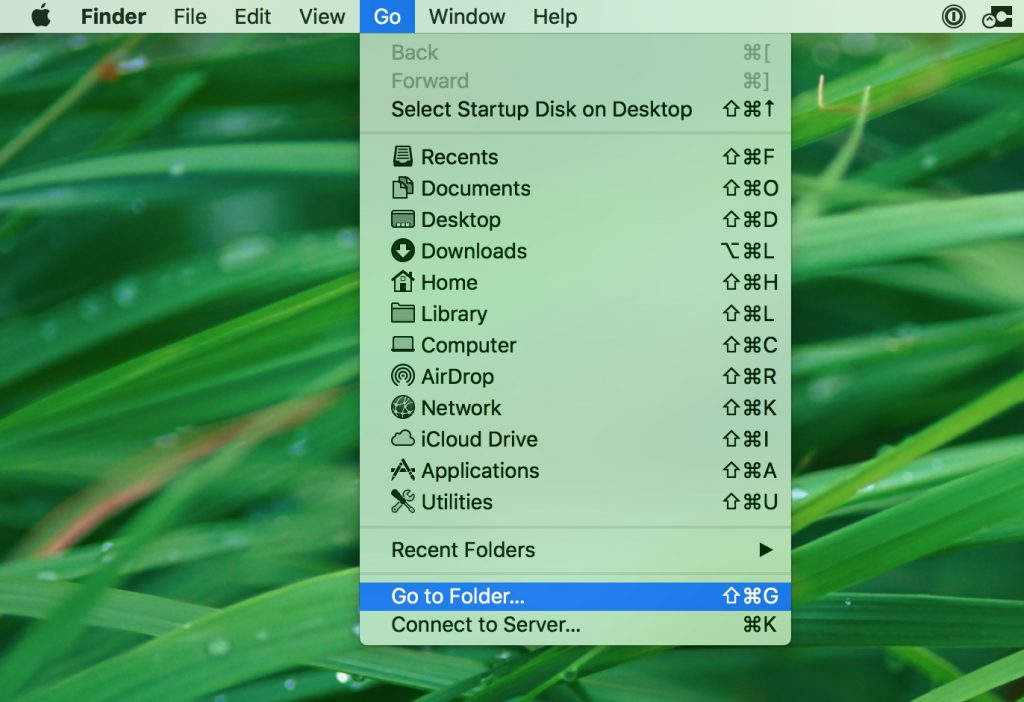
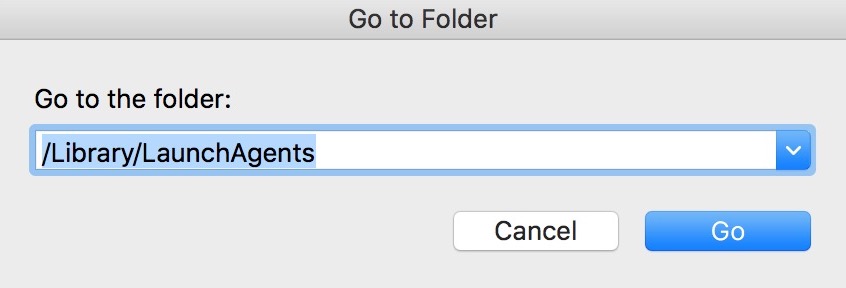
1. Click on "Go" and Then "Go to Folder" as shown underneath:
2. Type in "/Library/LauchAgents/" and click Ok:
3. Delete all of the virus files that have similar or the same name as Safari Redirect Virus. If you believe there is no such file, do not delete anything.
