In the digital era, email scams have rapidly evolved, becoming more sophisticated and challenging to recognize. Among the most alarming are the “Hello Perv” email scams, striking fear into the hearts of many by threatening to expose their online activities.
This form of digital extortion uses psychological tactics to manipulate victims into paying, often demanding ransom in Bitcoin. Our comprehensive guide will shed light on the mechanics behind these scams, their evolution, and, most importantly, how you can protect yourself from becoming a target.
By staying informed and leveraging security tools, such as SpyHunter, you can navigate these threats with confidence and maintain your online safety.
HelloPerv Scam Summary
| Type | Email Scam Message |
| Short Description | A scam that tries to scare you into paying a ransom fee for a supposed breach of your privacy. |
| Symptoms | You receive an email message that tries to trick you into thinking that you got recorded while masturbating. |
| Distribution Method | Email Spam Messages, Suspicious Sites |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
Understanding “Hello Perv” Email Scams: A Brief Overview
Email scams have been a persistent issue in the digital age, evolving alongside technological advancements. One such deceptive tactic is the “Hello Perv” email scam, which creates a pressing concern for many individuals online.
This scam, like many others, leverages fear and the potential for public embarrassment to extort money from victims. By understanding the mechanics and implications of these scams, individuals can better protect themselves from falling prey to cybercriminals.
What Exactly Is a “Hello Perv” Email Scam?
The “Hello Perv” email scam is a form of sextortion. In this scam, cybercriminals send threatening emails to their victims, claiming to have obtained compromising videos or images.
These emails often assert that the cybercriminals have recorded the recipients through their computer’s webcam while they were visiting adult websites.
The scammers then demand a ransom, typically in Bitcoin, threatening to release the compromising material to the victim’s contacts if their demands are not met. It is crucial to recognize that these claims are almost always baseless, designed to coerce victims into paying out of fear and desperation.
The Evolution of “Hello Perv” Email Scams Over the Years
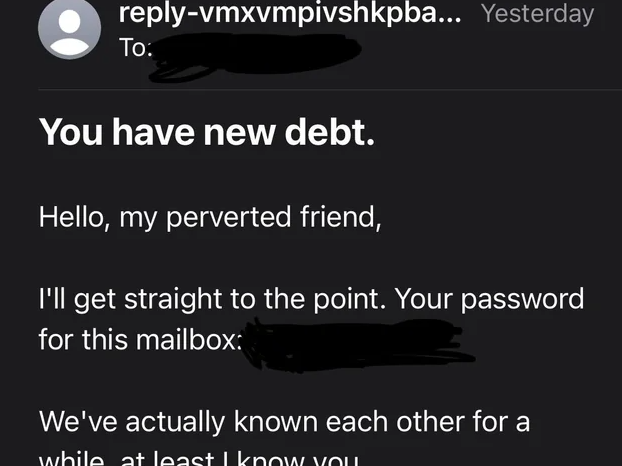
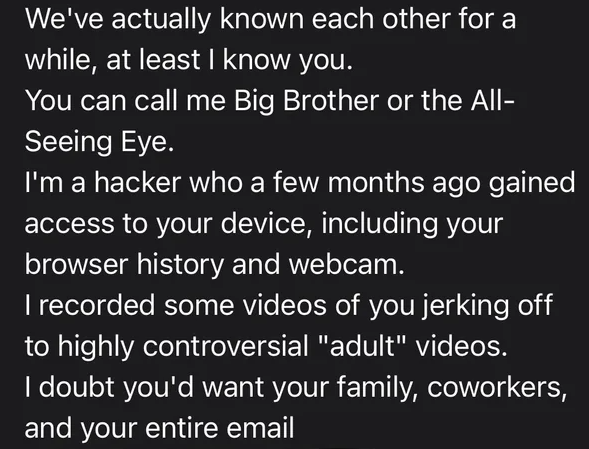
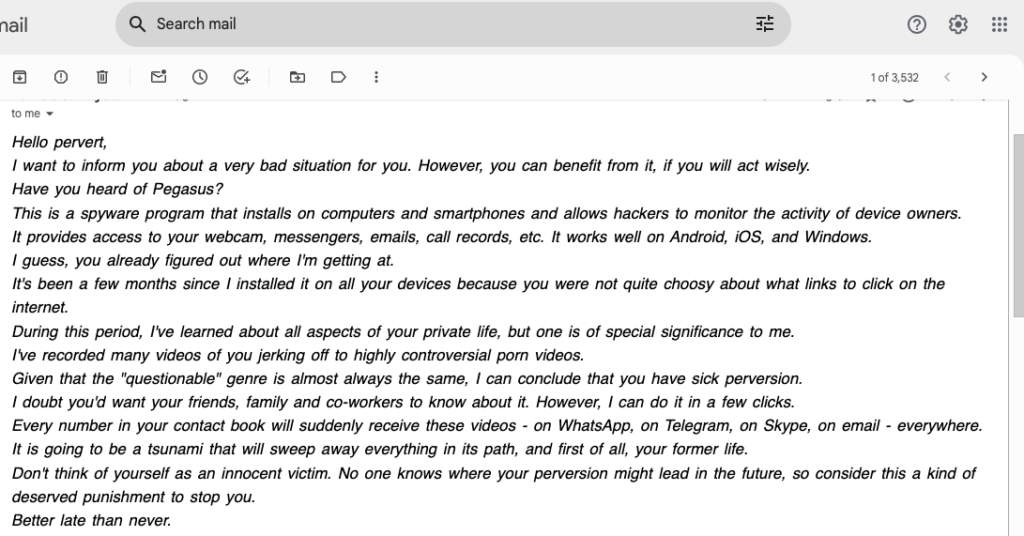
Over the years, the “Hello Perv” email scams have evolved in complexity and tactic. Initially, these scams were relatively straightforward, with blanket threats sent out en masse, hoping to snare unsuspecting victims. However, as public awareness has grown, so too has the sophistication of these scams.
Modern iterations may include personal information, such as passwords or phone numbers, obtained from previous data breaches, to lend credibility to the threats. Additionally, the language and structure of the emails have become more convincing, making it increasingly difficult for recipients to distinguish them from legitimate threats.
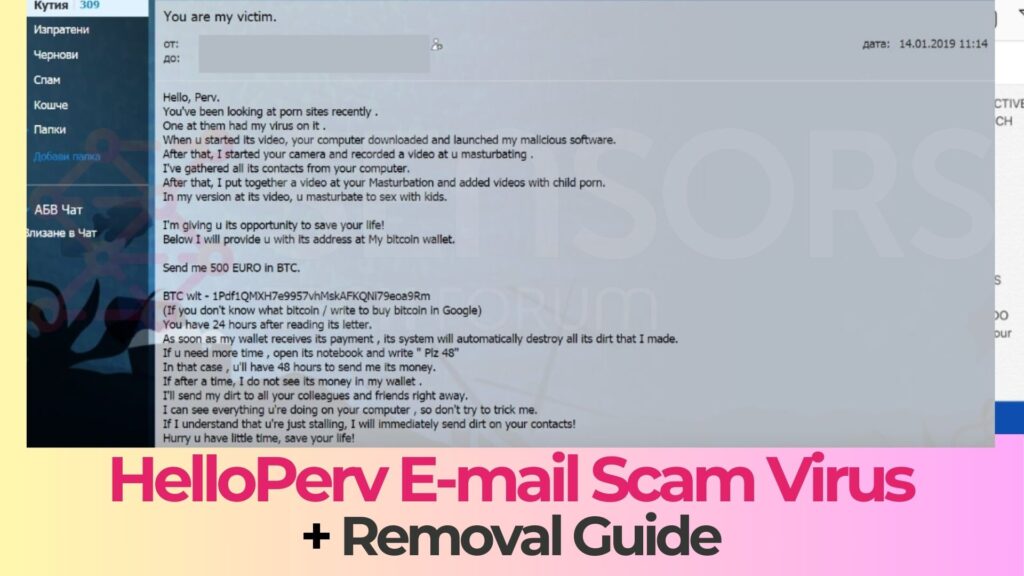
One of the scams has the following message to victims:
Subject: You are my victim.
Hello, Perv.
You’ve been looking at porn sites recently .
One at them had my virus on it .
When u started its video, your computer downloaded and launched my malicious software.
After that, I started your camera and recorded a video at u masturbating .
I’ve gathered all its contacts from your computer.
After that, I put together a video at your Masturbation and added videos with child porn.
In my version at its video, u masturbate to sex with kids.
I’m giving u its opportunity to save your life!
Below I will provide u with its address at My bitcoin wallet.
Send me 500 EURO in BTC.
BTC wlt – 1Pdf1QMXH7e9957vhMskAFKQNi79eoa9Rm, 1JVMTup4zuS1JMGXAYYRgvyr2PUmNnY6g2
(If you don’t know what bitcoin / write to buy bitcoin in Google)
You have 24 hours after reading its letter.
As soon as my wallet receives its payment , its system will automatically destroy all its dirt that I made.
If u need more time , open its notebook and write ” Plz 48″
In that case , u’ll have 48 hours to send me its money.
If after a time, I do not see its money in my wallet .
I’ll send my dirt to all your colleagues and friends right away.
I can see everything u’re doing on your computer , so don’t try to trick me.
If I understand that u’re just stalling, I will immediately send dirt on your contacts!
Hurry u have little time, save your life!
Furthermore, distribution methods have broadened beyond simple email blasts. Social media platforms and targeted phishing campaigns have become new vectors for these scams, allowing criminals to personalize their approach and potentially increase their success rate.
Despite these advancements, the core advice remains the same: recipients of such emails should exercise caution, verify the legitimacy of any threats, and use reliable security software to protect their devices.
For anyone concerned about falling victim to schemes like the “Hello Perv” scam, employing a robust security tool like SpyHunter can offer an additional layer of protection. SpyHunter is engineered to detect and remove malware threats, offering peace of mind to users navigating the complex digital environment. By staying informed about the nature of these scams and proactively protecting your online presence, you can greatly reduce the risk of being extorted by such malicious campaigns.
Other version of the scam has the following message:
Subject: Hi perv. I recorded you masturbating! I have captured ‘*********.mp4’!
ATTN: *********
THIS IS NOT A JOKE – I AM DEAD SERIOUS!
Hi perv,
The last time you visited a p0rnographic website with teens,
you downloaded and installed software I developed.My program has turned on your camera and recorded
the process of your masturbation.My software has also downloaded all your email contact lists
and a list of your friends on Facebook.I have both the ‘*********.mp4’ with your masturbation
as well as a file with all your contacts on my hard drive.You are very perverted!
If you want me to delete both the files and keep the secret,
you must send me Bitcoin payment. I give you 72 hours for payment.If you don’t know how to send Bitcoins, visit Google.
Send 2.000 USD to this Bitcoin address immediately:
(copy and paste)
1 BTC = 3,580 USD right now, so send exactly 0.567380 BTC
to the address provided above.
The Anatomy of a Sextortion Scam Email
Sextortion scam emails are a type of cybercrime that manipulates victims through fear by claiming to have compromising information. These emails typically follow a detailed framework designed to instill panic, shame, and a sense of urgency, pushing the recipient towards making a hasty payment, usually in Bitcoin. Understanding the anatomy of these scams is crucial for recognizing and avoiding them.
Key Elements Scammers Use to Instill Fear
The most effective sextortion emails exploit human emotions with precision. Here’s a closer look at how they do it:
- Provoking Emotions: Scammers draft emails to tap into fundamental fears about privacy and reputation. By alleging possession of intimate videos or photos and threatening to distribute them, these emails create a state of panic and distress.
- Urgency and Demand: A typical scam email will include a payment demand with a tight deadline, usually 24-48 hours, to prevent the alleged distribution of compromising material. This sense of urgency leaves little time for rational thought, pressing the recipient to act hastily.
- Bitcoin Payment: Demands for payment are often made in Bitcoin to avoid tracing. The specificity of the Bitcoin wallet address, coupled with a precise payment amount, adds a misleading layer of authenticity to the scam.
- Confidentiality: These emails usually advise against contacting authorities or seeking help, attempting to isolate the victim and prevent them from questioning the validity of the scam.
By familiarizing themselves with these common tactics, individuals can better defend against the emotional manipulation employed by sextortion scammers.
