The new iOS 10 operating system did prove to be a bit less secure because of the fact that some features in it were lacking in comparison to the earlier version of iOS(9). This plus the rewards for hacking an iPhone motivated numerous researching companies to put effort in cracking and unlocking in various ways the latest operating system running on Apple mobile devices.
Recently, a report by Renato Marinho, a director at Morphus Labs claims that common criminals have unlocked a stolen iPhone 6S in less than 2 hours time.
An Apple iPhone 6S device which was protected by the newer 6 digit password as well as the unique and typical for iPhones ID fingerprint has become the primary target of thieves who stole it somewhere around October the 15th.
The criminals who hacked the iPhone did not steal any funds or anything of great importance, but somehow they managed to restart the unique Apple ID password from the phone which was locked. The crooks were even able to use social engineering techniques, pretending to be the user of the phone during a phone call to his personal bank.
The researchers believe that the attack was not one of those targeted thefts for which the criminals have to prepare before actually conducting it, primarily because the thief took the iPhone from the victim amongst other items and last.
Furthermore, the thieves did not manage to steal any other documents or information from the victim, only cash and the device itself.
The six-digit password was very difficult to guess because it was completely random without any logical hints that could give it away like a birthdate, phone number, and other information. Despite this, it did not stop the criminals from unlocking the phone and resetting some of it’s credentials in approximately 2 hours time after the theft itself occurred.
As soon as the phone was stolen, the victim attempted to activate the “lost mode” of the iPhone demanding it to be deleted via iCloud. Two and a half hours after the theft has occurred, the victim’s password from his Google account was already changed and shortly after this, the iPhone’s Apple ID password was changed.
Finally, the iPhone was located and erased remotely, but it was already too late because the two important accounts (Apple ID and Google) were restarted.

How Did the Thieves Unlock the iPhone
It remains a mystery on how were they able to unlock the device so fast, but the researchers at Morphus Labs have come up with a theory on how it may have worked.
Based on the investigation over what has occurred, it is likely that since this iOS version displays detailed information from a locked iPhone especially when it comes to account information, the crooks may have unlocked it using methods that allowed for information extraction via the notifications of the device.
Based on the exclusion methods from what was investigated, the criminals could not have used online services that give the Apple ID based on it’s unique IMEI number because these services were time-costly.
The most likely scenario may have been that the criminals used the phone number of the victim which is not difficult to find out. If the phone number is known and along with it the associated names, the crooks could have used this to crack the Google account.
To test this theory, researchers have removed the SIM card associated with the device and inserted it in another phone to reveal the sensitive information. The researchers then attempted to look for the phone number online, primarily googling it or looking on Facebook for any associations with a profile. They did not succeed initially, but later on they have become proactive. The neat researchers managed to install apps such as WattsApp that do not require much to run, and they received crucial information such as the victim’s photo and status this way. Then, they got even more creative and managed to successfully add the profile to a WattsApp chat group and extract the name associated with the Google profile itself.
Then, the researchers inserted back the SIM card in the locked iPhone, but this time they have sent a message to the iPhone from a third-party WattsApp user. This vulnerability allowed them to answer the WattsApp message from the locked iPhone. When they answered the message from the locked phone, the answer message popped up with the unique number, the name as well as the surname in the same way they were arranged in the Google’s profile of the victim. This allowed the crooks to hack into the Google account by simply clicking “Forgot my password”, enter random text on the “Last password you remember” screen and then entering the name, the surname as well as the phone number that is associated with the Google account.
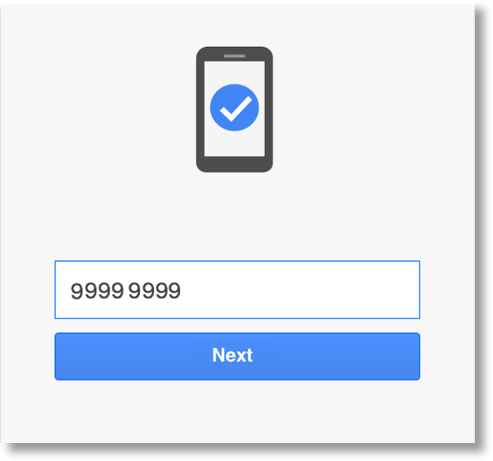
After the phone number was entered, Google immediately sends a unique code, as some of you may know, which if entered on Google’s password recovery page, you can enter a new password, as the researchers were able to do:
The same tactic was used when it comes to the Apple ID account. The researchers went to the password recovery screen and managed to change the password, this time using the hacked Google account to change the victim’s Apple ID password.
Based on this crucial Google and Apple ID information, the phone becomes owned by the criminal. Restarting the phone via iCloud only helps the criminal by cleaning it’s data and allowing the crook to enter the Apple ID, unlock it and hence use the completely wiped iPhone as it was always theirs. Simple, but genius.

What Conclusions Can Be Drawn
It is not clear whether the criminals have used this or other methods which were approximate, but first the Google account’s password then the AppleID were changed, allowing the criminals to possibly reset and unlock the device by using the information of the victim (name and phone number).
There are several important points that can be drawn according to Marinho. One of those is the notifications on the phone. While those notifications are very convenient if you wish to reply someone in a speedy manner, it gives anyone the possibility to read SMS messages as well as WattsApp “pm’s”. These notification settings should be disabled on the spot fully or partially.
Also, users who are sensitive about security should realize that the SIM card of the phone is it’s primary security weakness. While there is encryption used on iPhone devices, there is almost in any case no password protected SIM cards, and most of their PIN codes are the default ones.
Two-factor authentication is a good security measure to secure your mobile device, and it is strongly advisable to use it because it does not only rely on the phone number to change a password but also gives the possibility to choose from multiple methods for logging in.
Since there can be negative consequences for anyone, researchers feel concerned about the future security of SIM cards and that not every user is educated well enough to protect the devices properly. In our opinion efforts should be made to increase the security of the phones themselves when it comes to sim cards and applications as well as notifications, but users should also be educated basic security habits.