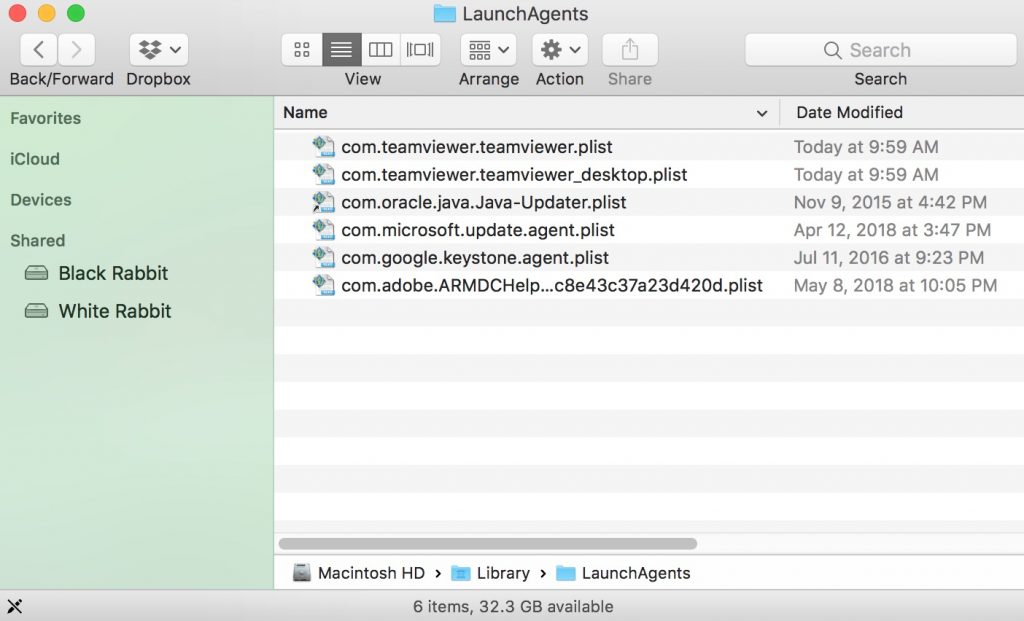
You can repeat the same procedure with the following other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
Tip: ~ is there on purpose, because it leads to more LaunchAgents.
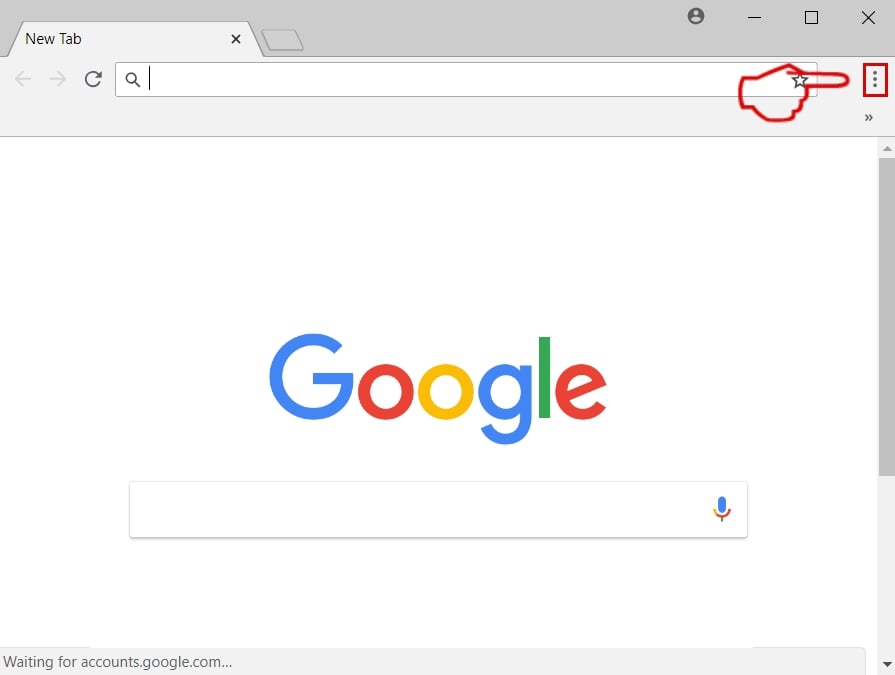
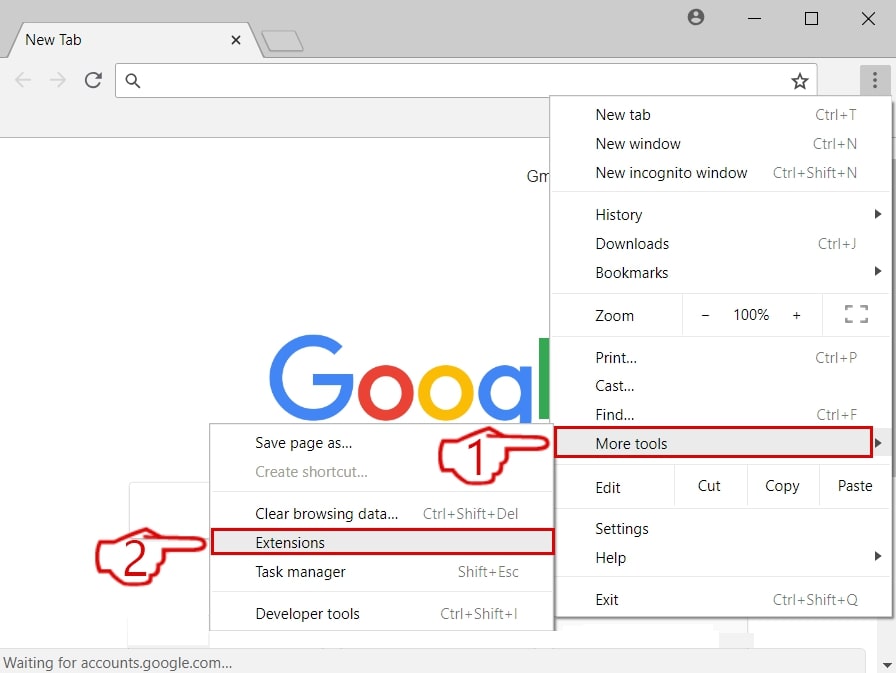
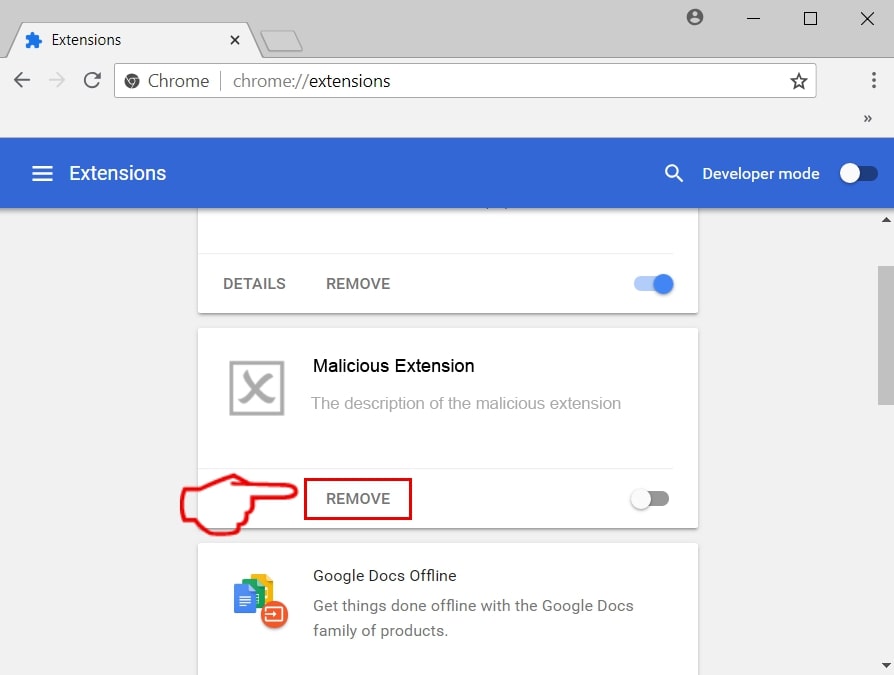
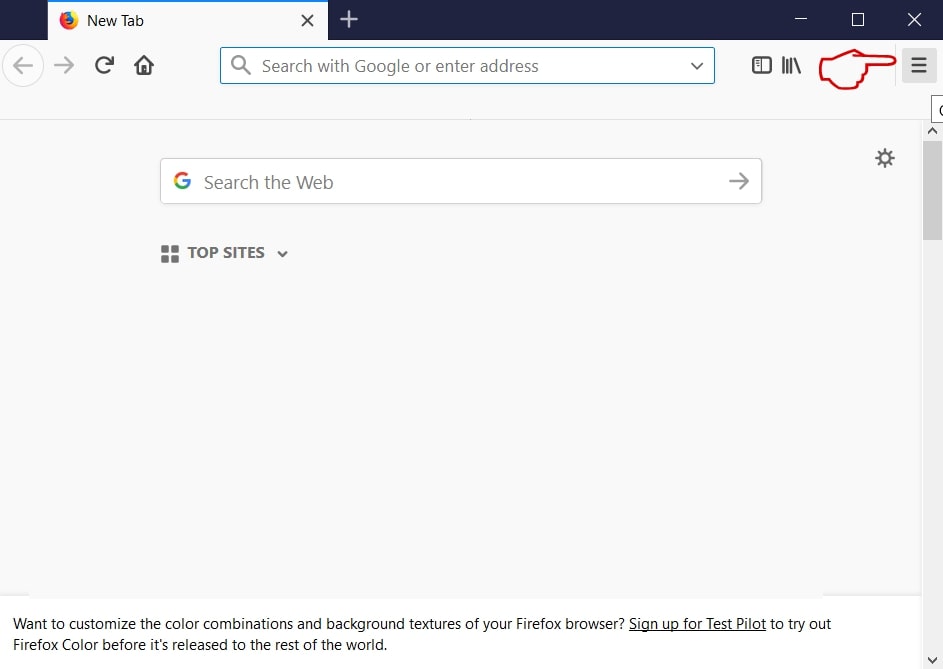
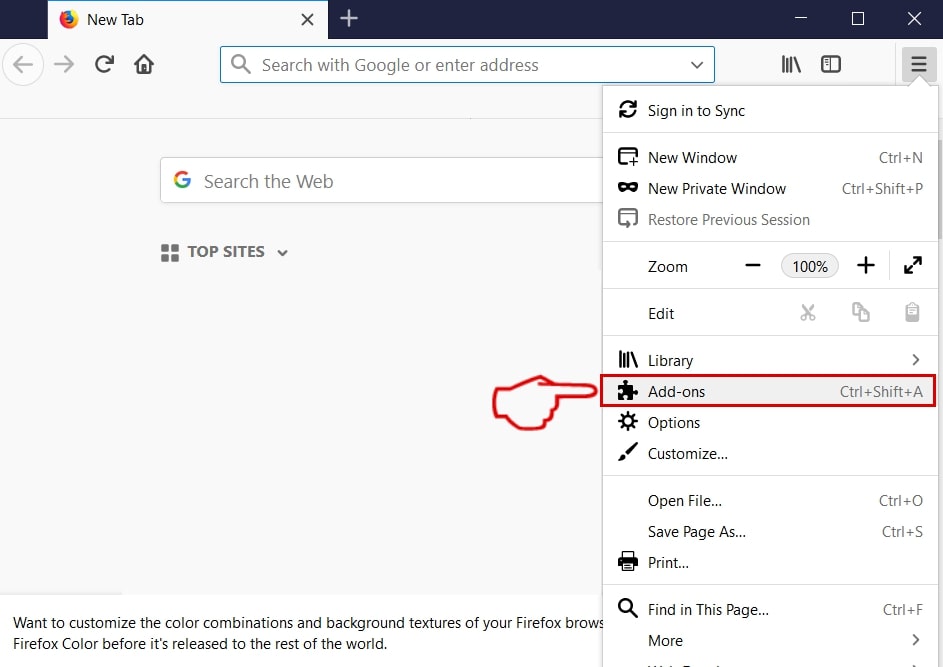
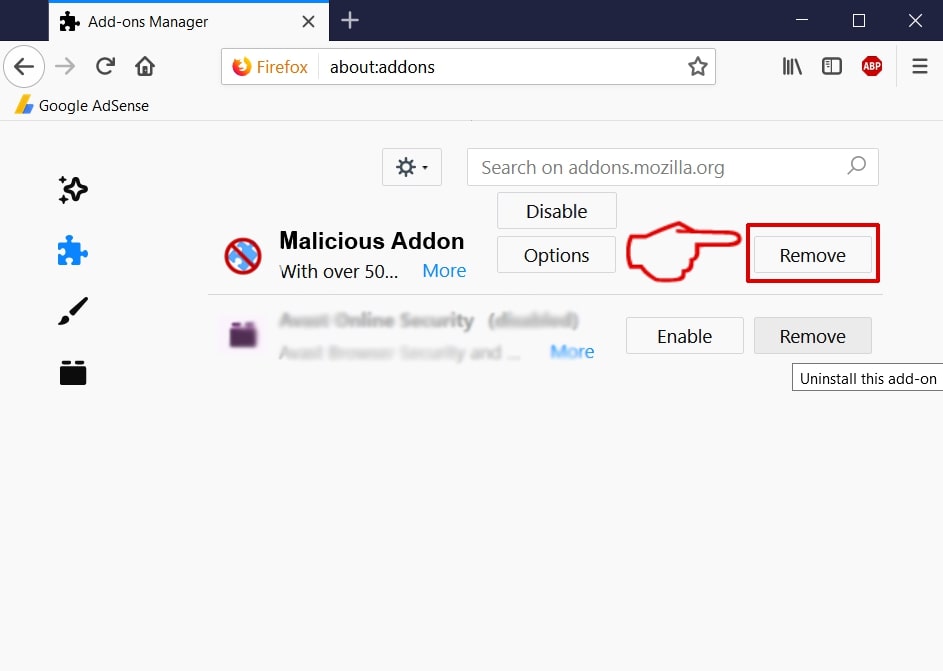
Step 3: Remove Safari Redirect Virus – related extensions from Safari / Chrome / Firefox
Safari Redirect Virus-FAQ
What is Safari Redirect Virus on your Mac?
The Safari Redirect Virus threat is probably a potentially unwanted app. There is also a chance it could be related to Mac malware. If so, such apps tend to slow your Mac down significantly and display advertisements. They could also use cookies and other trackers to obtain browsing information from the installed web browsers on your Mac.
Can Macs Get Viruses?