Distinguishing Characteristics of Scam vs. Legitimate Emails
It can be a problem to identify sextortion scams, especially when they contain seemingly personal information. However, there are certain characteristics that can help differentiate a scam from a legitimate threat:
- Vagueness: While a scam email might initially seem personalized, it typically lacks specific details about the alleged evidence. This nonspecific nature is a hallmark of mass-produced scam attempts.
- Error-laden Content: Sextortion emails often contain grammatical errors and unusual phrasing, which can be red flags. Legitimate companies or entities usually proofread their communication extensively.
- Suspicious Attachments or Links: Legitimate entities will not send unsolicited emails with attachments or links demanding immediate action. Instead, they will provide a secure method of verification. Scam emails, on the other hand, may include dangerous links intended to infect your device with malware.
- Unusual Payment Methods: Any legitimate issue regarding privacy or security breaches would not demand payment in cryptocurrency. This method of payment is favored by scammers due to its difficulty to trace.
When dealing with suspicious emails, it’s essential to approach them with skepticism. If you suspect a sextortion attempt, using security software like SpyHunter can provide an additional layer of defense by detecting and removing malware that could compromise your online security.
Remember, the goal of scam emails is to exploit the fear of exposure and shame to extract money. By staying informed and vigilant, you can protect yourself from becoming a victim. Verify the legitimacy of any alarming claim through direct contact with the company or entity allegedly involved and never rush into making a panicked payment.
Common Tactics Used in “Hello Perv” Email Scams
The “Hello Perv” email scam, a form of sextortion, employs a variety of tactics designed to intimidate, threaten, and ultimately deceive the recipient into paying a ransom, usually in the form of Bitcoin.
These tactics leverage psychological manipulation and exploit fears of public embarrassment and legal repercussions. Understanding these common strategies can empower individuals to recognize and effectively respond to such threats.
- Fear Appeal: Scammers concoct a narrative that exploits the recipient’s fear of being publicly shamed or exposed for visiting adult websites. They claim to have recorded videos or possess other incriminating evidence that, if disclosed, would harm the recipient’s reputation.
- Urgency: These emails often include a tight deadline by which the payment must be made, instilling a sense of urgency. This tactic pressures the recipient to act quickly, ideally without taking the time to question the scam’s legitimacy or consult with others.
- Anonymity: By demanding payment in Bitcoin, scammers hide behind the veil of cryptocurrency’s relative anonymity, making it difficult to trace the payment back to any individual.
- Technical Fabrication: The emails may contain technical jargon or claims of sophisticated software capabilities to convince recipients that the threat is genuine and that the scammer possesses the claimed malware-driven evidence.
The Psychological Warfare Behind Email Scams
Email scams like “Hello Perv” are meticulously crafted to leverage human psychology against the victim. Scammers understand that the mere suggestion of surveillance and exposure, coupled with the perceived legitimacy of their claims, can be enough to incite fear, shame, and panic.
This psychological manipulation is central to the success of sextortion scams, pushing individuals towards irrational actions—specifically, to complete specific demands for payment. The key to thwarting these attempts lies in recognizing the signs of manipulation and responding with informed skepticism rather than fear.
Why Do Scammers Favor Bitcoin as Payment?
Bitcoin and other cryptocurrencies are the preferred payment methods for sextortion scams for several reasons, key among them being the anonymity they offer. Unlike traditional financial transactions, Bitcoin payments can be made and received without revealing the users’ identities, making it exceedingly difficult for authorities to trace the scammers.
Also, Bitcoin transactions are irreversible, ensuring that once the payment is made, the victim cannot reclaim their funds, even upon realizing the scam. This combination of anonymity and finality makes Bitcoin an attractive tool for scammers looking to exploit their victims without leaving a paper trail back to themselves.
Steps to Take If You’ve Received a “Hello Perv” Email
Receiving a “Hello Perv” email can be unsettling, prompting fear and confusion. While the immediate reaction might be panic, it’s crucial to remain calm and approach the situation with a clear mind. Acting hastily can complicate matters, making you vulnerable to further scams. Follow these steps to secure your information and peace of estate.
Immediate Actions to Ensure Your Safety
- Do Not Respond or Pay: The first rule is not to engage. Responding or paying the demanded ransom only marks you as a susceptible target for future scams.
- Delete the Email:
Remove the scam email from your inbox. This prevents accidental interactions in the future and helps you move on from the attempt.
- Scan Your System: Use a reputable anti-malware tool like SpyHunter to scan your system for any malware that might have been installed without your knowledge. This ensures your system is clean and secures against hidden threats.
- Change Compromised Passwords: If the email includes a password you recognize, change it immediately along with any other accounts that use the same or similar passwords. Opt for strong, unique passwords for each account.
- Contact Your Bank: If you’ve shared financial information recently or suspect unauthorized transactions, contact your bank to alert them of potential fraud. This can prevent financial losses and secure your accounts.
Protecting Your Personal Information After a Scam Attempt
Once you’ve handled the immediate aftermath of a “Hello Perv” scam email, it’s essential to take steps to protect your personal information more broadly.
- Enable Multi-Factor Authentication (MFA): Activate MFA on all platforms that offer it. This adds an extra layer of security, making it harder for attackers to gain unauthorized access.
- Stay Informed: Educate yourself about common online scams and the latest cybersecurity threats. Knowledge is a powerful tool in preventing future attacks.
- Regularly Update Software: Ensure that all your software is up-to-date, including operating systems and antivirus programs. Outdated software can be vulnerable to attacks.
- Be Cautious with Downloads: Avoid downloading software or opening attachments from unknown sources. These can contain malware intended to compromise your system or steal personal information.
- Use Trusted Antivirus Software: A robust antivirus solution like SpyHunter can protect your digital life by detecting and removing malware, and providing real-time protection against threats.
By following these steps and maintaining vigilance, you can significantly reduce your risk of falling victim to “Hello Perv” and other email scams. It’s important to remember that these threats rely on inducing panic to cloud your judgment. Keeping a level head and taking decisive action is your best defense.
Preventative Measures to Avoid Email Scams
In an online world brimming with scams and phishing attempts, taking proactive steps to safeguard your email is more important than ever. By implementing a few simple strategies, you can significantly reduce the risk of falling victim to these malicious efforts. Here’s how to protect yourself and your digital identity from unwanted intrusions.
Strengthening Email Security: Tips and Tricks
Enhancing your email security is the first line of defense against cyber threats. Start by using strong and unique passwords for each of your accounts. This might seem like a basic tip, but it’s crucial for maintaining strong security. Opt for passwords that combine letters, numbers, and symbols. Equally important is enabling two-factor authentication (2FA) on all accounts that offer it. This adds an extra layer of protection, making it harder for hackers to gain unauthorized access to your personal information.
- Regularly updating your passwords and avoiding the use of the same password across multiple sites.
- Be cautious of unsolicited emails, especially those that ask for personal or financial information.
- Use email filters and security settings to help screen potentially dangerous emails.
- Be selective about where you share your email address, especially on websites and online forums.
How to Educate Friends and Family About Email Scams
Protecting yourself from email scams is one thing, but it’s equally important to ensure that your friends and family are also aware of how to stay safe online. Start by sharing your knowledge about recognizing phishing attempts. Key indicators include unexpected attachments, misspelled URLs, and requests for personal information. Encourage them to question the legitimacy of any email that feels ‘off’ and to verify the sender by other means if necessary.
- Share stories of common scams to make the dangers more relatable and understandable.
- Teach them to double-check the URLs and email addresses of senders before clicking on links or attachments.
- Suggest installing reliable security software, such as SpyHunter, which can offer an additional layer of protection by identifying and removing malicious threats.
Why Updating Your Software Regularly is Crucial
One often overlooked aspect of digital security is the importance of keeping software up to date. This goes beyond just the operating system; it includes all applications and especially your antivirus software. Developers frequently release updates and patches to address vulnerabilities that cybercriminals might exploit. By setting your software to update automatically, you can ensure that you’re always running the most secure version.
- Regular software updates help protect against the latest threats by fixing security holes.
- Check for updates on all devices, including smartphones and tablets, as these can also be targeted by scammers.
- Consider using a dedicated security solution like SpyHunter, which is constantly updated to combat the ever-evolving threat landscape, ensuring your system stays protected against potential email scams.
By adopting these straightforward but effective measures, you can create a robust defense system against email scams, safeguarding both your personal information and that of your loved ones. Remember, staying informed and cautious is your best weapon in the ongoing battle against cyber threats.
Implementing Robust Security Practices for Long-Term Protection
In an age where digital threats loom at every corner, establishing strong security practices is crucial for safeguarding personal and sensitive information from scammers and cybercriminals. One of the simplest yet most effective steps you can take is to ensure your digital hygiene is impeccable. This includes regularly updating your passwords, being vigilant about the links and attachments you click on, and staying informed about the latest cybersecurity trends and threats. It’s not just about protecting yourself from immediate threats but also about laying a foundation that keeps your digital presence secure over the long term.
Utilizing Multi-Factor Authentication: A Must-Do
Multi-factor authentication (MFA) adds an additional layer of security that goes beyond the traditional username and password model. By requiring two or more verification methods—such as a password combined with a text message code or a biometric factor—MFA ensures that even if one credential becomes compromised, unauthorized users cannot easily gain access to your accounts. Setting up MFA across all your critical accounts, including emails, banking, and social media, substantially reduces the risk of identity theft and unauthorized access.
- Begin with Essential Accounts: Start by securing your most sensitive accounts, like email and online banking, to ensure they’re safeguarded against unauthorized access.
- Explore Authentication Options: Many services offer various forms of MFA. Choose one that balances security with convenience, such as authentication apps, which are generally more secure than SMS codes.
- Regular Review and Update: Make it a habit to periodically check and update your MFA settings to fend off any new vulnerabilities.
The Role of Comprehensive Antivirus Software in Scam Prevention
Antivirus software plays a pivotal role in maintaining your online safety. Effective antivirus programs do more than just scan for and remove malware; they offer real-time protection against a wide range of threats, including viruses, spyware, ransomware, and phishing attacks. With new threats being developed daily, having a comprehensive antivirus solution that is regularly updated is non-negotiable for anyone seeking to protect their digital environment.
- Selecting the Right Antivirus: Opt for reputable antivirus software that provides comprehensive threat protection. Consider features like real-time scanning, automatic updates, and the ability to spot and block phishing attempts.
- Periodic Scans: In addition to real-time protection, schedule regular full-system scans to catch any threats that may have slipped through the cracks.
- Maintain Up-to-Date Protection: Ensure your antivirus software is always updated to the latest version. Cybercriminals constantly evolve their tactics, and staying updated means you’re protected against the latest threats.
For those seeking an advanced layer of protection, SpyHunter offers a robust solution designed to detect, remove, and block malware, potentially unwanted programs (PUPs), and other malicious objects. By integrating cutting-edge technology, SpyHunter ensures your digital safety is never compromised.
Spotting Malware and Scamware: Keep Your Devices Safe
As the digital environment becomes increasingly complex, staying ahead of malware and scamware is crucial for safeguarding personal and organizational data. These malicious software types are designed to infiltrate, damage, or gain unauthorized access to your computer system, often leading to data theft or loss. Recognizing the indicators of malware and scamware can help you take prompt action to prevent potential harm.
Malware can manifest in several forms, including viruses, worms, trojan horses, and ransomware. Typical signs of an infection include a sudden slowdown in computer performance, unexpected pop-up ads, and the appearance of unfamiliar applications or files. Scamware pop-ups, often encountered through phishing emails, tricks users into compromising their security. Watch out for emails requesting sensitive information, threatening messages demanding immediate action, or offers that seem too good to be true.
To effectively spot malicious activities, be vigilant about changes in your system’s performance and maintain
- Windows
- Mac OS X
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
- Safari
- Internet Explorer
- Stop Push Pop-ups
How to Remove Hello Perv from Windows.
