Security researchers alerted that hackers are distributing a malware Advanced Battery Saver Android on the Google Play Store. The hackers hijack personal data and reconfigure the devices in order to perform various system modifications. It is rated as a very dangerous instance that should be removed as quickly as possible in order to prevent it from being used as a conduit for financial abuse and identity theft crimes.
Discovery of the Malware Advanced Battery Saver Android App
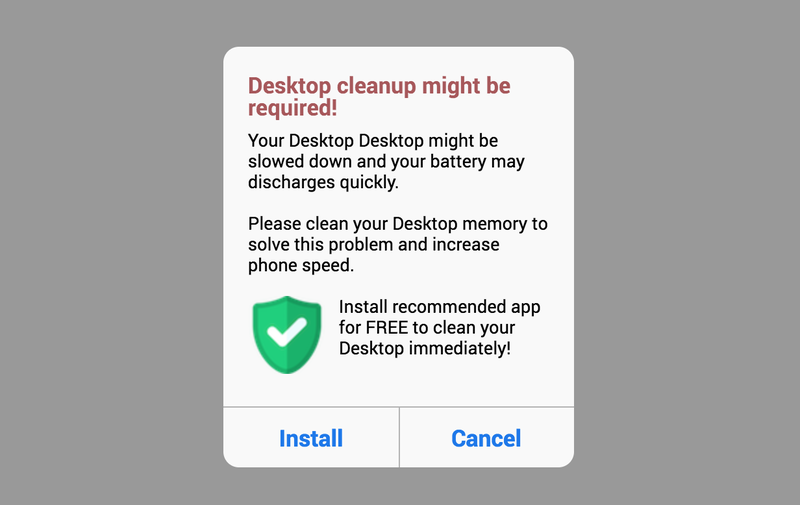
Image by Risk IQ
While performing a security audit on Android applications security researchers discovered a fake notification message that appeared to differ from the standard templates often used by hackers. The phishing message uses information about the victim’s devices such as the make and model in order to personalize them. This is one of the most common and effective blackmail tactics as many users cannot tell the difference between a legitimate and a fake message. The script that is spawned appears to be a redirect which also checks for the set language. This means that it is possible that there are several versions of the message.
The notification message prompts the victims to install or cancel an installation of the malware “Advanced Battery Saver” app. They are redirected to the Google Play entry which is designed like any other system utility app. Like other infected apps it uses fake developer credentials, user reviews and an elaborate description.
Malware Advanced Battery Saver Android App Capabilities
Once the victims users resort to install the app they will be asked to allow permssions such as the following
- Read sensitive log data
- Receive text messages (SMS)
- Receive data from Internet
- Pair with Bluetooth devices
- Full network access
- Modify system settings
When the application has been installed on the victim devices it will start a series of built-in commands. The analysis reveals that instead of improving battery life it actually reduces it. The app includes a built-in stealth protection mechanism that kills certain system or user-installed software. The common methods use signatures of well-known anti-virus programs or system utilities that can interfere with it’s correct execution.
Once the victim code is allowed to run undisturbed it will proceed running by instituting a information gathering module. It retrieves a list of both sensitive private data and device information: IMEI number, phone number, make and model, location, interests, passwords, accounts and etc. The next step is to connect to a hacker controlled server using a secure connection. It is used to collect the obtained information and to set up an ad clicker. It configures the infected devices to navigate to preset websites which in turn generates revenue for the hacker operators.
Consequences of Advanced Battery Saver Android App Customizations
We anticipate that future versions of the Advanced Battery Saver Android app may be configured with different parameters and delivered via another malicious payload. The hackers behind it can embed it in different forms or use another infection method.
The fact that there is no information available about the criminals behind means that this can be the work of either an individual hacker or a criminal collective. If its source code is made available either publicly on the hacker forums or traded on the markets then more dangerous offspring strains can be expected.
The full report on the malicious app is available on Risk IQ’s site.