Yes. As much as any other device, Apple computers do get malware. Apple devices may not be a frequent target by malware authors, but rest assured that almost all of the Apple devices can become infected with a threat.
What Types of Mac Threats Are There?
According to most malware researchers and cyber-security experts, the types of threats that can currently infect your Mac can be rogue antivirus programs, adware or hijackers (PUPs), Trojan horses, ransomware and crypto-miner malware.
What To Do If I Have a Mac Virus, Like Safari Redirect Virus?
Do not panic! You can easily get rid of most Mac threats by firstly isolating them and then removing them. One recommended way to do that is by using a reputable malware removal software that can take care of the removal automatically for you.
There are many Mac anti-malware apps out there that you can choose from. SpyHunter for Mac is one of the reccomended Mac anti-malware apps, that can scan for free and detect any viruses. This saves time for manual removal that you would otherwise have to do.
How to Secure My Data from Safari Redirect Virus?
With few simple actions. First and foremost, it is imperative that you follow these steps:
Step 1: Find a safe computer and connect it to another network, not the one that your Mac was infected in.
Step 2: Change all of your passwords, starting from your e-mail passwords.
Step 3: Enable two-factor authentication for protection of your important accounts.
Step 4: Call your bank to change your credit card details (secret code, etc.) if you have saved your credit card for online shopping or have done online activiites with your card.
Step 5: Make sure to call your ISP (Internet provider or carrier) and ask them to change your IP address.
Step 6: Change your Wi-Fi password.
Step 7: (Optional): Make sure to scan all of the devices connected to your network for viruses and repeat these steps for them if they are affected.
Step 8: Install anti-malware software with real-time protection on every device you have.
Step 9: Try not to download software from sites you know nothing about and stay away from low-reputation websites in general.
If you follow these reccomendations, your network and Apple devices will become significantly more safe against any threats or information invasive software and be virus free and protected in the future too.
More tips you can find on our MacOS Virus section, where you can also ask any questions and comment about your Mac problems.
About the Safari Redirect Virus Research
The content we publish on SensorsTechForum.com, this Safari Redirect Virus how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific macOS issue.
How did we conduct the research on Safari Redirect Virus?
Please note that our research is based on an independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware definitions, including the various types of Mac threats, especially adware and potentially unwanted apps (PUAs).
Furthermore, the research behind the Safari Redirect Virus threat is backed with VirusTotal.
To better understand the threat posed by Mac malware, please refer to the following articles which provide knowledgeable details.




Bonjour, je ne trouve pas le virus qui me redirige vers bing. Je suis sous Mac Os Catalina 10.15.3. Comment faire pour supprimer définitivement bing?