Step 1: Scan for Hello Perv with SpyHunter Anti-Malware Tool



Step 2: Boot Your PC In Safe Mode





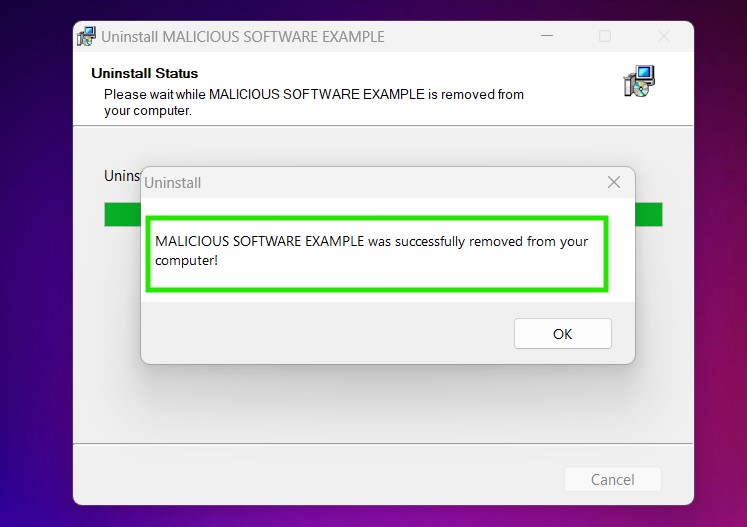
Step 3: Uninstall Hello Perv and related software from Windows
Uninstall Steps for Windows 11
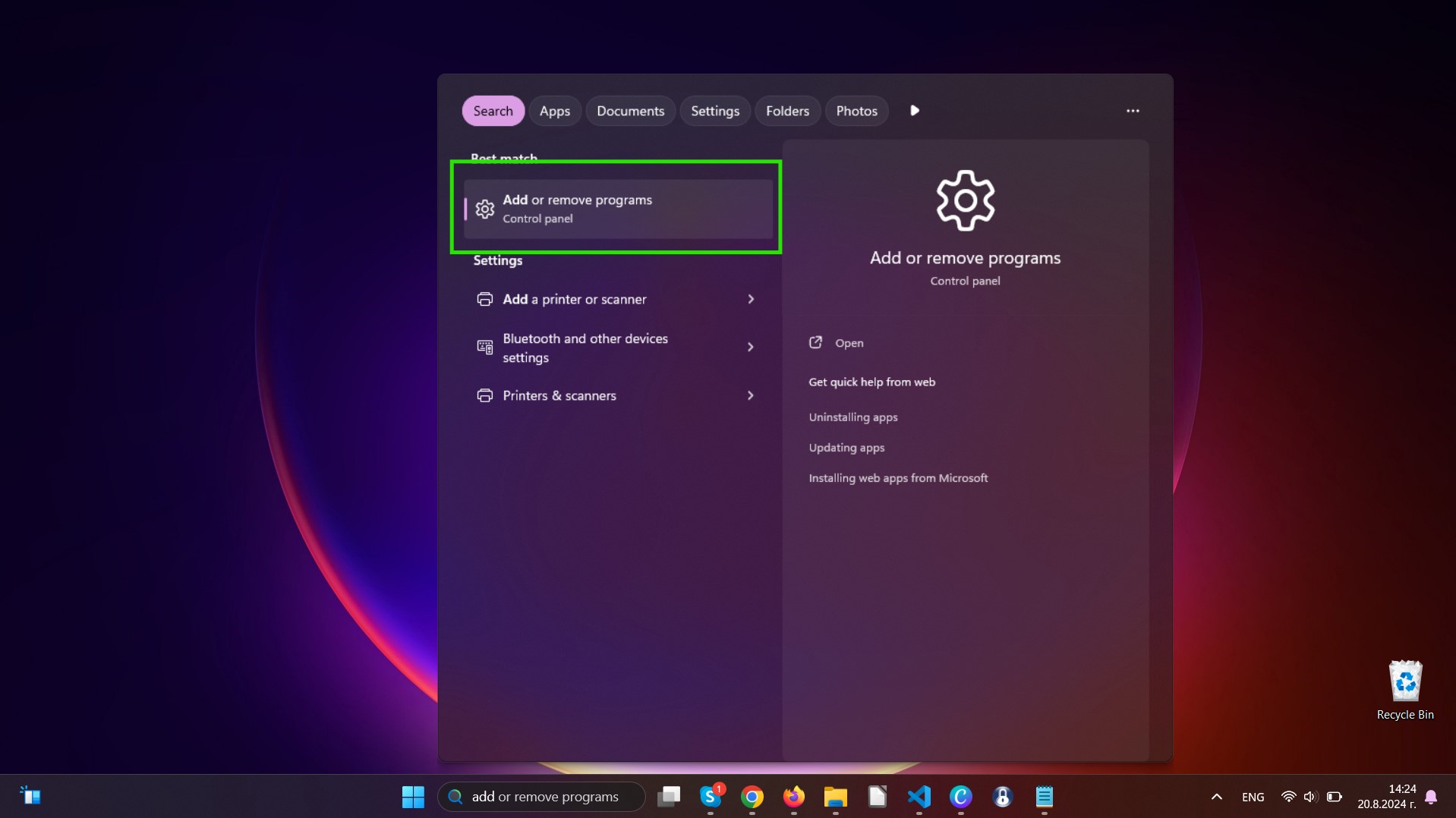
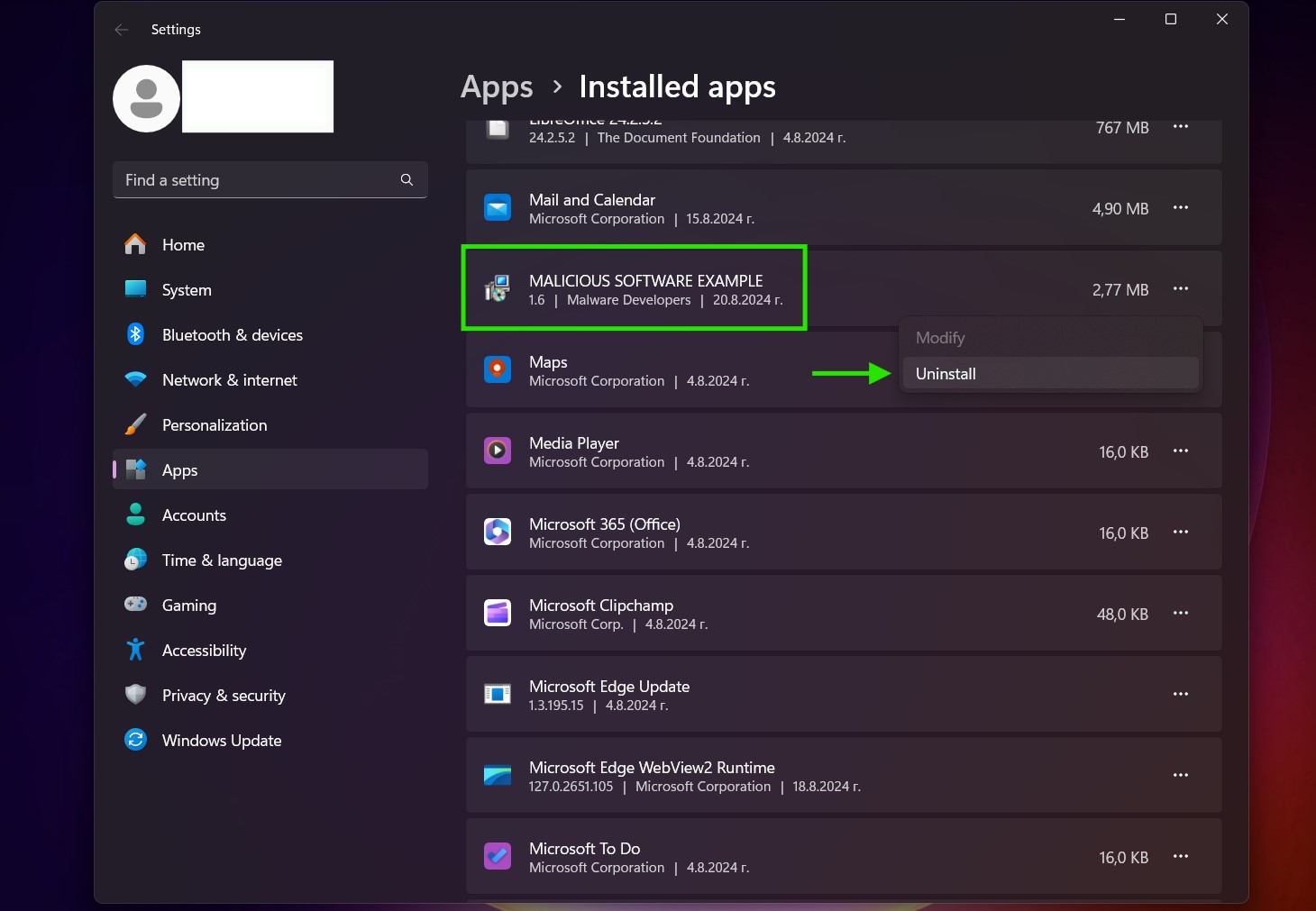
Uninstall Steps for Windows 10 and Older Versions
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully uninstall most programs.
Follow the instructions above and you will successfully uninstall most programs.
Step 4: Clean Any registries, Created by Hello Perv on Your PC.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by Hello Perv there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Video Removal Guide for Hello Perv (Windows).
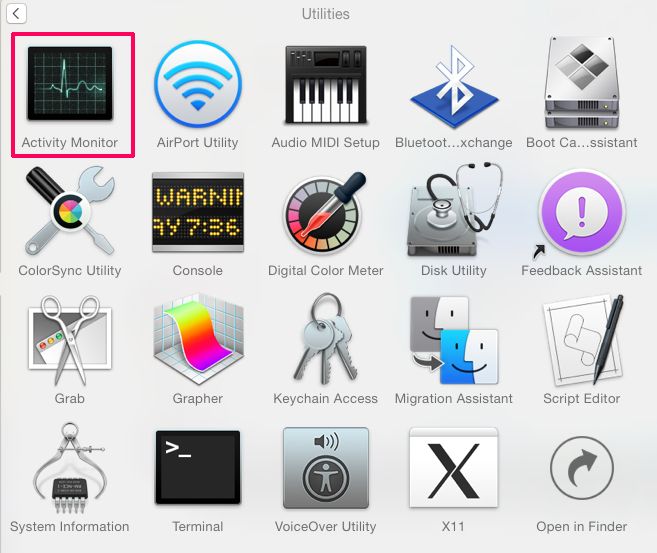
Get rid of Hello Perv from Mac OS X.
Step 1: Uninstall Hello Perv and remove related files and objects
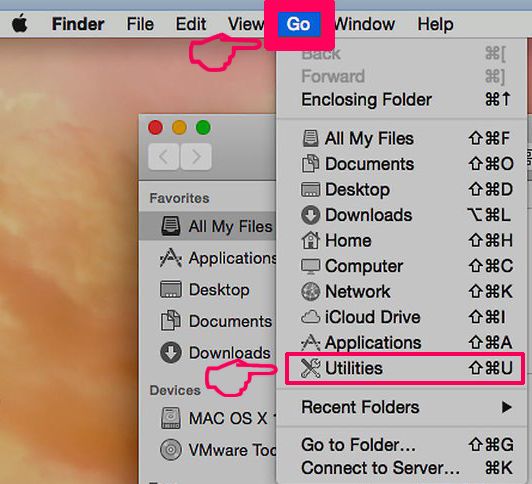
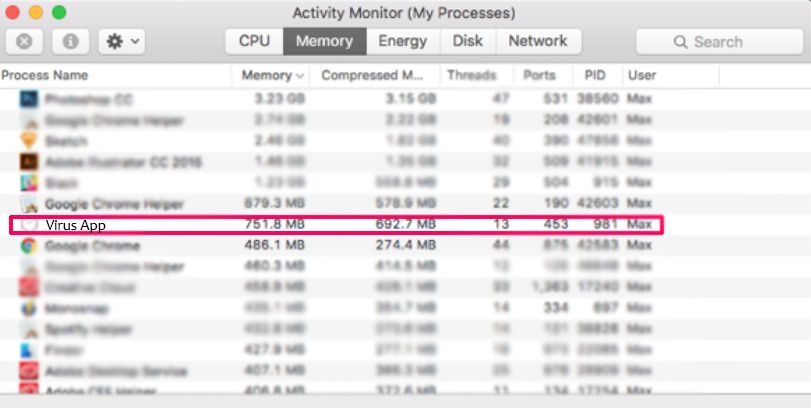
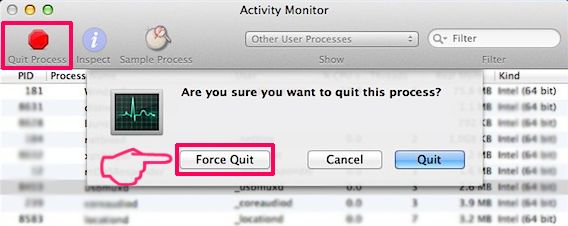
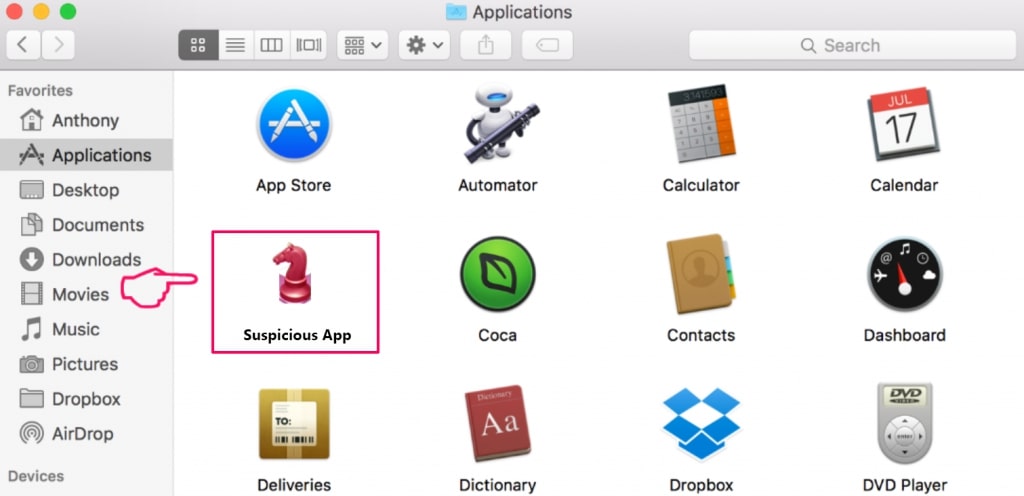
Your Mac will then show you a list of items that start automatically when you log in. Look for any suspicious apps identical or similar to Hello Perv. Check the app you want to stop from running automatically and then select on the Minus (“-“) icon to hide it.
