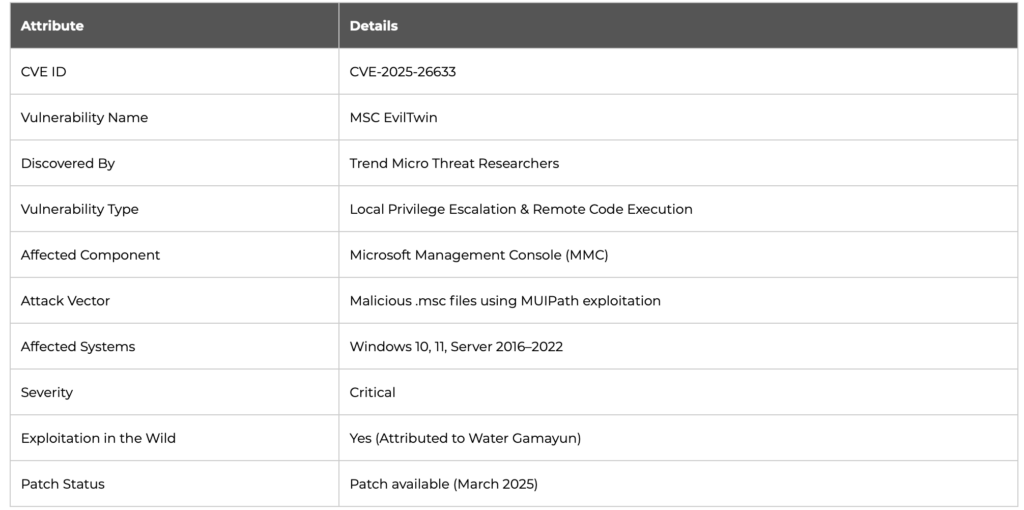
In early 2025, cybersecurity researchers uncovered a zero-day vulnerability in Microsoft’s Management Console (MMC), tracked as CVE-2025-26633 and nicknamed MSC EvilTwin. This critical flaw is being actively exploited by a threat group dubbed Water Gamayun and represents a dangerous vector for remote code execution on Windows systems.
What Is MSC EvilTwin (CVE-2025-26633)?
The CVE-2025-26633 vulnerability stems from how MMC loads localized resources (.msc files) via the MUIPath environment. Attackers can craft a malicious console file and place it within an en-US subdirectory, allowing it to override a legitimate one when executed. The exploit enables adversaries to load DLLs and execute shell commands without user interaction, bypassing traditional security controls.
CVE-2025-26633 Technical Details
- Vulnerability type: Local privilege escalation and remote code execution
- Attack vector: Malicious .msc files leveraging MUIPath
- Affected systems: Windows 10, 11, and Windows Server variants running vulnerable versions of MMC
- Discovered by: Trend Micro and community researchers
How the MSC EvilTwin Exploit Works
The core of the exploit lies in tricking MMC into prioritizing a malicious console file. This is achieved by planting two identically named .msc files:
- A decoy (benign) console file in the expected directory
- A malicious counterpart in the localized
en-USfolder
When executed, MMC loads the localized malicious file via its search path behavior, allowing the embedded ExecuteShellCommand method to run shell commands, essentially handing over control to the attacker.
Exploitation Flow
- User opens a legitimate-looking .msc file
- MMC searches
en-USand loads the attacker’s payload - Malicious
ExecuteShellCommandlaunches PowerShell or cmd scripts - Payloads are dropped and executed silently
Payloads Delivered via CVE-2025-26633
Trend Micro researchers observed that Water Gamayun used the MSC EvilTwin technique to deliver a variety of malware strains:
EncryptHub Stealer
This modular info-stealer captures browser credentials, system metadata, clipboard content, and cryptocurrency wallet data. It uploads stolen assets to attacker-controlled infrastructure via HTTP POST requests.
DarkWisp Backdoor
A sophisticated backdoor offering full shell access, file transfer, and persistence mechanisms. It communicates with a command-and-control (C2) server using TLS-encrypted traffic.
SilentPrism Implant
This stealthy implant evades detection by using legitimate Windows services. It’s primarily used for lateral movement and data exfiltration.
Rhadamanthys Stealer
A commercial infostealer-as-a-service (IaaS) solution found in underground forums. It targets FTP credentials, chat clients, and banking applications.
Water Gamayun: Threat Actor Behind the Exploitation
Water Gamayun is a suspected Eastern European threat group known for leveraging living-off-the-land binaries (LOLBins), exploiting Windows internals, and deploying custom malware via phishing and malvertising campaigns. They’ve shown a pattern of using zero-day exploits for initial access, followed by modular payloads for data theft and espionage.
Attack Infrastructure
The group operates using a rapidly shifting network of dynamic DNS domains, cloud hosting providers, and legitimate web services like GitHub and Dropbox to host payloads and exfiltrate data. Their infrastructure was tied to earlier campaigns targeting financial and energy sectors in North America and Europe.
Mitigation and Defensive Recommendations
1. Apply Microsoft Patches
Microsoft has released an emergency patch for CVE-2025-26633. Organizations should apply the patch immediately via Windows Update or MSRC.
2. Disable Console File Execution Where Possible
Restrict .msc file execution to trusted administrators. Use AppLocker or Windows Defender Application Control (WDAC) to block unknown .msc files.
3. Monitor for Indicators of Compromise (IOCs)
Look for unusual shell activity, registry key changes, and file execution from localized folders (e.g., C:\Windows\System32\en-US\).
4. User Awareness Training
Educate employees about phishing emails, suspicious attachments, and the risks of opening unknown console files.
5. Endpoint Detection & Response (EDR)
Use advanced EDR tools to detect exploitation behavior such as shell spawning from MMC or unsigned DLL loading.
Conclusive Thoughts
The exploitation of CVE-2025-26633 is proves that attackers are increasingly adept at weaponizing overlooked system functionalities to bypass traditional defenses. By abusing a relatively obscure component like MMC’s MUIPath, the Water Gamayun threat group has demonstrated not only technical sophistication but a strategic understanding of Windows internals that many defenders underestimate.
What makes this exploit particularly insidious is its stealth. The use of localized folders, seemingly benign .msc files, and native execution methods allows payloads to fly under the radar of many endpoint security solutions. Combined with the modular nature of the payloads, ranging from info-stealers to backdoors, the threat becomes multifaceted, persistent, and capable of deep infiltration across enterprise environments.
From a strategic perspective, CVE-2025-26633 exemplifies a broader trend in modern cyberattacks: the transition from brute-force tactics to precision abuse of trusted system behaviors. In response to this transition, defenders should focus on improving behavioral detection, zero trust architectures, and sophisticated threat hunting.
Ultimately, the lesson here is clear: vulnerabilities don’t always reside in new code or third-party apps. They often lie dormant in the very tools and processes organizations have used for decades. Recognizing and addressing this blind spot will be critical in defending against tomorrow’s threats.


