 The following material is created to raise awareness of organization cybersecurity and provide adequate protection advice against ransomware threats.
The following material is created to raise awareness of organization cybersecurity and provide adequate protection advice against ransomware threats.
Since ransomware has grown from a random idea to a million-dollar business and most of the attacks are conducted against organizations, we have decided to research into the field and bring several interesting ideas on how to adequately protect organizations and what systems are needed to perform this. During the research, we have stumbled into several very interesting presentations and network topologies which help us understand better how ransomware is distributed and how it targets organizations.

The Research
One interesting presentation which we stumbled upon during the research was the presentation regarding cybersecurity in healthcare at the Healthcare Compliance Institute
Now, one would ask, why to focus on healthcare cybersecurity. There is a very good reason for doing this, and it is because healthcare is the sector where more than 80% of attacks are conducted, primarily because of the funds poured into the sector and the ability to pay the ransom. And it is quite effective too; most healthcare institutions have paid ransom to retrieve important data back.
And given that the healthcare sector is changing and implementing more and more technology in it, and even more IoT gadgets, it is important for a network administrator to build an adequate network which will help him to respond adequately to the fast pace of today’s world.

The Threat
When we take a look at an average 21st-century ransomware it won’t take a lot of time to understand it. Most simplistic threats are usually purchased at the underground marketplace, and they even have license and support alongside them, meaning that it does not take explicit skills to master and use ransomware viruses. Basically, if we had to split the ransomware infection process into multiple different phases, as the researchers at the HCI have done, we would end up with four main areas of control:
- The Infection and Distribution Process.
- The Virus Itself and It’s Management.
- The Encryption used.
- The Ransom Payment.
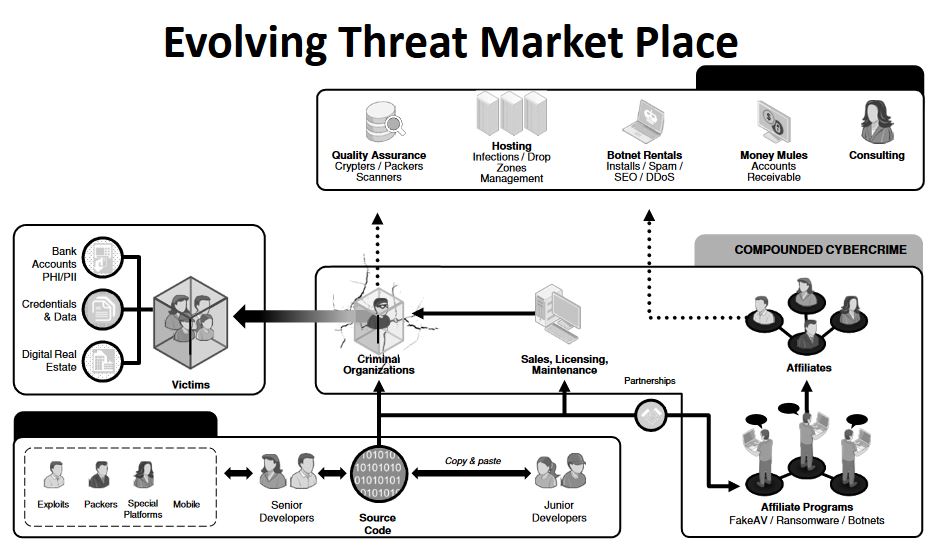 Image Source: Healthcare Compliance Institute (Beckie Smith)
Image Source: Healthcare Compliance Institute (Beckie Smith)
When we talk about infection and distribution, we have to realize that it is one of the most important areas in which most energy is thrown by the cybercriminals. This is primarily because ransomware is growing rapidly and the market for viruses has even become highly competitive, and everyone is battling over who has the best tools for the job. The most well-known tools for Infection are the ones who ensure successful infection to take place. These are the so-called cryptors, packers, scanners and other tools that ensure obfuscation. Cyber-criminal organizations put these tools as a priority to them, and they invest a lot in those tools, similar to how a company would invest in finding bugs in it’s software, for example. And while the infection is the key, it is also important to talk about spreading the malicious files that cause the infection. This is where cybercriminal organizations often turn to partners if they do not have the resources for this. These partners are usually black hat hackers with extensive experience in the field and a lot of resources. These resources are botnets, DDoS tools, and hardware, insanely huge databases of fake e-mail addresses, black SEO tools and many other tools that can make a simple .exe file famous in a matter of hours. And then, there is the issue of Hosting the distribution sites, also known as the C2 servers which are usually anonymized and tested before running the actual virus. These ghost hosts are with a very short lifespan, especially if they are distribution sites which contain the payload. So this about sums it up when it comes to distribution and infection.