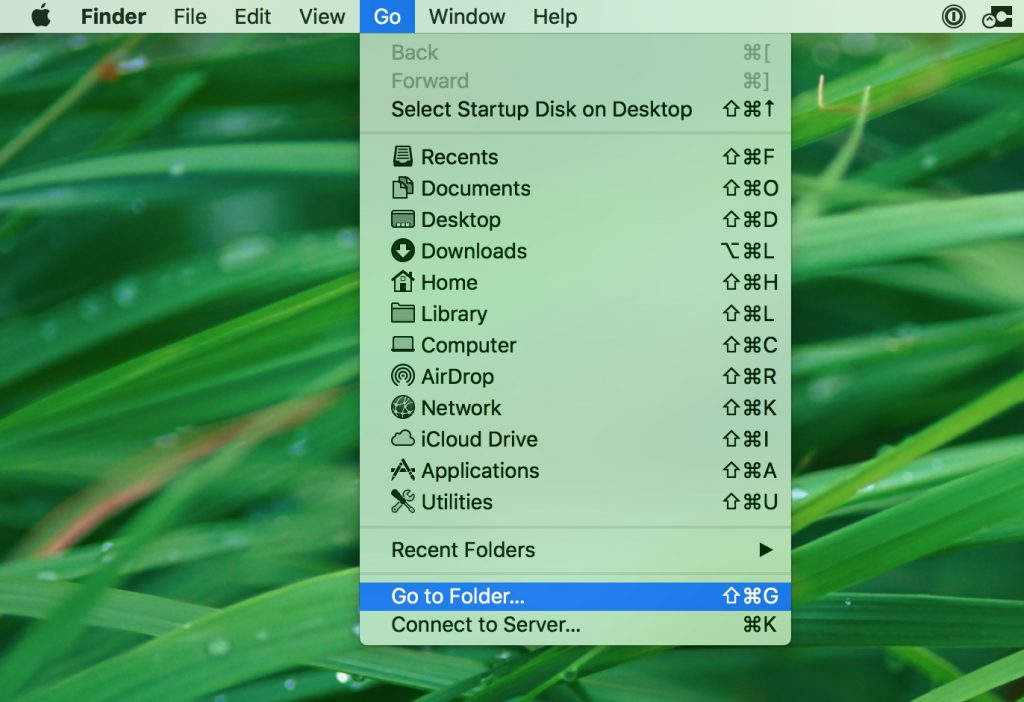
- Go to Finder.
- In the search bar type the name of the app that you want to remove.
- Above the search bar change the two drop down menus to “System Files” and “Are Included” so that you can see all of the files associated with the application you want to remove. Bear in mind that some of the files may not be related to the app so be very careful which files you delete.
- If all of the files are related, hold the ⌘+A buttons to select them and then drive them to “Trash”.
In case you cannot remove Hello Perv via Step 1 above:
In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below:
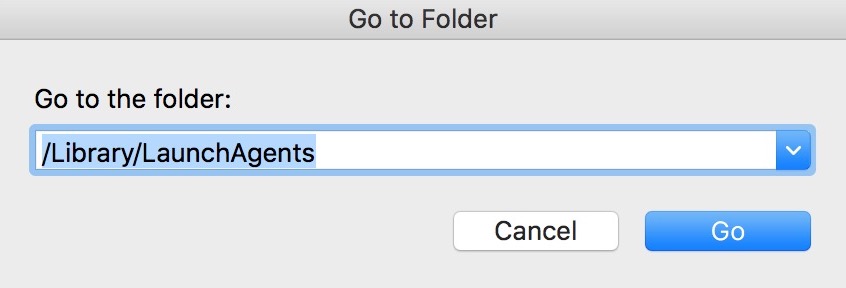
You can repeat the same procedure with the following other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
Tip: ~ is there on purpose, because it leads to more LaunchAgents.
Step 2: Scan for and remove Hello Perv files from your Mac
When you are facing problems on your Mac as a result of unwanted scripts and programs such as Hello Perv, the recommended way of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that will improve your Mac’s security and protect it in the future.
Video Removal Guide for Hello Perv (Mac)
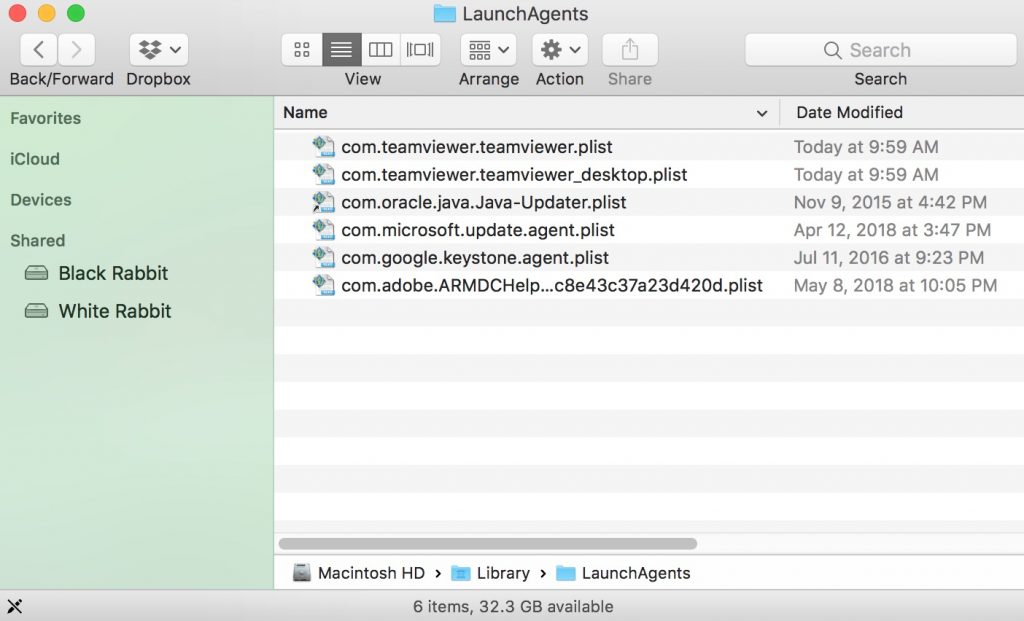
Remove Hello Perv from Google Chrome.
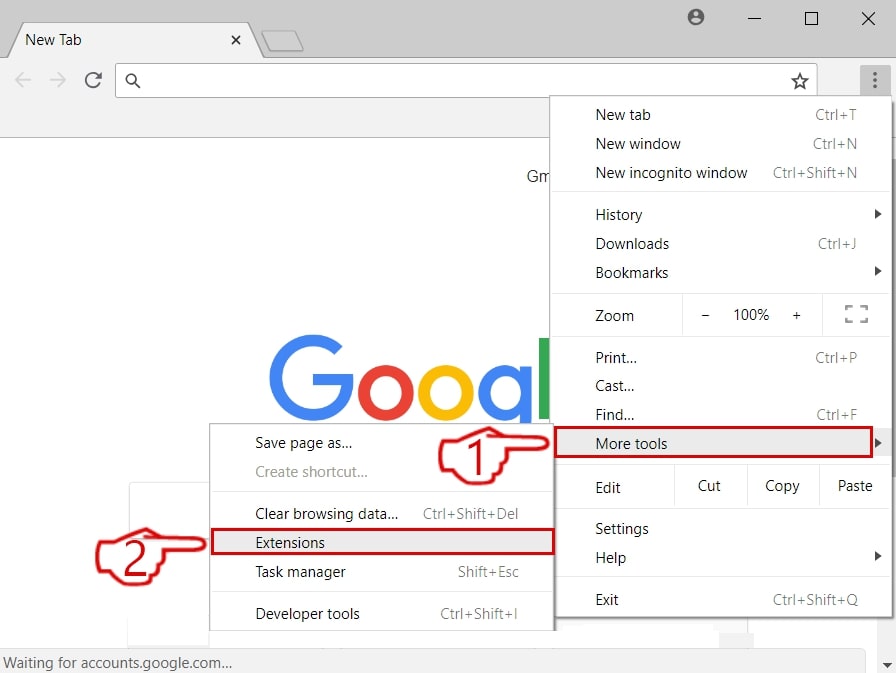
Step 1: Start Google Chrome and open the drop menu
Step 2: Move the cursor over "Tools" and then from the extended menu choose "Extensions"
Step 3: From the opened "Extensions" menu locate the unwanted extension and click on its "Remove" button.
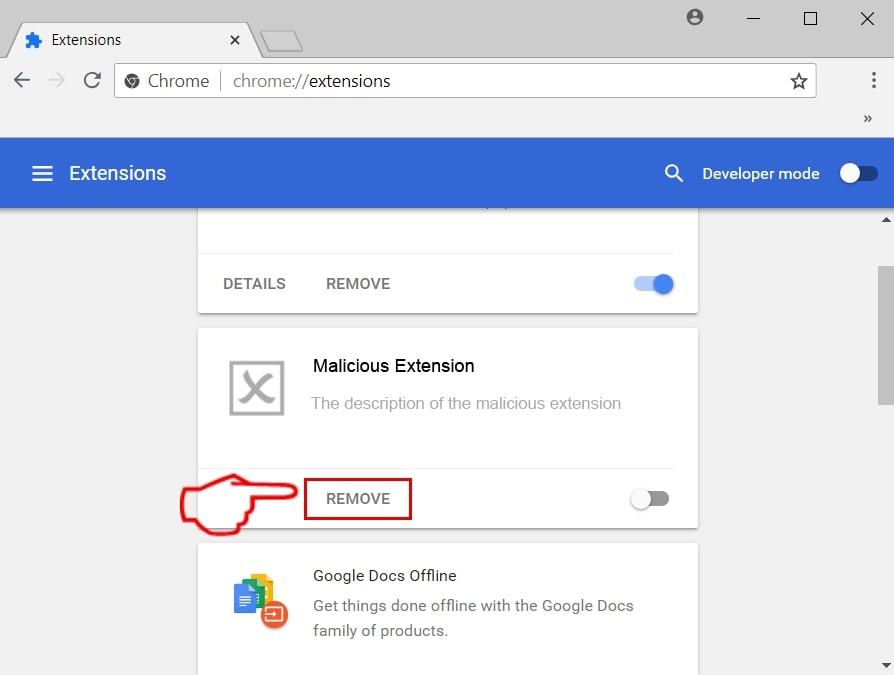
Step 4: After the extension is removed, restart Google Chrome by closing it from the red "X" button at the top right corner and start it again.
