 Criptografia não é algo ruim. De fato, ferramentas de criptografia são projetadas inicialmente para ajudar, proteger os dados e mantê-los longe de intenções maliciosas. Não importa quão bom seja, a criptografia tem estado no centro de muitos debates.
Criptografia não é algo ruim. De fato, ferramentas de criptografia são projetadas inicialmente para ajudar, proteger os dados e mantê-los longe de intenções maliciosas. Não importa quão bom seja, a criptografia tem estado no centro de muitos debates.
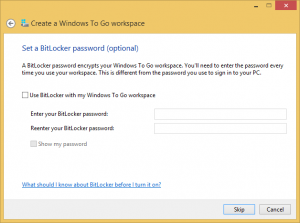
Você encontrará especialistas em ambos os lados da história - pró-criptografia e contra ela, isso é. Não importa qual seja a verdade, os pesquisadores devem sempre encontrar tempo e urgência para investigar o assunto e fornecer informações aos usuários. Um dos estudos mais recentes que enfatiza a criptografia diz respeito ao BitLocker, Utilitário de criptografia de disco da própria Microsoft. Foi testado em profundidade por Ian Haken de Synopsys, que revelou em seu vasto relatório (publicado em novembro 12, 2015) que a ferramenta pode ser facilmente contornada.
É assim que o relatório de Haken começa:
A criptografia de disco completo é uma medida defensiva em que todos os dados armazenados em um disco ou volume físico são criptografados, portanto, protegendo todos os dados armazenados em um dispositivo, como senhas salvas, e-mails, tokens de sessão, e propriedade intelectual (...) BitLocker é a solução de criptografia de disco completo da Microsoft incluída em certas versões do Windows, introduzido pela primeira vez em 2007. Este artigo descreve um ataque que é capaz de contornar a autenticação do Windows, mesmo na presença de criptografia de disco completo do BitLocker, e, assim, permite que um invasor acesse os dados de um usuário ou instale software. Em sistemas efetuados, esse ataque, portanto, ignora todas as proteções oferecidas pelo BitLocker.
BitLocker - Sim ou Não?
Antes de o BitLocker ser implementado no Windows, um codificador malicioso pode facilmente inicializar um sistema Linux ativo e acessar os arquivos do usuário no disco rígido. Hoje em dia, O BitLocker deve estar aqui para oferecer criptografia impenetrável de disco completo. Contudo, o pesquisador da Synopsys revelou o fato preocupante de que o recurso BitLocker pode ser omitido, nenhuma habilidade sofisticada de atacante é necessária.
Quem está em perigo devido à vulnerabilidade?
não é de surpreender, os computadores corporativos são os mais propensos a sofrer um ataque que ignora o BitLocker. Imagine o seguinte cenário. Um invasor tira um laptop da rede, o domínio não pode ser alcançado. O computador então se retira para um nome de usuário local e senha armazenados em seu cache.
(...) O ataque para ignorar a autenticação local e, assim, derrotar a criptografia de disco total do BitLocker assume as seguintes condições:
1. O BitLocker está habilitado sem autenticação de pré-inicialização, para que o invasor seja capaz de inicializar a máquina na tela de login.
2. A máquina se juntou a um domínio e um usuário de domínio autorizado fez login anteriormente na máquina.
Como Haken realizou seu teste de vulnerabilidade?
Ele descobriu uma maneira de substituir a senha em cache (desconhecido para o atacante). A única coisa necessária aqui é configurar um servidor de domínio falso idêntico ao original, e criar uma conta de usuário com uma senha criada há muito tempo, para iniciar uma mudança de senha baseada em política.
A falha foi corrigida?
A Microsoft já corrigiu o bug, prometendo que nenhum invasor o explorou na realidade. O bug deveria ter sido corrigido com o lançamento das atualizações de segurança no Boletim de segurança MS15-122. A Microsoft também disse que contornar o BitLocker poderia acontecer apenas se uma série de eventos específicos ocorressem.
De acordo com Haken, a vulnerabilidade é devido ao fato de que 'Naquele momento, um invasor com controle físico de uma máquina cliente significa que ela já está totalmente comprometida.'Ele também acrescenta que'quando os modelos de ameaça mudam, a arquitetura de segurança dos aplicativos pode precisar ser cuidadosamente revisada junto com eles.' Palavra.
Salte para o todo relatório de Ian Haken.
Mais para ler:
janelas 10 vs. janelas 7
Chega de Google Chrome no Vista e XP