When we discuss the virus files and their management, it all comes down to programmers. Such are usually people who were underappreciated or who have decided to make an extra buck by using their programming skillset. These developers create the source code for a ransomware infection and post the virus for sale, usually in the deep web. Some cybercriminal organizations, however, may have their developers who do the job, instead of risking to buy a code from others, who cannot be trusted. Whatever the case is, the virus should be programmed well and suitable to make a statement that it has infected the user. Furthermore, many cybercriminals value the ability to modify the virus itself – custom wallpaper, anti-VM tools, tools that change extensions, file names, custom ransom note, etc. Some ransomware viruses that are being sold online were even reported to offer hosting services for the command and control websites, where an administrator panel with every infected computer is viewed.
And when we talk about administrative panels and controlling the infection process, we have to discuss payment and payoff control. The cybercriminal organizations usually use anonymous e-mails or anonymous Tor-based web pages where the victim can communicate with them because customer support is very important. If organizations are attacked, it is important to known that the ransom amount is significantly larger.

The Attack
For an attack on a specific organization, for example, hospital to be conducted, the cybercriminals would first do some research about the organization they are about to hit. They will inspect the network and even infiltrate it partially to see what is it’s topology. Then they will contact the developers and affiliates to provide them the adequate obfuscators and tools for the specific software of the organization itself. For example, if the computers in the hospital are running updated versions of Windows 10 with advanced anti-malware protection, the attackers would choose obfuscation, which hides the virus from machine learning by injecting code into the legitimate rundll32.exe process, like the latest CERBER Ransomware string is doing.
Then, the attackers will begin the delivery process, and if some of the computers in the organizations have already been corrupted, they will use that and spread botnet or other intermediary malware. Another method is if they hack an e-mail of a user in the organization, for example, a senior manager and send a massive spam e-mail containing the infection file as an attachment. This technique is very effective, and some attackers have even been reported to use spoofed e-mails which were masked extremely well and cannot be differed from the original ones.
The next phase is to simply wait for the infection to happen and lay low while they are controlling the process and waiting for the payoff to be made. From there multiple “money mule” accounts are usually used in a sophisticated network of online cryptocurrency accounts which are then paid off to multiple affiliate wallets. Then, paid amounts are usually laundered through a BitCoin mixing service which completely hides the funds and then pays them off the authors of the virus.

How to Fight Back?
Experts with an extensive background in malware research outline that network administrators and security professionals should focus on these four key phases when they plan organization protection:
The Preparation Of The Defense And Budget Management
This phase includes handling the investments for cybersecurity and separating the activities that need to be conducted to achieve short term(hardware, software, etc) and long term(employee education) goals.