Erase Hello Perv from Mozilla Firefox.
Step 1: Start Mozilla Firefox. Open the menu window:
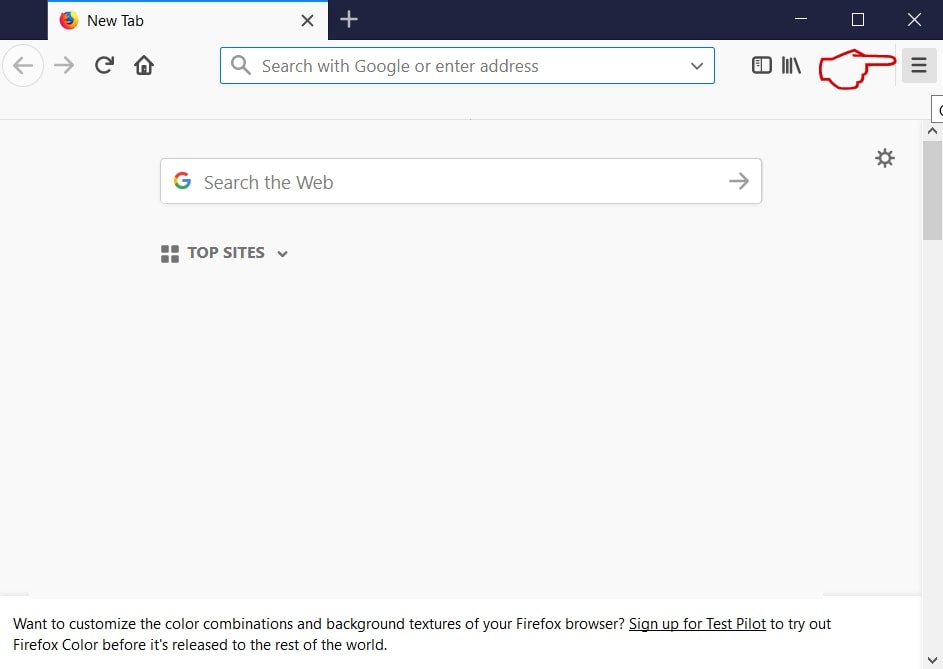
Step 2: Select the "Add-ons" icon from the menu.
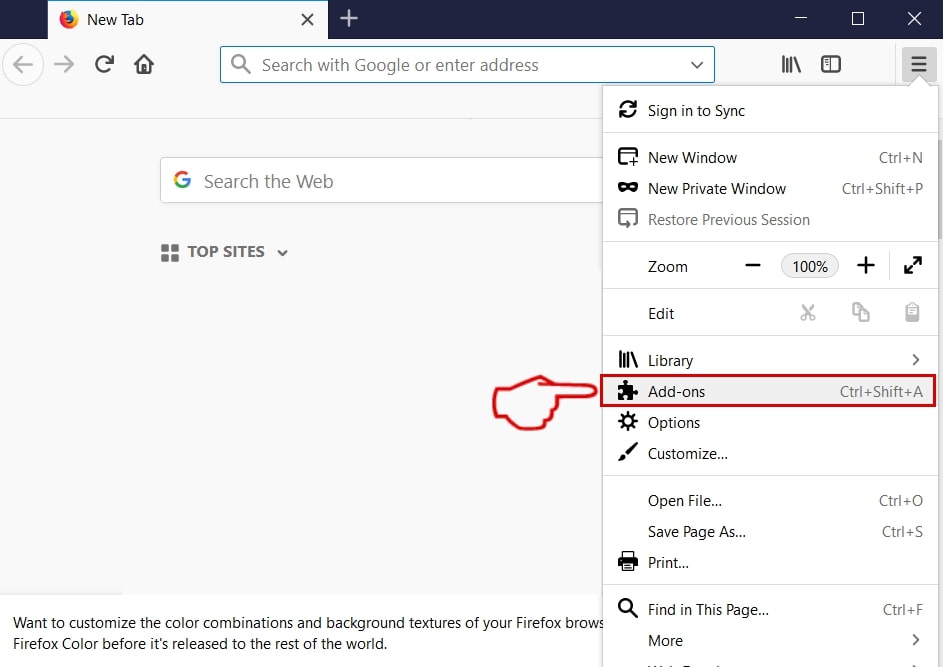
Step 3: Select the unwanted extension and click "Remove"

Step 4: After the extension is removed, restart Mozilla Firefox by closing it from the red "X" button at the top right corner and start it again.
Uninstall Hello Perv from Microsoft Edge.
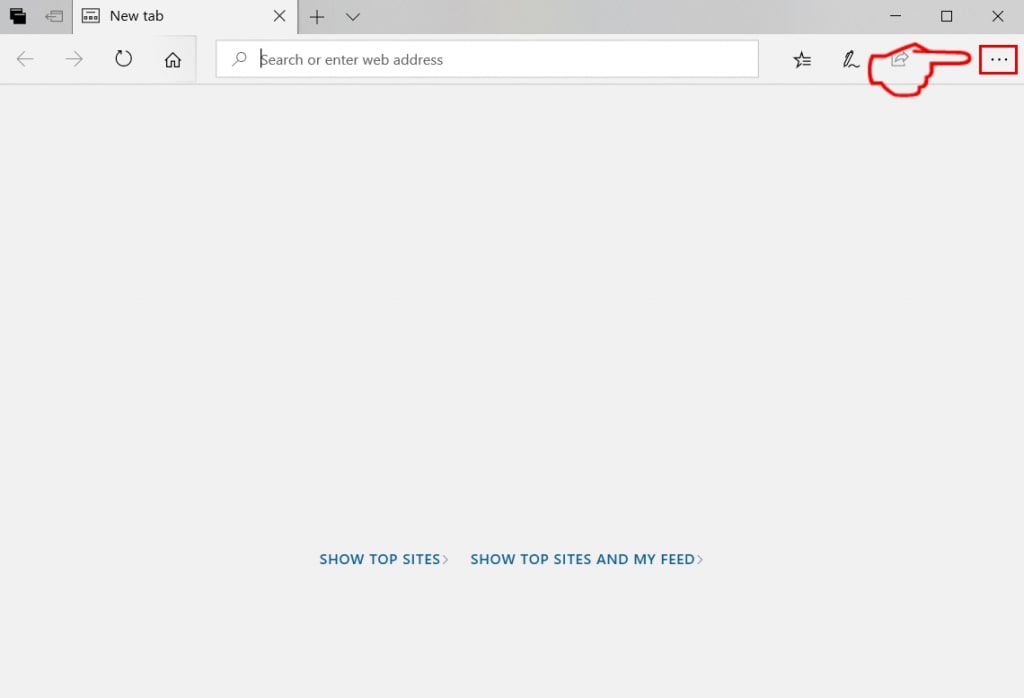
Step 1: Start Edge browser.
Step 2: Open the drop menu by clicking on the icon at the top right corner.
Step 3: From the drop menu select "Extensions".
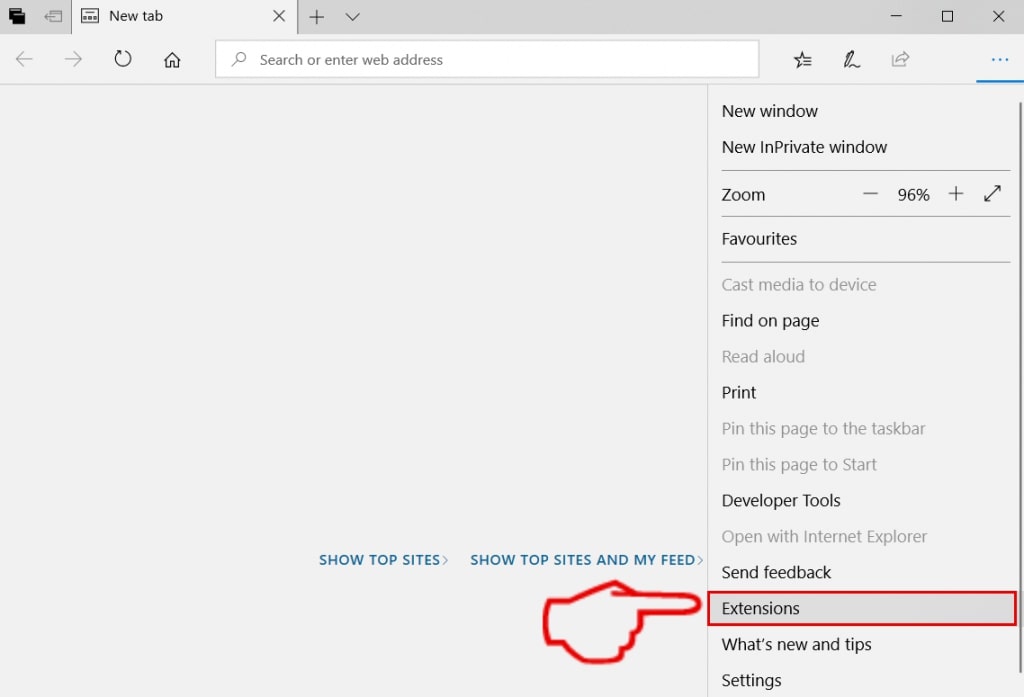
Step 4: Choose the suspected malicious extension you want to remove and then click on the gear icon.
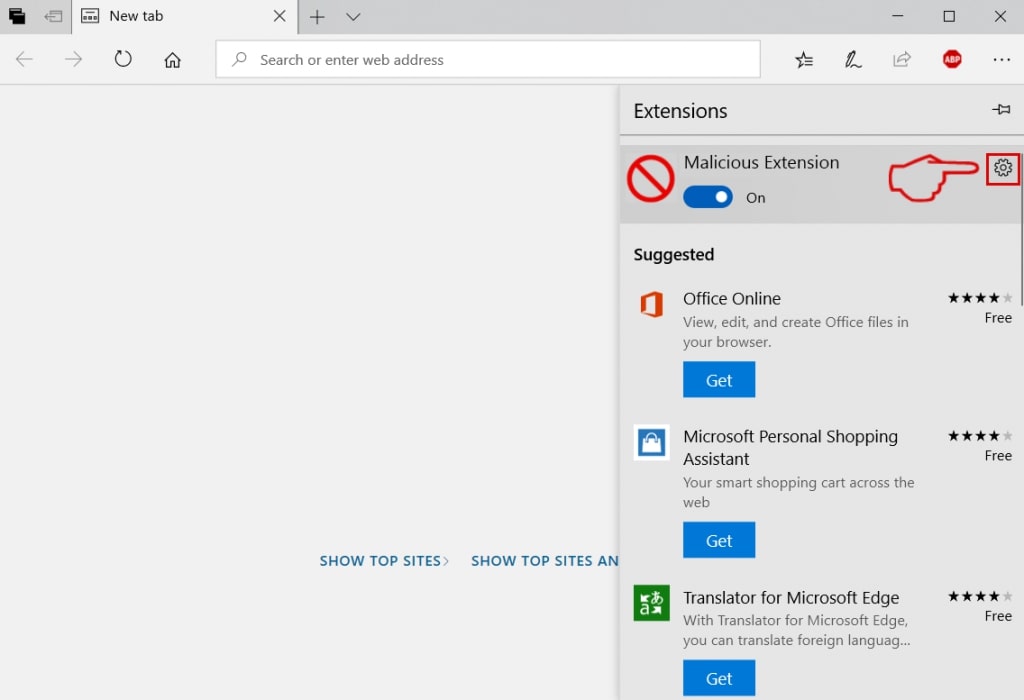
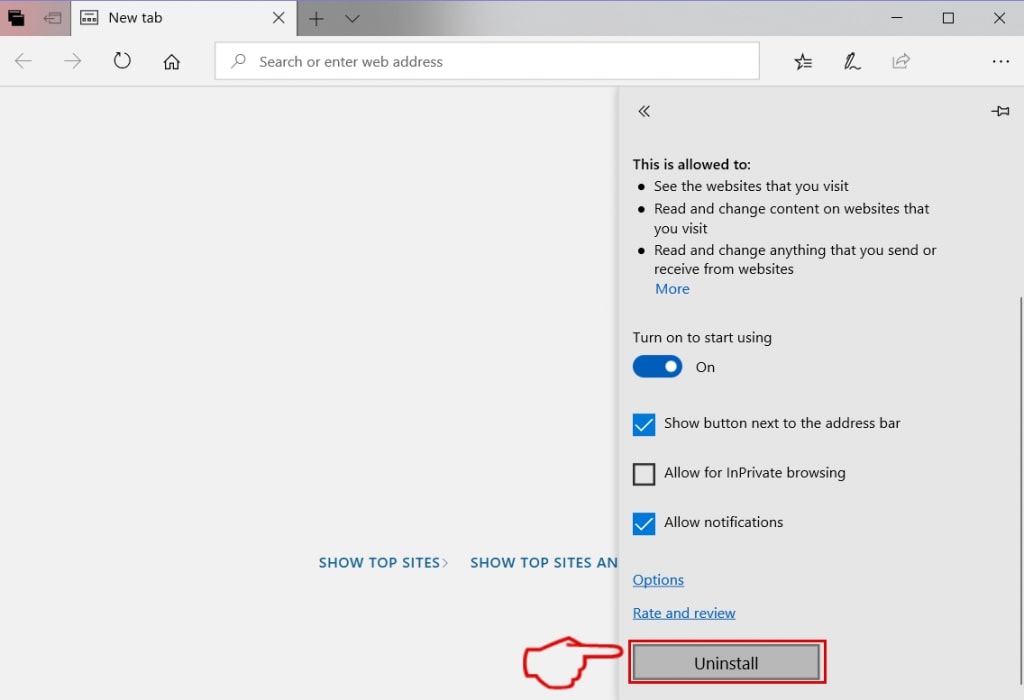
Step 5: Remove the malicious extension by scrolling down and then clicking on Uninstall.
