Hackers using the Asprox / Kuluoz botnet appear to have developed it to send links landing on different pages, depending on what operation systems victims are using – Android or iOS. In addition, it seems that there is a backdoor threat for Windows desktop as well, using the PC downloader BKDR_KULUOZ.VLU.
The important thing here is that one and the same phishing campaign is targeted to multiple devices, emails containing different links depending on the platform they land on.
In a blog post from Friday, 14 November, Wish Wu, a Mobile Engineer Threat Response from Trend Micro says that the malicious message stream was tracked last week. It seems to come from the Viber messaging application for both mobile and desktop recipients.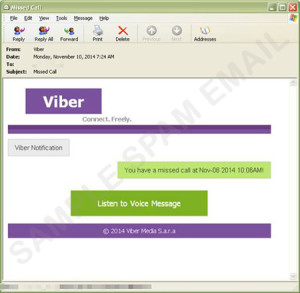
The victims receive an e-mail message, stating that the user has received a voice mail on their Viber account. Opening it, they see a link, leading to malicious streaming web-site. It asks them to register, provide credit card information and then charges them without their knowledge.
→What’s more notable is that redirection can also vary depending on the OS of the device. Android users were directed to the “Go Launcher” app on the Google Play Store. Apple users were directed to a Chinese gaming app on the iTunes site. It should be noted that both of these apps are not malicious.’, Wu states in his blog.
Other re-directing methods include adults-only platforms. In some cases, Android users are being lead to an APK (Android Package Application) and end up on a blank page while trying to access URL addresses of adult websites.
The malware is also tracking incoming and outgoing calls, sending logs to a remote server.
Suspicious messages, therefore, must be treated with increased precaution, the researchers say. Email messages can be easily tweaked and manipulated to look like coming from trusted sources from hackers.
“We advise users to be cautious when opening emails. Emails can be easily spoofed by spammers and other cybercrooks. Clicking links in emails should be avoided as much as possible. It’s far better for users to directly type the URL of the site on the address bar than rely on the embedded link.”, they advice.