The Protection and Intrusion Detection
This is most likely what is the area of the highest importance, according to the researchers at the Institute. It includes building the right network with cybersecurity in mind. Basically, such networks should be focused on completely separating the employees from the guest users and even creating a third-group of devices as shown in the topology created by the researchers below:
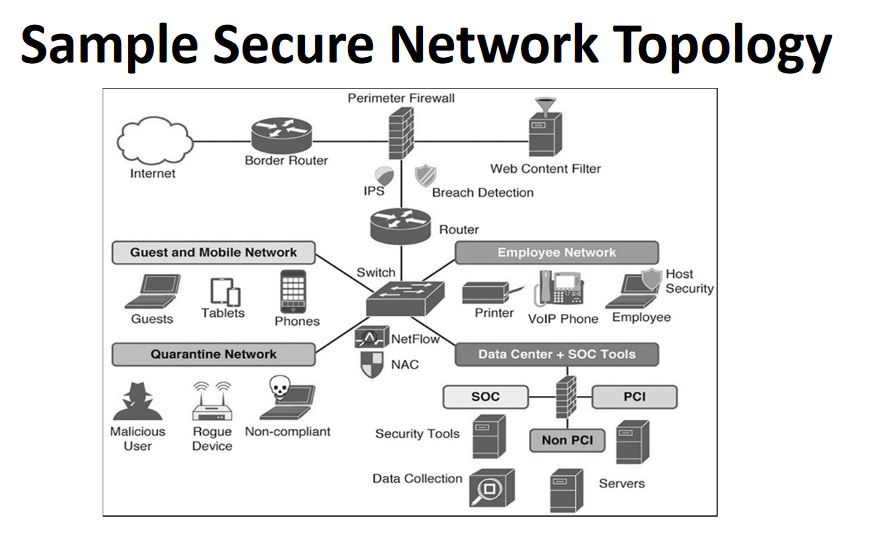 Source: Healthcare Compliance Instute
Source: Healthcare Compliance Instute
As visible from above, NAC (Network Admission Control) has been used in combination with the NetFlow feature. The NAC is used primarily because it restricts multiple network resources based on a pre-configured network criteria and policies. If those policies fail to be met by a device, the NAC does not let it further into any of the other networks and leaves it in the Quarantine one with lowest permissions of all. The NetFlow feature is used to collect the traffic of those devices as it enters and exits the main device (ex. the switch). It also has the so-called application analysis which sees what data passes and does this data behave in an intrusive manner.
And besides those features, there may also be multiple other layers of protection added throughout the whole network, not only the quarantine one. The best practice is to add protection for each sub-network build around the main controller device and separate the networks as much as possible while keeping them interconnected but limited only to administrative accounts.
Threat Response
This is the area where the infection is already inevitable. Usually, organizations with adequate protection have protocols that are often changed regarding how they react when being attack and who do they contact. According to the researchers at HCI, these protocols may include several key processes:
- Data Correlation.
- A collection of logs from the devices.
- Reporting of the intrusion and damages.
- Having adequate knowledge base to search information in.
- Having adequate threat database.
- Research of the threat and development based on the scenario.
Usually, this is not something that your average network administrator is capable of knowing. However, if a team is used which consists of different specialists in different fields to investigate the situation, the time for handling the threat would rapidly decrease. But administrators have to be trained on how to perform the first response when there is a threat, and for this, protocols by security organizations are necessary to be implemented, which should be included in the preparation phase of investment.
Threat Recovery
This final aspect of the system includes an implementing and learning from the threat to not only recover like traditionally but in an improved and updated manner to avoid future intrusions of this type to happen. It involves analyzing the aggregated data from the threat and implementing the key aspects on how the threat infection was conducted. It can ensure the adequate configuration of the network the best way possible to minimize future risk.
The Bottom Line
As a conclusion, the focus on organization cybersecurity has cost a fortune the last couple of years. And most of the attacks done by ransomware were on systems which were not properly backed up and secured. This is the reason it is strongly recommended not only to look at it as an investment but oversee the whole processes from the inside out and research and test it extensively. Of course, this does not mean that you will create a 100% ransomware-proof system, but it will result in a security system that will repel most sophisticated threats out there.
And furthermore, as an IT sphere, cybersecurity is moving onto a whole new level of data management and device security – the Internet of Things. We have already seen many IoT devices that were hacked, and with IoT Botnets like Mirai, we believe that the focus of experts should be focused on handling mobile and IoT devices more often, then just centralizing security to big devices, like multilayer switches, routers, firewalls and others.