Remove Hello Perv from Safari
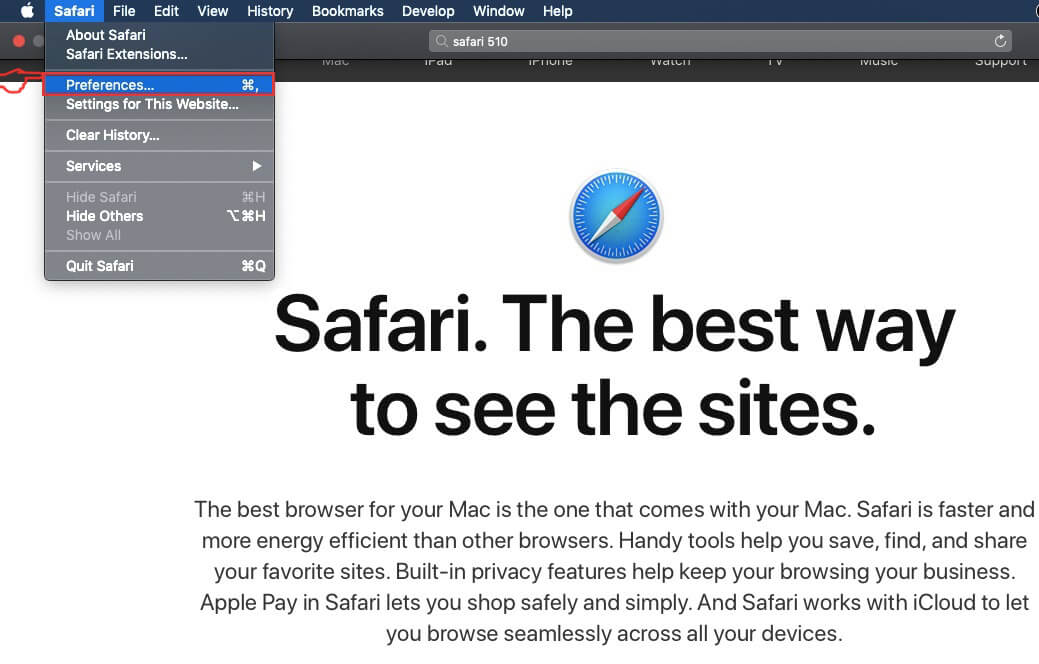
Step 1: Start the Safari app.
Step 2: After hovering your mouse cursor to the top of the screen, click on the Safari text to open its drop down menu.
Step 3: From the menu, click on "Preferences".
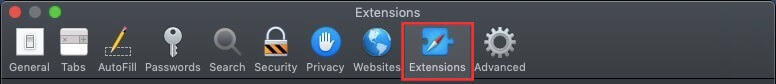
Step 4: After that, select the 'Extensions' Tab.
Step 5: Click once on the extension you want to remove.
Step 6: Click 'Uninstall'.
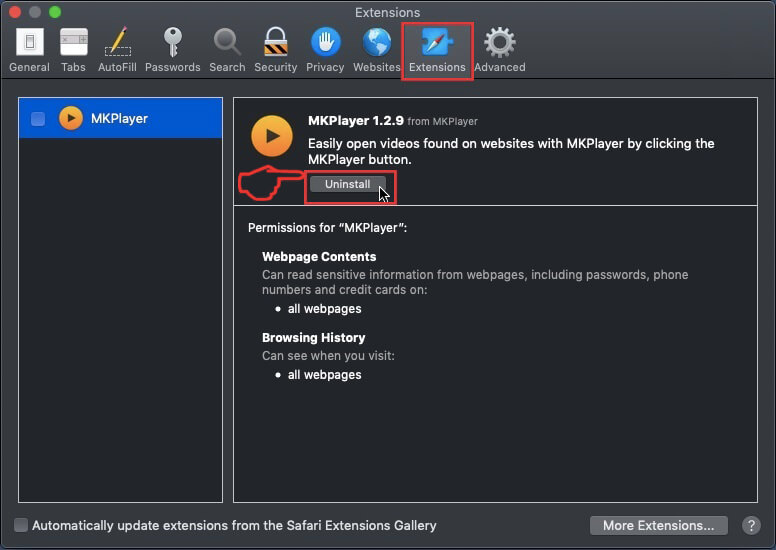
A pop-up window will appear asking for confirmation to uninstall the extension. Select 'Uninstall' again, and the Hello Perv will be removed.
Eliminate Hello Perv from Internet Explorer.
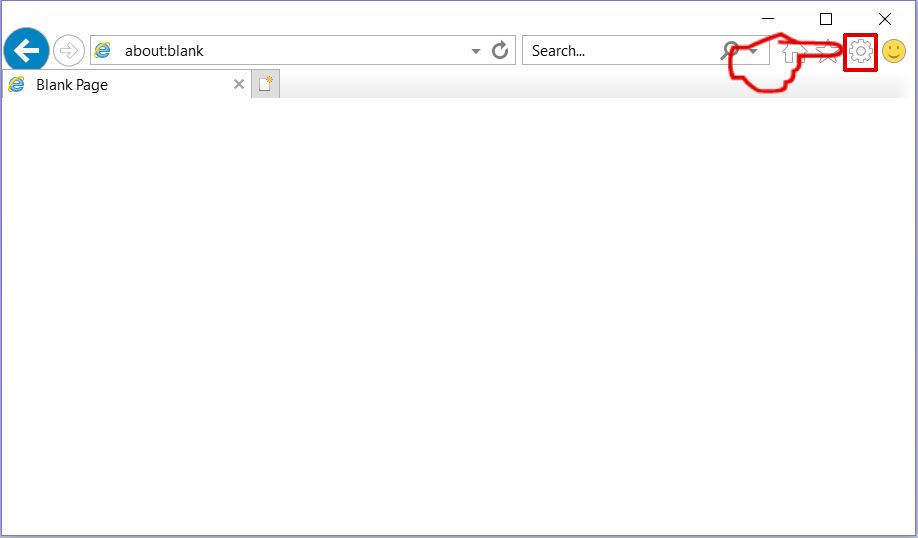
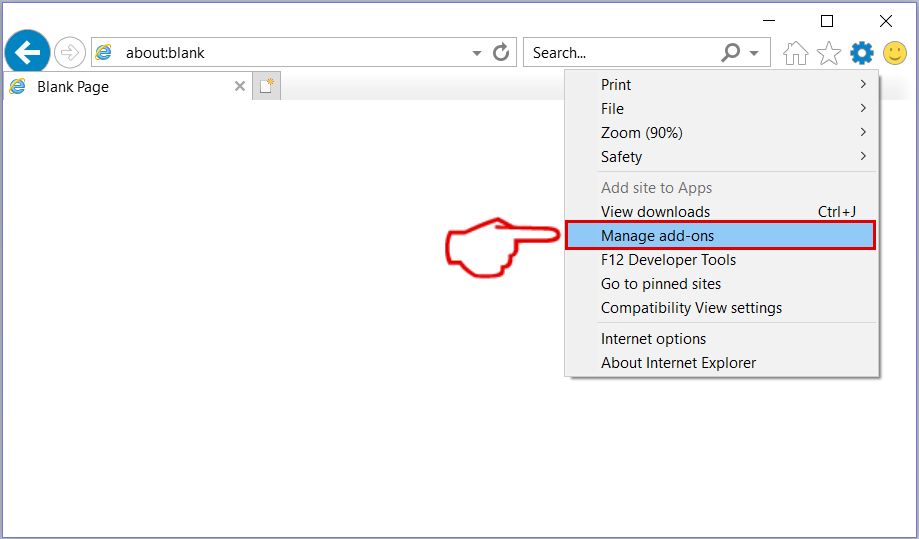
Step 1: Start Internet Explorer.
Step 2: Click on the gear icon labeled 'Tools' to open the drop menu and select 'Manage Add-ons'
Step 3: In the 'Manage Add-ons' window.
Step 4: Select the extension you want to remove and then click 'Disable'. A pop-up window will appear to inform you that you are about to disable the selected extension, and some more add-ons might be disabled as well. Leave all the boxes checked, and click 'Disable'.
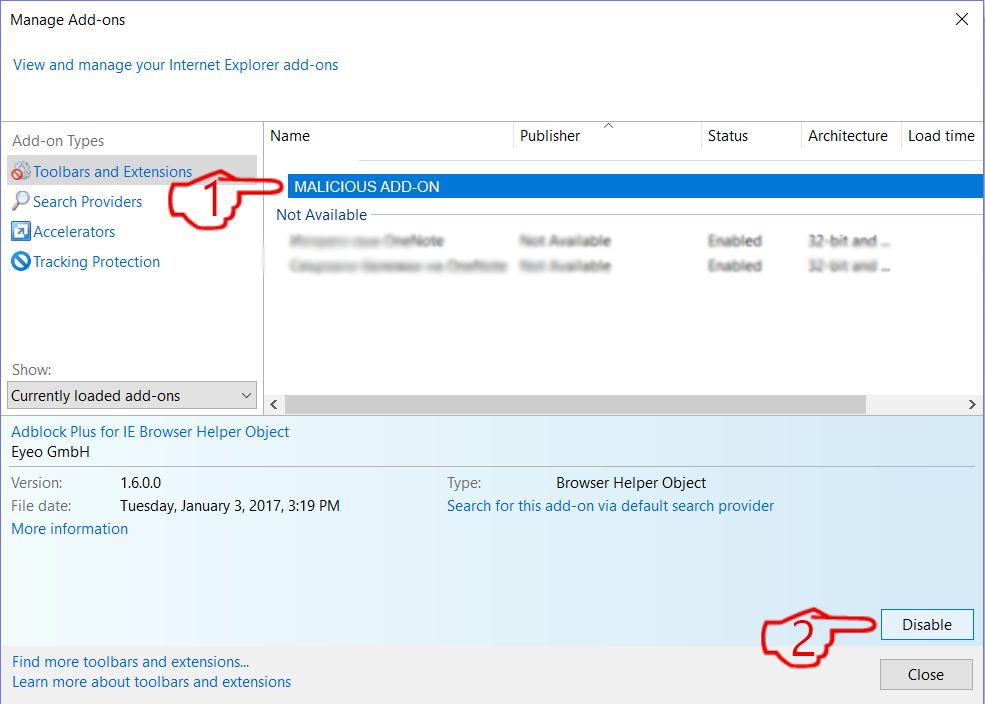
Step 5: After the unwanted extension has been removed, restart Internet Explorer by closing it from the red 'X' button located at the top right corner and start it again.
Remove Push Notifications from Your Browsers
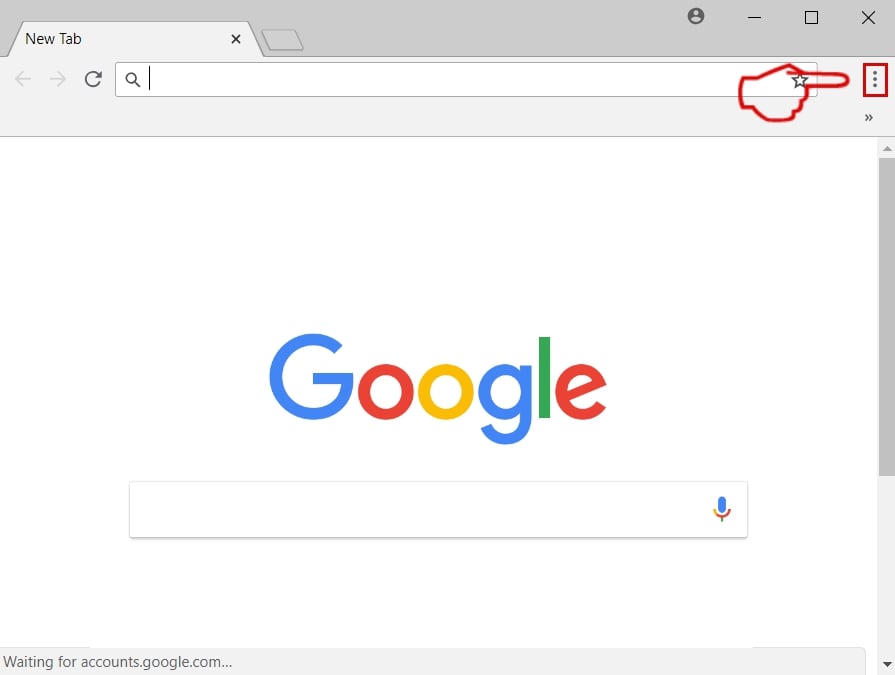
Turn Off Push Notifications from Google Chrome
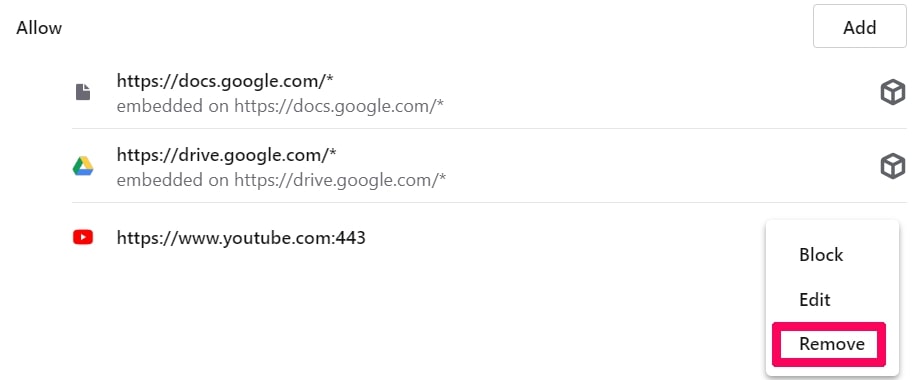
To disable any Push Notices from Google Chrome browser, please follow the steps below:
Step 1: Go to Settings in Chrome.
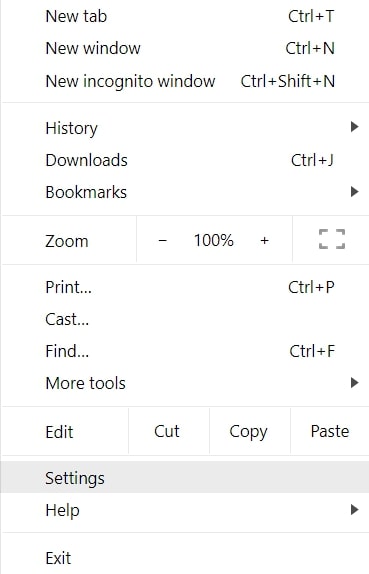
Step 2: In Settings, select “Advanced Settings”:
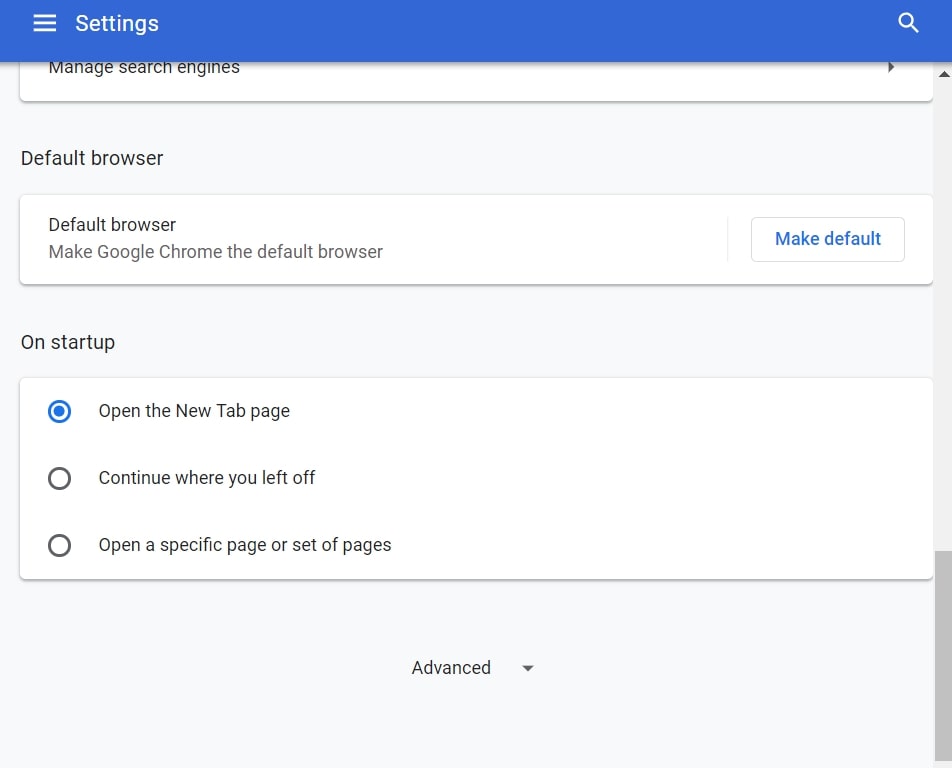
Step 3: Click “Content Settings”:
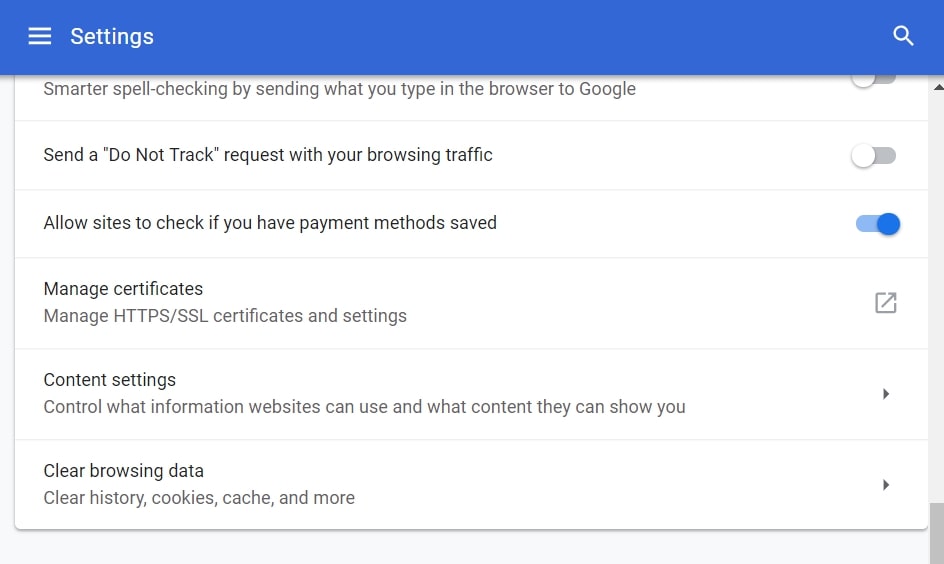
Step 4: Open “Notifications”:
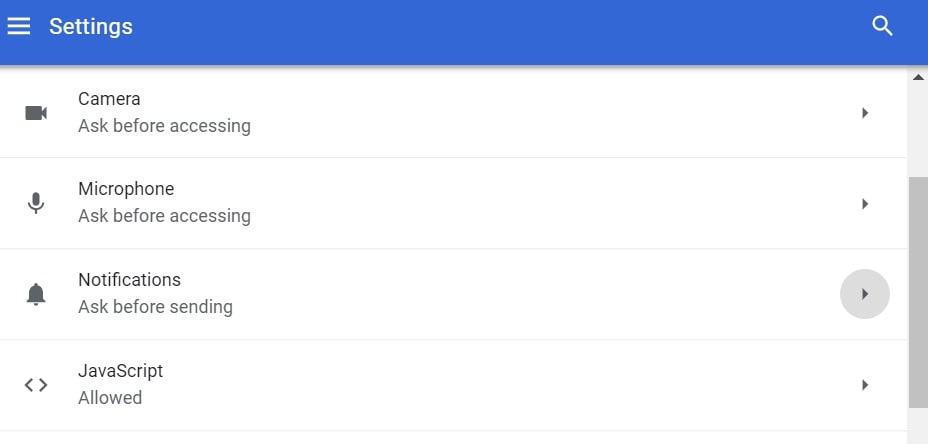
Step 5: Click the three dots and choose Block, Edit or Remove options:

Remove Push Notifications on Firefox
Step 1: Go to Firefox Options.
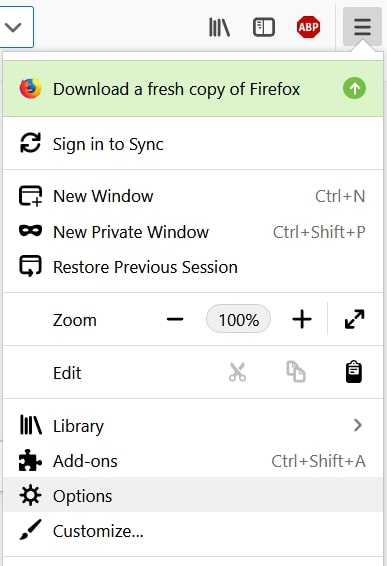
Step 2: Go to “Settings”, type “notifications” in the search bar and click "Settings":
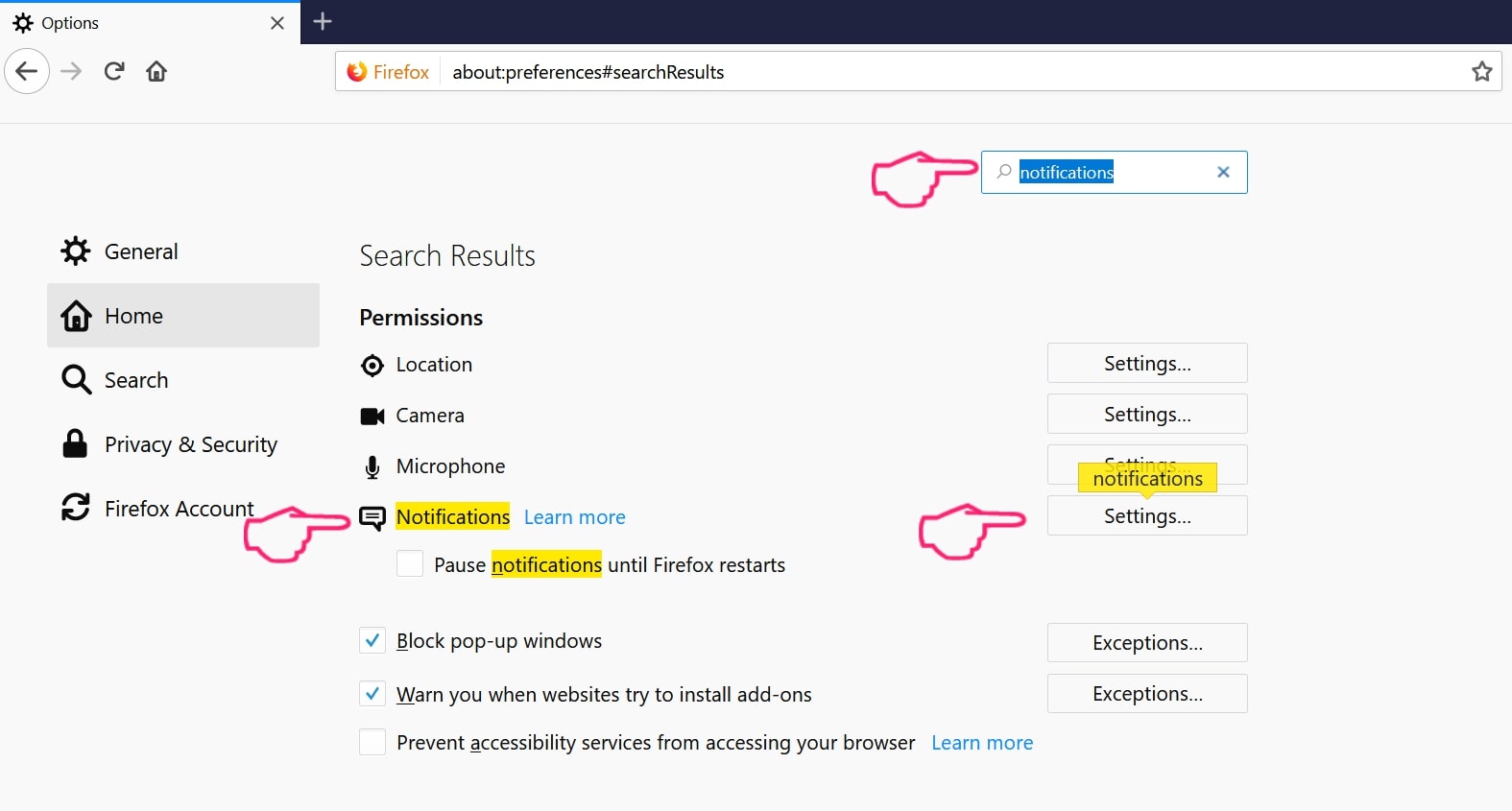
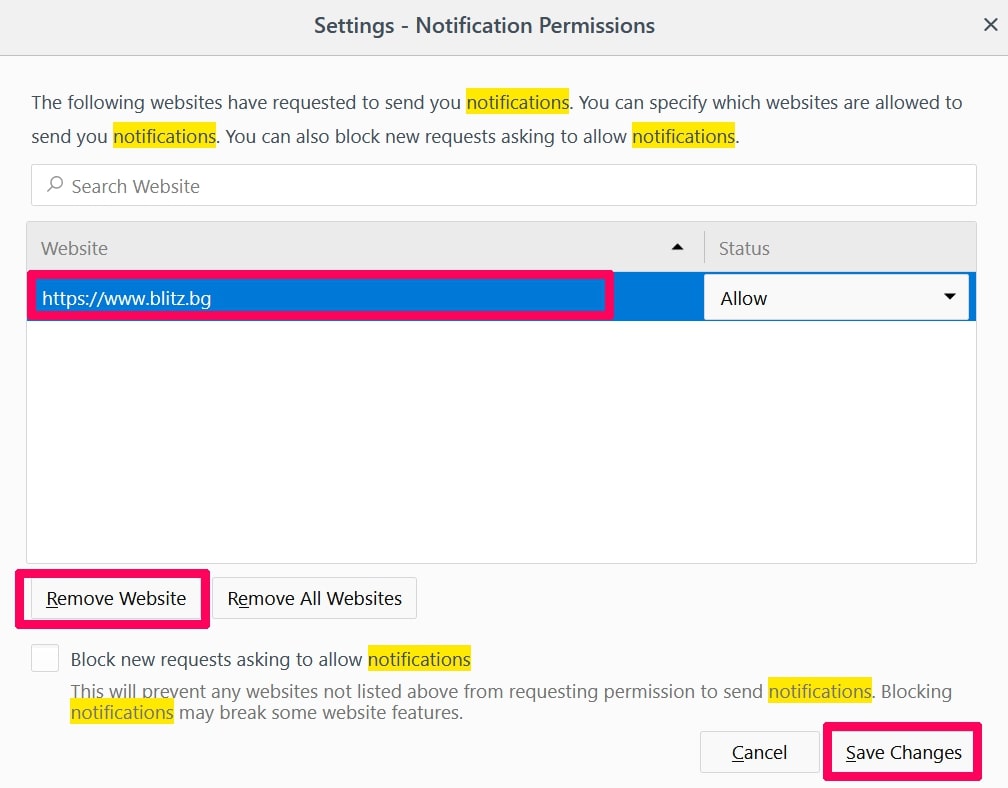
Step 3: Click “Remove” on any site you wish notifications gone and click “Save Changes”
Stop Push Notifications on Opera
Step 1: In Opera, press ALT+P to go to Settings.
Step 2: In Setting search, type “Content” to go to Content Settings.
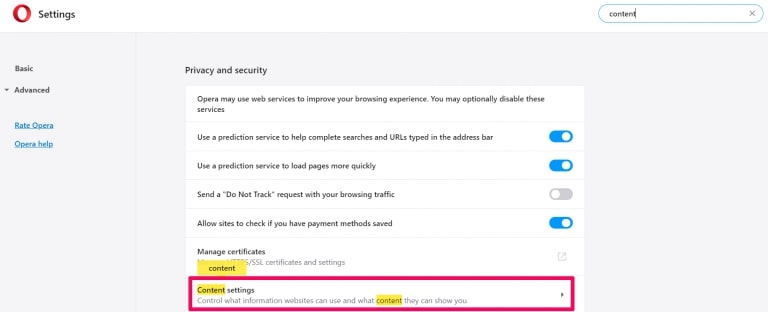
Step 3: Open Notifications:
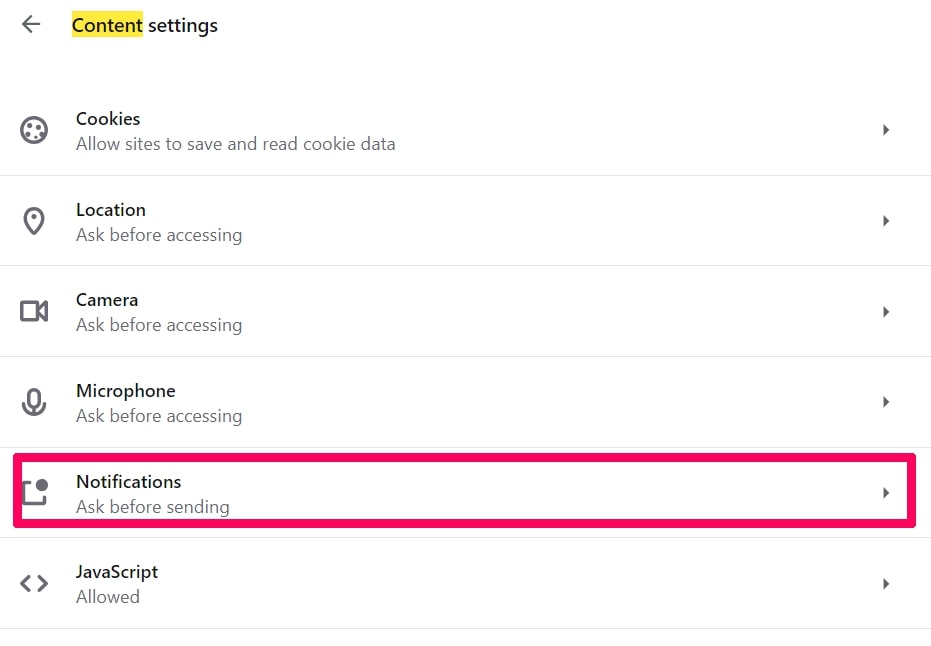
Step 4: Do the same as you did with Google Chrome (explained below):
Eliminate Push Notifications on Safari
Step 1: Open Safari Preferences.
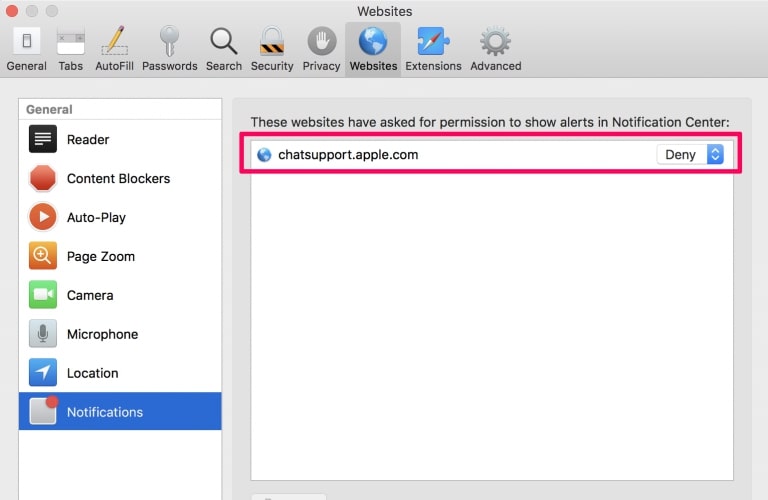
Step 2: Choose the domain from where you like push pop-ups gone and change to "Deny" from "Allow".
Hello Perv-FAQ
What Is Hello Perv?
The Hello Perv threat is adware or browser redirect virus.
It may slow your computer down significantly and display advertisements. The main idea is for your information to likely get stolen or more ads to appear on your device.
The creators of such unwanted apps work with pay-per-click schemes to get your computer to visit risky or different types of websites that may generate them funds. This is why they do not even care what types of websites show up on the ads. This makes their unwanted software indirectly risky for your OS.
What Are the Symptoms of Hello Perv?
There are several symptoms to look for when this particular threat and also unwanted apps in general are active:
Symptom #1: Your computer may become slow and have poor performance in general.
Symptom #2: You have toolbars, add-ons or extensions on your web browsers that you don't remember adding.
Symptom #3: You see all types of ads, like ad-supported search results, pop-ups and redirects to randomly appear.
Symptom #4: You see installed apps on your Mac running automatically and you do not remember installing them.
Symptom #5: You see suspicious processes running in your Task Manager.
If you see one or more of those symptoms, then security experts recommend that you check your computer for viruses.
What Types of Unwanted Programs Are There?
According to most malware researchers and cyber-security experts, the threats that can currently affect your device can be rogue antivirus software, adware, browser hijackers, clickers, fake optimizers and any forms of PUPs.
What to Do If I Have a "virus" like Hello Perv?
With few simple actions. First and foremost, it is imperative that you follow these steps:
Step 1: Find a safe computer and connect it to another network, not the one that your Mac was infected in.
Step 2: Change all of your passwords, starting from your email passwords.
Step 3: Enable two-factor authentication for protection of your important accounts.
Step 4: Call your bank to change your credit card details (secret code, etc.) if you have saved your credit card for online shopping or have done online activities with your card.
Step 5: Make sure to call your ISP (Internet provider or carrier) and ask them to change your IP address.
Step 6: Change your Wi-Fi password.
Step 7: (Optional): Make sure to scan all of the devices connected to your network for viruses and repeat these steps for them if they are affected.
Step 8: Install anti-malware software with real-time protection on every device you have.
Step 9: Try not to download software from sites you know nothing about and stay away from low-reputation websites in general.
If you follow these recommendations, your network and all devices will become significantly more secure against any threats or information invasive software and be virus free and protected in the future too.
How Does Hello Perv Work?
Once installed, Hello Perv can collect data using trackers. This data is about your web browsing habits, such as the websites you visit and the search terms you use. It is then used to target you with ads or to sell your information to third parties.
Hello Perv can also download other malicious software onto your computer, such as viruses and spyware, which can be used to steal your personal information and show risky ads, that may redirect to virus sites or scams.
Is Hello Perv Malware?
The truth is that PUPs (adware, browser hijackers) are not viruses, but may be just as dangerous since they may show you and redirect you to malware websites and scam pages.
Many security experts classify potentially unwanted programs as malware. This is because of the unwanted effects that PUPs can cause, such as displaying intrusive ads and collecting user data without the user’s knowledge or consent.
About the Hello Perv Research
The content we publish on SensorsTechForum.com, this Hello Perv how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific, adware-related problem, and restore your browser and computer system.
How did we conduct the research on Hello Perv?
Please note that our research is based on independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware, adware, and browser hijacker definitions.
Furthermore, the research behind the Hello Perv threat is backed with VirusTotal.
To better understand this online threat, please refer to the following articles which provide knowledgeable details.


